PCSC Access Controllers (11)
Browse Access Controllers
- Controller Type
- Networkable
- Standalone
- Standalone/Networkable
- Make
- PCSC
Access control controller products updated recently
Access control controllers - Expert commentary

In this article, Peter Jackson, Managing Director at Jacksons Fencing, emphasizes the significance of implementing and upholding robust security measures, highlighting their role i...

A study found that over 80% of smartphones have biometric protection enabled, up from 68% a few years ago - these statistics alone show the trajectory of biometric security solutio...
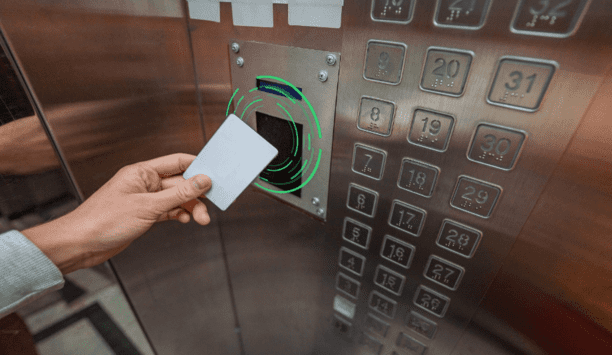
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from buil...
Latest PCSC news

PCSC, a designer and manufacturer of access control solutions and Coolfire Solutions, a St. Louis based software company known for creating Military-Grade situational awareness pla...

The BioConnect Identity Platform provides an integration of Suprema's biometric solutions with the majority of leading access control systems BioConnect and Sup...
Systems may be reliable and performing as originally intended, but can also beoutdated in comparison to current technology offerings Let’s start by defini...
Related white papers
Cybersecurity in Keyless Access Management
Three Essential Reasons To Upgrade Your Access Control Technology In 2022
Securing Unmanned Infrastructure at the Network Edge
Healthcare security articles
Just like fighting against the spread of disease in a clinical environment, healthcare providers must mobilize, coordinate with interconnected partners, and apply sufficient budgetary resources to com...
According to the U.S. Occupational Safety and Health Administration (“OSHA”), hospitals are considered one of the most dangerous places to work in America. In fact, OSHA&nbs...
The Security Executive Council, with Rice University and MD Anderson Cancer Center, will facilitate a day and a half of expert-led sessions on workplace violence risk management for corporate security...
At Hannover Messe 2024, Siemens presents the first generative artificial intelligence (AI) product for engineering in an industrial environment. Siemens Industrial Copilot The Siemens Industrial Cop...
HID, the pioneer in trusted identity solutions, announces it has been positioned by Gartner® as a Pioneer in its 2024 Magic Quadrant for Indoor Location Services. The evaluation was based on speci...
Vismo will launch the latest version of its Locate & Protect App at the International Association for Healthcare Security and Safety (IAHSS) Annual Conference and Exhibition 2024, at booth #713, f...
ASSA ABLOY Opening Solutions will be exhibiting an expanded range of innovative products at booth #8061 during ISC West. With access and intrusion risks rising in schools, healthcare spaces, and worsh...
Cohesity, a pioneer in AI-powered data security and management, announced it is collaborating with Intel to bring Intel’s confidential computing capabilities to the Cohesity Data Cloud. Leverage...
Identiv, Inc., a global digital security and identification pioneer in the Internet of Things (IoT), has entered into a definitive asset purchase agreement to sell its physical security, access card,...
Thailand’s pioneering fair for security and fire safety for commercial and industrial premises, announced at the press conference at Grand Hyatt Erawan Bangkok that the 2024 edition will return...
ASIS International, the world’s largest association for security management professionals, announced its keynote lineup for the hybrid Global Security Exchange (GSX) 2024, taking place on 23-25...
NetSPI, the proactive security solution, has announced its achievement of CBEST accreditation, marking a significant milestone in its commitment to delivering high-value penetration testing and red te...
In an era when digital technology intertwines with everyday life, the healthcare sector stands at the forefront of adopting innovative solutions to safeguard sensitive information. Among these technol...
With 5G, AI, and IoT technologies maturing, the accelerating demand for AI-based security and safety solutions makes Secutech the ideal place for system integrators, distributors, and property develop...
3xLOGIC, a pioneering provider of integrated and intelligent security and business solutions, will debut its recently launched edge-based deep learning analytics cameras at The Security Event 2024. Th...
Mobile access articles
Zenitel, a provider of intelligent communication solutions, announced the launch of two new door entry intercoms: the Turbine Extended Intercoms TEIV1+ and the TEIV4+. The new products display Zenite...
Physical security is essential for a modern production facility, users don’t want just anyone entering the building or accessing secure areas. But what about production machinery? Machine authe...
Interface Systems, a major managed service provider of business security, actionable insights, and purpose-built networks for multi-location businesses, announced that it is releasing an enhanced cust...
Federation of Gujarat Industries (FG)), Vadodara has conferred the Outstanding MSME Excellence Award at the 18th FGI Awards presentation ceremony. The objective behind the institution of these awards...
Geekplus, the global pioneer in mobile robot and smart logistics solutions, has deployed the first Shelf-to-Person PopPick project in the Nordics for one of the biggest online pharmacy wholesaler...
The Cygnus ALERT notification and monitoring platform is a cloud-based solution designed to strengthen site safety. Using Cygnus ALERT, construction professionals and site administrators can receiv...
Hanwha Vision is announcing that its Q series cameras will be fully compatible with Genetec™ Security Center SaaS, the company’s newly announced unified software-as-a-service solution. Ge...
Smart Spaces announces that it has partnered with the trusted identity provider, HID, to make access to Workspace’s The Light Bulb building in South West London fast, simple, and secure, by maki...
IDEMIA Secure Transactions (IST) once again demonstrates its post-quantum leadership, announcing the first crypto-agility solution that will enable service providers of secure products, such as banks...
SwiftConnect is thrilled to celebrate its Elite status in the HID Origo Technology Partner program, which is dedicated to partners with a focus on mobile technologies. The Elite premium tier of HID&r...
Nuke From Orbit, a UK fintech startup, has unveiled findings from its latest research report, ‘Evolving smartphone usage and the growing threat to consumers’. The report sheds light on a...
ASIS International, a major authority in security standards and guidelines, proudly announces the release of an American National Standards Institute (ANSI)-approved standard dedicated to security ris...
A major access management business is gearing up for a trio of industry awards. The Key Safe Company, which supplies police preferred key safes and security products, has secured several industry awar...
RecFaces, a facial recognition software company, has announced the successful deployment of its flagship product, Id-Guard at Jorge Chávez International Airport in Lima, Peru. This implementat...
In a collaborative move with the W3C Consortium, Siemens and Microsoft have announced their commitment to converge the Digital Twin Definition Language (DTDL) with the Thing Description standard from...
Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
DownloadAre You Ready For An On-Site Emergency?
DownloadIntegrating IT & Physical Security Teams
DownloadHikvision NVR 5.0 and Full Line Hardware Storage Solution
DownloadBank Security
Download- Madrid Multi-Residential Complex Streamlines Operations With Mobile Digital Access
- Central African Mining Firm Amplifies Efficiency With Matrix's Solutions
- Fashion Label Elevates Security With Matrix's Elevator Access Control
- ExpoFactory Increases Booth Security With ASSA ABLOY's Digital PIN Door Lock Solution