Expert commentary
Access control and video surveillance technologies are expensive to buy and install. So it’s important that end users make sure they get a system that works the way it is supposed to work and the way they want it to work. To that end, the principles of project management can help end users find an integrator and to manage the work of installing or upgrading security systems. If you are experienced with security technologies, you might consider managing the project yourself. If not, consi...
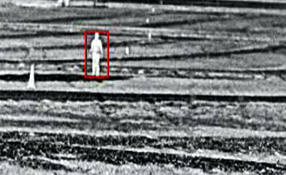
Thermal cameras can often be used to cover larger areas than standard visible light cameras Smart thermal cameras use on-board video analytics and a high degree of video processing to detect people very accurately in complete darkness, bright sun, and bad weather over the typically large perimeters associated with transportation applications. Combining manpower and smart thermal technology makes security for transportation assets more effective. At the end of the day, it takes...
The security industry has been earning more than its share of accolades for employing military veterans. With big companies such as G4S Secure Solutions employing more than 9,000 veterans in various positions – 22 percent of its workforce – the industry has become distinctly “military friendly.” In fact, the company and rival Allied Barton Security Services were both named 2014 Military Friendly Employers by Victory Media, publisher of G.I. Jobs. Both have also won the G...
If your company has a facility or a current business meeting in Seoul, South Korea, you would want to know the details behind the recent knife attack on the U.S. ambassador to South Korea, Mark W. Lippert. You would want to know that the attacker belonged to a group promoting the unification of North and South Korea and that South Korean President Park Geun-hye called the event an attack on the South Korea-U.S. alliance. You would want to know where in Seoul the attack occurred as well as many...
The FERC standard CIP-014-1 became effective, according to the Federal Register, on January 26, 2015 The electric power industry works with several federal agencies, including the Federal Energy Regulatory Commission (FERC), the Department of Homeland Security (DHS), and the Department of Energy (DOE) to improve sector-wide resilience for cyber threats. The industry also collaborates with the National Institute of Standards and Technology (NIST), the North American Electric Re...
Differences between standard data applications and the requirements of networks designed for IP video security applications are critical for your system's performance When the need to purchase a network switch arises, many IT directors immediately turn to two favorites, HP or Cisco. They have become to the networking environment what IBM was to computers: “No one ever got fired for buying IBM.” Certainly, switches play a crucial role in enhancing your network by in...
With the industry’s largest security trade show just weeks away, we spoke with leading systems integrator Securadyne Systems, Austin, Texas, for their assessment of ISC West and how they use the show to benefit their organization. Terry King, vice president and regional general manager, shares his thoughts on what Securadyne Systems plans to accomplish at this year’s event. SourceSecurity.com: What is your take on ISC West and what do you get out of it? Terry King: ISC West has al...
There’s more talk than ever in the security industry about cloud-based systems – where they are, where they’re going, the risks, the rewards. New opportunities for integrator companies, especially related to recurring monthly revenue (RMR), are among the benefits of new cloud-based systems. For insights into those opportunities, we spoke with Robert Hile, currently director of strategic accounts for SureView Systems and a strong proponent of cloud-based systems, whose backgroun...
Standards for camera manufacturers presented a new challenge with the introduction of security cameras that require more than 30 Watts of power Standards for camera manufacturers presented a new challenge with the introduction of security cameras that require more than 30 Watts of power. Many of these involve pan-tilt-zoom (PTZ) domes and heaters and blowers that require additional power. This development created two areas of confusion which is highlighted in this article by N...
Lost or damaged keys cost authorities thousands of dollars to replace Keys are a common element in any transportation department, and an automated key control system is a valuable tool. Key management systems offer multi-site transportation facilities increased security and control to help prevent authorized key access as well as reducing the number of lost or misplaced keys. As an example, road repair is often done at night and requires equipment, vehicles, lights, generato...
Improvements in the technology have lowered – but not eliminated – concerns about false alarms False alarms have plagued the video analytics market since the beginning. Improvements in the technology have lowered – but not eliminated – concerns about false alarms. Companies providing video analytics systems say the question isn’t whether false alarms can be eliminated, but rather how they can be managed. “We’re still very far away fro...
It’s important for everyone in a high school to wear an ID Handwritten check in and check out books fail to alert the security risks posed by individuals on school campuses. Installing visitor management systems is imperative to screen and manage visitors and thereby enhance the level of safety in schools. However, it takes training and practice to use school visitor management technologies effectively. Security technologies can go a long way toward making K-12 sc...
The security industry continues to move away from closed, proprietary systems and instead is fine-focused on open solutions that assist the move to total integration. The benefits of achieving this feat belong to both installing company and end user. Benefits of open security solutions Open, interoperable systems make it easier to integrate a wide array of sensors, devices and communication technologies across the enterprise. That means quicker installations, lower labor costs and heightened s...
According to research firm IHS Technology, the residential intrusion alarm market is expected to grow by 9.4 percent in 2015 For years, the industry’s penetration rate for security alarm systems has hovered from a conservative 18 percent of households to a more liberal 22 percent or so. According to research firm IHS, the residential intrusion alarm market is expected to grow by 9.4 percent in 2015. Perhaps this increase is due in part to the rise of interactive ser...
Supply chain risk management involves identifying and dealing with supply chain uncertainties that pose a threat to business continuity Today’s complex world needs risk managers, business people that think about the bad things that might happen and lay plans to eliminate or at least mitigate those risks. This article explains the need to identify and respond to risks involved in a supply chain. Manufacturers should make efforts and develop strategies to enhance supply ch...
Combining thermal imaging with analytics provides a robust system Prices are dropping for thermal cameras. Now they are much more affordable for non-military customers – and more likely to be used in combination with video analytics. Combining thermal imaging with analytics provides a robust system; the technologies work well together. Thermal cameras make it easier to detect motion because you are eliminating much of the detail and only emphasising temperature “c...
A true IoT platform is the confluence of Internet, business and sensory data The era of IoT - the Internet of Things - is upon us. A deluge of urban sensory data is flowing into data centers every minute, putting pressure on data-center resources and accumulating at a rate faster than anyone can process. Is the proliferation of sensory data simply evidence of an increasingly intrusive world, or can IoT be used for the improvement and development of intelligence-equipped cities...
Milestone Interconnect provides a cost-efficient and flexible way to have central surveillance operation across geographically dispersed sites The transportation vertical is embracing the open platform for video systems. In the past, manufacturers required transportation end users to purchase the camera, the recorders and the software all from one manufacturer. Now, with IP, organizations in the transportation vertical can use off-the-shelf cameras, servers (recorders) and sof...
Analytics at the edge provide the ability to process what is happening in a field of view and discern if a relevant alert is triggered There are multiple benefits to using video analytics at the edge (i.e., near or inside the camera). For one thing, analytics at the edge provides the ability to process what is happening in a field of view and discern if a relevant alert is triggered. This can be faster and less expensive than the original video analytics model of using a separ...
PoE power is a complex issue in itself made even more complex by the lack of standardisation Standards are like a warm blanket on a cold winter night. They make us feel safe and warm. A standard tells us the devices we use within our systems will interact with each other regardless of manufacturer. For IP-powered PoE devices, we depend on standards such as 802.3af for devices requiring up to 15.4 watts and 802.3at for devices powered up to 30 watts. We depend on the devices...
Compliance with regulatory requirements are not enough to protect the US electric grid Many companies use compliance and best practices to assist in their fight to protect the U.S. electric grid. They rely primarily on what three groups say – FERC (Federal Energy and Regulatory Committee), CERT (U.S. Computer Emergency Readiness Team) and NERC (North American Electric Reliability Corporation). These groups issue advisories, standards and guidelines for the industr...
Retail has the greatest potential for analytics because it can be used both for security and for marketing & operations Video analytics isn’t just for security. In general, the ability to leverage data from video provides a new wealth of information and “intelligence” about all aspects of the business. The retail vertical is leading the way in reaping the benefits of video analytics beyond the security function. There are two reasons retailer...
Veterans are able to use their skills from the military to help develop strategies Ex-army officers/ military veterans bring considerable skills and invaluable experience to security companies. Not only do they play an important role in frontline positions, but also their exposure to a diverse array of security challenges make them increasingly valuable in formulating security management strategies. At the same time, such companies also offer the veterans an alternative and r...
The ability to clearly see facial features and other identifying characteristics on each passenger greatly enhances security Some of the video technology used in the transportation vertical is purpose-built, but the wide range of applications and environments is conducive to a variety of general-purpose technology, too. Leading IP camera makers like Axis, Sony and Panasonic have introduced new products to enhance safety and security of travel in trains, bu...
Intelligent searches of video archives provide investigators faster access to any needed video clip That video analytics can be immensely useful in forensics is relatively less known. However, forensic search capabilities offered by some modern video analytics solutions can not only save investigators significant amounts of time but also help them find results more accurately. These solutions leverage facial recognition and advanced object tracking, demographic analytics, lice...
Various vertical markets such as retail, airports, and transportation have benefited from video analytics Video analytics systems have progressed far beyond the theoretical and are now being used effectively in a range of applications. Let’s look at some of the real-world scenarios that have taken advantage of the latest video analytics systems. Video analytics aren’t just for security. For a traffic application, Agent Vi provides business intelligence on the ave...
The better the sensors, the better the analytics Garbage in, garbage out. The familiar cliché is just as applicable to the area of video analytics as any other field of computing. You simply must have a high-quality image in order to achieve a high-functioning analytics system. The good news is that video cameras, which are the sensors in video analytics systems, are providing images that are better than ever, offering higher quality – and more data – for us...
Many security company employees say they first learned about opportunities in the field through other employees The nation’s security companies are increasingly turning to U.S. military veterans to fill the ranks of both uniformed guards and management personnel. Getting the best former soldiers, airmen and sailors into the civilian workforce requires recruiting, and some of the best recruiters are other veterans. A wide variety of current security company employees say...
Forty-one percent of cyber incidents involved the energy sector The Bipartisan Policy Center, the Industrial Control Systems Cyber Emergency Response Team, which is part of the U.S. Department of Homeland Security, reports responding to 198 cyber incidents in fiscal year 2012 across all critical infrastructure sectors. Forty-one percent of these incidents involved the energy sector, particularly electricity, according to a February 2014 report. Considering the enormity of the...
The action of a voltage applied to a resistance element, draws power from the switch’s PoE port We often think about a power supply operating in a single format. A power source provides power to a device. You plug it into a wall outlet and that’s all that happens. PoE power is a far more complex. There is interaction between the source providing power and the device receiving power. This interaction is governed under the 802.3 AF and AT standards. These differences...
Browse expert commentaries
Expert Section
Related videos
CLIQ Connect
DNAKE Access Control Terminals: Minimalist Design, Maximum Security!
Unlock the Future with Abloy Pulse: Keyless, Energy-Efficient Security Systems