Cymulate, the industry standard for SaaS-based Continuous Security Validation, has announced the launch of two new solutions, to enable businesses to validate their security technologies and policies.
Attack Surface Management (ASM) discovers exploitable external assets, and Vulnerability Prioritization Technology (VPT) that integrates with vulnerability scanners, to reduce risk exposure time on internal assets. These new offerings empower security teams, to efficiently prioritize vulnerabilities and mitigation steps, ensuring a shorter time to remediation.
Common Vulnerabilities and Exposures (CVEs)
With the exponential increase in Common Vulnerabilities and Exposures (CVEs), organizations are in a constant race to discover, prioritize and remediate vulnerable assets. Current vulnerability management platforms do not take into account the effectiveness of compensating controls and their ability to detect and/or prevent the exploits, associated with the discovered vulnerabilities.
They end up using uncontextualized vulnerabilities and information that leads to inaccurate prioritization, which wastes time trying to push patches that do not always address the problem.
Enhancing vulnerability management
In order to simulate a full-scale attack, a company needs to go back to the reconnaissance stage
In order to simulate a full-scale attack, a company needs to go back to the reconnaissance stage and look for all the organization's weaknesses and vulnerabilities. Cymulate's platform maps these, find the weaknesses, and gathers all the initial intelligence information about the organization.
ASM and VPT immediately improve vulnerability management programs through these identified exploitable assets and integrates with the VM platform, to contextually prioritize the discovered vulnerabilities. By demonstrating in real-time, which exploits can or cannot circumvent the cyber security controls, Cymulate reduces the overwhelming vulnerability scan results, down to an actionable, prioritized and manageable list.
“Our customers were facing an ongoing challenge of patching vulnerable assets,” said Avihai Ben-Yossef, the Co-Founder and Chief Technology Officer (CTO) of Cymulate.
Cymulate’s platform contextualizes the vulnerabilities
Avihai Ben-Yossef adds, “We looked at the possibility of acquiring a company that collects attack surface data, for contextualizing the vulnerabilities presented by Cymulate, but after much research, we saw that existing ASM solutions do not offer organizations, the full coverage that they need, to optimally produce a contextualized vulnerabilities prioritizing list. We are proud to have developed a solution in-house that meets the needs of our customers.”
“Security challenges have greatly intensified this past year, creating more daily problems for security teams to handle and stay on top of, however, many lack the resources to deal with them,” stated Eyal Wachsman, the Chief Executive Officer (CEO) and Co-Founder of Cymulate, adding “Controlling the risk of vulnerability patching, in line with the enterprise's security posture, makes the difference between businesses losing a few minutes or hours of downtime, versus days or months.”
Eyal Wachsman adds, “Equally, enabling the visibility of higher risk penetration vectors, where attackers are most likely to start their campaigns from, is just as critical. With these additional capabilities, more customers find Cymulate solving multiple use cases as a holistic security posture validation platform.”
Attack Surface Management (ASM)
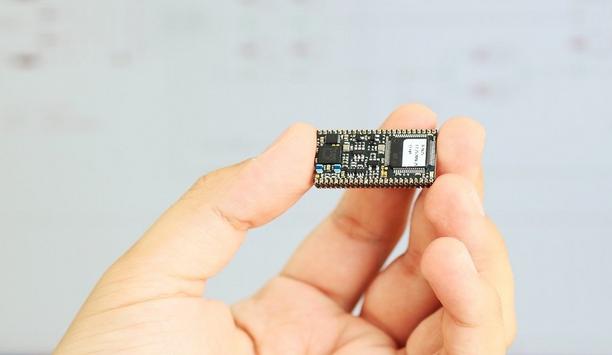
Cymulate's Attack Surface Management (ASM) technology emulates real attackers, to identify digital assets
Cymulate's Attack Surface Management (ASM) technology emulates real attackers, to identify digital assets (such as domains, IP addresses, and more) and assess their exploitability against the organization's security policies and solutions. With findings mapped to the MITRE ATT&CK’s framework's TTPs (Tactics, Techniques, and Procedures), business enterprises can take the necessary mitigation steps.
A record number of nearly 20,000 vulnerabilities were disclosed in 2020, of which 57% were classified as critical or high severity, yet patching remains a struggle for many organizations, due to limited resources, the complexity of legacy systems, inability to prioritize, and internal pressures. This new solution offered to security professionals and executives assesses the vulnerabilities' potential impact on the security posture and prioritizes the patches to implement, assuring business continuity.
Vulnerability Prioritization Technology (VPT)
Cymulate's Vulnerability Prioritization Technology (VPT) solution integrates with leading third-party vulnerability management solutions including Qualys, Tenable, Insight, and Microsoft Defender.
The solution cross-references information on vulnerabilities provided by these vendors, with the analysis from Cymulate's security posture validation platform offering a practical view of compensatory security controls over unpatched vulnerabilities in the network.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance