Synology Inc., globally renowned high-performance, reliable, versatile, and environmentally-friendly NAS servers and storage solutions firm, has announced the launch of the RackStation RS1221+ and RS1221RP+ (redundant power) 2U 8-bay rackmounted storage servers, which have been specially built to deliver high performance in a space-efficient and cost-effective manner.
“The RackStation RS1221+ and RP+ storage server units are designed for small businesses, and indeed, ‘small’ they are,” said Michael Wang, Product Manager at Synology, Inc.
Michael adds, “These units not only pack in a huge leap forward in performance, but do it at a modest depth for 2U units in their class. What's more, for businesses that require higher availability, the RP+ version is equipped with dual power supplies for redundancy and added reliability.”
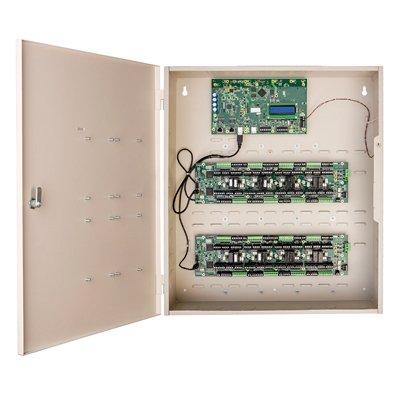
RackStation RS1221+ and RS1221RP+ storage servers
The new RackStation series units deliver 3.6X higher compute performance and 3.8X random read IOPS at 108K
The RS1221+ and RS1221RP+ rackmounted storage servers are the first RackStation series units built around the AMD Ryzen V1500B processor. Compared to their predecessor, the new RackStation series units deliver 3.6X higher compute performance, 3.8X random read IOPS at 108K, and 2.3x higher sequential write performance at 1,147 MB/s.
This basically translates to faster performance in data management and backup tasks, while also allowing businesses to scale to higher numbers of concurrent users and services, and the same time maintain a high performance output.
Compact servers for space-sensitive deployments
At only 306.6 mm and 407.5 mm deep (including front server handles), the RackStation RS1221+ and RS1221RP+ storage servers are less than half the depth of standard 2U rackmounted devices, making them ideal for smaller rackmount enclosures, such as wall mounted cabinets, or two-post racks (RS1221+ only), where space is at a premium.
The RackStation RS1221+ and RP+ storage server units are configured with 4 GB of DDR4 ECC memory by default, upgradable to 32 GB. Its PCIe 3.0 slot enables easy upgrading to 10GbE with a compatible NIC, or to add super-fast NVMe cache via Synology M.2 cards and Synology SVN3000 series SSDs.
These rackmounted server units can scale to 12 drive bays using an RX418 expansion unit and compatible drives. For businesses wanting extended support, its 3-year limited warranty and can be extended to 5 years.
Efficient data management and protection
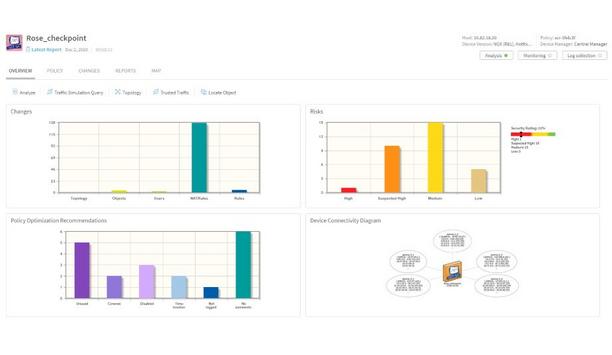
Synology DSM enables backup of IT infrastructure with the Synology Active Backup suite
Synology Diskstation Manager (DSM), Synology's unified operating system, simplifies difficult and cumbersome data management processes while still giving users ample control over decisions that matter.
Synology DSM enables backup of IT infrastructure with the Synology Active Backup suite and hosting of on-premises private cloud with Synology Drive, virtual machines with Virtual Machine Manager, mail servers with MailPlus, and other SaaS services.
Global availability
RS1221+ and RS1221RP+ are available from Synology resellers globally.
- The predecessor, the RS1219+ contains an Intel Atom C2538 processor.
- Performance figures are achieved in the Synology lab with optimized network and configuration settings. Actual performance could vary in different environments. Comparison done against prior-generation RS1219+.
- Check compatibility list for compatible Network Interface Cards.
- 2 SSD cache can be enabled using the E10M20-T1 and M2D20 M.2 SSD adapter cards with Synology SNV3500 or SNV3400 NVMe SSDs. SSD caching is also supported via SFF (2.5") SSDs.
- The capacity of the RS1221+ and RS1221RP+ can be expanded using a Synology RX418 expansion unit, purchased separately.
- Supports LFF (3.5 inch) or SFF (2.5 inch) SATA drives. Check compatibility list for validated drives.
- RS1221+ and RS1221RP+ include a 3-year limited hardware warranty, which can be extended to 5-years with the optional EW201 bundle, a 7-year Extended Warranty service add-on.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance