Dahua Technology, a video-centric smart IoT solution and service provider, recently ranked 1st in the MIT Scene Parsing Benchmark.
Based on deep learning algorithms, Dahua Technology’s Scene Segmentation Technology tops the world's best results in Scene Parsing, surpassing other major AI companies and academic research institutions, and exceeding scene parsing research results in relevant papers of ICCV, ECCV, and CVPR. This achievement marks Dahua Technology’s position in the field of scene parsing.
Computer vision technologies
ADE20K_MIT is an evaluation dataset for MIT Scene Parsing Benchmark released and maintained by the MIT CSAIL research group. It is one of the internationally authoritative computer vision semantic segmentation algorithm evaluation datasets. The dataset is used to evaluate the performance of computer vision technologies such as Scene Perception, Scene Parsing, Instance Segmentation, and Semantic Segmentation.
The challenging evaluation attracts participants from hundreds of well-known AI laboratories
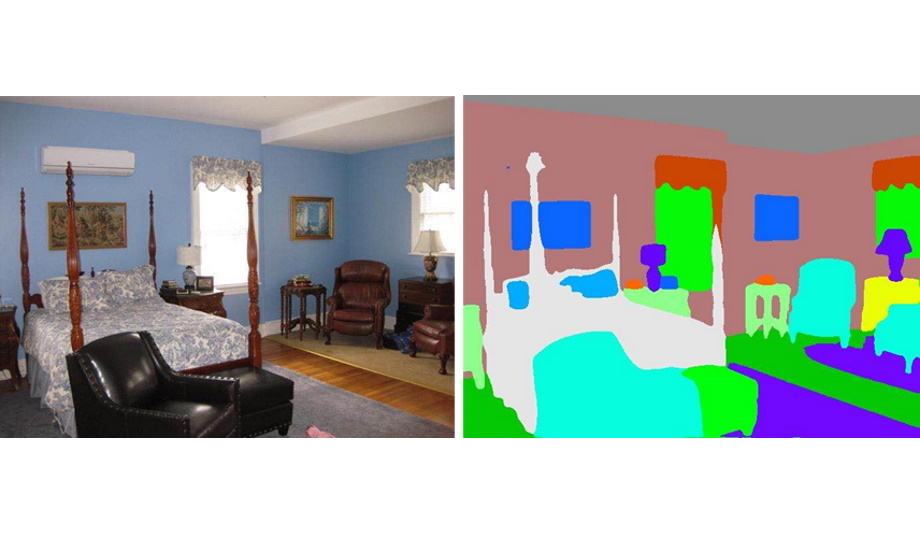
With a wide range of targets and a large range of target scales, the challenging evaluation attracts participants from hundreds of well-known domestic and foreign AI laboratories and top academic research institutions, including MIT, Microsoft, Peking University, Tsinghua University, Chinese Academy of Sciences, Alibaba, etc. Scene parsing is to segment and parse an image into different image regions associated with semantic categories, such as sky, road, person, and bed. It is one of the core technologies in the segmentation field, which solves problems such as occlusion, unclear categories, and easy confusion in complex scene parsing.
Self-Developed deep learning platform
In this international evaluation, Dahua Technology innovatively utilized its algorithm advantages in Semantic Segmentation and Panoptic Segmentation based on its self-developed deep learning platform, and developed a set of Semantic Segmentation frameworks based on Graph Convolutional Neural Networks(GCN). Through multi-scale features fusion, adaptive IoU Loss Function on the frequency domain, and by taking advantage of Multi-model Feature Fusion Technology, the Dahua framework effectively improves the mean of the Pixel-wise Accuracy and Class-wise IoU of Scene Segmentation, which ultimately tops the evaluation records of scene parsing dataset.
Dahua Technology continues to cultivate and innovate in the field of AI technology, and constantly improves the core competitiveness of its algorithms and computing power. In 2018, Dahua Technology ranked first in 12 global AI rankings including road segmentation, vehicle tracking, multiple object tracking, 3D object detection, human detection, vehicle detection, scene flow, optical flow, and person re-identification.
Setting complex configurations
Dahua Scene Parsing Technology can automatically identify traffic sign information
In the succeeding year, 2019, Dahua Technology ranked first in 10 global AI rankings including person re-identification, instance segmentation, semantic segmentation, gait recognition, and remote sensing image analysis. Dahua Technology actively accelerates the transformation of AI technology achievements into real productivity and empowers the intelligent upgrade of the industry.
In the field of smart traffic management, Dahua Scene Parsing Technology can automatically identify traffic sign information including lane lines, turning arrows, stop lines, pedestrian crossings, etc. For example, in a violation preliminary trial, this technology can be used to achieve automatic analysis of the target’s trajectory and illegal behavior without manually setting complex configurations, which improves work efficiency, eases the use of the product, and continuously expands the application of solutions related to traffic scene parsing.
Improving road safety and travel efficiency
At the same time, with AI enforcement camera, e-police system, dual-lens enforcement camera, smart traffic signal control and other deployments to maximize the advantages of AI technology, it can also improve road safety and travel efficiency, providing a powerful technical engine for intelligent traffic management.
In the future, Dahua Technology will provide key technical support for the expansion and application of smart logistics, smart water services, smart farming, and smart retail through the accumulation and breakthroughs in AI technology, aiding the industry's innovation and development.