A lot has been said about door security — from reinforced door frames to locking mechanisms to the door construction — all of which is crucial. But what security measures are in place beyond the perimeter door in case the worst happens and it’s somehow breached?
Hopefully, many more levels of access control are in place to prevent, or at least slow down, a perpetrator’s ability to compromise protected assets.
Additional interior layers
Interior security measures must operate as an integrated, multilayered system that eliminates single points of failure. These inner protections safeguard not only the physical infrastructure but also the operational integrity, confidentiality, and availability of the systems housed within.
Beyond simply preventing unauthorized individuals from getting inside, the goal is to create a controlled, monitored, and resilient environment in which every movement, action, and access attempt is verified, logged, and, when necessary, challenged. As modern buildings, data centers, and infrastructure sites host critical functions and potentially sensitive intellectual property, these additional interior layers become essential to protecting both organizations and their proprietary assets.
Interior security controls
One of the most important interior security controls is granular access segmentation
One of the most important interior security controls is granular access segmentation. While a perimeter door may verify an individual’s right to enter the building, the interior should treat every room, cage, and corridor as its own security zone. Role-based access control and strict least-privilege principles should limit personnel to only the areas they absolutely require.
For example, a network engineer may need access to routing equipment but not storage racks; a janitorial contractor might be allowed into shared hallways but not any equipment rooms at all. These access restrictions should be enforced using intelligent keys, biometric scanners, mantraps, and, at particularly sensitive locations, two-factor authentication. Segmenting access in this way limits the potential damage from a single compromised badge or insider threat and ensures that a single breach does not cascade into a total facility compromise.
Low-light and infrared capabilities
Biometric authentication within a building adds a layer of confidence beyond perimeter controls. Technologies such as facial identification help prevent the use of stolen, cloned, or borrowed credentials. These systems complement anti-tailgating measures, such as sally ports or mantraps, which ensure that only one authenticated person passes through at a time.
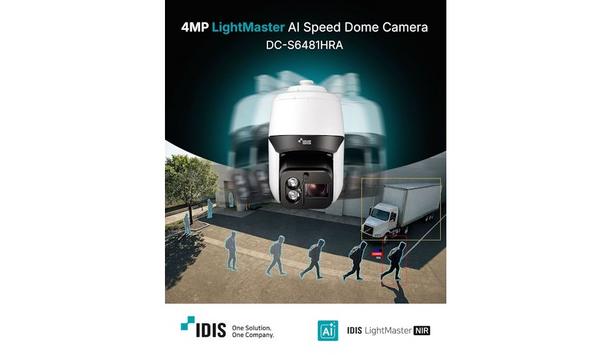
Interior surveillance is another essential measure. High-resolution cameras equipped with low-light and infrared capabilities should cover every hallway, door, rack row, and logistical pathway.
Camera feeds must be continuously recorded, and retention policies must align with regulatory requirements. Intelligent video analytics, such as motion pattern recognition and heat mapping, enable the detection of atypical behaviors — such as someone lingering near a cage they are not authorized to access or movement at odd hours.
Physical tamper-detection mechanisms
Cabinet security provides a vital layer of granularity in the access hierarchy, ensuring that even within secure facilities
Integrating surveillance with access control systems creates a strong correlation; when someone successfully passes through a secured door and enters a room, the system can track whether the number of people seen on camera matches the number authenticated, and alert security if a discrepancy occurs.
However, it is increasingly important that access control not stop at the room level, because the most sensitive assets are often housed in cabinets, racks, or storage units within already-secured spaces. Cabinet security provides a vital layer of granularity in the access hierarchy, ensuring that even within secure facilities, assets remain protected.
Physical tamper-detection mechanisms on racks, cable trays, and server chassis add another dimension: they can detect if a panel is opened, a cable is unplugged, or a device is removed without authorization.
Secure destruction protocols
Another internal measure is the use of secure storage and chain-of-custody procedures for any components that contain intellectual property or personally identifiable information. Hard drives, backup media, and even printouts should be stored in locked cabinets accessible only to people with proper clearance.
When decommissioning hardware, secure destruction protocols such as shredding or degaussing should be performed in controlled areas and thoroughly logged. Every movement of sensitive equipment should be traceable, from installation through end-of-life disposal. Such processes reduce the risk of data leakage from improperly discarded or undocumented devices.
Consequences of improper behavior
Staff should be trained to recognize social engineering attempts, unusual behaviors, and procedural deviations
Operational security procedures also contribute significantly to interior protection. Background checks, ongoing employee vetting, and mandatory training ensure that individuals with access to sensitive areas understand their responsibilities and the consequences of improper behavior. Staff should be trained to recognize social engineering attempts, unusual behaviors, and procedural deviations.
Maintaining a strict visitor escort policy prevents non-employees from wandering unobserved. All visitors should wear highly visible identification badges and be monitored continuously by authorized personnel. The building's interior should be treated as a controlled environment at all times, not merely a workspace.
Continuous auditing and logging form
Continuous auditing and logging form another pillar of interior security. Access logs from intelligent keys, biometrics, video, and environmental systems must be stored securely and evaluated regularly for anomalies. Automated systems can flag irregular patterns, such as repeated attempts to access unauthorized areas or entering rooms at odd hours.
Manual audits validate that the access control list remains accurate, that no inactive or former employees retain credentials, and that documentation matches reality on the floor. These logs are indispensable during investigations, compliance assessments, and incident response efforts.
Interior security controls
Security networks should be isolated from the main IT networks to prevent a cyber incident
Finally, redundancy and resiliency must be built into interior security controls. Electrical power for access control, intelligent keys, biometrics, and video systems should be backed by secondary sources, generators, or uninterruptible power supplies.
Security networks should be isolated from the main IT networks to prevent a cyber incident from disabling physical protections. The goal is to ensure that interior security remains functional even during outages, disasters, or cyber disruptions.
Multilayered approach
Together, these additional interior measures create a layered defense that makes a secure building, data center, or infrastructure site extremely difficult to compromise. Rather than relying on a single barrier at the entrance, the environment becomes an ecosystem of mutually reinforcing controls — physical, operational, digital, and procedural.
This multilayered approach allows structures to maintain high levels of protection even as threats evolve, ensuring that the systems inside remain secure, resilient, and trustworthy.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance