DH2i, a renowned provider of multi-platform Software Defined Perimeter (SDP) and Smart Availability software, announced the launch of DxOdyssey for IoT. The new edge-optimized Software Defined Perimeter (SDP) solution, ensures end-to-end Zero Trust IoT (Internet of Things) connectivity, for the highest possible levels of security for IoT data, communications, and operations.
McKinsey advised that edge computing would represent a potential value of $175 billion - $215 billion in hardware by 2025. And, according to Verified Market Research, the Global IoT market size was valued at $212.1 billion in 2018 and is expected to grow 25.68 percent between 2019-2026 and reach $1,319.08 billion by 2026.
Network connectivity solution
“For IoT, edge computing has proven itself invaluable in its ability to overcome a multitude of IT issues, thereby enabling organizations to make faster, more efficient and effective use of the volumes of data generated from IoT devices,” said Tom Smith, Analyst, Insights From Analytics. “Unfortunately, one issue that edge computing has not been able to solve for IoT is security. In fact, in most cases, edge computing can actually introduce even greater security risk, if not managed properly.”
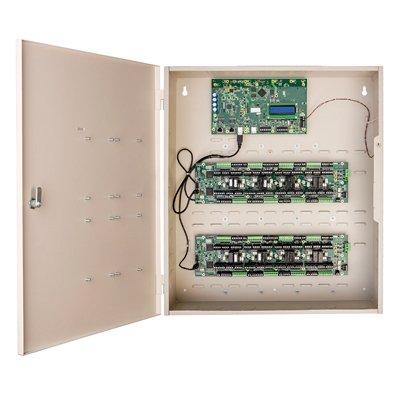
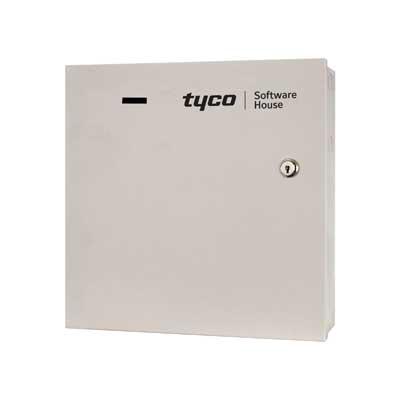
DH2i’s new DxOdyssey for IoT was designed specifically for medium and large organizations architecting IoT deployments, that need secure and discreet network connectivity between the edge devices, data center, and cloud. DxOdyssey for IoT answers their call for a single cost-effective network connectivity solution that scales from edge devices to the largest data center servers and cloud platforms and is simple to configure and manage.
Eliminating network attack
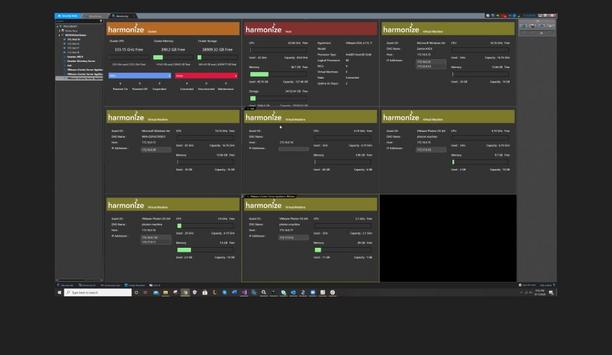
Offered via a small-footprint container (< 250mb), DxOdyssey for IoT enables organizations to build and manage secure, dynamic end-to-end data tunnels between edge device services, data center, and cloud hubs, creating a Zero Trust network architecture that virtually eliminates any attack surface.
DxOdyssey for IoT enables organizations to build secure, dynamic workload-centric connections between edge devices"
“DxOdyssey for IoT enables organizations to build secure, dynamic workload-centric connections between edge devices, data center, and cloud environments at the highest ROI - all while eliminating network attack surfaces,” said Don Boxley, CEO and Co-Founder, DH2i.
IoT connectivity solutions
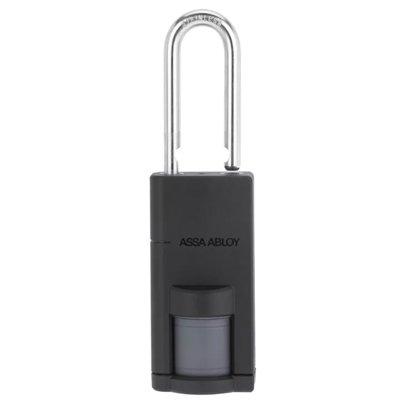
“For the first time, organizations will be freed from traditional IoT connectivity solutions that use VPNs, SD-WANs or open ports which require in-depth networking knowledge, are expensive and tedious to configure, and create large and dangerous attack surfaces.”
About DxOdyssey for IoT:
- Lightweight, <250MB, purpose-built container
- Supports ARM64- and x64-based edge devices
- Patented TCP payloads via high bandwidth UDP technology with enhanced UDP error correction
- DTLS encryption & Public Key node authentication
- More secure and performant alternative to VPNs and open ports
- Supports edge device low-latency requirement
- Supports edge device-specific access policies
- Available as an Edge Module on Microsoft Azure Marketplace
- Ideal for Azure SQL Edge use cases
Data security solution
“Microsoft Azure SQL Edge brings the most secure Microsoft SQL data engine to IoT gateways and edge devices, supporting built-in data streaming, storage, and AI in connected, semi-connected or disconnected environments. Built on the same codebase as Microsoft SQL Server and Azure SQL, Azure SQL Edge provides the same familiar developer experience, and tooling that customers already know and trust,” said John “JG” Chirapurath, Vice President, Azure AI, Data and Edge at Microsoft Corp.
“When combining the native on-device capabilities of Azure SQL Edge with the dynamic tunneling technology of DH2i’s DxOdyssey for IoT, users are provided with the optimal end-to-end data security solution for all IoT deployments.”