Security risks are on the rise. Whether it’s detecting insider threats, preventing data breaches, or fighting economic espionage, security issues are becoming a daily struggle for many organizations. According to a report by the research and consulting firm Gartner, 30% of critical infrastructure organizations will experience a security breach by 2025.
This is why adopting an Access Control System (ACS) is more important than ever. An ACS uses identity authentication to make sure that only approved parties can enter secured spaces and protect sensitive areas and assets from people users don’t trust. But how does identity verification work? In this post, Alcatraz AI explains how facial authentication can promote a safer workplace.
What is identity authentication?
Identity authentication is an essential requirement for many in-person and online procedures. A user might be verifying their identity multiple times a day without even noticing it. If users present a photo ID at a bank or sign in to websites with their fingerprints, they are proving their identity. Identity verification is an important process that ensures a person is who they claim to be.
Identity verification is an important process that ensures a person is who they claim to be
Identity verification software works by comparing the presented information with a verified data set to produce a positive match. Once the traits and characteristics of the person match the one that is supposed to be, they are allowed to enter a premise or use a service. Identity verification systems reduce the risk of breach and fraud by inhibiting unauthorized access.
Methods of identity verification
In an era when security breaches are becoming commonplace, access control systems are essential for protecting an organization. With identity authentication at the core of access control, many different types of verification techniques have been developed to secure services and spaces. Below are the most common ways how identity is verified to grant access:
Something You Know the technique
The “something you know” verification technique relies on passwords, PIN codes, or answers to security questions to authenticate a user’s identity.
When the correct information is entered, the user is given access to an account or area. Also known as knowledge-based authentication (KBA), this verification method is often used for online services and keypad door lock systems.
Something You Have modality
The “something you have” identity verification modality uses an object in your possession to grant access to a privileged location. This object can be a badge, key card, or fob.
Using Radio Frequency Identification (RFID) and other technologies, card/badge readers capture and read data from the object’s magstripe or a microchip to validate credentials.
Something You Are approach
The “something you are” approach relies on biometric identity verification software to authorize access
The “something you are” approach relies on biometric identity verification software to authorize access. Biometrics are uniquely human characteristics like fingerprint design and iris pattern that can be used to identify an individual.
Common biometric identity verification systems employ fingerprint validation, iris scanning, or facial authentication to confirm a user.
Facial authentication vs. Facial recognition
Facial authentication systems are often confused with the more controversial facial recognition technology. While both rely on biometric identification, facial authentication and facial recognition are not the same. Facial recognition systems can collect biometric data from an individual without their knowledge or consent. Many consider this a violation of their privacy.
However, Alcatraz Rock is a compliance-based system that does not operate without the consent of the user. Users voluntarily enroll in the software and actively interact with it to verify their identity. Because users opt in to the system, organizations can take advantage of biometric identity verification while staying compliant with privacy laws.
How does Alcatraz AI facial authentication work?
Access is granted when the user’s face matches stored biometric information in its database
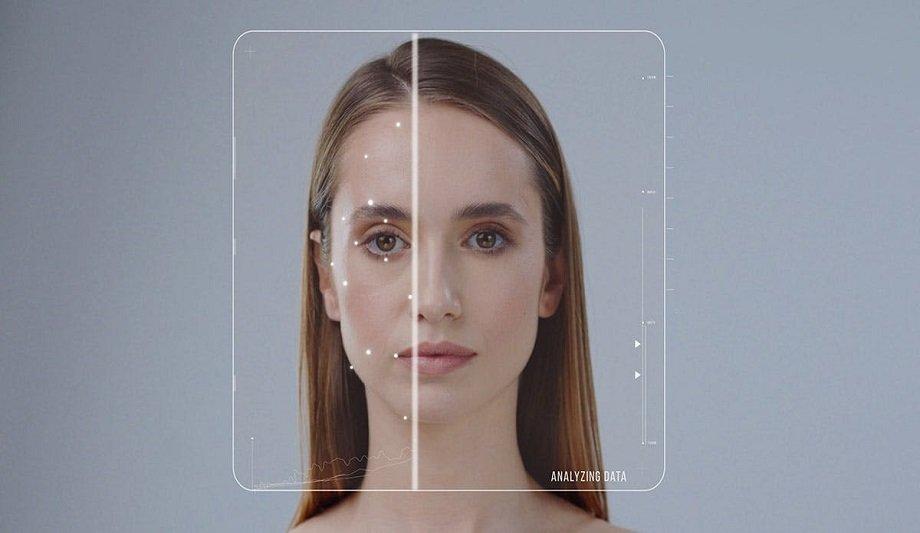
The Alcatraz AI facial authentication access control system uses artificial intelligence and 3D sensing technologies to enable highly secure, frictionless entry into privileged locations. All users must give their explicit consent before enrolling in the identity verification system. Once consent is acquired, the user interacts with the Alcatraz hardware to register their facial data.
When a user comes within proximity of the Alcatraz Rock, the identity verification software performs a matching process to authenticate the individual. The user’s facial data is compared to an encrypted, fully-closed database that they have previously opted into. Access is granted when the user’s face matches stored biometric information in its database.
Benefits of facial authentication access control
Modern security challenges demand modern security solutions. Legacy access control systems such as card readers and keypad door locks have much vulnerability which increases the risk of security breaches.
Leveraging cutting-edge technologies, biometric identity verification systems promote a safer environment while reducing the costs of your security infrastructure. Following are some benefits of facial biometric systems:
Robust security controls
Traditional access control systems make it easier to commit fraud. Key cards and PIN codes can be stolen and used by anyone to gain unauthorized entry into secured premises.
Unlike data and objects that can be stolen or shared, facial biometrics is unique to an individual. This ensures that only authorized users can access sensitive assets.
Seamless user experience
Alcatraz Rock is a touchless and autonomous access control system that authenticates faces in real-time
Facial identity verification is much more efficient than other methods of access control. Entering PINs, swiping cards, or scanning fingers creates friction and wastes time.
The Alcatraz Rock is a touchless and autonomous access control system that authenticates faces in real-time. This convenient approach to identity confirmation creates a seamless user experience.
Impossible to replicate
A major benefit of investing in facial identity verification software is that it’s spoof-proof. Key cards can be duplicated for less than $10 and finger prostheses can bypass many fingerprint scanners.
Facial data, on the other hand, is impossible to replicate. The Alcatraz Rock ensures that the authorized user is physically present at the access point.
Enhance access controls with Alcatraz AI
Security threats are becoming increasingly sophisticated and more difficult to prevent. The old ways of protecting the assets are no longer effective to overcome modern challenges.
Users need cutting-edge access control technologies to safeguard resources from espionage and theft. Facial identity verification systems provide the most robust security possible.
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems