Banking & Finance security applications - Expert commentary
With increased demands being placed on safety and security globally, and supported by advancements in IP cameras and 360-degree camera technology, the video surveillance industry is growing steadily. Market research indicates that this worldwide industry is expected to reach an estimated $39.3 billion in revenue by 2023, driven by a CAGR of 9.3 percent from 2018 to 2023. Video surveillance is not just about capturing footage (to review an event or incident when it occurs), but also about data...
As technology advances, the world is becoming increasingly connected, changing the way users think about and interact with security systems, which continue to evolve across all verticals and applications. With this change comes new opportunity for security integrators; security systems are advancing, creating new needs for products and services — some of which can be met through the adoption of cloud-based service systems. Cloud technology is no longer a dreamt-up version of the future of...
If you’re responsible for a medium or large-sized office, it’s more important than ever that you have access to a means of ensuring people’s safety, managing risks and fraud, and protecting property. Any security system that you employ must therefore meet the most demanding commercial requirements of today’s offices, and tomorrow’s. This means thinking beyond a basic intrusion system and specifying a comprehensive solution that integrates smart features like access...
There’s no denying that cyber-crime is one of the biggest threats facing any organization with the devastating results they can cause painfully explicit. Highly publicized cases stretching from the US government to digital giant Facebook has made tackling cyber security a necessity for all major organizations. The consequences of breaches have just become more severe, with new GDPR rules meaning any security breach, and resultant data loss, could cost your organization a fine of up to four...
Considering how much the modern smartphone has become a common everyday tool and cultural icon, it’s hard to believe it has only been with us for a relatively short space of time. The first Apple iPhone was launched in 2007 and yet in a little over a decade the smartphone has become as essential as our keys or wallet. From its conception as a multi-faceted communications device, it has morphed into something far more integrated in our daily lives. Services such as Apple Pay, Android Pay a...
By 2020, video surveillance using fixed, body and mobile cameras is expected to capture an astounding 859 PB of video daily. Increasing retention regulations and higher resolution cameras, are forcing the video surveillance industry to reassess its approach to data storage. Large capacity primary storage tends to be expensive to procure and costly to implement – especially without a sound architecture that can balance storage performance levels with the speed of access needed to recall vid...
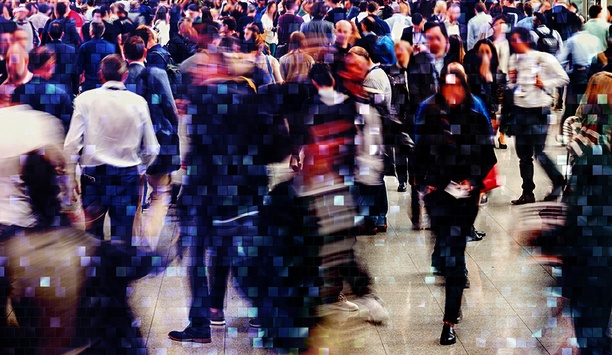
The rise to prominence of smart cities should not go unnoticed. To the untrained eye, you might not realise just how connected your city is and how it’s helping your everyday life. From crossing the road to monitoring water levels, technology is allowing cities to think quicker and act smarter. Data-Driven Decisions A recent whitepaper by ABI Research has revealed that the total global cost-saving potential offered by smart cities stands at more than $5 trillion. This shows how technolog...
Over the past few years, biometrics has rapidly expanded into consumer applications, like the financial market for customer authentication, to payment services and withdrawing cash from ATMs in high-fraud markets. However, its adoption as an additional authentication factor for physical access control systems (PACS) and other enterprise applications, hasn’t been as rapid. But this is changing. Biometrics offers numerous benefits at the door and throughout the enterprise. With the advent o...
Most technology companies have one goal in mind: to provide customers with high-quality, affordable products that can efficiently help streamline operations. Whether it's surveillance cameras, video management software, access control technology or any other type of security device, today's leading organizations invest in expertise in these product segments and strive to produce the highest quality solutions. To effectively fulfill this task, technology providers are always searching for emergi...
Surveillance systems can track the locations of cellphone users and spy on their calls, texts and data streams. The Washington Post has reported on such systems that are being turned against travelers around the world, according to security experts and U.S. officials. The summer season highlights the need to take extra precautions when traveling. When traveling anywhere in the world, for business or pleasure, citizens need to be aware of and alert to looming physical and cybersecurity threats....
In the physical security space, video analytics have historically over-promised and under-delivered, often leaving end users sceptical about their capabilities. However, increased integration with security solutions and other business systems, as well as developments in deep learning and artificial intelligence (AI), have given video analytics a significant boost in recent years. Here, we take a look at the key trends putting video analytics in the spotlight, and how this opens up new opportunit...
As anyone who has ever flown on a commercial airline since 2001 knows, security measures at airports are well enforced and the emphasis on traveler safety is all around the airport and its grounds. Mass transportation, meanwhile, presents a special but not any less significant challenge when it comes to determining security issues. These facilities need to develop the means to protect a constantly changing and large population of passengers. And unlike airports these facilities often have hundr...
For the past several years, there has been a focus by integrators and customers to assure that their card-based access control systems are secure. To give businesses an extra incentive to meet their cybersecurity threats, the Federal Trade Commission (FTC) has decided to hold the business community responsible for failing to implement good cybersecurity practices and is now filing lawsuits against those that don't. For instance, the FTC filed a lawsuit against D-Link and its U.S. subsidiary, al...
Artificial intelligence and machine learning are the rage in tech right now and not surprisingly, many cyber companies are beginning to automate an increasing amount of their operations. Some of this is great, particularly when it assists cybersecurity professionals to automate mundane tasks and focus more of their attention on higher level analysis. But so far, machine learning is more hype than helpful for cybersecurity, but that does not mean you can’t automate some tasks to keep your...
Live events at large venues like arenas, stadiums or convention halls – whether they involve wrestlers breaking chairs over each other’s heads, Axl and Slash letting bygones be bygones and reuniting Guns ‘n’ Roses, your favorite NFL team annihilating the opposition 62-3, or a convention involving anything from politics to food to Star Trek – are exciting affairs that channel the camaraderie of the crowd into a powerful collective energy. But they also are vulne...
In the state of the residential security market today, we see many who are offering home security packages that rely on numerous sensors and multiple devices to provide a comprehensive coverage of the home and provide peace of mind. Each individual sensor or device within the package provides a specific functionality, and the user finds himself burdened by an overwhelming amount of sensors and devices. This overload is intensified by the penetration of additional IoT and smart devices into the...
Audio is often overlooked in the security and video surveillance industry. There are some intercom installations where audio plays a key role, but it’s not typically thought about when it comes to security and event management. Audio takes a back seat in many security systems because audio captured from a surveillance camera can have a different impact on the privacy of those being monitored. Audio surveillance is therefore subject to strict laws that vary from state to state. Many state...
A deep native integration of Bosch cameras with software from ISS proactively catalyzes the best in security and surveillance, while providing advanced intelligent video tools. ISS SecurOS provides intelligent enterprise video management solutions with emphasis on providing scalability and flexibility to meet the customer’s needs. Deeply integrating built-in video analytics from Bosch cameras improves operator efficiency and situational awareness to manage complex environments. ISS Secu...
According to IHS Market, it is estimated that there are over 60 million security cameras in the United States, and other reports say these cameras capture more than four billion hours of footage per week. Over the last decade, IP camera technology has dominated the conversation as it has provided users with a broad offering of enhanced image quality and features. With a large percentage of existing security systems relying on analog, many end users looking for high definition (HD) video qualit...
If you’ve been paying attention over the last twelve months, you will have noticed that deep learning techniques and artificial intelligence (AI) are making waves in the physical security market, with manufacturers eagerly adopting these buzzwords at the industry's biggest trade shows. With all the hype, security professionals are curious to know what these terms really mean, and how these technologies can boost real-world security system performance. The growing number of appli...
It’s not hard to see why more and more locations are requesting security solutions that operate on an open system. Selecting products and platforms that utilize open standards—Session Initiation Protocol (SIP), HTTP, IEEE, RESTful APIs, etc.—provide additional levels of interoperability, scalability and versatility that give organizations the flexibility they want to be proactive with safety and security. Unfortunately, creating the right solution today isn’t quite as si...
Schools today are charged to provide an environment that is both safe and conducive to learning, which can be difficult considering the range of security incidents and challenges they face, including bullying, fights, graffiti, theft and more. In addition to working within often tight budgetary constraints, a main challenge is to provide the highest level of security in an aesthetically pleasing way that doesn’t make students feel as if they are in prison. While these two needs may seem...
Security teams at casinos and gaming facilities are challenged daily to balance a welcoming and guest-focused attitude with a firm and capable presence to prevent and handle security issues, manage surveillance and security systems, and protect employees, guests, and assets. And all of this needs to be accomplished while complying with strict gaming regulations. An experienced security systems integrator can assist you with many of those challenges, including the very important job of ensuring...
The physical security industry is rapidly changing, ever evolving, and one that is growing faster than most other sectors of the greater global market. The latest research shows that the forecasted growth rates will be a compound average growth rate (CAGR) of 7.2% and a total market revenue opportunity of $41.27B through 2022. These economic indicators make the industry a very attractive investment for entrepreneurs and for investment from large corporations from other industries. At ISC West 2...
Dollars spent by video surveillance customers must go towards ensuring high-availability capture, storage and on-demand access to live and archived video. Reaching this goal mandates high-availability of independent components – camera, network, storage (edge, external), internet connectivity, display, all Video Management Software (VMS) components and an architecture that can take advantage of this. In this note, we focus on seeing our way through to a video surveillance architecture, tha...
The Internet of Things (IoT) is having a significant and ever-changing impact on the way we view video security. Today, cameras are expected to be so much more than devices with which to simply capture images; they need to be far smarter than that. These future-facing cameras are becoming an integral part of the vast digital connectivity infrastructure, delivering a parallel performance as intelligent sensors with the ability to extract the kind of invaluable data that helps businesses make impr...
It had been a particularly slow night. The plant security guard had just made his rounds on this Sunday evening shift. As soon as he passed the weighing scales, he could enter the guard shack and get off his feet. Challenging A Curious Incident However, on this night, he noticed the waste vendor’s truck sitting half on and half off the scale. He stopped dead in his tracks to see if the truck would back up and completely sit on the scale. It never did. The observant guard walked up to the...
With the recent tragic events in Florida, it’s evident that schools require more tools to help ensure their students’ safety. With that, school and municipal officials all over the country are looking for more advanced ways to combat gun violence. While there is no perfect solution for the myriad of threats and emergencies with which our schools are confronted, many have looked to technology to help improve communications before, during and after incidents. For schools across the...
With the ever-growing availability of video data thanks to the low cost of high-resolution video cameras and storage, artificial intelligence (AI) and deep learning analytics now have become a necessity for the physical security industry, including access control and intrusion detection. Minimizing human error and false positives are the key motivations for applying AI technologies in the security industry. What Is Artificial Intelligence? Artificial intelligence is the ability of machines to...
Video surveillance across the world is growing exponentially and its major application is in both public safety and law enforcement. Traditionally, it has been fixed surveillance where cameras provide live streams from fixed cameras situated in what is considered strategic locations. But they are limited in what they can see given by their very definition of being “fixed”. The future of video surveillance includes the deployment of more mobile video surveillance with the benefits it...