Veracity Cables & Cable Assemblies (1)
Browse Cables & Cable Assemblies
- Make
- Veracity
- Other Veracity products
- Veracity Network Video Recorders (NVRs)
Cable & cable assembly products updated recently
Cables & cable assemblies - Expert commentary
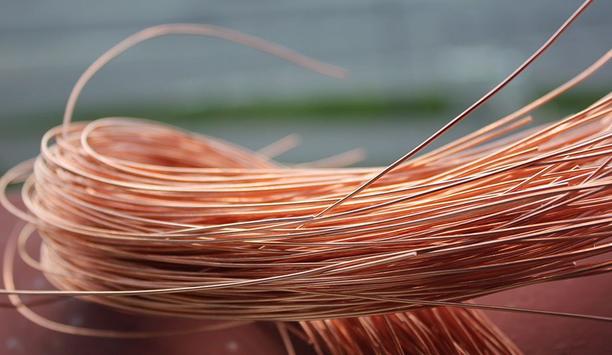
For decades, cable theft has caused disruption to infrastructure across South Africa, and an issue that permeates the whole supply chain. Here, Ian Loudon, international sales and...
According to IHS Market, it is estimated that there are over 60 million security cameras in the United States, and other reports say these cameras capture more than four billion ho...

Atlanta’s new $1.5 billion stadium, home to the NFL Atlanta Falcons football team and MLS Atlanta United soccer club and site of the recent NCAA national college football cha...
Latest Veracity news

Mayflex, the distributor of Converged IP Solutions, has strengthened its external security team with the addition of two new experienced and accomplished recruits. Jason Cooke joi...

Mayflex, the distributor of Converged IP Solutions, has appointed Richard Townsend in the role of Account Manager for Converged Technology with an emphasis on IP Security. ...

barox Kommunikation AG, the global manufacturer of professional standard switches, PoE media converters and IP extenders, is proud to announce its inclusion in the new Harper Chali...
Trending topic articles
It took just seven minutes to steal more than $100 million in jewels from the Louvre, in an operation so swift and precise it exposed a deeper flaw in how even the most secure institutions protect wha...
With Idesco Oy acquiring Exilight, effective January 1, 2026, they will start providing safety and emergency lighting products as part of the offering. Exilight products will remain under Exilight bra...
Hikvision, a world-pioneering manufacturer and supplier of security products and solutions that deliver the ideal combination of high performance and extreme value, now announced the release of its Hi...
Hornets Sports & Entertainment (HSE) and Honeywell announced a multi-year strategic partnership that designates Honeywell as the Official Building Automation Partner for the Charlotte Hornets.&nbs...
Dubai World Trade Center — Sheikh Saeed Hall 2, Stand C43, January 12–14, 2026. Organizations of every size and type have discovered how connected digital access helps them implement smart...
Integrated access control and security manufacturer TDSi is delighted to welcome Damian Garner to the team. Damian joins as New Business Sales Associate and brings over 20 years of sales an...
Kitakobushi Resort operates multiple distinctive properties in Shiretoko, Hokkaido – a UNESCO World Natural Heritage site since 2005. Their portfolio includes a large resort hotel overlooking th...
Alcatraz, the pioneer in facial biometric authentication for physical access, now announced the successful completion of its SOC 2 examination as of November 7, 2025. The independent audit was conduc...
Datalogic, a pioneer in automatic data capture and process automation, will demonstrate how its integrated portfolio is empowering the intelligent store at NRF 2026, thanks to AI-driven integration....
Deep Sentinel, the pioneer in AI-powered proactive video surveillance with real-time human intervention, now announced the launch of its Mobile Monitoring Trailer — a fully mobile, solar-powered...
The contract was signed, live at the SPS in Nuremberg, Germany: CADENAS is now the newest member of the Eplan Partner Network. CADENAS Managing Director Terry Jonen and Eplan Managing Director Ha...
AI is one of the fastest-growing technologies in the history of modern business, with the ability to revolutionize industries, optimize operations, and drive innovation, but it is also introducing sec...
Smeup, a key partner for companies engaged in digital transformation, now announced the expansion of its adoption of Cubbit, the first geo-distributed cloud storage enabler, as part of a Business Alli...
WatchGuard® Technologies now announced that its endpoint security solution delivered outstanding performance in the latest MITRE ATT&CK® Enterprise Round 7 (ER7) Evaluation. The results h...
EnGenius Technologies Inc., a pioneer in advanced connectivity and cloud-managed networking solutions, today announced that Crossroads Church in Rowlett, Texas, has completed a comprehensive security...
The Key To Unlocking K12 School Safety Grants
DownloadHoneywell GARD USB Threat Report 2024
DownloadPhysical Access Control
DownloadThe 2024 State Of Physical Access Trend Report
DownloadThe Security Challenges Of Data Centers
Download- Hitachi Rail Improves Digital Transformation Using NVT Phybridge Ethernet Over Coax (EoC) Switches
- Dallmeier Deploys Panomera Multifocal-Sensor System To Secure Gazprom Arena Prior To 2021 Euro Football Championship
- VIVOTEK Collaborates With Existo To Deliver A Comprehensive Surveillance Solution For Michigan Cannabis Cultivation Facility
- FLIR PT-Series Thermal Camera And SpotterRF’s CSR Systems Offer Perimeter Detection For U.S. Electrical Substations