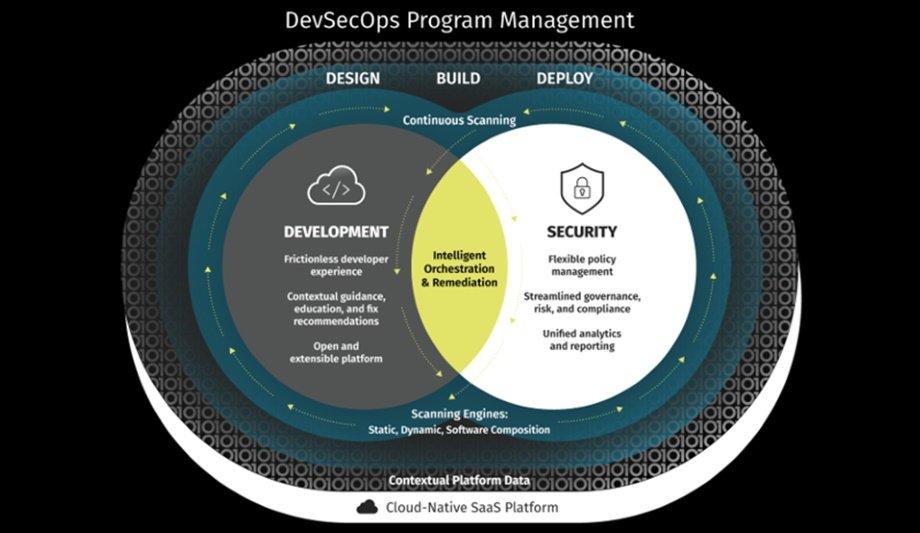
Veracode, a globally renowned provider of Application Security Testing (AST) solutions, has announced its Continuous Software Security Platform, which seamlessly embeds application security into the Software Development Lifecycle (SDLC).
The platform streamlines workflows by bringing together development and security teams, in order to provide a broad understanding of risk, remediation guidance, and progress at every stage of the development process.
Leveraging multiple methods to assess software
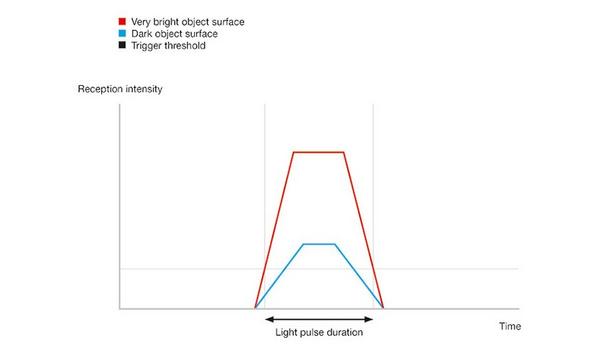
According to Veracode’s latest research, there has been a 20x increase in average scan cadence, over the past decade
According to Veracode’s latest research, there has been a 20x increase in average scan cadence, over the past decade, with most applications tested three times per week, as opposed to three times per year, a decade ago.
The research also showed a 31 percent increase in organizations using multiple scan types, over the last three years alone. Currently, major organizations all over the world recognize the need to leverage multiple methods to assess their software and do so across all stages of the development lifecycle.
Pervasive but not invasive for developers
Gartner predicts that by 2025, 70% of organizations will consolidate the number of vendors securing the lifecycle of cloud-native applications to a maximum of three vendors.
This suggests companies are already looking for a comprehensive platform that provides flexible policy management, a holistic assessment of software risk, and integrated remediation guidance while simplifying the complexity of managing multiple solutions.
With increased pressure to build and deploy software at breakneck speed, development teams require security checks to be seamlessly integrated into the tools where they work so they can find and fix vulnerabilities quickly. Meanwhile, security teams must meet increasingly stringent compliance standards defined by their boards and regulatory bodies.
Continuous Software Security Platform
Veracode’s Continuous Software Security Platform is pervasive but not invasive
Veracode’s Continuous Software Security Platform is pervasive but not invasive, because it provides a frictionless experience for developers, by embedding vulnerability analysis with remediation guidance directly into the integrated development environment.
Brian Roche, the Chief Product Officer (CPO) at Veracode, said, “Other vendors in our space have incomplete or disjointed solutions that lack consistent reporting and analysis, leaving customers playing a game of ‘whack a mole’ across different tools.”
Holistic view of the company’s software security posture
He adds, “We have continued to evolve our platform to create a seamless and integrated experience for developers, as well as provide security teams with a holistic view of their software security posture from design, through development and deployment. We see this as a win for both development and security teams that will result in the delivery of software that is more secure.”
The Veracode Continuous Software Security Platform enables users to define and manage security policy, gain a comprehensive view of software security across their application portfolio, and leverage rich analytics to make informed plans, communicate metrics, comply with policy, and meet regulatory requirements.
Detect, predict, manage and mitigate security risks
Powered by almost two decades of data, the platform enables organizations to detect, predict, manage, and, ultimately, mitigate their security risk. These intelligent capabilities empower companies to deliver secure code at the speed and scale, which is expected in the modern world.
The new Veracode Continuous Software Security Platform release features several new capabilities including:
- Single-Pane-of-Glass Reporting: Security teams can now access unified reporting directly in the portal for Static Analysis, Dynamic Analysis, Software Composition Analysis, and Manual Penetration Testing. Administrators and developers now have a consolidated view into security risks, as well as flexible policy controls, through stronger license management reports, in order to address issues quickly.
- Self-Service Peer Benchmarking: With comprehensive data and anonymized insights provided across all platform users, customers now have direct access to reports on the portal, which enables them to easily benchmark their DevSecOps program results against others in their industry. Tapping into many years of data and learning, customers can see how their program metrics stack up and establish plans, in order to address their risk.
- Software Bill of Materials (SBOM): Security teams can now generate and export Software Bill of Materials (SBOMs) on demand, with an integrated representational state transfer (REST) API. This returns data for a specific application in CycloneDX SBOM format, which is a standard designed for use in application security contexts and supply chain component analysis. Additionally, data from the API can be mined and transformed outside of the Veracode Platform as well.
- Intelligent Remediation: The Continuous Software Security Platform will leverage technology acquired from Jaroona, in order to detect and remediate software vulnerabilities through machine learning (ML). Jaroona, which was recognized by Gartner Research as a ‘Cool Vendor’ in 2021, outperforms traditional approaches by 7 times to 10 times, in terms of accuracy, false negatives, and false positive rates, and reduces the burden on technical resources.
Ensured security of products and services
According to Tabrez Naqvi, the Director of Information Security and Risk at Cox Automotive Inc., “The security of our products and services is very important to us, and Veracode helps us ensure that we never lose our customers' trust and confidence.”
Veracode is a major AppSec partner for creating secure software, reducing the risk of a security breach, and increasing security and development teams’ productivity. As a result, companies using Veracode’s platform can move their business, and the world, forward.
With its combination of process automation, integrations, speed, and responsiveness, Veracode helps companies get accurate and reliable results so that they can focus their efforts on fixing and not just finding potential vulnerabilities.
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems