Over the past year, companies have had to deal with the COVID-19 pandemic and how it has affected their operations. From new digital services through to security, the response to more hybrid and remote working showed some of the assumptions that we have made over the years, and it required companies to innovate and fill those gaps.
Physical and IT security was no exception to this. In the rush to support home working, many IT security teams realised how much they rely on physical security to help with their identity management approaches. To adapt to what is taking place now, identity management has to evolve too.
Challenging our assumptions around identity management
Identity management involves ensuring that authorized and authenticated individuals can get access to the tools and data they need to work, and restricting access from those that don’t. Identification is establishing who a user is, and then authentication verifies someone is who they say they are through a combination of different methods or factors linked to who they are, what device they are using, what they know, and what they have.
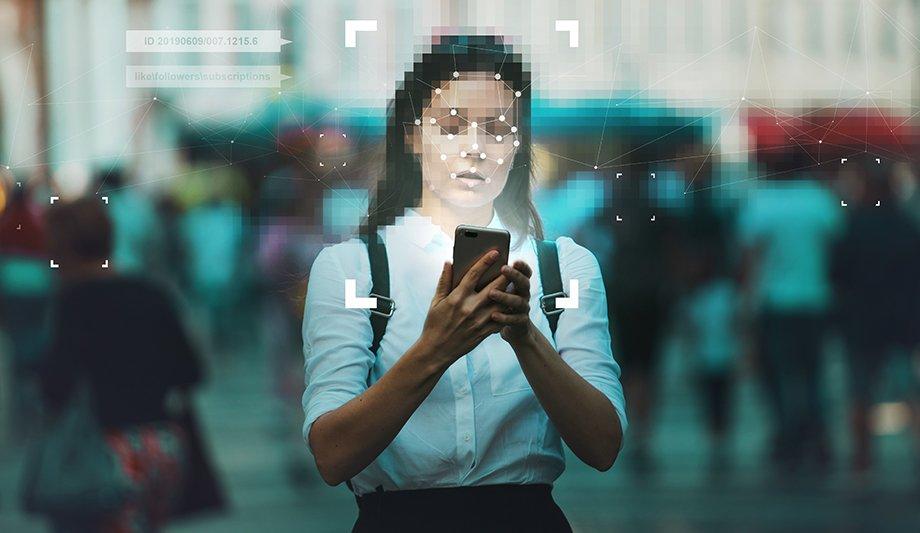
Physical security provides an identity perimeter by restricting device access to only those that are allowed to enter a location, whether this is through using technology like smart cards or biometrics through to people managing who can enter the building at reception. With this boundary in place, using a combination of username and password is enough to meet security requirements. A more ‘zero trust’ approach is needed where we trust nothing and verify everything
However, the pandemic took this away. For many IT security teams, this showed how much they had taken physical security for granted in their security planning. Alongside having to provide remote access that is secure, these teams had to think about how to manage identities securely as well. The default approach of username and password is not enough when everyone can be working on any device and from essentially any location. Instead, identity has become the new perimeter. The new office is wherever a user and device are, and authentication must change that we can prove people are who they say they are.
A more ‘zero trust’ approach is needed where we trust nothing and verify everything. The mindset behind zero trust security is to regard all sources of network traffic, both external and internal, as potential routes for attacks. Therefore, all users and resources must be verified and authenticated wherever they come from, system data must be collected and analyzed for risks, and network access and traffic must be limited and monitored. While it may seem a bit paranoid, zero-trust security is rooted in the realities of the cloud computing age.
Multi-factor authentication or MFA can be used to add more types and factors for authentication. So, in addition to something you know like a password, you can use something you have as well. This would typically be a one time password sent to the user’s phone or from a cellphone authenticator app, which fills the role of something they have. Managing this at any scale requires work. For large companies with established processes and identity management strategies, this would be something they could add on as part of that remote working implementation. However, for many smaller businesses that don’t have established IT directories or that have a wide range of different and new applications in place to support, it is more challenging.
Everything is different
One reason for this is the sheer variety of IT assets, devices, and applications that now have to be supported. Rather than the IT-designed network of machines that is standardized and fully controlled, we today have a far wider range of devices, operating systems and locations in play. Alongside this, there is the issue of controlling access to cloud-based services and Software-as-a-Service (SaaS) applications, which have also grown in popularity.
The traditional IT directory that is normally used as the starting point for identity management is not normally equipped to manage the modern identity landscape. Looking at cloud-based directories is therefore a worthwhile step, as these are built to manage Identities, SaaS applications and VPNs and also support both multiple operating systems and the wide range of different devices that today’s users have.
From a physical security perspective, identity and access management can be an area to develop. While the need for building access is reduced at the moment, it will return when the pandemic ends. In these circumstances, new approaches may also be needed. For example, fingerprint biometric security processes are popular to fill the requirement around verifying that someone is who they say they are. However, traditional approaches like fingerprint scanners may be less popular as they require users to touch the readers. For high traffic locations with lots of people, that will be a risk.
Instead, combining access and identity can be made easier through approaches that take advantage of the new flexibility that pandemic responses needed. For example, using the physical access control support in today’s smartphones can enable organizations to use biometric fingerprint readers or face recognition without having to enforce everyone using the same biometric reader. By linking to phone applications that employees have on their devices, fingerprints or other forms of biometric data can be used to grant access.
Thinking about context
Looking into the future, many of us are looking forward to things going back to the way that they were before the pandemic. However, there are a lot of things that we had to adapt and use to keep operations running and secure during lockdown that we should continue to make use of. Rather than simply going back, we should look ahead at a more hybrid approach to everything, including security.
This includes looking at context for identity and access management. Rather than simple approaches that are either too insecure or overkill for employees, we can set out situations that match the most common working situations and then enforce some rules on when access is granted. For this, we can look at how to use authentication and access control more effectively alongside other security factors. As we move to a more hybrid way of working, this flexibility of approach will be necessary to cope with all the different scenarios that employees will be in
The first element here is the devices that users have. Trusted devices can be their own factor for authentication, where a device trust can be set up with a specific user account and linked to a specific device like a PC, laptop or tablet. If the user is not using one of those devices, then they can have an additional factor for authentication used, such as entering a one-time password from their cellphone or a cellphone push authentication. This approach does not restrict users that may need to work from other devices occasionally, but it does protect against theft of passwords or dictionary attacks on credentials.
The second element is location. When users connect, they will use an IP address that connects them to a network either in the office, to their home provider, or to a public network. Depending on the circumstances, you can put rules in place on how you manage those connections. For a user that is in the office, they may get access automatically in the same way they used to.
With conditional access based on geolocation, user access can be allowed or blocked based on a user’s physical location or challenged with a step-up authentication. For example, your business may be based in the UK and with offices in Europe. Getting an access request from India or China may not be legitimate, so IP addresses from those countries can be automatically blocked. Alternatively, if you do have staff that will travel to those countries, then access can be dependent on using a known device and authentication step before signing in.
The approach here is to use conditional access based on identity, location, and device and make access as simple as possible for the user and without causing excess risk to the organization. By looking at specific circumstances and context, you can design your access management approach to fit the user. As we move to a more hybrid way of working, this flexibility of approach will be necessary to cope with all the different scenarios that employees will be in.