Expertise in safety-critical equipment for the rail industry has won significant contracts for Pickersgill-Kaye (Kaye), this time from Nabtesco Corporation, a Japanese firm manufacturing high performance train door operating units for the global market.
Kaye and Nabtesco Corporation’s Italian subsidiary, Nabtesco-Oclap, jointly developed the Emergency Egress Device (EED) and Emergency Access Devices (EAD) for power doors currently being supplied by Nabtesco Oclap into a UK rail vehicle manufacturer for UK and Thailand operated new build vehicles.
Supplying Emergency Egress And Access Units
We have worked together to design suitable safety equipment for all their units that can be used on vehicles around the world"Leeds-based rail industry specialist Kaye, whose range is part of the High Security & Safety Group, a division of ASSA ABLOY Opening Solutions UK and Ireland, is one of the most trusted names in access control solutions. The business has already sealed a deal with Nabtesco for supplying over 1000 Emergency Egress and Emergency Access Units that will be fitted to newly built vehicles for a huge suburban commuter network under construction in Thailand and for new train projects in the UK.
Andy Hewitt, Kaye’s Rail Sales Manager, said: “Nabtesco-Oclap needed European-style EED and EAD devices for the train door gear it was manufacturing so they approached us. We have worked together to design suitable safety equipment for all their units that can be used on vehicles around the world, hence the UK and Thailand jobs.”
Reliable And Cost Competitive Products
Nabtesco-Oclap’s Commercial Director, Stefano Losito, added: “Kaye has a lot of experience developing EED and EADs. They offer very reliable and cost competitive products. We are delighted to be working with them and look forward to doing so in the future.”
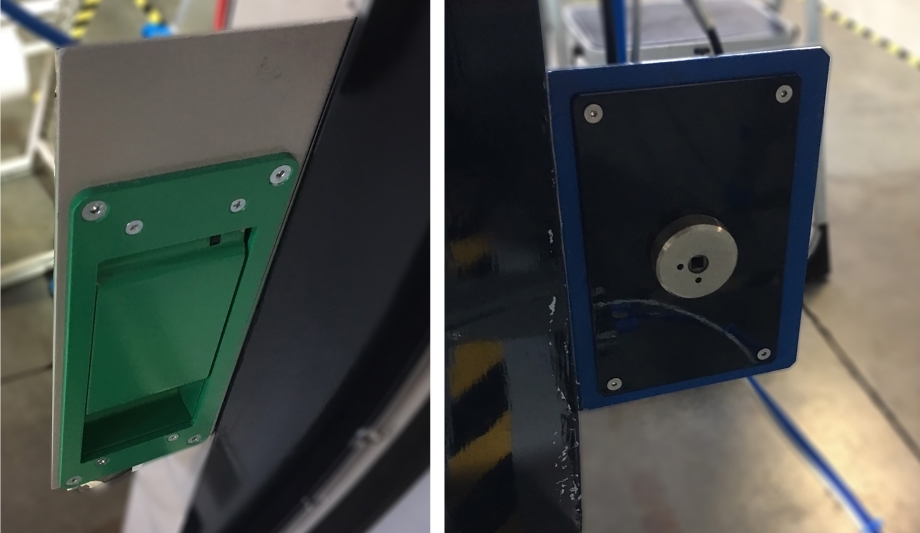
Kaye’s EED and EAD kit comprise a handle which when pulled activates an electric switch that alerts the driver to the operation of the devices but prevents the door being opened while the vehicles are moving. If after a set time the driver fails to respond, the train will automatically stop.
Kaye has built a solid reputation through the specialist design and manufacture of door locks and security systems
Supplying essential safety critical equipment for the rail industry, such as internal egress and external access devices, has been at the heart of Kaye’s success. It has built a solid reputation through the specialist design and manufacture of door locks and security systems. Custom-built equipment and standard products, including pre-production models, can all be made to order at its flagship center of excellence in Leeds.
R&D Hub To Boost Sales
Owner ASSA ABLOY’s comprehensive renovation has turned Kaye’s manufacturing facility into an R&D hub for rail technology to further boost sales and help the business compete successfully on the global stage, designing and engineering the innovative solutions that train builders will require in the future.
Nabtesco turned to Kaye for its safety critical systems because the Yorkshire company is a leader in safety critical equipment, guaranteeing products are manufactured with high quality materials and meet regulatory industry standards and specifications for the safe operation of trains, stations and infrastructure.