Over the past 40 years there have been numerous attacks carried out against cultural and hospitality venues in the furtherance of religious, ideological, criminal or political beliefs. By default, cultural and hospitality venues are attractive targets for terrorists due to their public accessibility, the volumes of visitors and guests or because of what the venue represents; in short because they are ‘soft targets’.
Examples of such attacks include the destruction of the Buddha’s of Bamiyan in Afghanistan by Mullah Omar, the 2015 attack on the Bardo museum in Tunis, the coordinated attacks in Mumbai through to the recent attack on a Berlin Christmas market where an tractor-trailer was used as a weapon.
So how can we protect these venues from terrorist attacks without making them a fortress or detracting from their main functionality?
Understanding Terrorist Threats
When implementing protective strategies, the first thing I need to understand is what threats exist and what risks they poses to the organization or individual being protected. In this case the threat source is terrorism. What is terrorism? There are many different definitions of terrorism but the one that I have used for over 30 years is: “The unlawful use, or threat of violence to achieve political or ideological aims.” This differs from organized crime which may use terror but is concerned with financial reward and gain. I define a terrorist as “Somebody who knowingly takes part in, supports or assists an act of terrorism.”
The next stage is understanding the ways in which the threats can impact the organization and the risks that exist from known, or anticipated attack methodologies. While the threat from traditional attack methods continue; car bombs, grenades, firearms etc., these are by no means the only threats that should be considered. The 9/11 attacks used aeroplanes, a boat was used against the US Cole and in 2016 a lorry was used to devastating effect to kill 86 and physically injure over 400 civilians during the Bastille Day celebrations in Nice, France.
Introducing Protective Security Measures
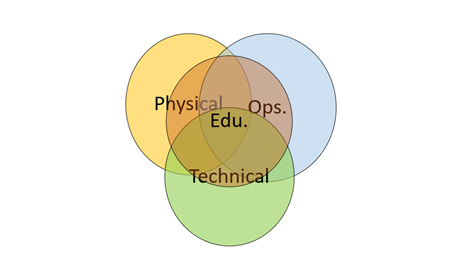
Once understood, the risks and vulnerabilities that exist for each attack method can be assessed and categorized. This allows protective security measures to be introduced that reduce the likelihood or impact of any attack that takes place. For ease, I categorize the protective security measures in one of four ways:
- Physical measures
- Operational (procedural) measures
- Technical measures
- Educational measures
These measures should be overarching and work collaboratively with each other to create defense in depth and increasing resilience and robustness. The idea being to provide a means of protecting assets and deterring, detecting and delaying attackers, while increasing response capabilities.
 |
| Once understood, the risks and vulnerabilities that exist for each attack method can be assessed and categorised |
Museums, hotels, bars and restaurants are places where people go to for relaxation and pleasure. Therefore, the implementation of security measures must be carefully considered so that the organization is still able to function without destroying or negatively impacting the customer experience. Understanding an organization’s risk appetite and tolerance levels are almost as important as the security measures that are introduced to protect them.
Physical Security Options
Physical security measures include barriers, fences, secure doors and windows. They can also include security personnel and the creation of stand-off and vehicle mitigation measures. CPTED methodologies and design practices are a great means of preventing certain attack types and creating better response capabilities. In some countries, security personnel can be armed, but not in all. During the 2017 New Year celebration attack at the Reina nightclub in Istanbul an armed police officer and 35,000 on duty police could not prevent the attack that resulted in 39 deaths.
Although technical security measures may not deter or really delay terrorist attacks (unless used as part of a physical security measure) CCTV, search equipment and access control systems do provide an ability to identify pre-attack activity including surveillance and penetrative testing.
Security Education For Staff
An organization’s operational practices and procedures are a great protective security resource. Levels of alertness, introduction of surveillance detection program involvement of all staff in the security program, correct search procedures and robust access control to reduce the target attractiveness of the venue.Security education can enable 100 people to be involved in a surveillance detection program instead of just the security team
Security education is often either forgotten or not considered by many as a fundamental security measure. Security education allows staff to understand the security measures that exist, why they exist, the actions they are to take and the part that they can play in protecting themselves, visitors and venues from attack. Security education can enable 100 people to be involved in a surveillance detection program instead of just the security team and help staff understand suspicious activities and reporting practices. Security education helps deliver and maximize the effectiveness of each of the other security measures that are introduced.
Proactive Planning
An organization has to be realistic in its approach to protection from acts of terrorism. The likelihood of preventing a terrorist attack is low, fact. Unless intelligence was available or surveillance detected the first a venue would know about it would be the attack itself. However, there is still an ability to make a significant impact in protecting visitors, staff, physical assets and reputation. These include:
- Proactive immediate response planning
- Establishing a recovery plan
- Providing welfare and medical support to victims.
 |
| Indirect victims may include first responders, crisis and emergency management teams and families of direct and indirect victims |
I still find organizations and venues that do not have emergency or crisis management plans that are specific and fit for purpose. Not only is it critical that a plan exists but also that senior management know and understand the actions that they need to take. Plans should be exercised so that the operational, tactical and strategic elements are being tested and where vulnerabilities are identified steps are taken to reduce or mitigate them.
Recovery planning is a vital part of your crisis management practices. Is there a fall-back location, can there be partial opening, what systems are operable and will they function off-site? The sooner an organization or venue can normalize operations the speedier the recovery will be. The longer it takes to recover, the increased risks to an organization’s operations, finance and reputation.
Welfare and medical support is not just about those directly impacted by the terrorist attack it also includes the indirect victims; first responders, crisis and emergency management teams, families of direct and indirect victims. Consider counseling, establishing outreach program, town hall meetings and lessons learned. Consider the welfare benefits of senior management visiting the scene, speaking with victims and being there to reopen the venue. Often it is not the physical effects that impact an organization but the psychological effects and trauma suffered, often over many months or years by staff.It has to be remembered that governments spend billions of dollars on counter terrorist programs but they are not able to thwart all attacks
Creating A Security Culture
To conclude, the chances that your organization or venue will become the victim of a terrorist attack are very slim and will normally depend on two factors; what you are doing and where you are doing it. It has to be remembered that governments spend billions of dollars on counter terrorist program but they are not able to thwart all attacks; neither can you.
Implementing sensible, risk based security measures means that resources are not being wasted unnecessarily. Including as many members of staff as possible in educational and detection program helps create a ‘security culture’ that everybody buys into.
“Failure to plan, is planning to fail!” Is a saying that has stuck with me since the early 1980’s. While you may not be able to prevent terrorist attacks, by ensuring your venue has appropriate plans to respond in a proactive manner the greater the opportunity to reduce the risks and resuming activities in a timely manner.
Discover how AI, biometrics, and analytics are transforming casino security



























