The industry faces numerous challenges in the coming year. Physical and cyber security threats continue to become more complex, and organizations are struggling to manage both physical and digital credentials as well as a rapidly growing number of connected endpoints in the Internet of Things (IoT).
We are witnessing the collision of the enterprise with the IoT, and organizations now must establish trust and validate the identity of people as well as ‘things’ in an environment of increasingly stringent safety and data privacy regulations. Meanwhile, demand grows for smarter and more data-driven workplaces, a risk-based approach to threat protection, improved productivity and seamless, more convenient access to the enterprise and its physical and digital assets and services.
Using Smartphone Apps To Open Doors
Cloud technologies give people access through their mobile phones and other devices to many new, high-value experiencesEnterprise customers increasingly want to create trusted environments within which they can deliver valuable new user experiences. A major driver is growing demand for the ‘digital cohesion’ of being able to use smartphone apps to open doors, authenticate to enterprise data resources or access a building’s applications and services.
Cloud technologies are a key piece of the solution. They give people access through their mobile phones and other devices to many new, high-value experiences. At the same time, they help fuel smarter, more data-driven workplace environments. With the arrival of today’s identity- and location-aware building systems that recognize people and use deep learning analytics to customize their office environment, the workplace is undergoing dramatic change.
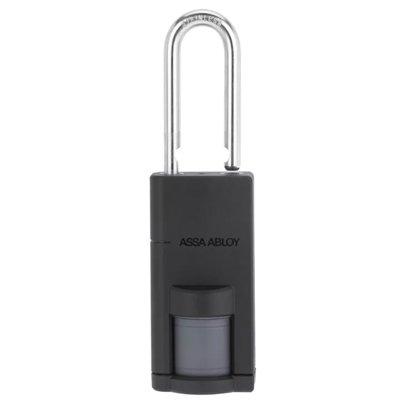
Improved Fingerprint Solutions
Cloud-based platforms and application programming interfaces (APIs) will help bridge biometrics and access control in the enterprise, overcoming previous integration hurdles while providing a trusted platform that meets the concerns of accessibility and data protection in a connected environment. At the same time, the next generation of fingerprint solutions will deliver higher matching speed, better image capture quality and improved performance.
 |
| The next generation of fingerprint solutions will deliver higher matching speed, better image capture quality and improved performance |
Liveness detection will ensure that captured data is from a living person. Biometrics authentication will also gain traction beyond access control in immigration and border control, law enforcement, military, defense and other public section use cases where higher security is needed.
Flexible Subscription Models
Access control solutions based on cloud platforms will also change how solutions are deployed. Siloed security and workplace optimization solutions will be replaced with mobile apps that can be downloaded anywhere across a global ecosystem of millions of compatible and connected physical access control system endpoints.
These connections will also facilitate new, more flexible subscription models for access control services. As an example, users will be able to more easily replenish mobile IDs if their smartphones are lost or must be replaced.
Generating Valuable Insights With Machine Learning
Machine learning analytics will be used to generate valuable insights from today’s access control solutionsEducation, finance, healthcare, enterprise, and other niche markets such as commercial real-estate and enterprises focused on co-working spaces will benefit from a cloud-connected access control hardware foundation.
There will be a faster path from design to deployment since developers will no longer have to create an entire vertically integrated solution. They will simply add an app experience to the existing access control infrastructure. New players will be drawn to the market resulting in a richer, more vibrant development community and accelerated innovation.
Data analytics will be a rapidly growing area of interest. Machine learning analytics will be used to generate valuable insights from today’s access control solutions. Devices, access control systems, IoT applications, digital certificates and location services solutions, which are all connected to the cloud, will collectively deliver robust data with which to apply advanced analytics and risk-based intelligence.
As organizations incorporate this type of analytics engine into their access control systems, they will improve security and personalize the user experience while driving better business decisions.