With the coming of a New Year, we know these things to be certain: death, taxes, and… security breaches. No doubt, some of you are making personal resolutions to improve your physical and financial health. But what about your organization’s web and mobile application security? Any set of New Year’s resolutions is incomplete without plans for protecting some of the most important customer touch points you have — web and mobile apps.
Every year, data breaches grow in scope and impact. Security professionals have largely accepted the inevitability of a breach and are shifting their defense-in-depth strategy by including a goal to reduce their time-to-detect and time-to-respond to an attack. Despite these efforts, we haven’t seen the end of headline-grabbing data breaches like recent ones affecting brands such as Marriott, Air Canada, British Airways and Ticketmaster.
App-Level Threats
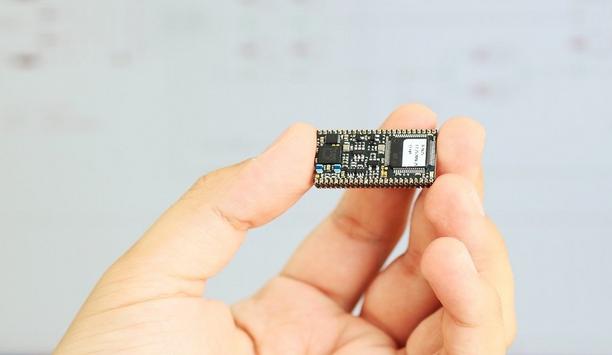
The apps that control or drive these new innovations have become today’s endpoint
The truth of the matter is that the complexity of an organization’s IT environment is dynamic and growing. As new technologies and products go from production into the real world, there will invariably be some areas that are less protected than others. The apps that control or drive these new innovations have become today’s endpoint — they are the first customer touch point for many organizations.
Bad actors have realized that apps contain a treasure trove of information, and because they are often left unprotected, offer attackers easier access to data directly from the app or via attacks directed at back office systems. That’s why it’s imperative that security organizations protect their apps and ensure they are capable of detecting and responding to app-level threats as quickly as they arise.
 |
| It’s imperative that security organizations protect their apps and ensure they are capable of detecting and responding to app-level threats as quickly as they arise |
In-Progress Attack Detection
Unfortunately, the capability to detect in-progress attacks at the app level is an area that IT and security teams have yet to address. This became painfully obvious in light of the recent Magecart attacks leveraged against British Airways and Ticketmaster, among others. Thanks to research by RiskIQ and Volexity, we know that the Magecart attacks target the web app client-side.
During a Magecart attack, the transaction processes are otherwise undisturbed
Attackers gained write access to app code, either by compromising or using stolen credentials, and then inserted a digital card skimmer into the web app. When customers visited the infected web sites and completed a payment form, the digital card skimmer was activated where it intercepted payment card data and transmitted it to the attacker(s).
Data Exfiltration Detection
During a Magecart attack, the transaction processes are otherwise undisturbed. The target companies receive payment, and customers receive the services or goods they purchased. As a result, no one is wise to a breach — until some 380,000 customers are impacted, as in the case of the attack against British Airways.
The target companies’ web application firewalls and data loss prevention systems didn’t detect the data exfiltration because those controls don’t monitor or protect front-end code. Instead, they watch traffic going to and from servers. In the case of the Magecart attacks, the organization was compromised and data was stolen before it even got to the network or servers.
 |
| Today’s proven obfuscation techniques can help prevent application reverse engineering, deter tampering, and protect personal identifiable information and API communications |
Best Practice Resolutions
The Magecart attacks highlight the need to apply the same vigilance and best practices to web and mobile application source code that organizations apply to their networks—which brings us to this year’s New Year’s resolutions for protecting your app source code in 2019:
Alert
The key to success is quickly understanding when and how an app is being attacked
First, organizations must obtain real-time visibility into their application threat landscape given they are operating in a zero-trust environment. Similar to how your organization monitors the network and the systems connected to it, you must be able to monitor your apps. This will allow you to see what users are doing with your code so that you can customize protection to counter attacks your app faces. Throughout the app’s lifecycle, you can respond to malicious behavior early, quarantine suspicious accounts, and make continuous code modifications to stay a step ahead of new attacks.
Protect
Next, informed by threat analytics, adapt your application source code protection. Deter attackers from analyzing or reverse engineering application code through obfuscation. Today’s proven obfuscation techniques can help prevent application reverse engineering, deter tampering, and protect personal identifiable information and API communications.
If an attacker tries to understand app operation though the use of a debugger or in the unlikely event an attacker manages to get past obfuscation, threat analytics will alert you to the malicious activity while your app begins to self-repair attacked source code or disable portions of the affected web app. The key to success is quickly understanding when and how an app is being attacked and taking rapid action to limit the risk of data theft and exfiltration.
 |
| Protecting encryption keys is often overlooked but should be considered a best practice as you forge into the new year with a renewed commitment to app security to ensure your organization’s health and well-being in 2019 |
Encrypt
Finally, access to local digital content and data, as well as communications with back office systems, should be protected by encryption as a second line of defense, after implementing app protection to guard against piracy and theft. However, the single point of failure remains the instance at which the decryption key is used.
Effective encryption requires a sophisticated implementation of White-Box Cryptography
This point is easily identifiable through signature patterns and cryptographic routines. Once found, an attacker can easily navigate to where the keys are constructed in memory and exploit them. Effective encryption requires a sophisticated implementation of White-Box Cryptography.
One that combines a mathematical algorithm with data and code obfuscation techniques transforming cryptographic keys and related operations into indecipherable text strings. Protecting encryption keys is often overlooked but should be considered a best practice as you forge into the new year with a renewed commitment to app security to ensure your organization’s health and well-being in 2019.
Protecting Applications Against Data Breach
According to the most recent Cost of a Data Breach Study by the Ponemon Institute, a single breach costs an average of $3.86 million, not to mention the disruption to productivity across the organization. In 2019, we can count on seeing more breaches and ever-escalating costs. It seems that setting—and fulfilling—New Year’s resolutions to protect your applications has the potential to impact more than just your risk of a data breach. It can protect your company’s financial and corporate health as well. So, what are you waiting for?
Discover how AI, biometrics, and analytics are transforming casino security