Checkmarx, the pioneer in cloud-native application security, has released the annual Future of AppSec Report, which gives an in-depth look at the current state of application security, future investments, and organizations’ most critical security concerns.
The study reveals that 92% of companies surveyed had experienced a breach in the prior year due to vulnerabilities of applications developed in-house.
Application security
In recent years the responsibility for application security has shifted away from dedicated security teams and is shared between AppSec managers and developers.
In the Future of AppSec study, 49% of respondents said that their developers were involved in key AppSec solution purchases, 41% said that AppSec managers were involved and 40% indicated CISO involvement.
Importance of a robust approach
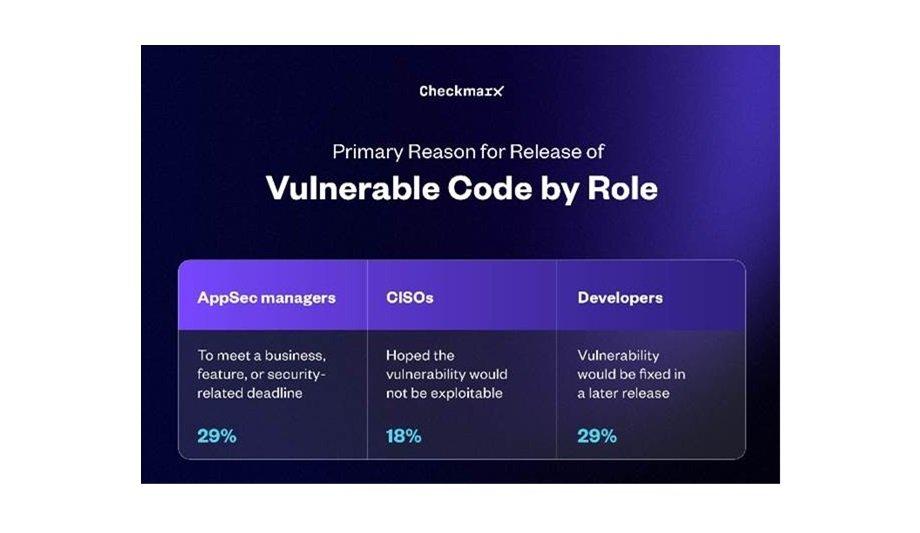
18% of CISOs said that they hoped the vulnerability would not be exploitable
With more software to secure that has been deployed in more environments with less time available to secure it, a remarkable 91% of companies have knowingly released vulnerable applications. Breaches are more likely to occur without a robust approach to application security.
Asked why respondents had released vulnerable applications, business pressure was a significant reason with 29% of AppSec managers saying they had released the applications “to meet a business, feature or security-related deadline,” 18% of CISOs saying that they hoped the vulnerability would not be exploitable, and 29% of developers saying that the vulnerability would be fixed in a later release.
AppSec risk mitigation
“The mitigation of AppSec risk is becoming a shared responsibility at a time when cloud-native applications are deployed multiple times each day,” said Amit Daniel, Chief Marketing Officer at Checkmarx.
He adds, “Enterprise CISOs are coming to Checkmarx looking for a way to gain visibility into the security posture of their entire organizational footprints. Our goal is to provide them with that visibility as a way of building what we call ‘DevSecTrust,’ or trust between developers and security that can help bring their AppSec maturity to a whole new level.”
Top three security concerns
The seamless integration of developer-friendly AppSec tools within their workflows is essential
Developers’ top three security concerns are focused on the tension between time-to-delivery demands and the potential volumes of vulnerabilities requiring remediation, including impediment of the development process by security demands, difficulty knowing which vulnerabilities to fix and how to prioritise them, and lack of context to help remediate vulnerabilities.
A significant 61% of developers said that it’s critical that security not block or decelerate the development process or become a barrier to business success. To close the gaps in application security, the seamless integration of developer-friendly AppSec tools within their workflows is essential.
Composition of applications
The composition of applications has become more complex, increasing to include source code, open source packages, infrastructure-as-code (IaC), containers, and more.
This exponential increase in complexity is one main driver behind the need for organizations to scan across the entire software development life cycle, from code to cloud.
Comprehensive AppSec platform
The research clearly illustrates the need for a comprehensive AppSec platform that addresses these concerns and more, equipping all teams involved to:
- Build #DevSecTrust, a state of cooperation and trust between AppSec and developer teams.
- Improve the developer experience by providing prioritisation of risks as part of a toolkit integrated with their preferred IDEs.
- Consolidate cloud-native AppSec with a holistic approach.
- Secure the entire application footprint from code to cloud.
Methodology
Checkmarx commissioned Censuswide to conduct a survey among 1504 developers, CISOs, and AppSec managers in companies from 1000 to 10,000+ employees from North America, Europe, and Asia-Pacific.
The survey took place in December 2023. Censuswide abides by and employs members of the Market Research Society, which is based on the ESOMAR principles.
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems