Who Should Be ‘In The Room’ When Deciding to Buy Security Systems?
Editor Introduction
We in the physical security market tend to watch closely how the buying decision is made. If anything, the buying process has become more complex in recent years. We have seen the impact of security systems extending beyond the core security department, and with greater impact come more stakeholders. “Buying by committee” is more the rule than the exception, and the committee is getting rather large in some situations. We asked this week’s Expert Panel Roundtable: Who should be “in the room” when decisions are being made about physical security systems?
When it comes to security planning, one person can't possibly do it all. This is especially true for education and healthcare institutions that need to remain open to the public while maintaining security. Creating a comprehensive strategy for these campuses will mean establishing open communications with stakeholders and forging symbiotic relationships throughout your community. By forming a small task force, you can make sure you are always operating from a position of knowledge, consent and support. Take every opportunity to speak to as many different organizations as you can. While key staff, including campus police and facilities and operations management, should be included in the decision-making process, don’t forget about checking in with your IT professionals, local law enforcement, students/patients, parents, and neighbouring businesses both on and off campus.
The landscape of today’s decision-makers is much different than that of the past. No longer is it just the security team “in the room;” there are many diverse stakeholders involved. What used to be a few people sitting around a table making decisions has now grown extensively to double digits. Different teams from IT, HR, Legal Business Continuity, and Security, including subset specialists from each group, all participate and have a voice in the security system decision-making process. Each department provides input and expertise from their department’s point of view to help their organisation make the best decision possible for the good of the whole company. This is critical in today’s changing security landscape.
The answer to this question depends on various elements of the project, such as the types of systems, size of the project, the industry segment and requirements for integration with other systems. Apart from security personnel, here are other attendees depending on the project:
- IT personnel – for system design, integration, equipment procurement, cyber security considerations, etc.;
- Consultant(s) and A&Es – if they’re involved in the spec/design;
- Integrators – if they’ve already been selected as part of the process;
- Vendors – if particular products have been selected;
- Architects/interior designers – for facilities that require attention to building/facility/store design;
- Human Resources/Operations – if there’s need to access employee databases and data, especially for access control;
- Compliance – to ensure systems comply with company or institutional policies;
- Finance – to discuss budgets, payment schedules, etc.;
- City planners and other city departments (such as power) – this is critical if the deployments are in city centers and other city departments are involved.
In today’s security deployments, there are more people who should be “in the decision-making room” than have been in the past. I have found that the most successful plans and implementations involve an access control security professional, a video security professional, an IT or networking staff member, and a facilities professional. In having these professionals in the room, the project has the appropriate individual constituents to protect people, property, and assets while taking into consideration the transport and storage systems and their respective workflows in construction and facility utilization.
In the modern business world, interest in physical security has gone way beyond the security department. This is due in part to all the other functions security can have a role in, such as time-and-attendance recording, lone worker protection and building environmental controls, to name a few. Along with the physical security team, undoubtedly the IT team will need to be heavily involved as both systems will be linked directly and have a symbiotic relationship in protecting the organization. Equally, the facility management team will want to ensure systems adequately protect and monitor staff and facilities safety. The human resource department will be interested in the time-and-attendance aspect, which is also vital to the accounting department, who will use this information for budgeting. Undoubtedly, as the overseeing “eyes and ears” of the business, physical security has a role to play across most divisions of a business.
When building a reliable, intelligent physical security system, it is critical to consider the skills and opinions of all stakeholders who will control or manage the solution as it becomes a part of the fabric of everyday operations. For example, in a university setting, representatives from different departments such as campus police, school administrators, board of trustees members, architects, facility managers and other heads of security should all weigh. Including them ensures that the design, effectiveness and sustainability of the proposed installation come together to form a cohesive solution that is easy to use and prioritises the safety of students, faculty and staff. In non-scholastic environments, it is just as important to collaborate with different departments to gauge how each one will leverage the system's benefits in their decision-making.
Depending on the size of the enterprise, there can be just a few, or many voices that need to be heard in this process. Naturally, the financial decision maker(s) will be involved. If the purchase involves IP-based technology, IT should be involved early and often to achieve their buy-in on how the technology fits the overall IT infrastructure. Physical security managers and risk managers obviously need to be engaged, but it is always good to get input from other line managers as well as the users of the proposed system. Ease of use and support of the system should be evaluated by employees who will use the system, not just their managers. Get buy-in from C-level management after the business case has been made and all other input vetted. The CEO and other C-suite executives want to know that the purchasing team has done a thorough evaluation.
Editor Summary
When it’s time to discuss a security buying decision, you might want to send out for more donuts. These discussions are likely to draw a big turnout of stakeholders from all parts of the customer’s company, not to mention consultants, accountants and others. For anyone looking to sell a system, it comes down to more questions to answer and more needs to fulfil. And all you have to do is get everyone nodding in unison.
Expert commentary
Security beat
Security bytes
- Getting To Know Dan Grimm, VP And General Manager Of Computer Vision At RealNetworks
- Big Wins And The Importance Of Showing Up: Insights From SecurityInformed.com Editor Larry Anderson
- Setting Goals, Business Travels And Radioactivity: Success Secrets From Tiandy's John Van Den Elzen
- Getting To Know Jeff Burgess, President/CEO At BCDVideo
Healthcare security articles
Rapid technological advancement, artificial intelligence (AI) and machine learning (ML) are revolutionizing traditional on-premises video security systems. These next-level tools are not just enhancin...
Milestone Systems, a global pioneer in video technology, is at the forefront of the video security industry, emphasizing responsible technology innovation across its operations. The company will host...
ASSA ABLOY Opening Solutions returns to Global Security Exchange (GSX) for 2024's powerhouse get-together of security professionals from around the world. Digital access control Attendees can visit...
As the backbone of community welfare, healthcare facilities cater to crucial public needs from emergency care to specialized medical treatments, and due to its position as a significant facet of the w...
Rhombus, a pioneer in cloud-managed physical security, announced the availability of two additions to its comprehensive lineup of security solutions: the R600 Multisensor Camera and the E50 Envir...
HID®, a worldwide pioneer in trusted identity solutions announces the launch of the next-generation FARGO® HDP5000e designed to deliver vibrant, high-definition cards and IDs. HID's Isaac You...
Suprema, a global pioneer of AI-based security solutions, announces that its products and services are fully compliant with the latest global data protection regulations and security certifications.&n...
Cyber resilience research commissioned by Cohesity, a pioneer in AI-powered data security, reveals the true cost of ransomware to finances and business operations and why overconfidence may be the cau...
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the launch of Genetec Cloudlink™ 110, the lates...
i-PRO Co., Ltd. (formerly Panasonic Security), a global pioneer in professional security solutions for video protection and public safety announced the establishment of a comprehensive AI governance f...
Gcore, the global edge AI, cloud, network, and security solutions provider announced the launch of Gcore WAAP, its end-to-end web application and API protection solution. Gcore WAAP Leveraging advan...
Barco, a global pioneer in visualization and collaboration solutions, is proud to announce its pivotal role in shaping the visitor experience for the Belgian pavilion at Expo 2025 in Osaka. Bar...
King Faisal Specialist Hospital & Research Center (KFSHRC) is at the forefront of the healthcare AI revolution. Since 2019, the hospital's dedicated AI center has been developing innovative applic...
Convergint, a global pioneer in service-based systems integration, today announced that it has acquired Esscoe, a premier provider of mission-critical security and fire and life safety systems in the...
Huffmaster Management (Huffmaster), the provider of choice for Fortune 500 companies seeking strike services, industrial and healthcare staffing, security services, and more, announced the intern...
The Security Challenges Of Data Centers
DownloadSecurity Practices For Hotels
DownloadAccess Control System Planning Phase 2
DownloadSIA Identity and Biometrics Symposium
DownloadGunshot Detection
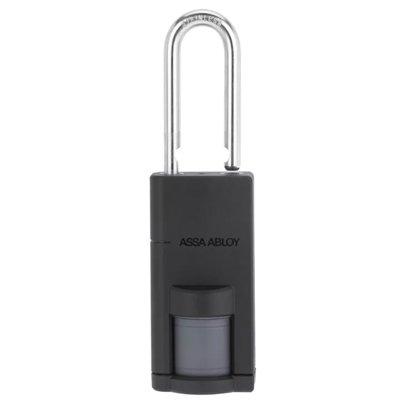
DownloadASSA ABLOY Aperio P100 Padlock
Climax Technology TouchPanel-3
ASSA ABLOY eCLIQ Electronic Key For Enhanced Building Security