How Should Your Security Company Measure Total Cost Of Ownership (TCO)?
Editor Introduction
How much does a security system cost? We all know that total costs associated with systems are substantially higher than the “price tag.” There are many elements, tangible and intangible, that contribute to the costs of owning and operating a system. Taking a broad view and finding ways to measure these additional costs enables integrators and users to get the most value from a system at the lowest total cost of ownership (TCO). However, measuring TCO can be easier said than done. We asked this week’s Expert Panel Roundtable to share the benefit of their collective expertise on the subject. Specifically, we asked: How should integrators and/or end users measure total cost of ownership (TCO) when quantifying the value of security systems?
I would suggest to technology integrators and end users that they measure the total cost of responsible and safe ownership. This is especially true if they identify their technology as critical, life-safety solutions and their networks as mission-critical elements of their business. Divide the overall cost by time-in-use to determine the true worth of a solution. Low cost is easy to measure: Buy it, deploy it, someday replace it. On the other hand, the calculation of total cost of responsible and safe ownership should account for integrity of the baseline solution, the ability to adopt incremental innovations over time, ongoing revisions and updates that fortify the solution for performance uptime, cyber integrity, new regulations and other future needs. The best TCO in most cases is not the lowest TCO. The technology landscape continues to evolve. Therefore, our measurements for cost of ownership need to change also.
When assessing the “total cost” of ownership, one must examine both the initial cost and the cost over the lifetime of the system. Oftentimes, the focus is on the amount of money initially spent on equipment, as opposed to recognizing that the system will require operational and other costs throughout its life. Some questions to ask: Am I tied to a limited number of manufacturers? Am I able to change manufacturers as my needs change over time? Will my system adapt to coming updates of security features and can it be managed effectively in the network environment? If you feel restrained by limited choices, it may be wise to choose a security system and components that follow the development of commonly adopted standards. And what about total cost if no security system is installed? Do the costs of potential risks with no security outweigh the cost of the system?
When looking at TCO you need to consider the obvious initial capital cost – compared to alternatives – and also the operational costs across the lifespan of the systems, across one, three and five years. On top of this, though, security can add additional value through integration. For example, an access control system can collect movement data that can be integrated with HR systems, saving on data collection costs. If security is linked to environmental controls it can also be used to regulate and check lighting, heating and ventilation systems, to ensure there is no wastage of resources. As they oversee an entire facility, security systems can offer operators unrivaled insights into the movement of people and daily operations of the organization. Security providers need to promote this advantage and use it to demonstrate compelling TCO through value-added services. This is a more sustainable business model than simply providing cheap security solutions!
Measuring TCO should take into account not only the initial capital investment, such as controllers, readers or video equipment, but also the cost associated with maintaining the software moving forward. Are there annual licensing fees associated with the software? There are solutions available on the market today that do not charge annual licensing, and these fees can add up very quickly each year. Another factor to consider is whether the solution is interoperable and built on open-platform technology. Also important is how well the software integrates with other data management tools to streamline updates and accessibility into multiple systems in a single platform. If you can get multiple systems talking to each other and sharing data, you can automate many processes, thus reducing resources and costs and ultimately bringing a higher level of efficiency to your overall solution.
It's good to consider things like interoperability and whether you're investing in technology that makes up a comprehensive solution, but I would challenge integrators and end users to take it one step – maybe even 10 steps – further and consider pushing the envelope a bit in their buying decisions. The security industry is on the brink of a revolution, if you will, as more and more solutions implement advanced artificial intelligence capabilities into their products that act to deliver more value for the investment. In my opinion, this progressive attitude toward enhancements can position end users and integrators as leaders and innovators in their own right, which can attract a different kind of consumer base to make additional capital investments in emerging tech rather than legacy systems. It's an exciting time overall to think about it.
When considering TCO, it can be a challenge to incorporate all the factors, and to give each proper weight in the calculation. Obvious factors to include are: Initial cost of equipment and software; cost of deployment and installation; supporting infrastructure; maintenance contract costs; and environmental support costs, such as electricity and climate control. Less obvious elements that are equally important to consider include space consumption and special building, training costs, the cost to upgrade/replace at end-of-life, and ease of use. For the latter, the cost of additional time and effort required to use the system as compared to another system must be factored into the TCO. Be cautious not to overlook this second set of factors; also, do not assign more weight to any one factor than reasonably reflects actual costs to your business. Each end-user is different, which makes this a somewhat personalized calculation.
It’s important to fully understand the total cost of ownership because a security budget can be impacted by direct and indirect costs, and tackling what these costs may look like during the planning phase will help your program stay on track. From the beginning, integrators need to identify what business outcomes they are trying to drive through their security systems. They must look past security as a standalone system and incorporate the building management, and fire and life-safety systems to see how they can collectively drive specific outcomes. Through systems integration, end users can better measure the value of their security system because all of their building goals are aligned.
As integrators and end users evaluate security systems, they should consider some of the same items and some different items based on their role in the install. End users must consider the direct and indirect costs of a security system spanning equipment costs, operating costs, maintenance, licensing and warranties. Usually the upfront equipment costs are the biggest budget items, but ultimately over time the license fees, software upgrade fees and maintenance end up with the largest overall cost. As end users compare systems, they need to review upfront capital expenses but also the costs over time and the operational efficiencies gained from a specific system. Take a cloud-based software for example: there is typically an annual license fee for the software, but the savings in on-premise infrastructure costs, internal IT staff and maintenance, and cybersecurity practices ultimately result in a lower total cost of ownership of a security system.
Technology continues to be the most prominent change agent in the market. The Internet of Things (IoT), big data analytics, mobile solutions, and artificial intelligence have had a significant impact on the industry and transformed how technology can be used to build value. In today’s market, advancements in data capture, processing, analysis, and visualization technology have enabled a new generation of intelligent capabilities that improve security and efficiencies, which deliver new levels of ROI. For the end user, investments must demonstrate value to the overall business, and security practitioners need to be able to justify a security expenditure by using language and budgeting processes that resonate with senior leaders. Being able to demonstrate that video, for example, is valuable in not only reducing the opportunity for loss but enhancing business objectives is very powerful. The adaptability of video cameras, analytics, and artificial intelligence makes it easier to justify investment.
Video surveillance is as a strategic tool to help organizations mitigate risk, reduce costs and improve operations. But measuring the financial return from investments in surveillance technology — especially when much of the value is derived from preventing something from happening in the first place — can be challenging. End users need to review the overall cost associated with their video security solutions, including equipment investment, operating costs and the loss associated with any incidents. It's also critical to look at the value deemed from investments in technology and how it helps reduce risk or an event’s impact, as well as how much the technology helps to ensure assets, intellectual property, employees and even brand reputation are protected. Additionally, stakeholders should evaluate how technology can be used in risk management, as well as how it can add value to operations at the same time.
Identifying the true value of a security system depends on a variety of factors, and determining a set figure for the total cost of ownership may be tricky. But one of the most important aspects that contributes to a security system’s worth is its ability to provide the user with only the relevant and actionable information needed to efficiently respond to a security event. A reduction in the TCO comes when end users are able to save time and resources by focusing on crucial video data rather than sifting through hours of non-critical footage. In addition, a software solution that requires fewer installation and training hours, has little to no cost in licensing or maintenance, and enhances intelligence and flexibility will prove to integrators and/or end users to be a valuable security system that saves on TCO and increases ROI.
Customers continue to invest in projects that maintain and improve their security, reduce fraud, and enhance customer engagement. When users can demonstrate the importance of technologies to address these three pillars of business, leaders can better understand the value technology investments deliver. As a security practitioner, it is important to be able to demonstrate to your C-level executives that you understand the importance of the total cost over investment lifecycle. Integrators need to arm their customers to have this conversation by providing the tools to express long-term value. Overall, we’re finding that new use cases and the opportunity to fuse rich data sources improve the argument for long-term value and benefits. We see an overall trend away from simply reacting and toward proactively identifying the potential areas where fraud can occur and addressing the exposure before it becomes a problem. Prevention is really where true ROI lies.
Measuring TCO in advanced physical security solutions such as video management system (VMS) technology can usually be divided between tangible and intangible costs. Concrete features such as VMS backward compatibility; cameras accommodated per server; use of less expensive hardware; automatic updates; remote diagnostics and the capability for direct NAS recording anywhere on the network; eliminating local storage costs, can all be quantified for cost purposes. VMS solutions based on an open architecture platform can integrate with a variety of other systems such as license plate recognition systems, access control, visitor management and various types of analytics for a more cost-efficient system. Subtler, yet equally important, cost benefits can be derived from partnering with an experienced integrator who can engage with the customer to investigate and address specific challenges. They can recommend VMS solutions that eliminate costly manual configurations, saving time and money for both the integrator and the user.
The vital nature of security makes the quality and reliability of security products critical, and there are many advantages to working with a U.S.-based manufacturer to secure high-quality security solutions. Despite increased competition from providers whose products are manufactured in countries where labor costs are lower, U.S. manufacturers have a well-earned reputation for superior quality, as they have invested heavily in advanced plants and technologies while abiding to high manufacturing standards. Customer service and flexibility are key, as well, and U.S. companies are willing to work with installers and end users to develop customized solutions, often without significant cost increases. U.S. manufacturers are also committed to providing customers with fast and easy access to products, services, and support. Overall, working with a U.S.-based manufacturer allows you to receive the benefits of investments in machinery, equipment, processes and procedures, which result in high-quality security solutions.
Editor Summary
Performance uptime, cyber integrity, training, flexibility to adapt, maintenance contracts and environmental support are just some of the many elements listed by our Expert Panel Roundtable as having an impact on TCO. Considering these and many other factors can lead end users and integrators to a more realistic measurement of TCO. In the end, cost justification of security systems is a shared challenge in the market. Manufacturers must consider broader issues of TCO when designing their products, and integrators increasingly use such measurements when making a sale. Most challenged is the end user, who must make a case within their company to spend scarce resources to buy more security technology. TCO, and other issues of cost justification and ROI, are critical elements in how security systems today are bought and evaluated.
Expert commentary
Security beat
Security bytes
- Getting To Know Dan Grimm, VP And General Manager Of Computer Vision At RealNetworks
- Big Wins And The Importance Of Showing Up: Insights From SecurityInformed.com Editor Larry Anderson
- Setting Goals, Business Travels And Radioactivity: Success Secrets From Tiandy's John Van Den Elzen
- Getting To Know Jeff Burgess, President/CEO At BCDVideo
Healthcare security articles
Rapid technological advancement, artificial intelligence (AI) and machine learning (ML) are revolutionizing traditional on-premises video security systems. These next-level tools are not just enhancin...
Milestone Systems, a global pioneer in video technology, is at the forefront of the video security industry, emphasizing responsible technology innovation across its operations. The company will host...
ASSA ABLOY Opening Solutions returns to Global Security Exchange (GSX) for 2024's powerhouse get-together of security professionals from around the world. Digital access control Attendees can visit...
As the backbone of community welfare, healthcare facilities cater to crucial public needs from emergency care to specialized medical treatments, and due to its position as a significant facet of the w...
Rhombus, a pioneer in cloud-managed physical security, announced the availability of two additions to its comprehensive lineup of security solutions: the R600 Multisensor Camera and the E50 Envir...
HID®, a worldwide pioneer in trusted identity solutions announces the launch of the next-generation FARGO® HDP5000e designed to deliver vibrant, high-definition cards and IDs. HID's Isaac You...
Suprema, a global pioneer of AI-based security solutions, announces that its products and services are fully compliant with the latest global data protection regulations and security certifications.&n...
Cyber resilience research commissioned by Cohesity, a pioneer in AI-powered data security, reveals the true cost of ransomware to finances and business operations and why overconfidence may be the cau...
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the launch of Genetec Cloudlink™ 110, the lates...
i-PRO Co., Ltd. (formerly Panasonic Security), a global pioneer in professional security solutions for video protection and public safety announced the establishment of a comprehensive AI governance f...
Gcore, the global edge AI, cloud, network, and security solutions provider announced the launch of Gcore WAAP, its end-to-end web application and API protection solution. Gcore WAAP Leveraging advan...
Barco, a global pioneer in visualization and collaboration solutions, is proud to announce its pivotal role in shaping the visitor experience for the Belgian pavilion at Expo 2025 in Osaka. Bar...
King Faisal Specialist Hospital & Research Center (KFSHRC) is at the forefront of the healthcare AI revolution. Since 2019, the hospital's dedicated AI center has been developing innovative applic...
Convergint, a global pioneer in service-based systems integration, today announced that it has acquired Esscoe, a premier provider of mission-critical security and fire and life safety systems in the...
Huffmaster Management (Huffmaster), the provider of choice for Fortune 500 companies seeking strike services, industrial and healthcare staffing, security services, and more, announced the intern...
Mobile access articles
Zenitel, a provider of intelligent communication solutions, announced the launch of two new door entry intercoms: the Turbine Extended Intercoms TEIV1+ and the TEIV4+. The new products display Zenite...
Physical security is essential for a modern production facility, users don’t want just anyone entering the building or accessing secure areas. But what about production machinery? Machine authe...
Salient announced CompleteView v7.5, the latest update to its industry-leading video management platform. This version introduces improvements to operator experiences as well as major new enterprise c...
Munich’s Hofbräuhaus enjoys an iconic status, as both a heritage property and a spiritual home for lovers of German beer. “In this historic building is the world’s most famous t...
Radiofrequency (RF) technology specialists, SPX Communication Technologies launched Evenlode Lite, an entry-level video downlink system designed for regions new to airborne surveillance or those looki...
Wavelynx Technologies, a trailblazer in advanced, secure, and versatile reader and credential solutions, announced the launch of its industry-first app, Configure by Wavelynx, to revolutionize th...
HID, a worldwide pioneer in trusted identity solutions, announces the expansion of its signature line of Signo™ Readers to include models that meet varying customer needs – from harsh cond...
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the launch of Operations Center, a cloud-based work m...
Hanwha Vision, the global vision solution provider, has released the XRN-426S-1T recorder - a compact NVR with a built-in 1TB solid-state drive (SSD). The 4-channel recorder supports AI search, when...
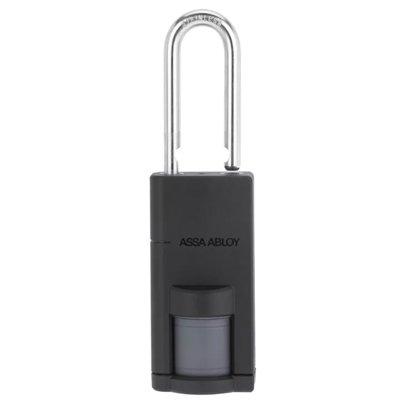
Fences, gates, storage cages, racks, containers, tool cabinets, and other non-standard openings often require restricted access and greater control. In many cases, they are secured with mechanical loc...
IDEMIA Public Security North America, the global provider of convenient and trusted biometric-based solutions, including physical and digital secure credentialing in the U.S, is partnering with My Fam...
Wireless access control company, CellGate, has just announced a full family of digital Virtual Key options for Watchman® W480, W482, W461, W462, WXL and WXL2 multi-family models. CellGate’s...
ABLOY rose to the top of the list as Finland’s most valued brand of 2024, according to an annual survey by pollster Taloustutkimus. Market research company - Taloustutkimus surveys Finnish consu...
Signo Express and Seos Essentials provide a comprehensive, affordable access control solution designed for small to mid-sized businesses. This suite maximizes security and flexibility without complex...
Award-winning security manufacturer, Gallagher, has announced the appointment of Merv Williams as Chief Marketing Officer (CMO). Williams will lead the development and delivery of Gallagher Security&r...
The Security Challenges Of Data Centers
DownloadSecurity Practices For Hotels
DownloadAccess Control System Planning Phase 2
DownloadSIA Identity and Biometrics Symposium
DownloadVideo Surveillance
DownloadASSA ABLOY Aperio P100 Padlock
Climax Technology TouchPanel-3
ASSA ABLOY eCLIQ Electronic Key For Enhanced Building Security