|
| The advent of IP security cameras has resulted in the need to maintain existing coax cable for networking applications |
Transmission of video and PoE power for IP security cameras over infrastructures can be confusing. Network infrastructures are designed using twisted pair cabling that we refer to as CAT (short for Category) cable, also referred to as UTP (Unshielded Twisted Pair). Security systems, coming from an analog environment, have historically transmitted over coax cable, and with the use adaptors can transmit over CAT cabling, which can be further broken down into single pair twist and untwisted applications.
Cabling shares one, often misunderstood commonality. Any physical medium has a form of resistance to any element carried on that cable. With regard to network transmission over CAT 5 and greater (5e, 6, 7), there is a distance limitation of 328 feet or 100 meters. The applicable standards state that the bandwidth applied at one end of the cable at 10/100/1000 (1G)Mbps will be realized at the other end. This is also where we find the first limitation. At this same 328-foot distance there is a loss of PoE power. 802.3af or 15.4 watts is a value realized only at the PoE source. Under the standard, after traveling through 328 feet, the power at the camera is 12.95 watts. The same is true for 802.3at which has a source power of 30 watts and 328-foot distance power of 25 watts.
The advent of IP security cameras has resulted in the need to maintain existing coax cable for networking applications. The first thing to realize is there are no standards for network transmission over coax. In reality the characteristics governing coax can be considered the opposite of CAT twisted pair cable. CAT cabling for network transmission consists of 4 wire pair, 2 of which are used for signal and PoE transmission. This ability to separate PoE and bandwidth transmitting over two pairs maximises power transmission. Coax cable, when used in the same application, is limited to a single pair – center conductor and shield. Its characteristics promote bandwidth but limit PoE transmission compared to UTP cable. I emphasize again, there are no standards for coax cable transmission.
This process becomes more confusing when you realize there are various type of cables that are called either UTP or Coax. All of these cable have different characteristics that have a direct impact on their ability to transmit bandwidth and PoE. The standards for UTP transmission were set for CAT 5 (5e). Categories 6, 7 and above will tend to have lower cable resistance and longer transmission distance; CAT 3, higher resistance and shorter distance.
| |
| Common types of coax cable have varying distance limitations |
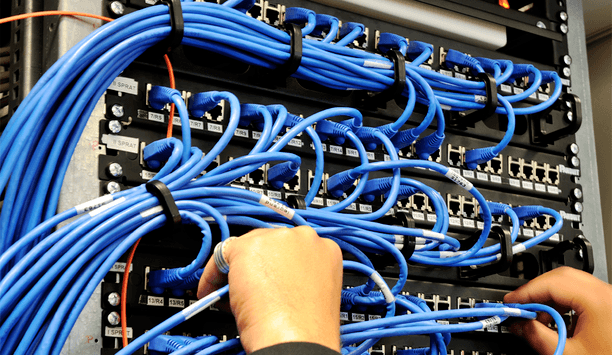
The same applies to coax cable. Again there is no standard, the typical cable found in analog security applications is RG-59. In general, application distance limitations ran between 750 to 1000 feet, greater than the 328 network limitation. This is why extenders are required to convert from coax to UTP and to extend the signal and power range. As with UTP cable, there are two similarities. First, there are different grades of coax; second, there are different types. All these differences generally apply to cable resistance and therefore distance performance. The most common types of coax cable are: RG 59, RG 6 and RG 11
Why is this important? In general there are two reasons. The first is in specifying equipment for a video security system, you are generally dealing with existing wiring and a fixed performance requirement. It is important to know the type and condition of the wiring in order to know what system performance requirements can be met. Second is a function of understanding specifications for the transmission equipment that will be used in the infrastructure. As noted, when maintaining coax, the use of coax-to-Ethernet convertors/extenders is required. In many cases even when UTP is used, distances over the 328-foot limit are required.
A manufacturer’s product specification sheet can truthfully state their products can perform at 100 Mbps, they can handle 802.3at 30 watts and they can transmit distances up to 6,000 feet. However these must be viewed as separate performance claims. The key word is separate. Notice in these statements there is nothing that ties 100Mbps and/or 30 watts (these are examples only) and claimed distance of 6,000 feet together. Neither is the type of cable used indicated. By themselves, each individual claim is truthful; however, applications require they work together, and this is usually not the case. Many times it is difficult to read between the lines of manufacturer’s specifications. Failure to do so can cost additional time, money and even lead to removing the infrastructure itself.
There is a simple answer. Call the manufacturer and have them confirm that their solution will perform as required for your specific application. If necessary, ask for proof that they have conducted testing to support their performance claims. Infrastructure is confusing, and you don’t need to be an expert, you just need to ask the right person(s) the right questions.
Discover how AI, biometrics, and analytics are transforming casino security