Johnson Controls, the globally renowned company in smart, healthy and sustainable building solutions, has launched Tyco Software House iSTAR Ultra G2, a next generation door controller, which is designed for cyber resiliency, providing customers with faster processing power, advanced enterprise functionality and the building blocks needed for future expansion.
iSTAR Ultra G2 door controller
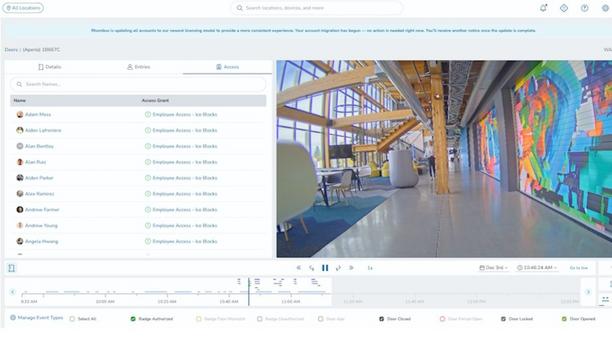
Ideal for mid-size to large scale deployments in higher education, healthcare, government, data center, industrial and manufacturing facilities, the iSTAR Ultra G2 is a highly flexible door controller, supporting both wired and wireless locksets, with expanded memory capacity, to ensure the device grows with customer needs. It can manage up to one million credentials, for up to 32 doors.
Advanced enterprise features such as dual GigE network ports using TLS 1.3 network authentication and cluster-based anti-passback provide the power to handle the most demanding access control applications.
Advanced hardware-based cyber security protection
Its advanced hardware-based cyber security protection using Trusted Execution Environment (TEE) means that the iSTAR Ultra G2 assures confidentiality of code and data, to help combat the most sophisticated hackers. The TEE guards against cyber-attacks, while the OSDP Secure Channel communication standard provides encrypted two-way communication between devices, including readers and controllers.
The addition of the iSTAR Ultra G2 expands our portfolio of door controllers"
“The addition of the iSTAR Ultra G2 expands our portfolio of door controllers, to include one of the most expandable solutions, available in the market,” said Rick Focke, the Director of Product Management, Enterprise Access Control, Security Products at Johnson Controls.
Rick Focke adds, “This device is an important solution for customers who need a highly scalable and cyber-resilient solution that serves as the heart of the access control system, connecting readers, sensors, software and locking devices.”
Onboard Public Key Infrastructure authentication services
Onboard Public Key Infrastructure (PKI) authentication services mean that the iSTAR Ultra G2 door controller is a self-contained, high-assurance solution and does not require third-party devices for authentication, thereby saving money and installation time. Global and peer-to-peer anti-passback technology prevent consecutive entries from single access control cards, to keep multiple people from using the same credential.
iSTAR Ultra door controller has been built using the Johnson Controls’ ISASecure certified development process, in accordance with the ISA/IEC 62443 control systems security standard and includes a back-up communication path, in the event of a primary network failure, so as to eliminate system downtime. Additionally, iSTAR Ultra G2 uses the same form factor as other iSTAR door controllers, so it fits easily into existing control panel boxes.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance