How Can ‘Security’ Systems Benefit The Larger Enterprise?
Editor Introduction
Security systems are vital to any company. Nowadays, however, they can also provide additional benefits to any enterprise beyond protecting people, assets and facilities. Specifically, systems that were previously focused on security can now be leveraged in new ways to benefit the broader enterprise. When this happens, the security department transitions from a ‘cost center’ to a repository of data that can benefit the whole company, and even contribute to the bottom line. We asked this week’s Expert Panel Roundtable: How can ‘security’ systems benefit the larger mission of an enterprise?
Since the larger mission of most enterprises is going to focus on growing revenue, anything a security system can do to help achieve that goal is a big win. Reducing shrink and loss is top-of-mind when we think of security, and its impact to the bottom line, but the latest AI-enabled cameras and systems go far beyond loss prevention to actually enhance and validate how a company operates and sells to its customers. These new security systems deliver business and operational intelligence that enables companies to analyze data such as entry counts, dwell times, paths, queues and product interaction. They also make it easy to compare this data with powerful dashboards showing the relative performance at each location. In this way, modern security systems are evolving into smart data sensor networks that marketing and sales teams increasingly rely on for validation of product placement and other measurable marketing initiatives.
Of course, security systems are valuable in keeping the people and assets of an enterprise safe, but security technology plays a larger role in the operational efficiency of an enterprise. In particular, during the pandemic, traditional security technologies such as people counting, queue management, access control, IP intercom and remote monitoring helped enterprises get back to business in a safe way that adhered to current guidelines. Even after the pandemic, these technologies will continue to play a key role, helping organizations to make more data-informed business decisions and improving the safety and security of the enterprise. Whatever an enterprise’s mission is, the right security system can make day-to-day activities more secure and efficient and allow for employees to focus on their business goals.
Security systems can do much more than simply record video to a VMS or NVR. With the latest developments in AI-based onboard analytics, cameras can be used to provide actionable data that helps businesses get a holistic view of their operations that goes beyond security. AI-based cameras can accurately measure customer traffic patterns in stores and help validate product display campaigns by showing dwell times. Queue analytics can help allocate staff when and where they are needed, and with object detection analytics, a camera can tell the difference between a human arriving at the entrance of a building and traffic passing by in the same field-of-view. With these advances, and more on the way, physical security systems are increasingly applied in non-traditional security applications to drive business value and become an essential part of an organizations’ technology strategy.
Security systems were once used strictly for security. Savvy enterprises realize that the value of security technology can extend into everyday business. As the number of IoT sensors expands, so does the amount of data collected. Instead of storing, ignoring, and eventually throwing that data away, organizations can leverage it to develop insights and identify patterns of behavior. This can help them make informed operational decisions, such as making better use of their space or optimizing the flow of people. There’s also an opportunity to create a common operating picture between physical and cyber security to manage enterprise risk more effectively. For instance, a vulnerability detected in one realm could trigger a change in the threat level in the other. To make this possible, technology vendors must become more aligned with their customers’ mission. No longer just a cost center, physical security departments become a source of valuable insights.
When it comes to the overall mission of an enterprise, security and safety systems contribute to maintaining both the bottom line and the top line of a company. A comprehensive system contributes to the safety and security of the company, its suppliers and partners protecting valuable assets. As an investment, it limits potential loss caused by different illegal activities. Not only do security systems help minimize loss, they can also increase revenues of enterprises by making the overall environment a safer space to operate in.
In any modern enterprise business, the requirement of electronic security has become increasingly vital. But, this in itself also has its own requirements. Security systems are designed to offer protection and reliability to the end user, and this protection falls into many different categories. In these trying times, we must look to offer features and functions above and beyond standard security disciplines. To benefit any end user, we have to look to ever-more-sophisticated technology as key. For example, access control permissions can be automatically managed by using middleware between the HR system and the security management systems. Health screenings as a part of access control will become a part of everyday life as will contact tracing. How about ANPR for car park access and space management or IT racks that can be secured providing audit trails? Then there’s integration to smart buildings that can assist with lighting and power control.
Typically, when people think of security, turnstiles, security guards and CCTV are the first things that come to mind. However, it goes so much further than ensuring a lobby or asset is secure, has a physical security presence, or an eye in the sky. Through flexible third-party integrations, a whole enterprise can be elevated to maximize the health and safety of its staff and guests and improve building efficiency. Fastlane products benefit from the capability of being integrated with all known security and building management systems. We have been seamlessly integrating Fastlane turnstiles and Door Detective door entry products with third-party technologies such as video analytics, time-and-attendance, HVAC and identity management for many years now, providing data and intelligence to building owners about how their asset is being used by its occupants.
Editor Summary
When the security department seeks to expand its mission beyond security, new doors open up throughout an enterprise. Fortunately, many newer technologies on the market enable security professionals to do just that. The capabilities exist. The first step to taking advantage of these new technologies is for security personnel to resolve to look at the bigger picture and focus on the company’s business (and bottom line) in addition to keeping criminals at bay.
- Related links
- Infrared Surveillance cameras
- Biometric Access control software
- Real Time Network Video Recorders (NVRs)
- Control Software Video Surveillance software
- Contact Access control software
- Detection Software Video Surveillance software
- TFT LCD Security Monitors
- Real Time / Event Network Video Recorders (NVRs)
- Thermal Surveillance cameras
- Wireless Surveillance cameras
- Carpool Anti-passback Access control software
- Proximity Access control software
- IP Surveillance Software Video Surveillance software
- Management Software Video Surveillance software
- Monitoring Software Video Surveillance software
- Surveillance Software Video Surveillance software
- Door Monitoring Option Access control software
- Face Recognition Software Access control software
- ID Badging Software License Access control software
- License Access control software
- Management Systems Upgrade Access control software
- Remote software for telecode door entry phone system Access control software
- Server software for MSDE Access control software
- Version Upgrade Access control software
- Visitor Management tool Access control software
- Axis Communications Video Surveillance software
- Axis Communications Access control software
- Genetec Video Surveillance software
- Genetec Access control software
- Hanwha Vision Surveillance cameras
- Hanwha Vision Video Surveillance software
- IDL Access control software
- Axis Communications Network Video Recorders (NVRs)
- Genetec Network Video Recorders (NVRs)
- Hanwha Vision Security Monitors
- Hanwha Vision Network Video Recorders (NVRs)
- Axis Communications Security camera lighting
- Hanwha Vision Security camera lighting
Expert commentary
Security beat
Security bytes
- Getting To Know Dan Grimm, VP And General Manager Of Computer Vision At RealNetworks
- Big Wins And The Importance Of Showing Up: Insights From SecurityInformed.com Editor Larry Anderson
- Setting Goals, Business Travels And Radioactivity: Success Secrets From Tiandy's John Van Den Elzen
- Getting To Know Jeff Burgess, President/CEO At BCDVideo
Mobile access articles
Zenitel, a provider of intelligent communication solutions, announced the launch of two new door entry intercoms: the Turbine Extended Intercoms TEIV1+ and the TEIV4+. The new products display Zenite...
Physical security is essential for a modern production facility, users don’t want just anyone entering the building or accessing secure areas. But what about production machinery? Machine authe...
Frontline Communications, a division of Pierce Manufacturing, Inc., an Oshkosh Corporation business, announced the delivery of a C-40X-2 mobile command vehicle to the Loudoun County Sheriff’s Of...
Paxton Access, the international security technology manufacturer, officially launches the highly anticipated video intercom mobile app, Paxton Entry. The brand-new app is available on the market as o...
Zimperium, the industry pioneer in mobile security, announced the availability of its mobile security portfolio in AWS Marketplace, a digital catalog with thousands of software listings from independe...
An attention-grabbing exhibit at GSX 2024 in Orlando involved a robot dog that could open a door. Boston Dynamics robot dog ASSA ABLOY impressed attendees with the robotics demonstration, featuring...
Identity-based cyber attacks continue to prevail and impact organizations. Stealing credentials was the top initial action in breaches, according to Verizon. Plus, 84% of identity stakeholders survey...
Providing exceptional professional services, enhancing guest experiences, and organizing structured hotel activities are essential for building a strong reputation and cultivating a loyal customer bas...
Commvault, a pioneering provider of cyber resilience and data protection solutions for the hybrid cloud, announced it will acquire Clumio, a technology pioneer in data protection for critica...
As part of the company’s ongoing efforts to continue innovating to deliver the highest quality product offerings for the fast-changing security industry, Axis Communications is exhibit...
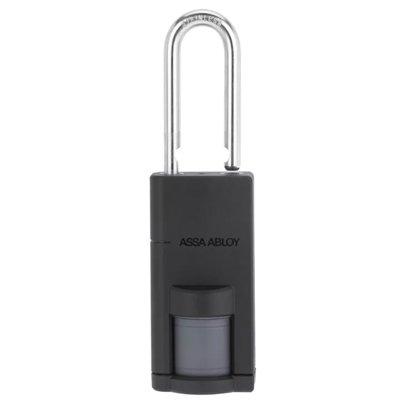
ASSA ABLOY Opening Solutions returns to Global Security Exchange (GSX) for 2024's powerhouse get-together of security professionals from around the world. Digital access control Attendees can visit...
Salient announced CompleteView v7.5, the latest update to its industry-leading video management platform. This version introduces improvements to operator experiences as well as major new enterprise c...
Munich’s Hofbräuhaus enjoys an iconic status, as both a heritage property and a spiritual home for lovers of German beer. “In this historic building is the world’s most famous t...
Radiofrequency (RF) technology specialists, SPX Communication Technologies launched Evenlode Lite, an entry-level video downlink system designed for regions new to airborne surveillance or those looki...
Wavelynx Technologies, a trailblazer in advanced, secure, and versatile reader and credential solutions, announced the launch of its industry-first app, Configure by Wavelynx, to revolutionize th...
The 2024 State Of Physical Access Trend Report
DownloadThe Security Challenges Of Data Centers
DownloadSecurity Practices For Hotels
DownloadHow To Solve The Disparate Systems Challenge
DownloadArtificial Intelligence
DownloadClimax Technology TouchPanel-3
Anviz M7 Palm Biometric Access Control
ASSA ABLOY Aperio P100 Padlock