The Jigme Dorji Wangchuck National Referral Hospital is a renowned institution in Bhutan delivering healthcare services. The hospital caters to the population of Thimphu and neighboring districts. The hospital not only functions as the National Referral Hospital for the entire country but also functions as:
- Regional Referral Hospital for the Western District
- District hospital for Thimphu District
- Human resources pool and technical backup for district hospitals
- Clinical training center for the Royal Institute of Health Sciences (RIHS)
- Technical support for public health programs
Elevator Access Control
As the hospital works round the clock, one of the major concerns was to manage complex shifts of employees. Elevator control, where only users with access rights can call the elevator, was another challenge the hospital wanted to meet. Furthermore, the customer also wanted a solution, with the help of which the admin could assign entry and exit points for patients, visitors and employees. Lastly, the management wanted to restrict visitor entry to a pre-defined time and rooms of the hospital for better visitor management.
Biometric Authentication For Crowd Management
Matrix pitched its access control, time-attendance and visitor management solution along with the different variants of biometric devices, which fulfills every requirement of this renowned hospital. Around 206 devices were installed in the hospital, which are used in controlling access at rooms and elevators. Devices were installed at the main entrance, ward rooms, server rooms, outside elevators, and ramps on every floor to restrict access.
There is no individual in the building who is not enrolled in the system. As the hospital works 24 hours, there are multiple shifts in which the employees work. Through this, the hospital could manage multiple shifts of employees. Approximately, 700 visitor profiles were created with constrained time to visit, limited rooms to enter and a pre-defined route of access. Also, crowd at the elevator was controlled by restricting the use to only users with elevator access rights.
Successful Implementation
JDWNRH fulfilled its requirement with Matrix People Mobility Management Solution and achieved the following results:JDWNRH fulfilled its requirement with Matrix People Mobility Management Solution
- Improved security by restricting unauthorized entry
- Reduced complexity of shifts by time-attendance solution
- Elevator crowd control
- Time and zone based entry restrictions for visitors and patients
Authentication And Verification Equipment
The following products from Matrix Comsec have been implemented at JDWNRH for efficient visitor management.
- COSEC VEGA FAX: Fingerprint and card based door controller for time-attendance and access control application
- COSEC VEGA CAX: Card-based door controller for time-attendance and access control application
- COSEC PATH DCFE: Fingerprint and card based door controller with IP65
- COSEC PATH RDCE: Card based exit reader with IP65
- COSEC ENROLL CARD: Card enrolment station
- COSEC ENROLL FINGER: Finger enrolment station
- COSEC VEGA CPM EM PROX: EM proximity card personality reader module for VEGA series door controller
- COSEC CPM EM PROX: EM proximity card personality reader module
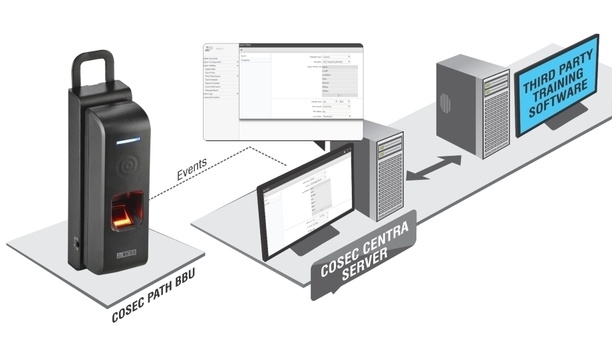
- COSEC CENTRA LE: Application server platform with 1,000 users and expandable up to one million users for basic access control and raw event data
- COSEC LE TAM: Time-attendance module for COSEC CENTRA LE users
- COSEC LE ACM: Access control software module for COSEC CENTRA LE users
- COSEC LE VMM: Visitor management module for COSEC CENTRA LE users
- COSEC USER100: User license for 100 users
Stay ahead in the era of intelligent security systems powered by Artificial Intelligence with our special e-magazine on AI in security.