 |
| Differences between standard data applications and the requirements of networks designed for IP video security applications are critical for your system's performance |
When the need to purchase a network switch arises, many IT directors immediately turn to two favorites, HP or Cisco. They have become to the networking environment what IBM was to computers: “No one ever got fired for buying IBM.” Certainly, switches play a crucial role in enhancing your network by increasing its speed and capacity. However, it is equally important to note that they can also slow down your network and the same is explained in the article by Neil Heller - Vice President, Vigitron, Inc.
With the transition of video security systems from analog to digital, IT network directors overlooked a key point in their rush to expand their jurisdiction over networking by adding the video security element. The fact is, IP video security networking requirements are not the same as those used for data networks. True, video transmitted over a network is data, but that is where the similarities end.
Network switch and its worthiness to IP camera
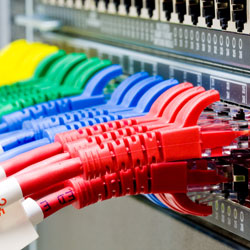
Nowhere are the differences more apparent than related to network switches and midspans. Let’s start by examining a standard network switch and its non-functional relationship to IP video security cameras.
We will begin at the switch port. In networking, information is transmitted in the form of packets. For most network switches, when the port is set at 100Mbps, the packet size is limited to about 1518 bytes. This is equal to about a two to three megapixel camera depending on the codec used, H.264 generating the smallest packet size and MJPEG the largest. Some switches that have port speeds to 1Gbyte can be programmed up to the Jumbo Frame, which defines packet sizes greater than 1581 bytes. Jumbo Frames are those that range between 1518 bytes and 9600 bytes. This latter ability wouldn’t present a problem with the exception that in networking, the output speed of a device must be matched to the input speed of the port.
As all IP cameras have output bandwidth speeds of 100Mbps, the input speed of the port must be set to 100Mbps. If the switch has an automatic port speed setting, it will sense the input speed from the camera and no manual setting is required. The problem exists when the packet output from the camera exceeds the limitation of the switch port setting at 100Mbps. In short, you can have issues with any cameras that are 3MP or greater.
If an NVR or VMS server is not communicating with an individual camera, you don’t know if the problem exists at control site device or the camera. Little consideration is given to the idea the problem may be the switch port and camera |
Switch fabric estimation
The second concern is the internal switch connection between all the ports. This is called the switch fabric or throughput. In most normal data applications, either not all ports are used or the data at each port is far less than the port’s highest capacity. Again, this is not the case with IP video security applications where all ports are used and each port needs to operate at its highest bandwidth capacity. For this requirement, the switch fabric must be able to handle at least two times the total bandwidth of all the ports. For example, if you have a 24 port, each port with the ability to operate at 1Gbytes, the switch fabric must have a bandwidth of at least 48Gbyte. Please note, there are no standards for switch fabric or port bandwidth packet size capacity. These are both quality issues.
The potential problems become clear as the megapixel size of a camera increases, as does the camera’s codec, and as the number of cameras in your system approach the maximum number of switch ports connected. The problem is often misunderstood. Operators don’t know why they only have good video quality when the camera capacity is less than the switch input maximum.
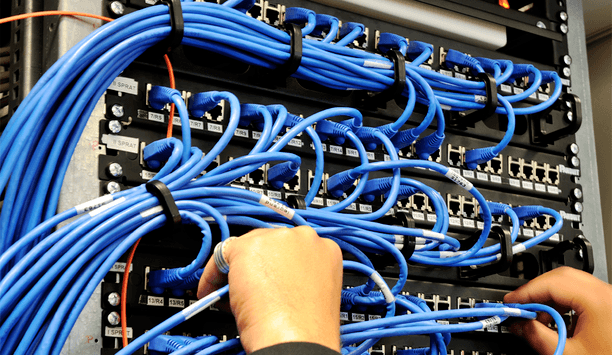
PoE-related concerns
Just as critical is the interaction between switch functions, or lack thereof, concerning PoE. Many of these center around the lack of protection. This starts with the individual port, which is not fused. Shorts in any individual channel can render the entire switch inoperable when the main power fuse is broken. During normal startup, PoE power required by each connected camera is sensed. If a short exists, or no camera is detected, or the amount of power requested by the camera exceeds the available port, the port will shut down. This is a function of the normal safety built into the 802.3 standards designed for PoE. When this occurs, the port is basically off and remains in the off condition as the physical Ethernet connection between the camera and switch port has already been established and new detection pulses are not generated.
There are several reasons this can occur. Even in properly installed systems, a good port-to-camera connection is not always established on the first try. Again, blame usually is placed on the camera. In some case, removing the Ethernet cable and reinserting will reestablish the connection. However, the first reactions are most likely to request a return authorization from the manufacturer or ask for a service call from the dealer.
The second PoE-related problem is best illustrated by an actual installation. Several schools in a distant had PTZ cameras with more than half their inputs into a single PoE switch. As PoE power was applied, the PTZ domes move to their reference position, resulting in a surge so great that it damaged the switch’s power supply. While the safety built into the 802.3 standard can protect the individual port, it does not account for potential high power surges at the actual startup. For PTZs and other accessory features, the surge occurs only after initial communication is established and PoE power applied. The standard only applies to sensing the need for PoE, and if the PoE power requested is available. There is no protection against surges or the number of ports within a switch that are subject to surges.
During normal operation, |
During normal operation, a PoE network switch has no ability to account for surges occurring from PTZ, LED, Day/Night, Auto Backfocus, and other accessory features. If these occurrences have durations of greater than approximately 40ms or require more power than available at the port, port PoE will simply shut down, rendering the camera useless. This is a concern when the normal operating power of the power of the camera is at the edge of an individual power class and the surge exceeds that class power limit.
Within a network, connected devices pass through the switch. There is no connection accountability between the switch port and device connected to it. As such if an NVR or VMS server is not communicating with an individual camera, you don’t know if the problem exists at control site device or the camera. Little consideration is given to the idea the problem may be the switch port and camera.
Finally, there is the AUPC, or Actual Usable Port Count. A 24-port switch does actually have 24 ports, but when you consider that a least one port is connected to the recording or viewing device, the usable port count is reduced to 23, if the switch is connected in a series then you use two ports and the count is further reduced to 22.
All of these define the differences between standard data applications and the requirements of networks designed for IP video security applications. These differences are not defined by nor part of any of the standards that govern compatibility in networking standards. They are, however, critical in the performance and reliability of your security system.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance