Richard Suls, Security & Risk Management Consultant, WithSecure, “As a security researcher focused on cybersecurity and the protection of sensitive data, I believe that the SEC's decision to require publicly traded companies to disclose cyber attacks within 4 days of identifying a "material" impact on their finances is a significant step in the right direction. This rule change represents a major shift in how cyber breaches are handled and disclosed, and it has several potential benefits for both investors and the overall security landscape."
"Firstly, the mandatory disclosure of cyber attacks within a specific timeframe will enhance transparency and accountability. By imposing a strict deadline, companies cannot delay or obscure information about cyber incidents, ensuring that investors and stakeholders are promptly informed of potential financial implications resulting from breaches. This will help in preventing the manipulation of financial data and the withholding of crucial information that could impact investors' decisions."
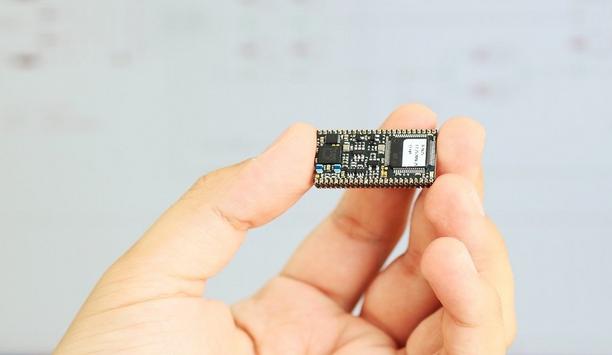
Resources in cybersecurity
New rule act as a strong incentive for companies to invest more resources in cybersecurity"
Richard Suls adds, "Secondly, the new rule can act as a strong incentive for companies to invest more resources in cybersecurity measures and incident response capabilities. When faced with the prospect of publicizing a cyber attack and its financial impact, companies are likely to prioritize cybersecurity as a core aspect of their business strategy. This could lead to increased spending on advanced security technologies, threat intelligence, employee training, and proactive risk assessments, ultimately strengthening the overall resilience of the corporate sector against cyber threats."
"Moreover, the requirement to disclose "material" impacts can lead to a better understanding of the true financial consequences of cyber attacks. By sharing this information, companies can learn from each other's experiences, facilitating the development of industry-wide best practices in incident response and mitigation. This collaborative approach can lead to a more robust and adaptive security landscape, making it harder for threat actors to exploit common vulnerabilities across multiple organizations."
Culture of Proactive Cybersecurity
Richard Suls adds, "However, it's important to acknowledge that implementing this rule will also pose challenges to companies. Four days may not always be sufficient to fully understand the scope and impact of a sophisticated cyber-attack. There might be cases where companies require more time to conduct thorough investigations and accurately assess the financial repercussions. To address this concern, the SEC should consider providing guidelines on what initial information needs to be disclosed within the 4-day period, while allowing companies to provide updates and supplementary details as they become available."
"In conclusion, the SEC's decision to enforce prompt and transparent disclosure of cyber attacks is a commendable effort to bolster cybersecurity practices and safeguard the interests of investors. By embracing this new rule, companies will be compelled to take cyber threats more seriously and prioritize the protection of their sensitive data and financial assets. As security researchers, we welcome this initiative and hope that it will foster a culture of proactive cybersecurity and information sharing within the corporate landscape.”
SEC obligations
Companies that have been breached would do well to focus first on showing a duty of care
Paul Brucciani, Cyber Security Advisor, WithSecure, “Companies that have been breached would do well to focus first on showing a duty of care to their customers rather than the SEC. Class actions and a tattered reputation could be more damaging than a fine."
"General counsels should advise their colleagues that a breach is not always a breach - calling a security incident a “data breach” will not trigger SEC obligations. Until you are certain a breach has taken place, refer to it as an incident. Consider also using two investigation teams: one commissioned by external counsel to conduct a forensic investigation under legal privilege to educate the external counsel about aspects of the breach so that counsel can provide informed legal advice to its client; and if necessary, a second team to support the incident response team in investigating and fixing the data breach."
SEC’s quest
Given the SEC’s quest for transparency, executive directors who manage cyber risk should ponder the following advice:
1. Favor discretion over rules: Cyber security based on compliance to rules or standards may make it easier to get through client audits, but it may not make you secure. Standards take many years to agree and implement, by which the cyber threat has moved on, and they reflect the minimum capability that standard-setters consider to be generally appropriate, rather than an aspirational capability. Independently scrutinize standards set by consensus and create a logical, defensible cyber risk strategy, specific and appropriate to your organization.
2. Have ‘skin in the game’: Make those responsible for managing risk define the cyber risk management strategy: avoid the mistakes made by financial sector regulators, for example, allowing banks’ capital requirements to be set by the rating agencies. Not only are rating agencies not responsible for managing banking risk, but they are also susceptible to market pressure. It is they who set disastrously low-risk ratings to new and lethal financial products like collateralized debt obligations which caused the 2007 financial crisis. Execs need to have ‘skin in the game’.
3. Adopt a barbell security strategy: a combination of high and low-risk management strategies, avoiding the middle ground. Protect the maximum extent possible IT systems that host your critical data and if necessary, take more risk with the rest of your network by focusing on resilience rather than security.
4. Rehearse what you would do when a security incident happens: periodic testing of your security incident response fitness effectively vaccinates your business against a breach. Train your incident response team to control the language they use when they communicate as it could be used in court as evidence. The most resilient companies are those that have learned how to operate without internet access or even without IT. Make provisions for re-building your IT from scratch.”
Discover how AI, biometrics, and analytics are transforming casino security