Canon IP Network Cameras
Sorry no products match your search. Your search criteria may have been too narrow. If you remove some of your search criteria, this may yield more productive results.
Browse IP Network Cameras
- Color Type
- Color
- Monochrome
- Color / Monochrome
- True Day / Night
- Indoor/Outdoor
- Indoor
- Outdoor
- Indoor/Outdoor
- Mount Type
- Bell
- Bell Mount
- Board
- Board - in
- Board-In
- View more
IP Dome camera products updated recently
IP Dome cameras - Expert commentary

Dr. Henrik Siegle has been the CTO at Bosch Building Technologies since November 2021. In this interview, he speaks about the megatrends of energy efficiency and sustainability, an...

Residential burglaries and break-ins are a problem for many homeowners. The FBI estimates there were approximately 1,117,696 burglaries in 2019 in the United States, which accounte...

If defense is the best form of attack, then in security, planned preventative maintenance (PPM) is the best way to protect your business from harm. Also known as PPM, the service e...
Latest Canon USA, Inc. news

Milestone Systems’ CEO Thomas Jensen is stepping down from his position with immediate effect, and the company is now searching for a new pioneer. ”To further st...

The PSA Network (PSA), the consortium of professional systems integrators announced the lineup of sponsors for PSA TEC 2023 (TEC), which is taking place in Dallas, Texas, USA, from...

BriefCam, the industry’s renowned provider of Video Content Analytics and Video Synopsis solutions, has announced the appointment of Gil Briman as its Chief Executive Officer...
Related white papers
14 Success Stories About How Video Technology Is Improving City Life
Empowering Cameras With AI
The Rise of Ethical Facial Recognition
Trending topic articles
Suprema, a pioneer of AI-powered security solutions, announced that BioStation 3 is expected to set a new annual global sales record by the end of this year. This represents the highest annual sales...
The 19th Real Estate Development Summit Saudi Arabia – Luxury Edition successfully concluded after two days of high-level exchange, strategic collaboration, and global networking, bringing toget...
IDIS has launched two new advanced PTZ cameras, providing powerful AI and NIR performance. The extended range offers a broader choice of PTZ cameras to more efficiently cover open areas, in applicatio...
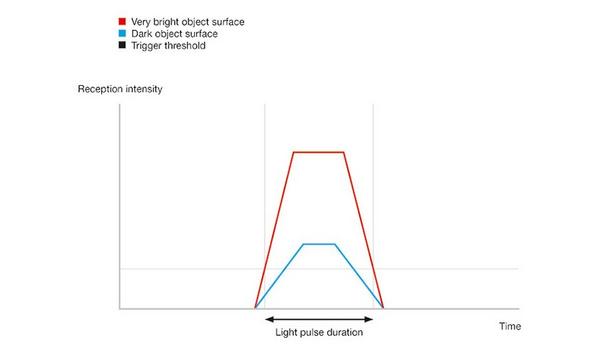
Leuze uses artificial intelligence (AI) to significantly improve the measurement accuracy of optical distance sensors for challenging industrial applications. This innovation improves measurement acc...
Alarm.com and Everon, LLC, a pioneering security integrator and premier provider of commercial security, video, fire, and life safety solutions, today announced a strategic partnership to deliver a un...
Integrated access control and security manufacturer TDSi now announces that from 1st January 2026, it will operate under the new name: TDSi by Hirsch. The change follows the global transformation of...
Aetina Corporation, a pioneering provider of Edge AI solutions, has announced the launch of its next-generation MXM AI Accelerator Module series accelerated by NVIDIA RTX PRO Blackwell Embedded GPUs,...
Abnormal AI, the pioneer in AI-native human behavior security, announced it has been recognized as a Leader in the 2025 Gartner® Magic Quadrant™ for Email Security, marking the company&rsquo...
DigiCert, a pioneer in intelligent trust, unveiled its 2026 Security Predictions, forecasting how AI, quantum computing, and automation will reshape global trust frameworks. The predictions highlight...
Building on earlier research published in October 2025, Zimperium announced that its zLabs team has uncovered a significantly enhanced variant of ClayRat, an Android spyware family first detailed in t...
Iris officially launches today, introducing a platform that transforms how cameras are controlled, and productions are managed. By turning virtually any PTZ camera into a software-connected, remotely...
Secutech, Asia’s premier security exhibition, will be held from 22 – 24 April 2026 at the Taipei Nangang Exhibition Center, Hall 1. This edition promises a robust showcase of more than 400...
Hikvision announced recently that it has achieved the ISO 37301:2021 Compliance Management System certification from SGS, the world's renowned testing, inspection, and certification company. This mil...
Balancing operational efficiencies and customer satisfaction with costs, resources, and legislative obligations is a challenge faced by every security services provider offering keyholding and alarm r...
Axis Communications, a industry pioneer in video surveillance, announces it has signed the U.S. Cybersecurity & Infrastructure Security Agency’s (CISA) Secure by Design pledge to transp...
The Key To Unlocking K12 School Safety Grants
DownloadHoneywell GARD USB Threat Report 2024
DownloadPhysical Access Control
DownloadThe 2024 State Of Physical Access Trend Report
DownloadThe Security Challenges Of Data Centers
Download