Protecting power grids is essential to deliver electricity that serves millions of consumers. Transmission substations are a component of the power infrastructure that presents unique security challenges. These important facilities often sit out in the open, in remote locations, and were historically protected by little more than cameras or chain-link fences.
Much of the current concern about securing electrical substations in the United States originated in response to a 2013 sniper attack, using military-style weapons, on Pacific Gas and Electric Company’s Metcalf Transmission Substation in Coyote, Calif., near San Jose. Gunmen fired on 17 electrical transformers, resulting in more than $15 million in damage. The crime is still unsolved.
Security Critical Infrastructure
The North American Electric Reliability Corporation’s Critical Infrastructure Protection (NERC/CIP) guidelines emerged in the aftermath of the attack, triggering growth in security spending to protect utilities.
The latest NERC/CIP Version 6 standards were issued in January 2016, with deadlines of various phases falling in July 2016, April 2017, and the final phase to be completed in September 2018. The earlier deadlines were for high- and medium-risk facilities, and the future deadline covers lower-risk areas. The standards target four areas of concern securing utility sites: security awareness, physical security, remote access connections, and incident response. Although medium- and high-impact facilities tend to be more critical, the connected nature of utility infrastructure means that security is only as strong as the weakest link.
Perimeter Security Requirements
Every facility has a baseline requirement for perimeter security protection around the site, although medium- and high-impact sites will have more stringent requirements. The geography surrounding sites – Is it an urban area or rural? Does the surrounding elevation provide additional lines of sight? – also impacts the types of systems they require.
A lack of similar incidents since the 2013 Metcalf attack could fuel debate on whether the extra security was necessary, and could even lead to a sense of complacency. “A lot of money has been spent on fancy systems at the top tier,” says Greg Hendrix, Sales Lead at Tyco Integrated Security. “But nothing has happened since Metcalf. The concern is that we could lull ourselves into a sense of everything’s OK. We need to find a balance between what’s appropriate and what isn’t, and it’s a moving target. There is no silver bullet.”
With 35 years in the physical security industry, Hendrix manages a specialized team of 12 pre-sale field engineers that focus on designing electronic security solutions for complex needs as part of Johnson Controls’ Centers of Excellence network.
 |
| Every facility has a baseline requirement for perimeter security protection around the site, although medium- and high-impact sites will have more stringent requirements |
Cameras And Access Control For High-security Facilities
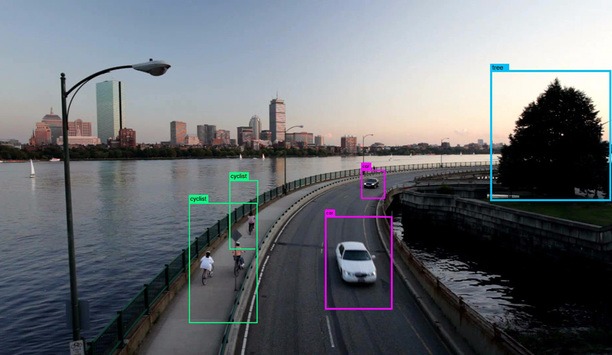
Hendrix assisted one utility industry customer as a primary design engineer for nine high-impact sites. The sites were high- to medium-tier sites that are part of the nation’s critical infrastructure. Thermal cameras with analytics were positioned to detect intrusions and discern between wildlife and human intruders. Avoiding false alarms is crucial if, for instance, 300 cameras are monitored at a single site. The analytics systems were augmented with pan-tilt-zoom cameras that could be directed to view intruders. Analytics zones were used to trigger large LED light panels to flood various zones with light in case of an intruder. If an intruder gets even closer, it would trigger a recorded voice to tell them to leave.
Metal fences that were 12 feet high and even concrete were used to protect lines of sight to provide a ballistics barrier against gunshots. Mountainous or hilly areas presented additional challenges, as someone could position themselves above the fence line. In some cases, automated gates use multi-factor access control readers (cards and PINs) to allow vehicles to pass and then to close behind them. In other instances, pedestrian-only gates are used, requiring vehicles to remain parked outside the perimeter. Video surveillance watches entrances and exits.
Compliance With NERC/CIP Regulations
Connecting IP cameras into a utility’s IT system, or even using a laptop to program a video system, can introduce cybersecurity vulnerabilities. The idea is not to contribute to the cybersecurity challenges utilities already face to protect the supervisory control and data acquisition (SCADA) monitoring systems and programmable logic controllers (PLCs) used in daily operations.
“The physical threat is evident, but the cybersecurity threat is not so obvious,” says Hendrix. “To focus on one without the other doesn’t make a lot of sense. The physical security folks focus on how we can physically detect and deter, and promote visibility. But we have to remind ourselves that the security of the cyber connection is critical. Security awareness applies to us as integrators as much as customers. We have to find an IT guru within the organization and make sure we are working together.”
Failure to adhere to NERC/CIP requirements, which are enforced using audits, trigger fines that could put the profitability of private utility companies at risk. “There is an opportunity for integrators to partner with customers and identify how to appropriately meet the requirements within budget and get these projects done,” says Hendrix. Among the audit requirements is a log showing who comes and goes at a facility; access control systems collect that information and provide the needed documentation. Employees are issued cards, and contractors and other visitors are required to be escorted by approved personnel into and out of a site. For frequent visitors and contractors, a credential can be issued. Promoting awareness of such policies and requirements is another factor in CIP compliance.
Discover how AI, biometrics, and analytics are transforming casino security