In its push to help IT and security operations professionals better respond to cyber incidents, Rubrik, the Zero Trust Data Security™ Company, announced Rubrik Ruby™, the generative AI companion for Rubrik Security Cloud designed to speed cyber detection, cyber recovery, and cyber resilience.
The company will leverage Microsoft’s Azure OpenAI, in combination with its machine learning-driven Data Threat Engine, to help discover, investigate, remediate, and report on cyber incidents.
Rubrik Security Cloud
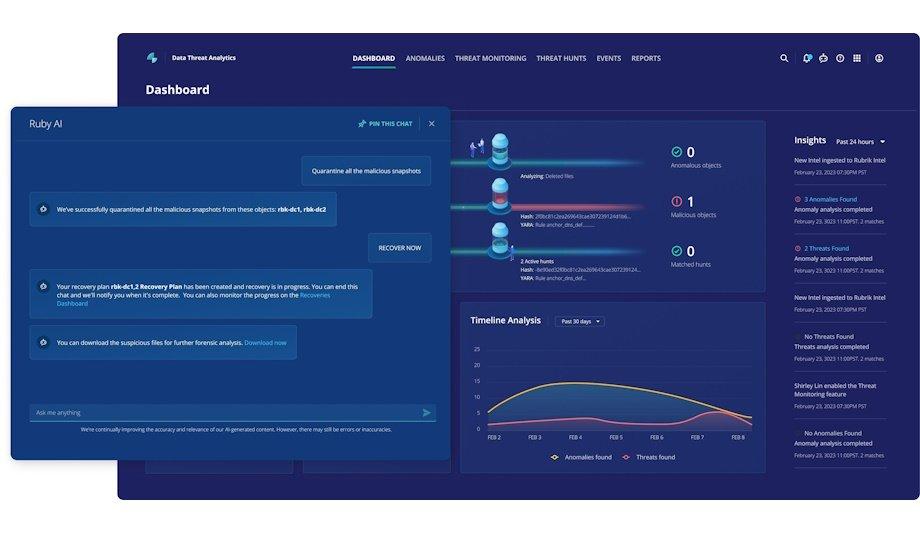
The company’s newest AI companion, Ruby, extends Rubrik Security Cloud with generative AI and automation. Ruby helps customers of all levels of cyber expertise through a guided response process that enables customers to explore, understand, and respond to a cyber incident, with the goal of resuming critical business operations more rapidly.
Company’s newest AI companion, Ruby, opens Rubrik Security Cloud with much AI and automation
“One of the most important values of Ruby is that we leverage Rubrik’s best practices and the experiences from our own field and ransomware recovery teams, who have worked with hundreds of customers across industries,” said Anneka Gupta, Chief Product Officer at Rubrik. “Think of Ruby as the personification of a security analyst in AI, who is there to hold the customer’s hand to resolve a security incident much faster than they could do before.”
Three fundamental ways
Rubrik deploys AI to serve customers in three fundamental ways:
- Detect anomalous activity in data across enterprise, cloud, and SaaS applications, to empower customers to identify malicious activity and determine the scope of a cyberattack or incident via Rubrik’s Data Threat Engine;
- Drive customer satisfaction with a highly engaged support team, which can be more proactive and targeted in alerting to potential problems before they broadly impact organizations’ systems via Rubrik’s internally developed Sentry AI platform;
- Provide best-in-class security expertise with a guided, rapid response process that helps them navigate challenging workflows and speeds safe recovery from cyber incidents via Ruby.
Engaging Ruby
In response to data risk alerts generated in Rubrik Security Cloud, users can interact with Ruby, the company’s AI assistant, to ask follow-up questions including whether any sensitive data was impacted, or what needs to be done to restore the environment. Ruby will provide guidance on additional questions to pose, and help customers successfully resolve incidents more quickly.
To fix an environment tracking a cyber incident, ample forensics is needed to decide the root cause
In this era of cloud and AI, data is exploding. According to the most recent Rubrik Zero Labs State of Data Security report, IT and security pioneers dealt with 52 cyberattacks on average in 2022. To restore an environment following a cyber incident, extensive forensics is required to determine the root cause, a process that typically requires sorting through countless manuals or enlisting an external service that can guide through the next steps.
Eliminate the roadblocks
“Securing business’ data must be a company-wide imperative; every employee should be empowered with the tools to quickly respond to incidents. Our goal with Ruby is to bridge any skills gaps and eliminate the roadblocks to cyber response so that all organizations realize business continuity and preserve the integrity of their corporate data,” said Gupta.
Ruby is planned to be available in the coming months to Enterprise Edition subscribers who opt-in. Over time, Ruby will expand to help customers continue to recover from cyber-attacks.
Discover how AI, biometrics, and analytics are transforming casino security