Counter terror






News
3xLOGIC, a pioneering provider of integrated and intelligent security and business solutions, will debut its recently launched edge-based deep learning analytics cameras at The Security Event 2024. The X-Series cameras combine state-of-the-art hardware with advanced analytics to deliver real-time, accurate, and actionable data, transforming how surveillance systems can be deployed and utilized. The X-Series uses object, people, perimeter, and vehicle identification algorithms to provide accurate detection and tracking in dense, complex, and busy environments. Using vast volumes of representative data, the cameras continuously analyze movements and behavior, while using predictive analysis to constantly track each object. Motion-based solutions The level of filtering is mainly useful for improving accuracy or seeing intricate behaviors 3xLOGIC’s analytics technology utilizes appearance-based models, as opposed to established motion-based solutions that depend solely on changes in pixels over time to indicate movement. This decreases the opportunity for false positives resulting from elements such as illumination changes or foliage, as the trackers identify and ignore them because they don’t look like objects of interest. This level of filtering is particularly effective for improving accuracy or detecting complex behaviors, and once an object begins tracking, a unique identification code is assigned that stays with the object in the field of view. 3xLOGIC’s deep learning analytics X-Series cameras can be deployed both indoors and outdoors and allow valuable business intelligence to be gained. Core applications include retail, commercial and office premises, education, hospitality, warehousing and distribution, healthcare, and critical infrastructure. 3xLOGIC’s deep learning analytics provide information about dwell time, entry and exit, appearance, and disappearance, abandoned and removed objects, traffic direction and tailgating, as well as people movement and counting. 3xLOGIC's VIGIL video management system Integration with VIGIL TRENDS makes security management easier and more efficient X-Series cameras form an integral part of 3xLOGIC's VIGIL video management system, allowing users to harness the full potential of their surveillance ecosystem. For example, person, object, and vehicle detection capabilities can be integrated into VIGIL CLOUD, so that only actionable detection and notifications are delivered. Meanwhile, the VIGIL Server provides support for use cases such as perimeter protection, business intelligence, and alarm notifications. Integration with VIGIL TRENDS makes security management easier and more efficient by turning data into meaningful information – collating, deciphering, and presenting it in a way that makes sense by showing present and historical data in a business context. X-Series edge-based deep learning analytics 3xLOGIC’s Mike Poe, Director, Product Management at 3xLOGIC said, "Our X-Series edge-based deep learning analytics cameras empower organizations to take their security to the next level by providing them with powerful analytical tools that deliver insights and actionable data, enabling them to make informed decisions and respond quickly to potential security threats.’
Over recent months, global rivals have made rapid progress in the proliferation of VTOL & Fixed Wing platforms and breakthrough technologies being used and integrated into their military strategies and warfare activities. Such escalation in recognition, advancement, and use, has posed a significant threat to U.S. programs and security, impacting civil and commercial targets alike. With these threats on the doorstep, it is essential to efficiently build out powerful countermeasures against malicious drone activities and to rapidly roll out these defense strategies and applications. Challenges with drone activity With these pressing needs in mind, ACI (the American Conference Institute), will gather top government pioneers, counter-unmanned technology experts, and global allies to share insights and build a collaborative plan to counteract the evolving challenges posed by drone activity. The 3rd Annual National Congress on Counter UAS Technology will take place on May 23-24, 2024, at the Cooperative Plaza Conference Center in Arlington, VA. Real-time usage of drone technology The 2024 event will shed light on the most complex technologies and legislation evolving in drone technology For those looking for an interactive review of global drone activities and national defense applications, this is the event for those visitors. Delving into the real-time usage of drone technology in war, emerging federal policies, and more, the 2024 event will shed light on the most complex technologies and legislation evolving in this space, while also providing a platform for collaborative efforts between government pioneers and technology innovators. Speakers at the summit Government, DoD & Industry Speakers at the summit will include Chairman, Major Gen (USAF-ret) James Poss (CEO, ISR Ideas, Former Assistant Deputy Chief of Staff for ISR, HQ, U.S. Air Force, Washington, D.C), Jeremy Kofsky (Senior Fellow, Information Warfare Institute for AI Research, Former AI Implementation DoD Fellow, USMC), Micah Campbell (Executive Director, UAS & Emerging Entrants Security AXU, Security & Hazardous Materials Safety), Travis Moran (Senior Reliability & Security Advisor, Federal Energy and Regulatory Commission (FERC)), Colonel Mike Parent, USA, (Chief, Joint Counter sUAS Office Acquisition and Resource Division) Brandon Youngblood, Group Manager, UAS Security and C-UAS Integration, FAA) and many more!
Elite Interactive Solutions (EIS), a pioneer in guard replacement services using proprietary intelligence and 100% verified police calls, announces the Chairman of its Law Enforcement Advisory Board (LEAB) has been selected for a public sector appointment. Tom Stone has been named Police Commissioner-at-Large to the Westtown-East Goshen Regional Police Department (WEGO) by the Board of Supervisors of Westtown and East Goshen Townships (Pa.). Review of policies and procedures He has served on Elite’s LEAB for 12 years and is a staunch ally of the company’s crime prevention efforts Tom Stone serves with an elected supervisor from each township. The Chief of Police reports directly to the WEGO Police Commission, which is also responsible for the review of policies and procedures and the direction of the department. He has served on Elite’s LEAB for 12 years and is a staunch supporter of the company’s crime prevention efforts and remote guarding’s role in reducing false alarm responses. Tom Stone is Executive Director Emeritus of FBI-LEEDA and was instrumental in establishing that organization’s educational development programs. He continues his commitment to law enforcement excellence through this new role. Law enforcement and public safety “I am honored to have been appointed to the Westtown-East Goshen Regional Police Commission,” said Tom Stone, adding “I look forward to working with the commissioners, the chief, and the dedicated men and women of the WEGO Police Department to ensure they have the resources needed for their safety and for the citizens they serve.” Tom Stone’s more than four decades of law enforcement and public safety experience include 22 years as Chief of Police and/or Public Safety Director. Additionally, he has worked with major law firms and municipalities to analyze police situational issues and provide expert opinions and reports, as well as expert testimony as needed.
The City of London Crime Prevention Association (CoLCPA) has proudly relaunched the Building Security Assessment Scheme in collaboration with the National Security Inspectorate (NSI) at Fishmongers’ Hall in the heart of the City of London. Security and fire safety Formerly known as CoLCPA’s Building Security Accreditation, this long-standing initiative, developed from a collaboration involving the City of London Police, the City of London Corporation, representatives of managing agents, and the security industry, aims to strengthen security and fire safety standards within multi-occupied commercial buildings. In existence for more than a decade, the scheme serves as a benchmark reflecting the commitment of the property owners or their representatives to safeguarding their premises, staff, visitors, and the public. Self-assessment Applicants undertake a self-assessment of their building’s security strengths and vulnerabilities Earlier in 2023, in response to evolving security needs, CoLCPA invited NSI to refresh the scheme, ensuring it aligns with the current security requirements while being practical for those overseeing building security. NSI is the sole third-party assessing body and has also taken over the administration of the scheme, streamlining the process for applicants. Applicants undertake a self-assessment of their building’s security strengths and vulnerabilities, followed by an independent on-site review by NSI. This process provides valuable insight into the existing strengths and constructive feedback for potential improvements. Comprehensive scheme criteria The comprehensive scheme criteria cover risk assessments, evacuation and evacuation plans, trauma pack accessibility, Safe Haven status, electronic security measures, and personnel training including Project Kestrel fire training and counter-terror training. Following a successful pilot in London, the first premises assessed under the new scheme received their award certificates at CoLCPA’s November meeting: 125 Old Broad Street, London EC2, Cushman and Wakefield, security provider: Unitrust 1 Curzon Street, London W1, landlord: Colliers, security provider: Vigilant Berkeley Square House, London W1 landlord: Colliers, security provider: Vigilant 33 Cavendish Square, London W1, landlord Colliers, security provider: Vigilant Future-proof current and planned changes The scheme will enhance the safety and security of all building occupants, and support the blue light services" Don Randall MBE, Chairman City of London Crime Prevention Association commented, “The CoLCPA are extremely pleased to be able to partner with NSI and update and refresh the newly formed 'Building Security Assessment Scheme'." "The scheme will enhance the safety and security of all building occupants, support the blue light services, and future-proof current and planned legislative changes." Demonstrate security commitments Richard Fogelman, NSI Chief Executive responded, “With over 50 years of experience in the security sector, we are honored to be chosen as CoLCPA’s trusted independent assessing body for the Building Security Assessment Scheme. Reviewing and enhancing the scheme has been a privilege, ensuring its relevance in today’s challenging environment." “We extend an invitation to commercial property owners and representatives in London to apply for the scheme to visibly demonstrate their security commitments and instill confidence their building security operations are dedicated to continual improvement.” Building Security Assessment Scheme certification We have demonstrated our commitment to keeping our tenants and the wider public safe" Peter Lavery, FSyI, Associate Director, EMEA Security & Operational Resilience Manager, Cushman, and Wakefield said, “Cushman & Wakefield is delighted to be amongst the first to have achieved this City of London Crime Prevention Association & National Security Inspectorate recognized ‘Building Security Assessment Scheme certification." "By submitting our building’s safety and security operation to a rigorous assessment process we have demonstrated our commitment to keeping our tenants and the wider public safe." Test, evaluate, and improve "Cushman & Wakefield is determined to continue to provide a safe and welcoming place for businesses, the public, and the local community and we are committed to working with the Police and our security partners to continuously test, evaluate and improve our processes." “We are especially proud that the assessment was facilitated by our Building Management team and Unitrust as one of our security partners, in the spirit of collaboration the award was ultimately achieved by a multi-disciplinary team, all of whom are committed to safety, security, and defeating crime.”
Expert commentary
Integrated security solutions are so often recommended by security specialists, while this sounds impressive, what does it actually mean? The short answer is: combining all aspects of security in a layered approach that leaves no vulnerable points. In this article, I will unpick the meaning behind this well used phrase, exploring the key components that make up an effective integrated security solution, while also revealing my top tips when it comes to maintenance and how to specify a solution that will provide real value for money. Integrated security solution When we think of integrated security, we tend to think it’s something that only applies to ultra-high security sites that are entirely inaccessible to the public. We generally picture towering fences topped with barbed wire, guard dogs and security patrols, glaring floodlights, deafening alarms, and warning signs. In actuality, the integrated security approach can be applied to any type of site that needs protecting In actuality, the integrated security approach can be applied to any type of site that needs protecting. This could be a high security data center or a water treatment plant that needs to be protected for public safety. It could also be a business park that requires open access during the day yet security at night, or even a school, where trespassing, truancy and theft of valuable equipment needs to be deterred, while welcoming environment is also necessary. Even residential properties require integrated security such as front and back garden fencing, CCTV, alarms, and security lights. The bread and butter To hone in on the ins and outs of an effective integrated security solution, it is helpful to follow the ‘5 Ds’ model of perimeter security. This covers the main components required to create a truly robust security strategy covering fencing and deterrents, surveillance and detection systems, access control, and personnel. Forming the first line of defense against unauthorized persons gaining access by freely walking onto, burrowing, climbing, or cutting through to the site is crucial but not the sole purpose of perimeter security. The type of perimeter security will also impact visitors’ first impressions of the premises, so while fencing and security toppings outlining a boundary act as a deterrent, they can also contribute to branding for the company by use of color or style, or if logos or other signs are fixed to it. This is especially important for schools, who want to create a secure but welcoming environment. Sensor-Triggered lighting Hostile Vehicle Mitigation (HVM) barriers should be deployed in the form of stand-off fencing Access control measures, such as gates, bollards, and rising arm traffic barriers, work best when used in conjunction with monitoring. Even on their own, they delay people from entering, however CCTV and other surveillance measures greatly improve their efficiency. Perimeter Intrusion Detection Systems (PIDS) are ideal for discreet monitoring and alert to any unwanted movement, and don’t underestimate the power of sensor-triggered lighting to deter trespassers. For sites with a threat of vehicle-borne attacks, Hostile Vehicle Mitigation (HVM) barriers should be deployed in the form of stand-off fencing around the main perimeter and barriers, bollards, and gates which restrict vehicle movement. Finally, nothing deters criminals more than the presence of other humans. Employing security patrols and access control staff will remove any sense of opportunity from intruders. Most appropriate protection A risk assessment will help site managers assess the most appropriate protection while also considering factors beyond security, including aesthetics, privacy, and noise reduction. The location of the premises will impact certain elements such as coatings. As a base standard, steel fencing must be hot dip galvanized or Galfan® zinc alloy coated to protect it from rust and corrosion. A risk assessment will help site managers assess the most appropriate protection To add color, polyester powder coating is the most durable, low maintenance option which does not chip or crack, Marine coating, is recommended for providing extra durability in coastal areas. If privacy is an important consideration for the site, opt for a solid fence type, however bear in mind this will hinder any line of sight and opens up spaces for intruders to hide behind, so assess the site’s needs accordingly. Tip top condition The maintenance of security measures is also an important element when considering an integrated approach, to check the system is working as it should be. Splitting a site into zones is a helpful way to map out where security is needed most and identify if there might be areas that require lower protection to prevent over-specifying. For example, higher-level security measures may be required in a zone that takes security staff longer to reach, to help deter or delay intruders as much as possible. Yet in clear lower-risk areas, it is possible to save budget by installing more frugal measures. Save vs splurge To get expert advice it is well worth taking advantage of free site consultations To get expert advice it is well worth taking advantage of free site consultations and counter terror initiatives where appropriate. Their input will help ensure the right, quality products are being specified where they should be, thus limiting the need to spend more money again in the future. If you’re still unsure, I would recommend testing temporary barriers on the site before installing permanent measures, this will help deduce what works and what doesn’t on the premises in question. However, if your risk assessment returned a ‘high risk’ result, it is best to not leave it months before implementing the final plan. Safety and security of buildings Finally, though it may seem counterintuitive, spending more upfront could help you save money overall - remember that quality fencing is going to serve you for a long time. It will need less maintenance and replacing, costing less in the long run. Budget is not an excuse for poor security which compromises the safety and security of buildings It is also worth checking the fencing specified comes with a long guarantee, this will ensure it is covered if defects arise as a result of manufacturing processes. Budget is not an excuse for poor security which compromises the safety and security of buildings, people and assets, particularly in the public realm. Instead, focus on getting it right from the very beginning, rather than risk having to spend the money twice. Full risk assessment There is no single solution when it comes to securing a site. Every situation must be considered individually, starting with a full risk assessment. We recommend an integrated approach to property security wherever appropriate. Along with a secure perimeter, this might also include effective lighting in shaded areas and at doors, gates, and shop windows, Perimeter Intrusion Detection Systems (PIDS), and well-placed CCTV. These measures can hinder entry and escape, or increase the chance of discovery and detection. The key message to take away, is that as helpful as modern electronic technology is, in the event of a power failure or malfunction, a site is left vulnerable if this is the only protection you have. Combining electronic measures with traditional, physical security fencing and gates is the only way to have guaranteed protection 24/7.
In the era of the ‘Great Resignation’, it may seem counterintuitive to say that people will power business security in 2022. However, a convergence of challenges over the past few years has led to an undeniable trend in the security industry: With more technology comes the need for more people to monitor, analyze and leverage the data that technology produces. Always-on approach to security Since businesses were forced into lockdown two years ago, we’ve seen technology adoption accelerate at an unparalleled rate, as leaders navigate the new working world. In fact, according to survey data published in STANLEY Security’s 2022 Industry Trends Report, more than three in four businesses (78%) report rapidly adopting new technologies due to the pandemic. Cloud security technology is among the tech that has experienced high rates of adoption; 91% of businesses report that they have implemented cloud security technology – such as cloud video surveillance and cloud access control – and nearly half (48%) say that this was due to the pandemic. Importance of remote security solutions Many businesses learned that remote security solutions have become a necessity To gain greater oversight and visibility into their security operations, many businesses learned that remote security solutions have become a necessity, in order to help protect their people, property, and assets, especially when their facilities aren’t fully occupied. However, an ‘always-on’ approach to security isn’t just about implementing cloud technology, artificial intelligence (AI), machine learning, and the like. Security still remains a question of people, particularly when it comes to creating a healthier, safer, and more efficient environment for businesses. Making sense of the data With an influx of data coming from various security systems and sources, businesses have a clear opportunity to appoint an expert, in order to oversee these new technologies. Many businesses already recognize the value in doing so: 65% expect to hire a leader this year to oversee new technologies they implemented, as a result of the COVID-19 pandemic. Over the next five years, more than one-third of businesses (38%) expect to hire a senior leader, in order to oversee security, data, and privacy. Identifying emerging training needs Such a leader would play an integral part in helping businesses to unlock the wealth of insights currently stored within their security infrastructure. For example, the data stored in security systems could inform talent management – identifying emerging training needs and ultimately, resulting in improved employee satisfaction and reduced attrition. In the retail sector, executives can extract data on footfall from CCTV and sensors In the retail sector, executives can extract data on footfall from CCTV and sensors, and directly correlate that to sales volume and value – thereby building a picture of how external factors impact revenues. This can be used to formulate predictions on consumer behaviors, promotions, and other sales activity. As we look to the future of the workplace and how organizations are using security systems to drive health, safety, and efficiencies – having an executive who is dedicated to this area will be critical in driving business growth and resilience. Doing more with less Around the world employees are quitting their jobs at a record pace, creating what has been dubbed the Great Resignation. In the United Kingdom, people are resigning at the highest rate in over a decade. In the United States of America, more than a fifth of the total workforce has left their positions, since April 2021. As businesses struggle to retain and recruit staff, they are looking for ways to overcome the labor shortage and optimize their operations, without compromising health, safety, and security. While leveraging technology and automation is certainly part of the solution, many are also turning to partners to support certain business functions, including security. Monitored security services Monitored security services, for example, allow businesses to gain 360-degree visibility into on-site operations, without hiring any new personnel. Instead, by partnering with a security provider that offers monitored security services, businesses have access to a professional team around the clock, in order to help spot potential threats, reduce risks, and increase efficiencies on-site. With monitored security, businesses can leverage the support of a whole team of security professionals With monitored security, businesses can leverage the support of a whole team of security professionals, working 24 hours a day, 365 days a year, regardless of the number of facilities they operate, their occupancy levels, or hours of operation. As businesses have increasingly limited resources, including time and labor, professional monitored security services can help them do more with less. Building business resilience Ultimately, a strong business security program is powered by people. Beyond technological progress, organizations need accountable experts to actively monitor their operations, make the call when there’s a threat, and unlock the invaluable insights stored within security systems. People, not technology alone, can build business resilience, by leveraging technologies and the data they produce, so as to create safer, healthier, and more efficient environments.
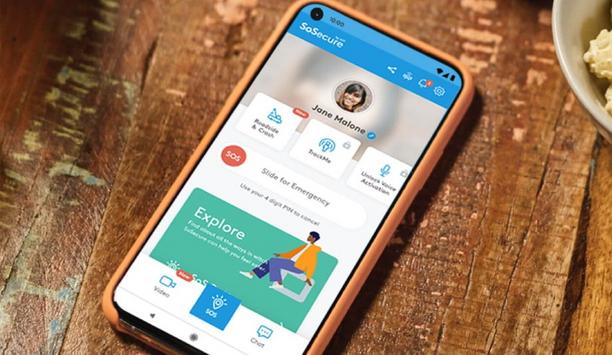
The past year has elevated consumer awareness about personal safety, from COVID-19 issues to social unrest, making safety top-of-mind and the need for personal safety solutions, even more prevalent. In addition, consumers spent more time at home, as schools closed, events were canceled and remote work increased. This prompted two major shifts that, in my opinion, most significantly opened the need for and raised the popularity of mobile safety solutions. Demand for grocery and food delivery apps surged Rise in use of app-based delivery services During the past 18 months, the use of app-based delivery services has skyrocketed During the past 18 months, the use of app-based delivery services has skyrocketed. With more use comes more interactions among strangers in homes and businesses, and while the majority of these moments are completely safe and convenient, incidents are happening, ranging from uncomfortable situations to physical assaults. And, with more delivery drivers on the road, there are going to be more accidents among gig-economy workers. Based on recent estimates, food and grocery delivery are expected to remain popular, even as we get back to normal life. High popularity of mobile security apps and wearables With more work shifting from stationary locations to working on-the-go, mobile security apps or wearables can be a lifeline in all sorts of situations. It’s important for these mobile safety products to be comprehensive, dynamic and designed to address the full range of people’s safety and security needs, from providing simple human reassurance to dispatching emergency help. Domestic violence cases increased According to the National Domestic Violence Hotline, due to COVID-19 lockdown restrictions, domestic violence rose as a result of many victims being stuck at home with their abusers, while sheltering in place and working from home. Mobile safety apps, such as ADT’s SoSecure U.S. Attorneys General and other state-elected officials have endorsed mobile safety apps, like SoSecure by ADT These situations necessitate the need for discreet ways for victims to call for help. U.S. Attorneys General and other state-elected officials have endorsed mobile safety apps, like SoSecure by ADT, as a tool to help victims of domestic abuse, safely call for help, without alerting their abuser. Over the past year, the mobile safety app market has seen tremendous innovation, including more user-friendly ways to make SOS calls. Today, within a single app, a person can summon help hands-free, by saying a secret phrase, by text or by swiping a button. Extension of mobile safety into wearable devices And, users can connect with people trained to help in unsettling situations over video, which can be an effective deterrent and provide video evidence. We’ve also seen the extension of mobile safety into wearable devices, in order to make these devices more discreet and usable. There will always be some safety risks in our lives. However, the good news is there’s no need to live in a constant state of fear. The easiest, most direct way to be prepared and ready to ‘fight back’ is by having a personal safety tool in your pocket, a mobile safety app that is there, when you need it most.
Security beat
Technology is driving new opportunities in the security industry. Innovation trends include artificial intelligence (AI), edge-based systems, mobile systems, a greater focus on software, and efforts to simplify operation of security systems, even as capabilities become more complex. ISC West 2022 reflected these changing trends. “In addition to emphasizing technology innovation, ISC West also reflected an industry that is resilient, dedicated and passionate,” said Mary Beth Shaughnessy, the Event Director of ISC Security Events. ISC West 2022 “Almost 12,000 dealers, installers, integrators, end users and consultants reconnected at ISC West 2022, and there were nearly 20,000 total industry professionals in attendance (including manufacturers),” adds Mary Beth Shaughnessy. The 550 exhibitors and brands on display reflected an industry that has come through the COVID-19 pandemic in better shape than ever, poised for even greater success in the years ahead. Turning video and access control into knowledge Deployment of AI to ‘watch video’ can inform users of what’s happening in real-time Motorola Solutions emphasized several themes that were heard repeatedly throughout the show. “One trend is fulfilling the need to turn video and access control into sources of knowledge, inside the enterprise,” said John Kedzierzski, Motorola Solutions’ Senior Vice President of Video Security and Access Control. Deployment of AI to ‘watch video’ can inform users of what’s happening in real-time, while monitoring access control yields the equivalent of an operating system inside a building. Using the Cloud offers consumer ease-of-use to systems The second trend listed by Motorola Solutions is working to bring the consumer ease-of-use experience into enterprise security solution applications. Professional security systems were previously complicated to buy, install, manage and upgrade. However, using the Cloud, even distributed enterprises can bring consumer ease-of-use to systems, from improving the out-of-box installation experience to boosting the ability to manage the system. Transition to ‘mobile first’ interfaces The third trend emphasized by Motorola Solutions is transition to ‘mobile first’ interfaces, reflecting the need for busy security executives to be on-the-go, but with full access to their systems, without being chained to their desks. Since the last springtime ISC West show in 2019, Motorola Solutions has grown rapidly, both organically and through acquisition of IndigoVision, Pelco, Openpath, Envysion, and Ava Security. Cloud-based Orchestrate system Integration is simple through a ‘drag-and-drop’ approach that doesn’t involve writing code In addition, the company is making it easier to integrate video and access control systems with Motorola’s radio systems, typically carried by security guards. The cloud-based Orchestrate system translates ‘events’ from access control and video, to trigger notifications on a mobile radio. Integration is simple through a ‘drag-and-drop’ approach that doesn’t involve writing code. Simplifying implementation of AI Artificial Intelligence (AI) has traditionally been associated with the use of large servers or even intelligence in the Cloud. Several exhibitors at ISC West helped to change that misconception. For example, Oosto offers a simpler and more economical approach. They supply edge appliances for AI. The purpose-built Vision AI appliance, a small box, puts intelligence at the ‘near edge’, by connecting to up to five cameras. Easy and dependable ‘failover’ ensures redundancy without a big investment, and the system can work with any IP camera, including an end user’s installed base of cameras. Oosto’s TCO (total cost of ownership) calculator Oosto’s TCO (total cost of ownership) calculator spells out how much a customer can save versus using a big server, including lower costs such and power and cooling. AI was probably the biggest buzzword at ISC West, but there was also emphasis on the practical results of applying AI to physical security. Artificial Intelligence (AI) - the biggest buzzword at ISC West I believe our purpose is to bring buzzwords, like Cloud and AI together in a way that is useful to end-users" “What surprises me (at the show) is that there is a lot of generic marketing of AI, but we are trying to step back from our analytics and look at applications that serve certain end-users,” said Jeff Corrall, Vice President - Product Management at March Networks, adding “As an industry, we are still at the stage of AI as a buzzword.” Jeff Corrall further said, “I believe our purpose is to bring buzzwords, like Cloud and AI together in a way that is useful to end-users. We have to live with the buzzwords, but what we really want is to apply them. That creates a stickiness with the end-user — when high technology is making a difference.” March Networks Labs address specific end-user problems and then apply their systems to provide a solution. Jeff Corrall adds, “A lot of AI is responding to what the customer is asking for, and we are stepping back and making sure the end-user will use it on a consistent basis.” ‘Edge versus cloud’ was a common theme at ISC West Edge versus Cloud ‘Edge versus cloud’ was a common theme at ISC West, pondering where in a system the ‘intelligence’, such as AI and machine learning, as well as other functionality, should reside. Among the companies addressing the quandary was Axis Communications, which focused on the issue using a racing theme at their presentation to the industry press. The winner of the ‘race?’ - The combination of both approaches working together as a team, of course. AXIS Speed Monitor on exhibit One introduction at the show was the AXIS Speed Monitor, a speed detection app available using ACAP Axis Communications also highlighted the deep learning analytics of the ARPEC 8 camera chip (introduced during the COVID-19 pandemic), which will be deployed across their camera line. One introduction at the show was the AXIS Speed Monitor, a speed detection app available using ACAP (Axis Camera Application Platform), the capability to load ‘apps’ onto camera chips at the edge. They also introduced the D4100-E Network strobe siren (a smart edge device), the Audio Manager Pro (a cloud-based software system enabling zoning and callouts for specific areas in a building), the W101 body worn cameras with GPS capabilities, and a Barcode Reader for doorstop applications (another ACAP app). ‘App Store’ approach to expanding applications Azena is at the center of expanding applications at the edge, promoting new applications through an ‘App Store’ approach that sells software apps that can be loaded onto cameras that are equipped with Azena’s operating system. In the last couple of years, the company (formerly known as Security and Safety Things) has expanded its offerings. There are currently 108 apps in the store from 30 to 40 app developers. There are 14 camera models (from six manufacturers) that are commercially available and run their operating system. The newest camera is a fisheye model from Vivotek. “What we have seen is that a lot of the use cases are pretty unique,” said Fabio Marti, Vice President - Marketing for Azena. Two examples are an application that monitors a flame to ensure it is burning cleanly (no smoke). Another system monitors nets covering fish farms to avoid birds getting tangled up in the nets. Fabio Marti said “A challenge is to find new business avenues for integrators. Everybody is not eager to look beyond their comfort zone.” Focusing on software to ensure user experience Software systems are one of the major focal points for innovation in security systems Software systems are one of the major focal points for innovation in security systems and Verkada is focusing on how software innovation can improve systems. “For decades, innovation was on the hardware front,” said Filip Kaliszan, Verkada’s Founder and Chief Executive Officer (CEO), adding “We saw an opportunity for more innovation on the software side. The customer experience revolves around software.” Ensuring an end-to-end experience “We want to guarantee an end-to-end experience,” adds Filip Kaliszan. As a new company with a ‘hybrid cloud’ approach, Verkada focused on appealing to end users to convince them of the value proposition. Once an end user was convinced, Verkada brought in an integrator partner to deliver the solution. In effect, Verkada finds demand and brings that demand to the integrator. Software-centric operation of a modern building Verkada is broadly focused on ‘software-centric operation of a modern building.’ After starting out in video, Verkada has since expanded into systems for access control, alarm systems, and other categories. They use a combination of third-party hardware and equipment that is custom designed to work seamlessly with their software systems. Verkada’s end goal is to put the various systems together into a platform. They will continue building each product category, which will eventually be unified into ‘the operating system for the building of the future.’
Security’s intersection with consumer electronics is on view at CES 2020, the world’s largest technology event, Jan. 7-10 in Las Vegas. The giant show features more than 170,000 attendees, 4,500 exhibitors and 1,100 industry thought-leaders featured on the CES stage. A range of technologies will be on display, from artificial intelligence (AI) to 5G, vehicle technology to AR/VR (augmented and virtual reality), robotics to home automation. Security plays a prominent role, too.The impact of this event for the smart home could be about delivering home analytics and enhancing privacy" Smart home market on the forefront The smart home market is a major focus. “For the smart home market at CES this year, we expect to see numerous announcements regarding home awareness,” says Blake Kozak, Senior Principal Analyst at IHS Markit. “This will include brands offering up additional analytics for consumer security cameras with a focus on edge-based solutions.” “The impact of this [event] for the smart home could be about delivering home analytics and enhancing privacy through cloudless architectures and new electronic door lock approaches,” he adds. An example of cloud analytics is the Resideo Home app, introduced in December, which will make whole-home monitoring possible for four critical networks of the home – water, air, energy and security. Resideo promises a “simplified and integrated smart home experience.” Video is also prominent at the show. “For cameras, we can expect to see more cameras focused on the outdoor space and possibly new form factors for video doorbells,” says Kozak. Familiar security industry brands exhibiting at CES 2020 include ADT, Ring, August Home and Yale (both part of ASSA ABLOY), Bosch and Alarm.com. Focus on Cybersecurity In 2020, companies will continue to focus on solutions for protecting consumer data" Cybersecurity is an aspect of many of the devices on display at CES. “Device security and data privacy play a key role in the adoption of connected devices,” says Elizabeth Parks, President, Parks Associates. “Consumer security concerns for smart home products will continue to be a barrier to adoption in the U.S. and Europe, and these concerns can actually intensify with device adoption-71% of U.S. smart home households are concerned about cybersecurity. In 2020, companies will continue to focus on solutions for protecting consumer data. One big area of interest is protection on the network router, providing whole home solutions, which are very appealing to consumers.” “At CES we will see the traditional players introducing new DIY (do-it-yourself) products, as well as new players announcing new product features, services, and partnerships,” Parks adds. Smart access control Smart locks will be among the security products at CES 2020. For example, PassiveBolt, a lock company, will show the Shepherd Lock, a touch-enabled smart lock with enhanced security through sensors and AI. The add-on lock converts existing locksets into touch-activated devices. Another lock manufacturer is Kwikset, whose door locks and door hardware include Wi-Fi-enabled smart locks, Bluetooth-enabled smart locks, keyless and keyway-less locks and connected home technology. Video doorbells, including industry-innovator Ring, have been a hit in the consumer market. At CES, Ring will expand the mission to make neighborhoods safer by creating a “Ring of Security” around homes and communities with a suite of home security products and services. The “Neighbors by Ring” app enables affordable, complete, proactive home and neighborhood security. Homeguard offers a range of affordable CCTV solutions for home and small business DIY CCTV demonstrations DIY security systems are another market. Homeguard is a leading DIY consumer brand offering a range of affordable CCTV solutions for home and small business, including wired and wireless CCTV kits, smart cameras, home alarm systems and wire-free HD CCTV kits. Swann Communications is also at the forefront of surveillance and monitoring with new products developments including wire-free HD cameras and doorbells, professional CCTV video surveillance systems, and 1080p full HD systems with “True Detect” heat and motion sensing. AVTECH, and subsidiary YesGo Tech, will demonstrate a compact Wi-Fi home security set, a series of special cameras with face recognition, thermal detection and license plate recognition, customized central management software and a university ID tag that is compatible with access control, OEM and ODM opportunities. Security and automation solutions D-Link’s home networking, security and automation solutions will help consumers connect, view, share, entertain, work and play. SECO-LARM, manufacturer of a Room Occupancy Monitor that shows whether a room is in use, has a line of keypads and proximity readers with built-in Bluetooth for convenient access. Another smart home security solutions provider, Climax Technology, integrates wireless security, home automation, energy management, home emergency monitoring and live visual monitoring. Personal safety mobile application Manufacturers are positioning outdoor cameras as deterrents to theft before a burglary happens" WaryMe designs and develops a personal safety mobile application to improve a user’s security in public places, schools, transports and companies by addressing major risks such as terrorism attacks, intrusion, fire and even industrial accidents. An all-in-one mobile application integrates alerting, crisis management and mass notification features. “Market players are looking to expand beyond established smart home devices like smart thermostats and networked cameras to products like smart water leak detectors, smart pet feeders, and smart air purifiers,” says Elizabeth Parks. “Manufacturers are positioning outdoor cameras as deterrents to theft before a burglary happens. This trend is part of a broader security marketing effort to extend the perimeter of home security beyond traditional home access points.” “Familiarity with smart home devices lags behind familiarity with smart entertainment products; it even lags that of smart speakers, which are quite new in the market,” adds Parks. “In 2020, we will see players working to advance the visibility and marketing around device integration, and specifically focus on use case scenarios around safety, security, and convenience, which have always been the primary drivers of adoption of these types of products.”
The UK Government has been working to reduce the risks associated with illegal drone use since a high-profile incident at UK’s Gatwick Airport in December 2018, when a drone sighting triggered a three-day shutdown of the UK’s second busiest airport, disrupting the travel plans of 140,000 people and affecting 1,000 flights. To address growing security threats by drones, the UK Government has released its ‘Counter-Unmanned Aircraft Strategy’. ‘Counter-Unmanned Aircraft Strategy’ This strategy sets out our approach to countering the threat the malicious or negligent use of drones can bring" “This strategy sets out our approach to countering the threat the malicious or negligent use of drones can bring,” says Brandon Lewis, the U.K. Minister of State for Security. “It will provide the security the public and drone users require to continue to enjoy the benefits of leisure and commercial drone use and facilitate the growth of the drone industry.” “Given the challenge posed by rapid advances in drone technology and the potential threat, the strategy will provide overarching direction to our efforts,” says Lewis. The strategy focuses on ‘small drones’, those weighing less than 20 kg (44 pounds). Countering malicious use of aerial drones The UK Counter-Unmanned Aircraft Strategy centers on mitigating the highest-harm domestic risks resulting from malicious use of aerial drones. They are: Facilitating terrorist attacks, such as modifying commercially-available drones to conduct reconnaissance or attacks. Facilitating crime, especially in prisons, where drones are currently used to deliver contraband. Disrupting critical national infrastructure, such as airports, where a malicious incursion using a drone can have serious safety, security and economic consequences. Potential use by hostile state actors. Maximizing benefits of drone technology The initiative will also look to build strong relationships with industry to ensure high security standards Over the next three years, the strategy will seek to reduce the risks posed by the highest-harm use of drones while maximizing the benefits of drone technology. It will develop a comprehensive understanding of evolving risks and take a “full spectrum” approach to deter, detect and disrupt the misuse of drones. The initiative will also look to build strong relationships with industry to ensure high security standards. Further, promoting access to counter-drone capabilities and effective legislation, training and guidance will empower the police and other operational responders. Tactical response to drone-based threats Because technology is rapidly evolving, the response needs to keep pace, according to the strategy document. Lewis adds, “We will therefore work to understand how drone-based threats might evolve in the future, both at the tactical and strategic levels.” The strategy will be to build an end-to-end approach to tackling the highest-harm criminal use of drones. It will also work to make it easier to identify malicious drone use against a backdrop of increased legitimate use. Legal drone operators will be required to register with the Civil Aviation Authority (CAA) and to pass an online competency test before flying a drone. Retailers who follow a specific set of safety guidelines when selling drones will be designated ‘DroneSafe’. Unmanned traffic management system The government is working toward future implementation of an unmanned traffic management (UTM) system, which provides a means of preventing collisions between unmanned aircraft and other manned or unmanned aircraft. The current strategy includes early planning for the system. An Industry Action Group will ensure a continuing relationship with the drone industry and help to improve existing counter-drone measures and identify new opportunities, such as use of ‘Geo-Fencing’ to restrict drones from flying in certain areas. Regulating commercial and domestic drones The UK Department of Transport is responsible for safe and lawful use of drones within the UK airspace The strategy will seek to communicate the UK’s security requirements to the counter-drone industry and to encourage a thriving sector that is aware of, and responsive to, the needs of government. Regulating drones is the responsibility of two UK government departments. The UK Department of Transport is responsible for safe and lawful use of drones within the UK airspace, while the Home Office has overall responsibility for domestic counter-drone activity. Fast-evolving drone and counter-drone technology Also, the Center for the Protection of National Infrastructure (CPNI) has been involved in reducing the vulnerability of sensitive sites, including airports. New performance measures will track the strategy’s success. Due to the fast-evolving nature of drone and counter-drone technology, the intent is to review and, if necessary, refresh the strategy in three years.
Case studies
Delta Scientific, the pioneering manufacturer of counter-terrorist vehicle control systems used globally, announced that on Monday, April 1st, a DSC501 High-Security Barricade stopped an unauthorized vehicle from entering an FBI field facility in Atlanta, Georgia. According to officials, the orange Buick Encore tried to follow an FBI employee’s car into the facility before being stopped by the Delta DSC501 barrier. The driver was then apprehended by special agents who were in the immediate area. Strength and reliability of Delta “Delta has a long history of thwarting attempts by unauthorized vehicles trying to enter facilities where they could potentially cause serious harm to civilians and structures,” states Greg Hamm, Delta Vice President of Sales and Marketing. “We are extremely proud to celebrate our 50th anniversary this year protecting the world’s most important institutions. The strength and reliability of Delta barriers is unrivaled.” FBI field office On June 27th, 2006, the DSC501 was tested to the most extreme parameters on record The DSC501’s protecting the FBI field office are the strongest in the world. On June 27th, 2006, the DSC501 was tested to the most extreme parameters on record. A 65,120-pound dump truck hit the DSC501 at 50mph and was stopped at the barrier. At the time of the test, this would have roughly equated to a K54 rating with the crash energy equaling 54,000,000 foot-pounds. ASTM M50 testing level How impressive is this? The current highest ASTM M50 testing level requires 12,500,000 foot-pounds of energy when impacting the barrier. This is a factor of over 4x which is extremely impressive considering the magnitude of the current M50 test. Contact Delta Scientific if they want to make sure the facility has the strongest, most reliable barriers on the market. They are celebrating 50 years in business in 2024.
Databuoy Corporation, a gunshot localization and real-time emergency alert intelligence system, and the Philadelphia Police Department announced that SHOTPOINT, Databuoy’s life-saving gunshot localization and detection system, has been selected by the Department for a pilot program to help to reduce gun violence throughout the city. With gun violence on the rise, officials sought a solution that could accurately detect a gunshot and localize where it came from, to prosecute more offenders and hopefully lessen the number of incidents. When public safety is at risk, having real-time systems that seamlessly communicate vital information is key for first responders. Databuoy's SHOTPOINT system Databuoy's SHOTPOINT system can be deployed in nearly any environment with near-perfect results. SHOTPOINT eliminates false positives, without human intervention, and provides accurate, quickly deployed reports to first responders. “Our system works reliably in high noise environments and around vehicular traffic without false detections,” Kathleen Griggs, Databuoy CEO said. “The system is automated and gets information to responding officers instantly and has supported police response and investigations for multiple homicides in the years we have been installed.” Game-changing technology SHOTPOINT is becoming more accessible to cities since it has been awarded MAS contract by GSA SHOTPOINT is a game-changing technology that is unsurpassed in its detection and location accuracy and one that law enforcement and security clients can trust. “We are deployed in some of the most volatile environments in the country, like the Fremont Street Experience in Las Vegas,” says former CBP Commissioner, David Aguilar, one of Databuoy Corporation’s Board of Advisor Members. “We are confident it will do the same for the City of Philadelphia.” SHOTPOINT is becoming more accessible to cities since it has been awarded a Multiple Award Schedule (MAS) contract by the General Services Administration (GSA) on a Service-Disabled Veteran-Owned Small Business (SDVOSB) contracting vehicle and is available on The Interlocal Purchasing System (TIPS) through a Minority Owned 8(a) Small Business. Pilot program “We are committed to the safety of our citizens,” Robert Keehfuss, Philadelphia Police Department, Public Safety Technology Program Manager said. “Philadelphia needs a system that will instantly give us the precise location where the shot occurred. Every second counts when it comes to saving lives and catching shooters, so the faster we get the detailed information, the better chance we have of protecting our citizens.” The pilot program between Databuoy and the Philadelphia Police Department will be ongoing for the next several months and cover one of the city’s heaviest gun violence areas. If the system performs to the goals outlined in the pilot, there is support for a larger rollout plan.
More than 2,000 innovative Safetyflex anti-terrorist bollards have now been installed in the heart of Melbourne, Australia, as part of a local government scheme launched in response to a fatal vehicle attack. Coventry-based Safetyflex Barriers has installed its spring steel bollard system across the Melbourne Central Business District (CBD) with the help of its Australian distributer, Ezi Security Systems. Most prominent pedestrian The city was rocked by a vehicle attack in January 2017 when a car was deliberately driven into pedestrians along Bourke Street, killing six people and leaving 27 seriously injured. In the aftermath, a AUS$52.5 million security upgrade at Melbourne's busiest and most prominent pedestrian sites was commissioned by The City of Melbourne, with hostile vehicle mitigation predominantly featuring Safetyflex’s advanced spring steel bollards. More than 2,000 of the slimline bollards have now been installed across key sites within the CBD, in addition to further sites in Australia, helping to keep high-risk crowded places safe from the threat of vehicle attacks. Anti-terrorist bollard system The unique thing about our bollards is they only require shallow foundations around 200mm deep" Marcus Gerrard, Director at Safetyflex Barriers, said: “Our patented anti-terrorist bollard system has been game-changing, providing unprecedented crash test certified performance in an attractive, slimline design. We are the only company in the world to use this type of technology in anti-terrorist bollards and crash rated street furniture.” He adds, “The unique thing about our bollards is they only require shallow foundations around 200mm deep, which is key in helping cities such as Melbourne navigate around in-ground obstructions, while still providing high-level security systems. The installation of the 2,000th spring steel bollard is of great satisfaction and pride, and reflects our strong experience and expertise in securing busy cities and centers worldwide. Our bollards will help ensure the safety of residents and visitors to Melbourne and Australia for years to come.” Stopping vehicle attacks The spring steel technology means the bollards can be installed in fixed, removable or retractable versions, while the elegant stainless-streel shrouds are also fitted with reflective bands to provide night-time visibility. The bollards have already proved their worth in stopping vehicle attacks, when in 2021 a stolen car fleeing police in Melbourne CBD was halted in its tracks by a Safetyflex bollard before the drivers could inflict any damage. Pedestrians were able to retreat to the protection offered by the line of Safetyflex bollards, ensuring nobody was hurt. Safetyflex has now become one of the biggest suppliers of anti-terrorist bollards in Australia, protecting high-profile locations in Brisbane, Melbourne and Sydney from the threat of vehicle attacks.
Cozaint Corp, the developers of intelligent surveillance solutions, has been selected by the Pascua Yaqui Tribe Police Department in Tucson, AZ, to deliver the BOBBY physical security tower to provide a “safe zone” location for local citizens to conduct sales transactions, custody transfers, or other dealing where a security monitored area would provide a safe setting. Cozaint’s BOBBY platform of physical security kiosk tower provides 24/7 situational awareness for organizations of all sizes with various IoT security sensors, constant video surveillance, and tied to a remote monitoring center. Cozaint BOBBY kiosk tower The Cozaint BOBBY kiosk tower also has a 27” interactive display that displays information about local tribal activities as well as allowing for visitors to activate a “panic button” if they feel threatened. The BOBBY “safe zone” tower is connected to the tribal police department where officers can see and speak with the user to determine if an emergency exists and how best to respond. “With certain transactions occurring between complete strangers —such as online sales— sometimes our community may wish to meet at a more secure location where video surveillance and the ability to reach one of our officers in an emergency is all in one safe zone,” said LT. Elizabeth Esparza of the Pascua Yaqui Police Department. BOBBY safe zone tower BOBBY safe zone tower delivers peace of mind to Pascua Yaqui Police Department and its citizens With 360-degree video surveillance coverage and 24/7 video recording, the BOBBY safe zone tower delivers the peace of mind that the Pascua Yaqui Police Department and its citizens are looking for to safely meet others with eBay or other sales transactions, when custody transfer events occur, or other interactions where a safe and monitored location is preferred. “Our BOBBY tower unit is an ideal community safe zone security platform, where users can rest assured that they are being monitored for safety and security reasons when dealing with various transactions with others in the community,” stated Jay Jason Bartlett, CEO, Cozaint, adding “Interacting with the Pascua Yaqui Police team in the event of an emergency provides an additional level of security for the local community.” BOBBY tower unit The BOBBY tower unit also displays local community information as well as current events, helping to keep the community up to date on what is happening throughout the tribe. This particular BOBBY tower unit is located on tribal land in the desert of Tucson, AZ, where the summer rains and high temperatures create harsh operational conditions for an outside device such as this.
Round table discussion
The death of Michael Brown at the hands of police in Ferguson, Missouri, in August 2014, highlighted to the public, the importance of body-worn cameras. There was no bodycam footage of the Ferguson tragedy. Arguably, it would have shed additional light on the shooting. Since then, body cameras have become a tangible legacy of Ferguson, Missouri. Bodycam footage is seen as providing greater accountability and ensuring an impartial record that can support, or debunk, any claims of police misconduct. Body-worn cameras are also finding their way into broader usage, even including customer service applications. We asked this week’s Expert Panel Roundtable: How important will body-worn cameras be moving forward?
A new generation of security professional is waiting in the wings. They will be faced with unprecedented challenges, as they seek to transform the security marketplace to the ‘next level’. Technology changes ensure the market will be very different 10 years from now and the fresh labor pool will need to be able to meet the host of new challenges. We asked our Expert Panel Roundtable: What exciting career opportunities in the security industry await the next generation?
Many of us take critical infrastructure for granted in our everyday lives. We turn on a tap, flip a switch, push a button, and water, light, and heat are all readily available. But it is important to remember that computerized systems manage critical infrastructure facilities, making them vulnerable to cyber-attacks. The recent ransomware attack on the Colonial Pipeline is an example of the new types of threats. In addition, any number of physical attacks is also possibilities. We asked this week’s Expert Panel Roundtable: What are the security challenges of protecting critical infrastructure?