Security access systems
They are excited to announce that RapidSOS is officially integrated with Apple Emergency SOS Live Video, now available with the release of iOS 18! Emergency SOS Live Video allows those in need to share streaming video and recorded media during emergency calls. During an emergency call, participating emergency dispatchers can send a request to share live video or photos over a secure connection, making it quicker and easier to provide urgent assistance. Emergency SOS Live Video ECC telecommuni...
HackerOne, the pioneer in human-powered security, revealed data that found 48% of security professionals believe AI is the most significant security risk to their organization. Ahead of the launch of its annual Hacker-Powered Security Report, HackerOne revealed early findings, which include data from a survey of 500 security professionals. Review of AI implementations AI red teaming offers this type of external review through the global security researcher community When it comes to AI, resp...
Permiso, the pioneer in identity security, has announced the launch of their Universal Identity Graph to provide risk and threat visibility for all identities, in all environments. The Universal Identity Graph combines industry pioneering Identity Security Posture Management (ISPM) with Identity Threat Detection and Response (ITDR) to provide the most comprehensive identity security solution in the market. Identity infrastructure “For most organizations, identity security is incredibly...
Pimloc a world-pioneering AI video privacy, redaction, and intelligence company announces a project pilot with Sussex Police and Microsoft. The collaboration helps to make multimedia redaction for subject access requests and digital evidence faster and more accurate through the implementation of cutting-edge artificial intelligence technologies, which marks the start of an exciting business development for Pimloc. Pimloc’s advanced AI Secure Redact is the ideal key for this union, as it...
As the backbone of community welfare, healthcare facilities cater to crucial public needs from emergency care to specialized medical treatments, and due to its position as a significant facet of the world's critical infrastructure, the healthcare sector faces a multitude of challenges in ensuring patient and visitor security, managing high traffic, and safeguarding sensitive data. Medical sites, such as large hospitals and urgent care clinics, see a wide variety of patients, medical staff, adm...
Dataminr, one of the world’s pioneering AI companies, is launching ReGenAI (Regenerative AI), a new form of generative AI that automatically regenerates textual descriptions as events unfold. Using predictive AI to analyze and synthesize key developments detected in more than one million public data sources, ReGenAI distills multidimensional events into concise event briefs that dynamically update. Regenerating event Customers can gain a rapid understanding of an evolving event th...
News
MERON, a new entry in the cyber-physical security marketplace, is showcasing its innovative new Physical Identity, Access and Incident Management solution branded MERON PIAM+ here at GSX 2024 in booth 1955. The new highly scalable, intelligent, and fully integrated platform leverages the most advanced modern technologies to establish new benchmarks in performance and cost efficiency for large enterprise applications. Advanced AI engine MERON PIAM+ uses the latest ideas in computer science including in-memory data frames MERON PIAM+ employs the latest concepts in computer science including in-memory data structures, infinitely scalable microservices, data management architecture, streaming data analytics and integration, and a highly advanced AI engine driving intelligent Co-pilots to automate tasks and workload of individuals. All this combines to deliver the fastest transactional performance and automatic self-healing processes to keep the application running, ensuring 99.9% uptime. New MERON PIAM+ platform “MERON PIAM+ resolves the significant shortfalls of older generation PIAM applications related to scalability, integration, security, cost efficiency, and the overall user experience,” said Imran Rana, Principal at MERON. “Our new MERON PIAM+ platform leverages new advanced technologies to deliver a comprehensive solution that is at least 300% faster than older PIAM applications and gets deployed in a fraction of time when compared to other applications.” Older-generation PIAM solutions MERON PIAM+ overcomes the numerous challenges of older-generation PIAM solutions as follows: Incomplete Identity Lifecycle Management: MERON PIAM+ eliminates the gaps in identity lifecycle management and the manual custom patchwork-laden deployments at customer sites, and the high support and maintenance costs associated with these processes. Need For Further Automation: MERON Co-pilots automate several tasks that are error-laden and manually done. Co-pilots work 24 x 7 x 365 in the background making the environment more proactive and predictive as opposed to being reactive. Cyber Vulnerability: MERON PIAM+ allows each microservice to have its own security measures tailored to meet the needs of each application, so if one microservice is ever compromised, it does not necessarily compromise other services. Limited Insights: MERON PIAM+ is an AI and data-centric platform that delivers real-time and offline analytics to derive actionable insights and detect anomalies before they materialize into potentially damaging events. Limited Scalability and Inflexibility: Unlike older generation PIAM software that is often built on monolithic architecture, MERON PIAM+ is built with microservices architecture that is easily and cost-effectively scalable, maintainable, and upgradable. Need for Incident Tracking: MERON PIAM+ integrates a real-time built-in incident management application with PIAM+ allowing users to effectively manage and track all incident types. Legacy Technology Stack: MERON PIAM+ employs AI-Co-pilots to automatically manage the platform, anomaly detection, self-healing of any fault, etc. Difficulty Upgrading: MERON PIAM+ offers a straightforward upgrade path as each microservices can be individually upgraded automatically while the system is up and running, minimizing system downtime. Slow/Costly Implementation: MERON PIAM+ is designed for rapid deployment utilizing preconfigured templates, workflows and rules resulting in deployment times that are up to 300% faster than existing PIAM applications. Poor/slow Performance: PIAM+ features a distributed data and event streaming platform to handle a high throughput of messages with minimal latency, ensuring data durability and reliability even in the event of hardware failures. Lack of API Support: MERON PIAM+ offers modern APIs that make integration with newer IT systems, cloud-based services, and IoT devices fast, easy, and more efficient. Inability to Support Modern Security Paradigms: MERON PIAM+ enables users to develop and enforce zero-trust models to best protect people and assets. Limited Innovation: Unlike MERON PIAM+, older PIAM applications are built on outdated technologies, which can make maintenance costly and resource-intensive, resulting in unwanted vendor-lock. Integrated solution “MERON PIAM+ offers many unique value propositions that challenge the status quo in the industry with a powerful, fully integrated solution that offers faster deployment, superior performance, future-proofed architecture, and lower cost of ownership,” concluded Rana.
A new entry in the cyber-physical security marketplace making its first public introduction, MERON is demonstrating a groundbreaking new solution for Physical Identity and Access Management (PIAM) branded PIAM+ here at GSX 2024 in booth 1955. MERON is launched by industry veterans Sharad Shekar and Imran Rana with the mission to usher in the next generation of AI-driven PIAM and Security Incident Management that overcomes the longstanding shortfalls of legacy solutions. Robust PIAM solution Meron is cloud agnostic and runs on cloud infrastructure like Amazon, Oracle, Microsoft, Google, and IBM MERON PIAM+ leverages the latest advancements in data science, artificial intelligence (AI) and micro-services architecture to deliver a seamlessly integrated, highly versatile and comprehensive PIAM and Incident Management application for on-prem or cloud deployment. Meron is cloud agnostic and runs on cloud infrastructure like Amazon, Oracle, Microsoft, Google, IBM, Alibaba, etc. “During the course of several consultation projects with pioneering companies over the past few years, it became quite clear that organizations with large numbers of employees and/or contracted workers are seeking a better, more robust PIAM solution that goes beyond legacy solutions,” said Sharad Shekhar, Principal at MERON. Creation of MERON technology Shekhar added: “This led to many discussions with longstanding partners and developers around the globe over the course of last two to three years, and the creation of MERON technology last year and public release of our new PIAM+ solution which we are debuting here at GSX 2024.” MERON PIAM+ delivers a comprehensive approach to managing identities over their entire lifecycle and securing physical access. It fully integrates identity verification, access control, incident management and security policies to ensure only authorized individuals can enter specific areas they have clearance to enter. Innovative PIAM+ solution MERON PIAM+ denotes itself from legacy applications by integrating advanced AI technologies This innovative PIAM+ solution streamlines the process of granting, monitoring, and revoking access, enhancing security and compliance while reducing the risk of unauthorized entry. By centralizing and automating these functions, MERON PIAM+ helps organizations protect their assets, ensure regulatory compliance and maintain more secure environments. MERON PIAM+ distinguishes itself from legacy applications by integrating advanced AI technologies, automation and analytics to provide enhanced security, efficiency, and adaptability. Launch of MERON PIAM+ The unique PIAM solution employs modern microservices-based platform architecture – a revolutionary approach that breaks down applications into smaller, independent services, each focused on a specific function resulting in unlimited scalability with improved system maintainability, support and upgradability. “We have already engaged with several large organizations who have expressed extreme interest in MERON PIAM+, and we are currently collaborating with select high-profile systems integrators with customer bases of large organizations,” continued Shekhar. “We are also now looking to further expand our business network, as well as our team of identity and access management technology and sales experts to further support the launch of MERON PIAM+.”
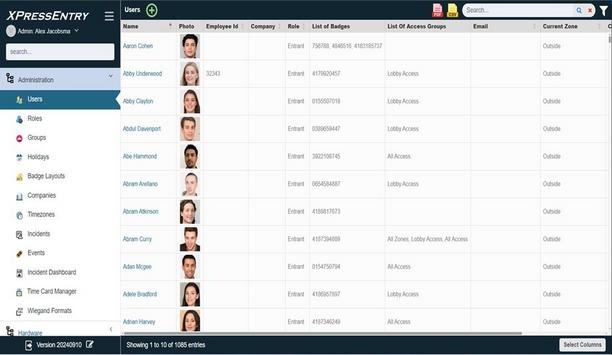
Telaeris, Inc., a global pioneer of handheld solutions for Physical Access Control Systems (PACS), announces its next-generation XPressEntry Admin Console at GSX 2024 (Global Security Exchange). New admin console The new admin console provides physical security and safety professionals a more efficient, web-accessible platform for managing XPressEntry including handheld badge verification, emergency mustering, events & training, biometric verification, entry/exit tracking, and much more. The new interface delivers simplified installation and enhanced user experience (UI/UX), enabling faster, more intuitive system administration conveniently from any workplace environment. XPressEntry Admin Console This unified, browser-based tool gives administrators the flexibility to access critical system data from any PC With the XPressEntry Admin Console and its 36+ industry-pioneering access control system integrations, security and safety teams can now oversee activities recorded in the access control system and manage the XPressEntry system including device configuration, real-time occupancy tracking, user role management, and more. This unified, browser-based tool gives administrators the flexibility to access critical system data from any PC with appropriate permissions, ensuring tighter security and safety oversight and operational efficiency. Key features for physical security and safety teams Seamless Access Control Integration: Ensure two-way communication between handheld devices and access control systems via configurable APIs and connection settings. Advanced Device Management: Control handheld reader profiles, activation of key features, and customization of validation screens to meet site-specific security protocols. User Role and Permissions Control: Manage who can access critical system data, configure security badges, and operate handheld devices in real-time. Live Data Monitoring & Reporting: Track entry/exit activity, occupancy levels, and handheld device statuses with real-time updates, supported by customisable reporting features. Robust System Configuration: Tailor protocols, security certificates, and settings for the organization’s unique security needs, whether deploying on-premises or via the cloud. Web Interface and Dashboard: Use any modern web browser to view and update any XPressEntry settings as well as see summary information in our updated dashboards. Addressing future security and safety challenges "The upgraded XPressEntry Admin Console aligns with evolving industry demands and web standards, offering security and safety teams the control and flexibility they need to protect both personnel and business interests effectively," said Dr. David Carta, CEO of Telaeris. "We are thrilled to launch the XPressEntry Admin Console and with this modernised solution, we have laid the fundamental groundwork for ongoing innovation, ensuring our partners stay ahead of future security and safety challenges." Physical access control systems XPressEntry handheld readers support the broadest range of badge technologies, biometrics, and facial recognition in the industry. As the first handheld solution integrating Android 13, XPressEntry handhelds provide enhanced performance and security to meet today’s complex physical security requirements. Visit Telaeris at GSX 2024 in Orlando, Florida for a live demo of the XPressEntry Admin Console at booth #1755, September 23-25, 2024.
Camelot Secure, a revolutionary new cybersecurity company, announced that it has been named a finalist in two prestigious categories for the 2024 Cybersecurity Association of Maryland, Inc. (CAMI) Cybersecurity Awards: Cybersecurity Innovation of the Year and Diversity Trailblazer of the Year. These awards celebrate Maryland-based companies and individuals driving innovation and promoting inclusivity in the cybersecurity industry. APT Hunting service Camelot Secure has made significant strides in cybersecurity innovation through its Advanced Persistent Threat (APT) Hunting service. The company’s Secure360 platform, which integrates AI, machine learning, and advanced threat intelligence, proactively detects and neutralizes cyber threats before they infiltrate critical systems. This groundbreaking approach has positioned Camelot as a pioneer in safeguarding businesses and government entities from evolving cyber risks. Inclusion in cybersecurity Camelot Secure is recognized for its duty to fostering variety and inclusion in cybersecurity As a Diversity Trailblazer of the Year finalist, Camelot Secure is recognized for its commitment to fostering diversity and inclusion in cybersecurity. The company actively engages with underrepresented groups, including partnerships with Historically Black Colleges and Universities (HBCUs), and creates pathways for minorities and underserved communities to thrive in cybersecurity careers. Camelot Secure’s CEO, Stan Oliver, emphasizes the importance of recruiting diverse talent and providing mentorship to cultivate a culture of inclusion and excellence. 2024 CAMI Cybersecurity Awards The 2024 CAMI Cybersecurity Awards winners will be announced on September 19th at the College Park Marriott Hotel & Events Center. For more information about the awards, please visit CAMI’s website. In addition to being a CAMI Finalist, Camelot is the recipient of many industry and cybersecurity-related honors, including: 2024 Security Innovator Award - Selected from passionately-written peer submissions, Camelot CEO Stan Oliver stood out from other applications as a trusted mentor who demonstrates exceptional leadership, innovation, and commitment to the cybersecurity industry. 2024 CSO Award from Foundry’s CSO - Camelot was honored for Myrddin, which integrates Natural Language Processing (NLP) technologies and the latest AI Generative Pretrained Transformer (GPT) to assist IT personnel in conducting Cybersecurity Maturity Model Certification (CMMC) gap assessments in a secure environment. 2024 Fortress Cybersecurity Awards - Camelot’s CEO Stan Oliver was named a winner in the Leadership category. 2024 Cybersecurity Excellence Awards - The company won the CEO of the Year, Best Cybersecurity Startup, and Advanced Persistent Threat (APT) Hunting awards. 2023 Top InfoSec Innovators Award - Cyber Defense Magazine recognized Camelot for its Advanced Persistent Threat (APT) Hunting offering. 2023 CSO50 Award from Foundry’s CSO - Camelot earned the honor for its CMMC eDiscovery Tool and its ability to significantly reduce the cost and complexity associated with CMMC compliance by focusing on the targeted identification and organization of sensitive data.
Securitas Technology, a world pioneer and global provider of security, health, and safety technologies, unveiled its Sustainability Initiatives, a pioneering effort to promote environmentally sustainable solutions in the electronic security industry. This initiative will be launched at the Global Security Exchange (GSX) 2024 show, September 23-25, in Orlando, Florida. Consumption of security devices Securitas Technology incorporates data on greenhouse gas emissions in all new sales proposals As part of this initiative, Securitas Technology will now incorporate data on greenhouse gas emissions in all new sales proposals to clients and prospective clients in the United States and Canada. The information will be calculated based on the annual energy consumption of security devices or systems, expressed in CO2 equivalent. Research shows that approximately 70% of the lifetime emissions of electronic security equipment are attributed to power consumption. Committed technology partners “Achieving a more sustainable future requires collective action, and sustainability is increasingly at the forefront of our clients’ priorities,” said Tony Byerly, Global President and CEO, Securitas Technology. “We are proud to step out and lead the industry to be more environmentally responsible, alongside our committed technology partners who have provided essential data for this important initiative. By offering clients accurate data on the emissions from the power consumption of our solutions, we empower them to make informed choices that not only enhance security but also reduce the environmental impact.” Data for client proposals Emissions data for client proposals developed in collaboration with Securitas Technology The emissions data for client proposals has been developed in collaboration with Securitas Technology’s strategic partners, representing many of the world’s pioneering manufacturers and innovators in the security industry. “As the world’s second-largest commercial electronic security company, we take our leadership role in seeing a different world seriously, and this is just the start of our journey,” declared Byerly. Expanding remote services In addition to providing emissions data, Securitas Technology is committed to expanding its remote services to help clients reduce or eliminate travel to sites and the associated emissions. The company aims to help clients minimize their environmental footprint through insights on occupancy patterns to optimize heating and lighting, transitioning clients to more efficient cloud-based systems, and building a more sustainable security ecosystem. Sustainable security solutions “Just as every client has unique security needs, they also have specific sustainability targets,” said John Tomin, Global Sustainability Officer, Securitas Technology. “By gaining a deep understanding of these challenges from the outset, we can work in partnership with clients to offer more sustainable security solutions that contribute positively to our shared sustainability goals.” Aligned with the SBTi Securitas is the first security solutions firm to have its sustainability targets validated by SBTi The Sustainability Initiative is structured to align with the Science Based Targets initiative (SBTi), a global commitment made by Securitas AB, the corporate parent of Securitas Technology. Securitas is the first global security solutions company to have its sustainability targets validated by SBTi, committing to reducing absolute scope 1, 2, and 3 greenhouse gas emissions by 42% by 2030 from a 2022 base year. This commitment is aligned with the Paris Agreement’s 1.5-degree Celsius goal. Expanding remote service Securitas Technology measures and reports on its sustainability progress under the SBTi framework annually. The company is actively pursuing several actions to reduce its own emissions, including the adoption of circular economy practices, and expanding remote service offerings, among many other considerations.
Salient announced CompleteView v7.5, the latest update to its industry-leading video management platform. This version introduces improvements to operator experiences as well as major new enterprise capabilities. Seamless user experience To better address the needs of the enterprise market segment, v7.5 introduces federation, storage encryption, and export encryption. Federation provides a seamless user experience across multiple sites while avoiding a single point of failure. This feature is especially valuable for large, geographically distributed deployments. Native support for storage encryption and export encryption ensures that video surveillance data is protected at rest and not mishandled for use as evidence. Federation and encryption capabilities “The federation and encryption capabilities are significant for enabling Salient to better serve the enterprise market segment,” said Ed Batchelor, COO at 4S Security. “Salient already has an impressive VMS which scales well in terms of performance and capability from small organizations to large, multi-national enterprises. We are excited to accelerate growth with Salient in the enterprise segment with these major new features.” CompleteView v7.5 The mobile apps are fully compatible with Salient’s cloud services and enable simple, secure remote access The v7.5 release improves the experience for operators with a new Android app, an updated iOS app, and a major improvement to the video search capability in the CompleteView VMS. The mobile apps are fully compatible with Salient’s cloud services and enable simple, secure remote access to live and recorded video. The video search experience has been updated with improved timeline and playback controls along with a more intuitive configuration of search parameters to boost investigator efficiency. Access live and recorded video “At Isringhausen Imports, we rely on Salient’s CompleteView mobile app to easily access live and recorded video from anywhere in the world,” said Jack Patrick, Director of Information Technology at Isringhausen Imports. CompleteView v7.5 is available and can be downloaded from the MySalient portal. "The iOS and Android app improvements in the v7.5 release are highly anticipated and will greatly improve the mobile experience for our team."


Expert commentary
As we head into a new year, it’s fair to say that it isn’t easy out there for the security integrator community. That’s understandable given the big ruptures felt in the market for physical security in 2023. Typically, Commercial Real Estate (CRE) landlords are the biggest and most influential buyers of physical security hardware and software, but this is starting to wane as heightened borrowing costs and biting inflation cause real estate valuations to plunge. Building security upgrades A lot of CRE landlords are in a fight for survival which unfortunately doesn't leave much room for budget spend on building security upgrades. This state of affairs is a problem for security integrators with extensive connections in the CRE space. Where do they pivot their services to keep their business growing in 2024? From the conversations I’ve been having with integrators and customers alike over the past few months – the answer is that the growth potential lies in the enterprise space. The trajectory of enterprise IT and physical security Aren’t enterprises carrying out cost-cutting efficiency drives and downsizing office space to reflect hybrid working It might initially feel unnatural to see the enterprise segment as a potential driver of demand for physical security services and products. Aren’t enterprises carrying out cost-cutting efficiency drives and downsizing office space to reflect hybrid working habits? These things are true but also present an opportunity for the right physical security proposition. Standardization of enterprise IT Take efficiency drives as an example. A key element of such efforts is an acceleration toward the standardization of enterprise IT platforms, hardware, and solutions, using the cloud. What was once a focus on moving on-prem systems and workloads to the cloud has shifted to efforts to keep cloud OpEx costs down by centralizing as much as possible. Practically, this means utilizing APIs to plug disparate IT applications and services into central platforms that boast a “single pane of glass” view. APIs APIs drive consumption, open new business models, and foster cross-industry partnerships APIs aren’t anything new to enterprises. They drive consumption, open new business models, and foster cross-industry partnerships. However, the use of APIs in the physical security sphere has been surprisingly slow to take off. There are multiple elements to this but a key reason is that some security software products on the market aren’t cloud-based. Adding cloud-based solutions to network Others are cloud-based, however, and these are the solutions that security integrators need in their portfolio to serve the influential enterprise market segment and its approach to IT networks. Selling the value of these solutions requires integrators to take it a step further by speaking the language of the enterprise IT buyer and understanding their goals. The power of Cloud-based access control in the enterprise Hybrid working and the occupancy rate fluctuations it brings require closer monitoring of access events The continued relevance of physical security for enterprises can’t be understated. After all, hybrid working and the occupancy rate fluctuations it brings require closer monitoring of access events – not less. Despite the discourse around office downsizing, the reality for most enterprises is that the office can’t be done away with completely and there’s always going to be growth experienced by successful companies that require an upgrade in physical square footage. Physical security Access control systems that are cloud-based will be preferred by the enterprise to fulfill the essential function of physical security. That’s because they align with the push towards centralization in the cloud that enterprises are carrying out business-wide. Access control has the potential to result in lots of disparate dashboards and apps. Think video management, license plate recognition, building management software, elevator monitoring, hot desking solutions, guest booking software, room booking functions, and more. Uniting all of these functions in one platform suits enterprise security teams well. Access control solutions Linking employee databases to an IAM solution, or creating seamless experiences by tying access credentials But this only scratches the surface. Access control solutions that can be integrated with hugely popular corporate software applications like Okta, Azure Active Directory, and Google Workspace quickly catch the eyes of enterprise IT security teams by pulling in the same direction as the broader tech stack. Whether it’s applying AI analytics to anomaly detection, linking employee databases to an Identity Access Management (IAM) solution, or creating seamless experiences by tying access credentials to things like meeting room bookings, it’s through APIs that cloud-based access control can thrive in an enterprise setting. Security integrators It’s worth also noting that as enterprises grow, access control gets harder. Managing the access requirements of thousands of employees across a global real estate footprint requires the scale that cloud computing is best placed to bring. Security integrators who can join the dots to make that link are well-positioned to pivot toward the enterprise. Broadening horizons Concepts like smart access and applying AI to access data to automate the monitoring of occupancy rates This pivot is understandably a daunting prospect but the potential for natural synergy shouldn’t be overlooked. Concepts like smart access and applying AI to access data to automate the monitoring of occupancy rates and security anomalies won’t be completely alien to cloud-first enterprises. That’s an opportunity for integrators to upsell more sophisticated security set-ups in a way that they may have found more difficult with CRE clients and prospects. Tailored propositions It would be remiss to avoid mentioning that ‘enterprise’ is a very loose term that encompasses businesses across multiple industry verticals. To better pivot, security integrators need to offer tailored propositions specific to set verticals that cover all bases as opposed to offer, for example, piecemeal alarm or video product solutions. Enterprise industry verticals Security integrators should be weary of all-encompassing narratives in 2024. Whether or not the global economic picture darkens, there are always going to be pockets of growth within certain enterprise industry verticals. Plus, anecdotally, the indicators point to enterprises being the driver of demand for cloud-based access control as we head into the new year. Integrators who can dial into that shift have a lot to gain and nothing to lose.
When a bomb detonated in the Port of Beirut, I had hundreds of employees under my care inside the blast zone. Within just two hours, I was able to determine who was impacted, understand their safety conditions, and share resources for on-the-ground support—all thanks to mobile technology. For Chief Security Officers, receiving calls like these launches a variety of protocols and necessary decision-making with the safety and security of people and assets as a top priority. And these calls are only becoming more common. Dependence on threat intelligence Mobile phones have dominated the post-COVID environment where people work from anywhere Threats ranging from natural disasters to geopolitical conflicts are becoming more frequent and complicate the responsibility organizations have in keeping their people safe. To meet these needs CSO’s are staying ahead of negative outcomes through creating a greater dependence on threat intelligence. In these times, effective, real-time risk management depends on hyper-local data from technology that is accessible, portable, and dynamic – such as cell phones. Mobile phones have revolutionized the way people live and work. They allow us all to walk around with a computer in our pocket, bringing the world to our fingertips and eliminating digital borders for over 90% of the world's population. Mobile phones have dominated the post-COVID environment where people work from anywhere and have geographically distributed teams but are also more vulnerable to threatening events. Mobile-friendly risk management platforms Mobile technology assigns workers with easy entry to data that can help keep them and their teams safe As we approach 2024, many organizations are adopting comprehensive risk management tools that empower personnel across the organization with the intelligence and knowledge they need to stay safe wherever they are. Mobile-friendly risk management platforms, such as Crisis24 Horizon, provide always-on awareness, on-hand threat intelligence, and immediate communications and distress signaling through location monitoring. Users receive location risk assessments and push notifications directly to their devices about nearby issues and threats no matter if they are on or off the job. While only select risk managers have complete control of the platform and all sensitive employee data is protected through encryption, the app distributes critical intel to foster a culture of shared awareness and responsibility. Thus, mobile technology empowers employees with easy access to information that can help keep them and their teams safe. Creating a culture of mobile technology adoption In the last few years, the world has proven the importance of being well-informed of risks and mitigation plans to minimize harm. However, psychological barriers tend to trump physical barriers when it comes to accessing the vast array of tools our mobile devices offer. World has proven the matter of being well-informed of risks and relief plans to minimize harm Adopting this technology and establishing a culture that enforces risk management across an organization is a daunting challenge that demands substantial commitment from leadership to be successful. Some companies have tackled this challenge by positioning security technology as part of the organization’s employee benefits package, such as commuter benefits and health insurance, to encourage people to take advantage of these resources and learn how to use them. Cohesive risk management culture Technology is only as effective as the people whose actions it informs, which is why adoption and integration are so important. When a cohesive risk management culture meets a powerful technology platform, individuals are enabled to receive threat alerts and counter their impacts, letting others know when and how to take the necessary precautions to protect themselves and their team. For more information on mobile technology and other security trends, check out the Global Risk Forecast, an annual report by Crisis24 that provides a comprehensive analysis of key events around the world most likely to affect operations in the coming year.
These days, business is more collaborative, adaptable, and connected than ever before. In addition to offering new identities and access privileges, new applications and data also increase the attack surface available to cyber criminals, hacktivists, state actors, and disgruntled insiders. These new identities need to be handled carefully. CISOs must develop an identity management strategy that is consistent across on-premises, hybrid, and cloud systems. Good security is built on solid identity governance and administration (IGA) principles. From ransomware to supply chain intrusions, high-profile cybersecurity events frequently take advantage of weak identity and access management procedures. The Identity Defined Security Alliance found that 84% of organizations experienced an identity-related breach during its one-year study period. Robust IGA system Consequently, organizations need to find best-of-breed solutions for each section of the fabric Some of the most well-known cyber-attacks have not been made possible by a nation-state exploiting a remote zero-day vulnerability; rather, they have been made possible by something as basic as a hacked orphaned account. This resulted in lateral movement from an insecure platform to a high-value system, illegitimate privilege escalation, or unsanctioned access to a computer system. To safeguard against such attacks, organizations must be aware of who has access to their systems and apps, and guarantee that access is revoked when it is no longer required. Here, a robust IGA system is helpful. It is not the whole picture, though; IGA is part of a larger identity fabric. A report by KuppingerCole noted that “Identity Fabrics are not necessarily based on a technology, tool or cloud service, but a paradigm for architecting IAM within enterprises.” The report pointed out that the paradigm is created using several tools and services. That’s because, contrary to marketing claims, no one vendor has a platform that provides all the needed elements. Consequently, organizations need to find best-of-breed solutions for each section of the fabric. Threats to the new corporate landscape Due to their exclusion from the corporate firewall and the security culture that comes with working on-site, remote employees and third parties are desirable targets for hackers. The transition to online office suites is another vulnerability that hackers are taking advantage of–for instance, through bogus authentication login dialogs. Additionally, hackers are using technologies like machine learning and artificial intelligence to circumvent current security tactics. A cyberattack powered by AI will imitate human behavior and develop over time. Even publicly available information might be used by this "weaponized AI" to learn how to get past a target’s defenses. CISO and the business users Attackers will finally find an entryway, but firms can protect the new perimeter–their identities It's no longer possible to secure the traditional perimeter. Attackers will eventually find an entryway, but businesses can protect the new perimeter–their identities. To defeat these threats, organizations must look again at identity and access management tools and how they are weighed against the impact on the organization. Should you mandate multi-factor authentication (MFA) more often and earlier? Should only company-owned devices have access to networks, or should access be restricted to specific business hours or regions? Should access to sensitive information and critical systems be given just temporarily or should it be offered on a task-by-task basis? Both the CISO and the business users they assist should be asking these questions. Staying ahead of threats with identity Access control limits decrease dangers but can come with a cost. If you give your users too much access, your organization becomes susceptible; if you give them too little, productivity suffers. But there are ways to strike a balance with security, compliance and productivity. More CISOs are turning to Zero Trust–which is based on the principle of maintaining strict access controls and not trusting anyone by default–to protect their systems from new attack types. However, Zero Trust is reliant upon having a thorough and baked-in strategy that underpins it. Other actions that companies can take include implementing automation for identity management, such as automating workflows for approval. This would significantly lessen the administrative burden and friction that security solutions like multifactor authentication (MFA) or time-restricted access to critical systems have on business users. This might include restricting access to particular devices, capping access hours during the day or enforcing MFA based on user behavior. Identity fabric: Putting it all together Make sure your identity architecture is scalable, secure, and provides a seamless user experience These are just two elements of the identity fabric approach. Most organizations today have implemented pieces of an identity fabric, which is basically an organization’s identity and access management (IAM) infrastructure and typically includes a mix of modular IAM solutions for multi-cloud and/or hybrid environments. Now, organizations need to define, enhance and develop this infrastructure. They must also institute guiding principles for how it should operate, meet current and future business requirements as well as identity-related cybersecurity challenges. In doing so, businesses can move past identity platforms and adopt an identity fabric perspective. The key is to make identity governance the starting point of your identity fabric strategy, ensuring seamless interoperability within your identity ecosystem. Make sure your identity architecture is scalable, secure, and provides a seamless user experience. Aligning security with business Due to the increase in knowledge workers using the cloud and working remotely, attackers are focusing on this group. These employees are easier to compromise, give access to valuable data and offer more attack targets. Knowledge workers also lack an administrator’s level of security expertise. Therefore, as part of their security fabric strategy, enterprises require a scalable IGA system. It is easier to comply with security and access regulations and takes less time for IT teams to do normal administrative activities when they invest in IGA, a crucial tenet of identity security. CISOs and boards, though, are currently looking at more than identity management. IGA is at the center of the debate about security and governance. Taking an identity fabric-based approach, with a foundation built on modern, cloud-based IGA, will safeguard identities, increase productivity, and make staff adherence to organizational procedures easier.
Security beat
Active shooter situations grab the most attention, but there is a long list of other threats facing schools, including bullying, vandalism and emergency medical situations. Broadly speaking, a comprehensive approach to school security should prioritize prevention, preparedness and response to all threats. Holistic security approach “Fostering a culture of safety within a school, which involves strong relationships, trust, and communication, is highly effective and does not require significant costs,” says Christin Kinman, End User Sales Consultant with Allegion, a security manufacturer. “It is crucial to educate stakeholders about the unintended consequences of quick fixes, like barricade devices, to ensure informed decision-making and a holistic security approach. The goal should be to promote safety and security for all, every day, in every situation.” Integrated and successful security plans While this might solve a particular challenge, it can also create unintentional conflicts" "Creating an integrated security plan requires a multi-faceted approach," says Kinman. "Too often, security measures are implemented as a reaction to either an event or a specific vulnerability. While this might solve a particular challenge, it can also create unintentional conflicts," adds Kinman. “Creating a successful security plan involves a comprehensive approach,” she says. “An effective, systematic approach begins with assessing, identifying, and valuing assets, identifying threats and vulnerabilities, quantifying the impact of a loss, analysis, and prioritization, and finally, development of mitigation measures.” Safety and Security An effective resource is the Partner Alliance for Safer Schools (PASS), which provides a framework to help with school assessments, including identifying and valuing assets, identifying external threats and internal vulnerabilities, assessing the impact of loss, and analyzing and prioritizing mitigation measures. Safety and security are words used seemingly interchangeably when it comes to schools, but they mean different things. “How we define these terms influences planning and addressing challenges,” says Kinman. “It is easiest to think of these terms as being either external or internal to the individual.” Coordinated security Safety is internal to the individual and relates to the individual’s perception of being free from harm Security is external to the individual and encompasses the protective physical, emotional, and environmental measures implemented in conjunction with policies, procedures, and training, as well as mental health measures and social and emotional learning. Safety is internal to the individual and relates to the individual’s perception of being free from harm or danger. Coordinated security measures create an environment of safety. Four main elements of physical security Kinman lists four main elements of physical security, often referred to as the 4D’s. These elements are deter, detect, delay, and deny: Deter refers to measures implemented to prevent an attack or threat from happening. These are usually visual deterrents that communicate legitimate use. Detect refers to measures that can detect the presence of a threat, such as video surveillance and monitoring. Delay refers to measures that slow down an attack or increase the level of effort needed for an incident to occur. Finally, deny refers to measures that prevent or restrict access to valued assets. Four layers of ground perimeter A layered approach to school security creates “layers” that must be defeated for an event to occur, says Kinman. Typically, the four layers are the ground perimeter, the private grounds around the building, the building perimeter, and the building interior. The ground perimeter layer demarcates public vs private space, and deterrence is the primary objective. The grounds layer allows for identification of legitimate vs illegitimate users and detection is the primary objective. The building perimeter layer prevents illicit users’ intent on harm from gaining access. The primary objectives at this layer are delay/deny. The building interior protects the most valuable assets, and the denial of an unauthorized individual is the primary objective. Report on Indicators of School Crime and Safety The second element is impact, also rated on a scale of 1-5 and ranging from negligible to catastrophic “Quantifying loss and assessing risk is one of the most important steps in creating an integrated security plan,” says Kinman, who explains that the two elements that guide this step are probability and impact. Probability is the likelihood that an event will occur, typically rated on a scale of 1-5 ranging from rare to almost certain. The second element is impact, also rated on a scale of 1-5 and ranging from negligible to catastrophic. “Probability multiplied by impact equals risk, which has a score ranging from 1-25,” says Kinman. “The higher the score, the higher the risk.” An analysis of vulnerabilities and threats using a matrix yields a systematic approach to prioritize improvements and identify mitigation measures. For statistics on crime and safety in schools, visit the Report on Indicators of School Crime and Safety: 2022. Security improvements “The costs of school security encompass various aspects, including physical measures, personnel, training and policy enforcement,” says Kinman. “While there is no fixed amount, it often involves investments in technology, such as access control and emergency response systems. Many security improvements do not require additional funding, like training staff and students on security protocols and implementing policies to create a culture of safety.” Generally, funding for public school security is a shared responsibility among federal, state, and local governments; communities also contribute. “Striking a balance between shared responsibility and ensuring adequate resources is crucial for effective school security,” says Kinman. K-12 school security Community members and parents can donate by being vigilant and noting any suspect activities Various stakeholders play crucial roles in enhancing K-12 school security in addition to schools and communities. Stakeholders include community members, parents, local government, local law enforcement, first responders, and non-profit organizations. “Engaging these stakeholders fosters a comprehensive approach to school security,” says Kinman. Community members and parents can contribute by being vigilant and reporting any suspicious activities. Local government can support schools with funding and resources, while local law enforcement and first responders can provide expertise, conduct drills, and establish emergency response protocols. Safe and secure learning environment In addition, non-profit organizations can offer valuable resources, training, and support programs to address specific security concerns. “By involving all these stakeholders, schools can tap into a diverse range of expertise, resources and perspectives, pioneering to a more effective and comprehensive approach to school security,” says Kinman. “Collaboration and communication among these entities are vital to ensure a safe and secure learning environment for students and staff.”
Companies at GSX 2023 emphasized new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasizes ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the Mid-Market to the Cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for pure cloud, but there are benefits to be realized from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realize the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘Soft’ Features for Integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organization more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organization more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centers around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasizing performance, protection (cybersecurity), and price, their data centers are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring center where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
A pioneer in the access control sector since 1971, AMAG Technology is looking to the future and the next generation of products that will expand its services to customers. “In our vision, we have advanced approaches that will not only provide our partners with advanced technologies but also ones that are easier to install with tools to expand their services,” says David Sullivan, who was appointed President of the venerable access control company in September 2022. New challenges at AMAG Sullivan brings a new outlook to the AMAG business, a part of Allied Universal, and a new vision to lead the company into the future. We caught up with David Sullivan to discuss his new challenges at AMAG and the journey ahead as the company looks to the future. Q: How does your background inform your approach to leading AMAG? I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry David Sullivan: With the exception of only a few short years, my career has been in access control. I have experience with several systems and have had the privilege to manage several successful access control companies. As a result, I bring a great deal of experience into my role at AMAG. I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry. Q: How would you describe AMAG’s journey over the last several years and how do you see the future? Sullivan: Prior presidents of AMAG always shared their leadership vision and direction with senior leaders located in the United Kingdom. This had an impact on the full direction of the business, sometimes limiting its ultimate success. Before I became a part of AMAG, these senior leaders that were located in the UK retired, placing for the first time the full management responsibilities of the president. This has allowed me to integrate the business into a single team, with single objectives, and a single vision. We expect to begin to reveal this new vision in the coming weeks. We are excited about the future of AMAG and believe we will surprise the industry with our new products and approach in the coming months and years. Q: How important is it that a manufacturer provides both hardware and software solutions? How does AMAG’s approach (in general) differentiate it in the market? We can design the complete solution, providing functionality that others may find more difficult to accomplish Sullivan: Regardless of the manufacturer, we all provide hardware and software. An access control solution is not complete without both. Some of us choose to make our panels, and others do not. Those who are dependent on third-party suppliers are restricted to the developments and direction of that company, and while it might be perceived to be an open technology, it still is proprietary to the hardware manufacturer. AMAG has controlled its manufacturing of panels from day one. The result means that we can design the complete solution, providing functionality that others may find more difficult to accomplish. Q: How does the breadth of AMAG’s product suite provide advantages to customers and/or integrators? Sullivan: AMAG’s product portfolio is unique and provides the end user with an end-to-end identity management solution from one company. Our Control Room PSIM, Symmetry CONNECT Identity Management Solution, Symmetry Access Control, and Symmetry GUEST solutions all integrate to provide the user with a broad set of features and capabilities from a single provider. There is no finger-pointing when we come to support your system. We hold full responsibility for making it work and can quickly provide a resolution to any application difficulties the user may be experiencing. Q: How does AMAG address the divide between on-prem and cloud systems? How do you help customers make the transition and/or plan for the future? We are in the early stages of developing our next generation of access control in which we intend to provide on-prem Sullivan: In our current product portfolio, we have three products that are cloud-based. Our mobile credential platform (Symmetry Mobile), our visitor management solution (Symmetry GUEST), and our physical identity and access management solution (Symmetry CONNECT) are all offerings that operate in the cloud. We are in the early stages of developing our next generation of access control in which we intend to provide on-prem, web client, and cloud-based offerings. One of the primary objectives is to ensure that the large installed base of systems that are out there today will be able to migrate not only to our next generation but as well to the cloud if the client so desires. Q: What is AMAG’s approach to mobile credentialing? Sullivan: As an access control provider, adding Symmetry Mobile credentialing to our portfolio just made sense. We want our customers to have a forward-thinking solution with the opportunity to save money not only on the physical badges but the cost of printing and distributing badges. Mobile credentials can be easily issued and revoked remotely, reducing administrative overhead, and eliminating the need for physical inventory management. Organizations can centrally configure what devices are used and the read range for each type of device and operating system, thus providing flexibility. Symmetry Mobile offers a customized questionnaire that controls access and reduces liabilities. Q: What has surprised you the most in your first year or so leading AMAG? Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company Sullivan: I wouldn’t say I was surprised by this as much as happy to see, but I would say that the quality of our people was a pleasant surprise. As well, the AMAG product offering is broad and has some unique elements. When coupled with the depth of the resources that we have in AMAG, I know that we are second to none. Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company that has so many talented people. Q: Please describe your dealer channel, and how you are seeking to expand it. Sullivan: The AMAG products are sophisticated and typically are installed for higher-end applications. With this sophistication comes a need to be well able to install such a solution. We have a strong group of certified and loyal partners who help us to deliver these enterprise solutions. We desire to provide our existing partners with updated and competitive systems to offer to their end users. Q: What is the security industry’s (and/or AMAG’s) biggest challenge in the next five years? We need to find ways to provide both our channel partners and the customers with solutions that are easily integrated Sullivan: I believe that the advancements that we are seeing in technology provide our industry with the opportunity to truly change how security is provided to our collective customers. As we advance these solutions, we will need to do so responsibly and in a way that helps the channel’s abilities. We need to find ways to train our partners to both install and support these more complex solutions. At the same time, we need to find ways to provide both our channel partners and the customers with solutions that are easily integrated, moving away from proprietary closed systems to open and cohesive solutions. This will ensure that the users get the best, and most complete solutions. Q: What does the industry as a whole misunderstand about AMAG -- time to set the record straight! Sullivan: Well, I am not ready to openly share where we are heading. We are in the process of putting together some advanced approaches to how we will do business with our partners. We are focused on providing tools that will enhance their services to their customers, and with products that are leading edge. I can only state that all should keep their eyes on AMAG, because over the next few years, we are going to surprise some people, and more importantly make our loyal partners quite powerful.
Case studies
OPTEX, the pioneering global sensing manufacturer, has specified and installed its compact and intelligent REDSCAN RLS-2020 LiDAR laser sensors at the new luxury five-star Londoner hotel in Leicester Square. Part of the Edwardian Hotels London group, The Londoner, which opened in September 2021, is billed as the world’s first super boutique hotel. It has 350 rooms across 16 storeys including six basement levels, featuring six concept eateries, a private members club, a cinema, a wealth of meeting and event space and an entire floor dedicated to health and wellness equipped with a gym, pool, and spa. Existing security system The hotel has six restaurant & bar areas in total with expensive whiskeys, wines, and other drinks on display 24/7 with no shutters or coverings. Given the cumulative value of the drinks behind each bar, the hotel needed to find a security solution to keep its valuable stocks protected. The solution needed to be accurate and reliable, and capable of integrating with the hotel’s existing security system, as well as being aesthetically discrete. REDSCAN RLS-2020 laser sensor OPTEX specified and installed its REDSCAN RLS-2020 laser sensor in the ceiling at each of the seven bars OPTEX specified and installed its REDSCAN RLS-2020 laser sensor in the ceiling at each of the seven bars. The RLS-2020 sensors provide a customizable ‘virtual’ wall or plane that cannot be seen by the naked eye with a 95-degree detection area of 20x20m or 30m radius detection range. The laser technology works by analyzing the speed, size, and distance of the objects detected, meaning they track the objects within the detection area and understand the ratio size/distance of the object. This provides the ability to accurately detect a specific size of the object either at a distance or close up. In the event of any movement being detected, a security alarm is raised, and alerts are immediately sent to the 24-hour on-site security control room. OPTEX laser sensors Darren Carter, Group Director of Safety, Security and Sustainability at Edwardian Hotels London, says OPTEX has provided the ideal solution: “We’ve worked with OPTEX for a number of years, and installed their technologies at a number of our other hotels in the group." “For this new and hugely exciting project, there was nothing else on the market that met our brief. The OPTEX laser sensors are a simple, yet highly effective solution, providing the very highest level of detection that easily integrate with our wider security operation at the hotel.” Partnership with Darren Ben Linklater, OPTEX Commercial Director, says OPTEX’s LiDAR technology delivers the greatest accuracy of detection: “We are constantly working to improve our technology to provide the highest quality sensing solutions,” he says. “Working in close partnership with Darren and his team, we were able to provide a highly accurate detection solution that met their requirements. We are proud to have worked on such a prestigious project, with the Londoner set to become one of the world’s most talked about hospitality experiences.”
Munich’s Hofbräuhaus enjoys an iconic status, as both a heritage property and a spiritual home for lovers of German beer. “In this historic building is the world’s most famous tavern,” explains its Security Manager, Robert Graßl, adding “The whole world goes in and out. Security is very important.” Bavarian Duke Wilhelm V commissioned Munich’s original Hofbräuhaus in 1589, initially as a brewery to supply the Wittelsbacher Hof. Moved at the end of the 19th century and severely damaged during World War II, it underwent reconstruction in 1958. It now attracts tourists and city locals, seating up to 3,000 guests indoors and a further 400 in the beer garden. Access rights management Digital devices and low-impact skills were needed to assure compliance with origin protection Although the building is an important heritage monument, it requires 21st-century digital access to keep site users safe and streamline day-to-day operations. They wanted fast, secure access rights management for employees and service providers – including up to 100 waiters working each shift – within a unified system that could authorize access at both the Hofbräuhaus and their food production facility in Brunntal. Of course, inobtrusive digital devices and low-impact installation were a necessity to ensure compliance with heritage preservation regulations. Digital access for a famous heritage building Many electronic access products and technologies are not appropriate for historic buildings. An eCLIQ key-based digital access solution is different: eCLIQ cylinders are compatible with the strict monument preservation requirements at the Hofbräuhaus. They have a flush fit, so don’t even appear to be part of an electronic locking system. With wireless installation at the doors, devices blend with the building interior. “We can exchange a mechanical cylinder 1:1 with an eCLIQ cylinder without having to modify anything on the door or install cables,” confirms Miriem Hammoudi, Business Development Manager at ASSA ABLOY Sicherheitstechnik GmbH. ASSA ABLOY fitted around 100 eCLIQ locking cylinders and supplied 340 eCLIQ programmable keys for Hofbräuhaus managers to issue to relevant staff and service contractors. Easy operation for flexible, cost-efficient management Every eCLIQ key has an integrated chip and is programmable individually for the keyholder Every eCLIQ key has an integrated chip and is programmable individually for the keyholder. The versatility of eCLIQ is demonstrated when a key is lost: Access authorizations are removed rapidly – simply by reprogramming cylinders – ensuring security is maintained. The eCLIQ system also helps manage workflows for service providers, such as cleaners: Their access is enabled on a time-limited basis. A standard battery inside each programmable electronic key powers the cylinder or padlock on insertion – and encrypts data transfer between cylinder, key and system – so no external power source or wiring is needed. Scalable web-based platform The Hofbräuhaus team manages their system via a flexible, scalable web-based platform, CLIQ Web Manager: “I can program keys from anywhere or also block them quickly if a key has been lost or if someone is no longer allowed to enter,” says Robert Graßl. He adds, “And I can install any cylinder in any door by adjusting the length. I don’t have to carry extra stock which is really cost effective.” New master key system With the hosting solution chosen, access data is stored securely at ASSA ABLOY, accessible anytime and from any location, which is an ideal configuration for managing large systems or multiple locations. Their system is easy to expand anytime – future-proofing Hofbräuhaus access. “The situation before the new master key system was installed was problematic,” says Robert Graßl, adding “Keys were distributed and nobody knew who held them. Now, everyone carries only one key programmed with details of where and when they can enter. It’s perfect.”
In response to the increased demand for oxygen supplies following the 2020 pandemic and subsequent rise in respiratory-related conditions, Jacksons Fencing completed a key project in 2024 to safeguard vital oxygen storage facilities at a pioneering UK hospital. Addressing the demand The pandemic highlighted the critical role of oxygen in treating patients, causing a surge in its use across hospitals. Some facilities even declared major incidents due to oxygen shortages, prompting a significant government investment of over £15 million to upgrade oxygen supplies and prevent future disruptions. As part of these improvements, many larger hospitals have started to feature on-site liquid oxygen storage facilities, where vast industrial tankers convert liquid oxygen to gas as needed. Securing essential resources Jacksons Fencing provided and installed a comprehensive security solution for a new oxygen storage compound Given the stringent safety requirements associated with liquid oxygen due to its extremely low temperatures, precise pressure needs, and related fire and explosion risks securing and managing these supplies is paramount. To address these needs, Jacksons Fencing provided and installed a comprehensive security solution for a new oxygen storage compound. Robust fencing solutions with invisible screen The installation includes 38 meters of Securi-Mesh® fencing, standing at a robust height of 2.4 meters. This fencing is mounted on concrete hardstanding and is complemented by two cantilever sliding gates and a single-leaf pedestrian gate with a push pad exit and key entry. Securi-Mesh fencing features a tightly woven mesh pattern designed to deter climbing attempts, and its small apertures significantly improve resistance to cutting. Additionally, the mesh provides an ‘invisible screen’ effect that allows for effective surveillance without obstructing views, facilitating quick issue identification. Space efficiency and secure gating Unlike traditional swing gates, these gates slide parallel to the fence line, requiring minimal space The cantilever sliding gates installed are particularly well-suited for the restricted space in front of the facility. Unlike traditional swing gates, these gates slide parallel to the fence line, requiring minimal space both in front of and behind the fence. This design not only maximizes space efficiency but also enhances security with quick operational cycles, allowing for faster vehicle and goods transit, reducing the time the gates remain open, and minimizing security risks. 25-year guarantee with reduced maintenance Furthermore, the absence of ground tracks for the cantilever gates reduces maintenance needs by preventing issues related to debris or track damage, causing fewer repairs, and reduced downtime. In addition to these features, the fencing and gates are backed by a 25-year guarantee, ensuring long-term durability and minimal maintenance. Barbican® vertical bar fan panel The green polyester powder coating chosen for the fencing provides extra corrosion resistance The green polyester powder coating chosen for the fencing provides extra corrosion resistance and contributes to lower long-term costs for the hospital. Sections of the fencing, installed at varying heights, are further secured with a Barbican® vertical bar fan panel, which offers both a physical barrier to intrusion and a visual deterrent. Oxygen storage facility security Peter Jackson, Managing Director, of Jacksons Fencing comments on the success of the project, "Contributing to this vital project, enhancing the security of oxygen storage facilities at a UK hospital, is a significant achievement." "The pandemic highlighted the crucial role of oxygen, we must safeguard these resources effectively." Securi-Mesh® fencing and cantilever sliding gates "The integration of our Securi-Mesh® fencing and cantilever sliding gates reflects our commitment to providing both superior protection and operational efficiency." "By addressing the specific security needs of these vital resources, we help ensure that hospitals can focus on delivering high-quality patient care without disruption.”
Corsight AI's facial intelligence technology, in collaboration with Digital Barriers, has enabled Essex Police to recognize faces both in real-time and during retrospective investigations. Digital Barriers, known for its patented AI-based video codec and secure edge platform, specializes in delivering live cellular video solutions for a range of scenarios, including military operations in Afghanistan, securing royal and presidential events, and the Olympics. Facial intelligence technology To ensure privacy, images of people not on the watch list have been deleted almost now, with no data retention or storage The deployment of facial intelligence technology led Essex Police to make three arrests at the Clacton Airshow on August 22 and two additional arrests in Southend on August 25 and 26. These arrests were related to serious offenses, including sexual assault. The technology, provided by Corsight AI and Digital Barriers, not only identified individuals wanted for serious crimes but also enforced orders against those on a watch list and protected vulnerable individuals at risk of harm. To ensure privacy, images of individuals not on the watch list were deleted almost instantly, with no data retention or storage. Utilizing new technology Assistant Chief Constable Andy Pritchard stated, “We’re an innovative and forward-thinking force, utilizing new technology to keep people safe and deter crime. Our live facial recognition technology is used to locate people we want to speak to in connection with ongoing investigations and to manage people with court orders or conditions. Criminals cannot think they can walk around our communities without being caught.” Neil Hendry, Defense & Government Director at Digital Barriers, explained: “Real-time facial recognition from security cameras, vehicle-mounted cameras, and body cameras is a challenge that very few technologies can perform reliably. Digital Barriers provides a reliable video stream, and Corsight AI was chosen for its high reliability in challenging conditions such as poor video quality, limited camera angles, darkness, extreme weather, and disguises.” Safety and security Tony Porter, Corsight AI’s Chief Privacy Officer and former UK Surveillance Camera Commissioner, added: “Drawing on our vast experience with law enforcement agencies worldwide, Essex Police adhere to the highest standards of fair use and transparency.” Rob Watts, President of Corsight AI, said: “It is a privilege for Corsight AI to contribute to the safety and security of the law-abiding people of Essex.”
Sharry, a global workplace experience platform built around digital employee badges, has successfully delivered its enterprise solution to London’s new international hub opened by PATRIZIA, a global real estate investment manager. The state-of-the-art mobile access leverages Gallagher Mobile Connect credentials and, through full integration with the Gallagher Command Center access control system, enhances physical security and significantly improves the workplace experience. PATRIZIA’s international hub Located in London’s Endell Street, PATRIZIA’s new international hub was opened after an extensive brown-to-green refurbishment that delivers sustainable ‘office of the future’ combining smart building tech, wellness amenities, hospitality services, street art, and flexible workspaces. The five-floor hub brings together PATRIZIA’s 200 UK-based employees. Their access to the existing Victorian building is completely managed through the PATRIZIA App and web-based PortalWX developed by Sharry. The workplace experience platform is fully integrated into the Gallagher Command Center access control system allowing users to unlock their office doors simply and quickly by presenting their smartphones. Innovative approach If an employee arrives from another office, they can generate a mobile access badge in the app in seconds “PATRIZIA’s employees in London and those visiting from our other offices can enjoy seamless and touchless mobile access to our new international hub in London’s Covent Garden,” said Shreya Sheth, Associate Director, Building Technology & Sustainability at PATRIZIA. If an employee arrives from another office, they can generate a mobile access badge in the app in seconds. There is no need to send a new badge request, pick up the plastic card in person, or wait for it to be sent, and think about returning it when they leave. This innovative approach saves time while strengthening security policy. Next-generation security solution “We are very excited to be supporting PATRIZIA with their new innovative London office. Their commitment to creating a flagship workspace for the future of work is truly inspiring. It's been an incredible honor to be able to support them with a smart workplace app and integrated access control solution for the space,” said Ondřej Vodňanský, Head of Sales EMEA at Sharry. “We are thrilled to collaborate with Sharry and PATRIZIA to deliver a next-generation security solution at their new London hub. By integrating our Mobile Connect credentials with Sharry's workplace platform, we've created a seamless and secure access experience that not only enhances security but also aligns with the modern, flexible work environment that PATRIZIA envisions,” said Gordon Swallow, UK Sales Manager at Gallagher Security. Enhance experience and operations Beyond mobile access, the PATRIZIA App offers users a comprehensive set of features designed to enhance their workplace experience. To name a few: Reservations: Employees can easily reserve shared workstations or book access to the Health Club. Service Requests: With one tap, users can request any service or maintenance through the app. Guestpasses: The app also simplifies visitor management by allowing users to invite guests to the building and send them a guestpass with all the necessary information. Integrated access control solution Sharry provides an efficient platform for managing workplace access and offers powerful tools For facility and office managers, Sharry provides an efficient platform for managing workplace access and offers powerful tools for communication and engagement with all users, including the ability to send news updates, polls, and event invitations straight to the mobile app. Sharry and Gallagher's integrated access control solution significantly enhances physical security in many areas. For example, a manager can remotely revoke any mobile or plastic badge with just one click in the PortalWX. Even the end-user can immediately report their plastic card as lost in the PATRIZIA app and thus suspend it. The Building Operating System Finally, managers can access real-time data on workplace occupancy, enabling more informed decisions regarding space and amenities utilization thanks to a partnership with Trigrr. The building operating system Trigrr has been deployed in PATRIZIA HQ to simplify system integrations and provide a centralized tool that unifies data, automation, and controls across Sharry, HVAC, IoT, and lighting. Thanks to Trigrr BOS, occupants can remotely control office room temperature, adjust lighting, monitor CO2 levels, or launch smart scenarios directly in the Sharry workplace platform. "Partnering with Sharry on the new PATRIZIA international hub is a fantastic opportunity to generate more value by combining all applications and systems into a flexible tool that can adapt building behavior in real-time according to the needs of the occupants," said Jean-Michel Verhulst, CEO of Trigrr.
About 20 miles northeast of Battle Creek, Michigan, and 30 miles southwest of the state capital of Lansing lies the bucolic city of Olivet, population 1600. Olivet may be small as far as municipalities go, but it knows how to think big when it comes to protecting the safety of the 1250 students enrolled in its three Olivet Community Schools. Schools of Choice program That may sound like a large student body for a town its size until they realize that the district serves a geographic area of over 100 square miles and communities that rely on an economy based primarily on farming, light industry, and the area’s two largest employers – the University of Olivet and the schools themselves. As a participant in the state’s Schools of Choice program, the district can accept pupils from neighboring areas, which make up roughly 33% of the Olivet Community Schools population in addition to the city’s resident students. John Mertz Mertz's career has progressed from teaching to roles such as Director of Instructional Services Guiding school operations is Superintendent John Mertz. With 33 years of public education experience in Michigan, his career has progressed from teaching to roles such as Director of Instructional Services, Assistant Superintendent, and now Superintendent. This is his fifth year in Olivet. “The interesting thing about being a school superintendent is that there are several things I didn’t know were going to come with the job and never received training on,” says Mertz. “And one of the biggest ones is school safety and security.” Video monitors He recalls a Saturday night when he was doing some work in his office while his daughter was attending a school event that evening. When he happened to look up at the large video monitors behind him displaying the schools’ camera feeds, he was surprised to see a lot of people coming and going during that hour. “I thought, who are all these people? Where are they going?” Mertz says when he looked a bit closer, he saw there were kids with backpacks and baseball bats who were all heading to the middle school gym, where they held practice. “I didn’t have any idea how they got in,” he says. “It turns out the coaches had a key that they used to unlock doors whenever they needed to after regular hours.” Unfortunate events He adds that it’s an unfortunate but common fact that many school districts have far more keys in circulation than have been officially issued. “It can be difficult to figure out where the keys are coming from." "Are they being shared, or copied? For me, that was a huge aha moment. I found myself saying we’ve got to do something about this; we’ve got to make sure we’re controlling who is getting into our buildings, for what purpose, and when.” Communication and transparency Mertz and the district to push for major improvements in the school’s safety and security system That’s what compelled Mertz and the district to push for major improvements in the school’s safety and security system. But Mertz says that before the district could even consider who to work with and what to purchase and install, his team had to make its case to the schools’ stakeholders – the staff members, the board of education, and parents. “The community needed to understand the rationale that warranted the upgrades. It’s all about communication and transparency.” Updating the access control systems “The biggest changes we identified meant replacing our outdated and often grainy security cameras with sharper, more advanced units and stepping up the capacity and capabilities of our access control system so we could better schedule and manage access at perimeter doors and for activity spaces." "But what was especially crucial was adding digital access control to our classrooms, which was a priority for further enhancing student and teacher safety.” Fiber connections and wireless networks Mertz adds that before deploying advanced cameras and access control, upgrades to fiber connections and wireless networks also had to be made. “So, we started reaching out to security system integrators and experts in access control like ASSA ABLOY to start figuring out what technology was out there that would be the most advantageous for our district. It was quite a journey.” Relationship, reliability, and response time Ultimately, Mertz says the district issued an RFP. “Along with assessing what we needed and increasing our knowledge of the solutions available, we were also concerned about the kind of partnerships we were going to form with the companies that would be awarded the upgrade project." "We talked about the importance of the relationship, reliability, and response time. We wanted companies that could continue to provide support and be accountable if issues arose after the project was done.” Three key solutions Olivet Community Schools ended up choosing PDT of Byron Center, Michigan to be their systems integrator Upon completing their thorough vetting process, Olivet Community Schools ended up choosing People Driven Technology (PDT) of Byron Center, Michigan to be their systems integrator. PDT Account Executive Charlie Booth explains that gaining a full understanding of Olivet Community Schools’ requirements helped narrow the decision to three key solutions and organizations. Integrating cameras, access control, and analytics “We brought Genetec™ in and did a demo of their Unified Security Solutions platform that integrates cameras, access control, and analytics to make everything work seamlessly together,” says Booth. At the same time, he started talking with ASSA ABLOY Integrated Solutions Specialist David Hood who then facilitated a demo of the SARGENT IN100 Aperio® Wireless Lock. SARGENT IN100 Aperio® Wireless Lock “We chose the Aperio line because the Olivet classroom doors always needed to be online and communicating with Genetec in case global actions were needed to secure doors, like in a lockdown,” explains Booth. “Having IN100 electronic access control locks at each door means the facilities department now just issues keycards to staff instead of brass keys, making it much easier to manage credentials. For the video surveillance upgrade, we specified state-of-the-art i-PRO cameras.” 24/7 door monitoring Superintendent Mertz says, “The integration of the new cameras and access control solution with the Genetec platform and AI analytics allows us to monitor door activity 24/7." "It gives us a keen understanding of who is in the building and when.” He says that along with ensuring only those with card credentials have access, the system also alerts staff if a door has an issue such as a card reader/lock battery that needs replacing. ZeroEyes AI gun detection Mertz adds, “We also incorporated weapons detection software. We received a grant from the state for ZeroEyes AI Gun Detection." "And in a partnership with the City of Olivet, we obtained a grant for our first school resource officer. None of this would have been possible without upgrading our infrastructure, cameras, access control technology, and analytics nor without the support of our school and community stakeholders.” Complement security features Technology features i-PRO cameras district-wide, over a hundred SARGENT IN100 Aperio wireless access control locks Olivet Community Schools’ complement of security technology features i-PRO cameras district-wide, over a hundred SARGENT IN100 Aperio wireless access control locks for classrooms, and the Genetec Security Center unified platform. Christopher Dunn, Public Sector Account Executive for Genetec, further explains the value of his company’s solution, “One of the largest challenges Olivet faced was moving away from the fragmented system of the past where there was one platform for video and a separate one for the limited access control system they had." Human, vehicle, and threat detection "They needed to be able to harness the power of the technology at the edge that the new cameras offer and utilize it with applications that can detect things like the differences between human beings, vehicles, and potential threats.” He adds, “Because of how Genetec is structured and integrates so perfectly with other products, we’re able to bring everything into a ‘single pane of glass’, including analytics. That single pane of glass provides a dashboard that combines video and data feeds from multiple sources into a unified view.” Curb-to-core approach Dunn says that bringing everything together in one platform also eliminates the need for training on multiple systems, which was another highly important priority for Olivet Community Schools. According to David Hood, “ASSA ABLOY takes a curb-to-core approach when working with school districts, starting with the perimeter and then working inwards. Olivet Community Schools has followed that same approach. They have the perimeter protected with access control on every door along with video surveillance, and working inward to offices and classrooms, they now have integrated solutions throughout.” People Driven Technology Hood adds that collaborating with People Driven Technology and Genetec has been outstanding. “People Driven Technology understands our solutions and hardware, and they’re certified on our products." "That’s made installation and integration with i-PRO, Genetec, and analytics applications a seamless process for Olivet Community Schools.” An automatic classroom lockdown “It's all about student safety, staff safety, and community safety,” emphasizes Mertz. “When you have people in your facilities, putting in these extra measures buys extra time." "So, heaven forbid, if there ever is an incident, you're prepared for it, ready to react, ready to swing into action with the systems in place that are going to help you do that, including activating an automatic classroom lockdown if necessary. Safe and secure building “When you look at success, it all comes back to the district and the kids. Now I determine success on whether our kids are safe. Are they happy? Are they healthy? Are they in an environment where they feel comfortable? That's really what it's all about now, especially coming out of COVID." "You need to have kids feel like they're in a place where there are trustworthy adults around them, where the building is safe and secure, and where they feel comfortable to learn.”


Round table discussion
Direct costs such as purchase price and maintenance are important elements in the total cost of ownership (TCO). However, there are others. Elements such as opportunity costs of lost revenue or hidden costs of energy consumption and environmental consequences can also impact the measure of TCO. Costs of training, integration, support, and scalability can also be examined. Considering the security industry impact of TCO, we asked this week's Expert Panel Roundtable: How does/should total cost of ownership (TCO) impact the decision-making process when choosing technologies for security?
By linking human resource (HR) systems to physical security, access control systems can automatically update permissions based on employee changes, such as promotions, terminations, or department transfers. In fact, connecting HR and information technology (IT) systems to physical security can provide many significant benefits in terms of access control, incident response, compliance, cost savings, and employee experience. We asked this week’s Expert Panel Roundtable: How can organizations integrate physical security with other systems, such as IT and HR?
College campuses are meant to be places of learning, growth, and community. Fostering such an environment requires the deployment of policies and technologies that ensure safety and security. Considering the growing role of security technology in the higher education market, we asked this week’s Expert Panel Roundtable: What are the new applications for security technology in the college and university markets?
Products


White papers

The Security Challenges Of Data Centers
Download
Access Control System Planning Phase 2
Download
Access Control System Planning Phase 1
Download
The Truth Behind 9 Mobile Access Myths
Download
Multi-Residential Access Management And Security
Download
Guide For HAAS: New Choice Of SMB Security System
Download
2024 Trends In Video Surveillance
Download
Boost Efficiency And Streamline Security With Integrated Access Control
Download
AI In Security Solution
Download
Managing Security In The Age Of Boundaryless Working
Download
The Top 4 Reasons To Upgrade Physical Security With The Cloud
Download
Access Control: The Enterprise Buyer's Guide
Download
Effectively Branding A Multifamily Property
Download
Integrating Control Access And Security
Download
Identity And Access Management
Download

Videos
Security access systems: Manufacturers & Suppliers
- Vanderbilt Security access systems
- HID Security access systems
- ABLOY Security access systems
- CyberLock Security access systems
- Alpro Security access systems
- Bosch Security access systems
- Software House Security access systems
- CEM Security access systems
- AMAG Security access systems
- Parabit Security access systems
- Honeywell Security Security access systems
- Delta Scientific Security access systems
- Aritech Security access systems
- TESA Security access systems
- ASSA ABLOY - Aperio® Security access systems
- Hikvision Security access systems
- Nedap AEOS Security access systems
- TDSi Security access systems
- Paxton Access Security access systems
- Dahua Technology Security access systems