OTORIO, the provider of operational technology (OT) cyber and digital risk management solutions, announced research pointing to wireless IIoT vulnerabilities that provide a direct path to internal OT networks, enabling hackers to bypass the common protection layers in the environments.
OTORIO Senior Researcher - Roni Gavrilov will present key findings and how organizations can overcome these issues at S4 2023.
Research finding
OTORIO’s comprehensive research into industrial wireless IoT devices and technologies has revealed a significant issue involving the implementation of “secure” remote access to critical infrastructure.
Because wireless IIoT is commonly connected both to the internet and the internal OT network, it poses a serious risk to OT environments.
Target devices
Industrial Wi-Fi access points and cellular gateways are the ideal targets for hackers to cause the most damage to facilities
The research demonstrates how local attackers can compromise industrial Wi-Fi access points and cellular gateways by targeting the Wi-Fi/cellular channels on-site, exposing devices to Man-in-the-middle (MITM) attacks, internal services, and even directly accessing Purdue Model Level 0 devices.
These devices are the ideal target for hackers who want to crash physical machinery and cause the most damage to production and facilities.
Risk of wireless IIoT
Attackers can leverage free and publicly available platforms such as WiGLE™ to identify a target, find its location and vulnerabilities, and exploit it successfully. “Wireless IIoT cloud platforms, in their current state, present a critical attack surface for industrial remote sites,” said Roni Gavrilov.
He adds, “We have found over 30 vulnerabilities in these IIoT devices, including a chain of vulnerabilities that could give an attacker direct access from the internet to thousands of internal OT networks.”
Wireless IIoT device breach
Wireless IIoT device breach could enable hackers to simultaneously bypass every layer of the Purdue Model
The Purdue Enterprise Reference Architecture Model provides a framework for OT security personnel on how to segment, and thereby protect, their networks.
However, OTORIO found that a wireless IIoT device breach could enable hackers to simultaneously bypass every layer defined by this model, including intelligent devices as well as control, manufacturing operations, and business logistics systems.
Disclosed vulnerabilities
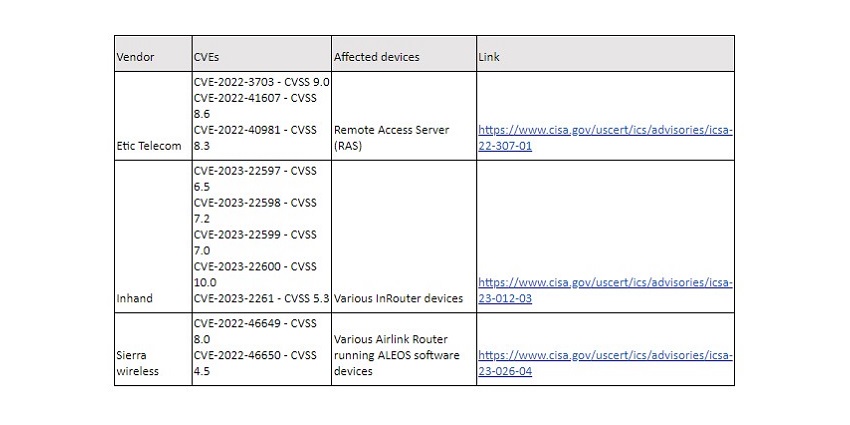
Through the research, multiple vulnerabilities were found across several different vendors, in both cloud management platforms and on-edge devices, some are still under responsible disclosure, the following table summarizes the disclosed vulnerabilities at the time of writing:
Having both cloud management and wireless connectivity increases the potential attack surface dramatically. What’s more, these devices directly connect to the lower levels of the Purdue model (L2 to L0), an attacker’s ideal entry point to OT networks.
Recommendations
To combat these threats, OTORIO recommends several architectural adjustments, including:
- Establishing a zero trust policy between cells and the L3 (control center) ensures that if an attacker compromises a single cell, they won’t be able to reach other cells or unnecessary services in the L3.
- Applying a whitelist-based communication template monitored by the FW/IPS between L3 and the cells. The communication template will guarantee that only allowed traffic is sent from the cells to the L3.
- Creating a proxy address for internet-managed devices (industrial cellular gateways, intelligent field devices, etc.). Traffic will be sent to the Proxy functionality, which will perform MITM on the data to detect any malicious behavior.
OTORIO is a Prime sponsor at S4 2023. To learn more about the findings, visit them in the “Moon” room on the third floor.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance










