Retail security systems
RISCO, a globally recognized pioneer in cloud-based security solutions, announces the launch of its latest innovation, the LightSYS Air wireless solution. This state-of-the-art system represents a significant leap forward in wireless security technology for professionals within the industry. LightSYS Air Building upon the success of the widely-praised LightSYS+ hybrid solution, LightSYS Air heeds the call for an enhanced security installer experience akin to its predecessor. By address...
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the launch of Genetec Cloudlink™ 110, the latest addition to its line of cloud-managed security appliances. This compact device is specifically designed to simplify video management in low-density deployments, providing a versatile solution that enables customers to transition to cloud or hybrid environments at their own pace. Genetec Clo...
RecFaces, in collaboration with Startologic, successfully hosted its three-city ‘Project Day’ event, held in Delhi on September 12, Bengaluru on September 5, and Mumbai on August 29. The event provided an in-depth exploration of cutting-edge facial recognition technologies, highlighting how these solutions can revolutionize security systems across industries. Project Day events The Project Day events brought together system integrators, technology partners, and industry prof...
Artificial Intelligence Technology Solutions, Inc., is proud to announce the launch of RADCam™, a groundbreaking residential security product from its subsidiary Robotic Assistance Devices Residential, Inc. (RAD-R). RADCam revolutionizes the concept of residential security by introducing what the Company sees as the world’s first AI-powered, purpose-built ’Talking Security Camera’. Latest advancements in AI RADCam offers all the features of traditional residentia...
Hanwha Vision, the global vision solution provider, has released the XRN-426S-1T recorder - a compact NVR with a built-in 1TB solid-state drive (SSD). The 4-channel recorder supports AI search, when integrated with Hanwha Vision AI cameras, as well as resolutions of up to 4K. With a solid-state drive instead of a traditional hard drive, this recorder offers a silent and reliable solution. Highly compact and versatile The recorder’s compact size of just 20cm by 14cm mea...
Scandit, the pioneer in smart data capture, announces the asset acquisition of shelf audit automation technology from MarketLab, a Polish image recognition and AI software company specializing in the retail industry. As part of the transaction, MarketLab's expert team will join Scandit to build and expand the new offering. MarketLab's expertise in fixed camera solutions complements Scandit's existing ShelfView mobile capture approach to provide a hybrid data capture shelf intelligence solution...
News
Kingdom Security, a UK security firm has welcomed commitments in the King’s Speech to tackle the scourge of shoplifting in retail stores but warned shoppers they need to stay vigilant. Shoplifting law changes Kingdom Security, who provide integrated security solutions to retailers across the country, welcome the proposed changes in the law to shoplifting offenses, and assaults on shop-workers to become a specific offence. The changes come as England and Wales recorded over a jaw-dropping 430,000 offences in 2022/2023 according to the ONS. Mitigating threats with security solutions Shoppers should also be vigilant, and protect their purses, wallets, and phones from getting stolen A planned reversal in the previous government’s categorization of theft of goods worth less than £200 as a minor offense will hopefully help tackle the rising problem, but Kingdom Security warns that this should not make shoppers complacent. Kingdom Security advises retailers and supermarkets to ensure they have a security presence aiming to mitigate such threats. Solutions range from including physical retail specialist security personnel, checking bags before shoppers leave the store, and the tagging of high-value items. Shoppers should also be vigilant, and protect their purses, wallets, and phones from getting stolen while shopping in-store. Shoplifting Shoplifting has been increasing in recent years, and with that, a direct rise in the level of retail violence and abuse has followed, with the BRC’s crime survey from February revealing a 50% year-on-year increase of shoplifting, to almost 1,300 incidents a day in 2022/2023. The widespread reports of shoplifting across the nation within supermarkets in recent years have been largely believed to have been fueled by the cost-of-living crisis say consumer experts. Welcoming the new commitments Graham Allison, Chief Executive Officer at Kingdom Security, says, "We’ve seen these rises in reports of shoplifting at retailers across the country, and welcome commitments to tackle the problem in the King’s Speech." He adds, "Businesses, including supermarkets, help mitigate the issue by having security officers, scanning gates, and a bag-checking operation in place." Crime risk analysis tools Graham Allison continues, "With a security agency that offers crime risk analysis tools, these solutions can be increased and reviewed dependent on particular issues in certain localities, dependent on the time of the day or day of the week." He further said, "Maintaining essential security measures in place can act as a deterrent for shoplifters and heighten public awareness of the issue, the proposed changes in the law are welcome steps in tackling the issue."
Carlisle Support Services appoints public and private security expert, John Lambert as Managing Director of Security and Events in the North. With a background that stems across 15 years within the public and private sectors, John is well-placed to advise, facilitate, and manage this division for all Carlisle contracts. Responsible for the delivery of the Northern security and events division for the business, he will ensure that the division continues to deliver market-pioneering solutions to the existing contracts within multiple sectors including Healthcare, Manufacturing, Retail and Transport. Perception of the security industry John’s extensive background extends into several voluntary roles including Chair of the Liverpool City Security Council, Deputy Chair of the International Professional Security Association (IPSA), Director of the National Skills Academy for Security, member of the Security Skills Board, and Director of the National Association of Healthcare Security. John holds member status of the Security Institute and the Emergency Planning Society Alongside this, John holds member status of the Security Institute and the Emergency Planning Society. Within these voluntary roles, John campaigns for better working conditions for front-line team members and aims to improve public perception of the security industry. Contract retention and organic growth Chief Operating Officer at Carlisle Support Services, Adrian White said: “Our Northern Division is our largest revenue driver for security services and covers key strategic regions in Manchester, Liverpool, and Birmingham. The last twelve months have seen us implement a firm structure and develop clear operational regions for optimal cross-contract collaboration. We have seen good contract retention and organic growth. John's appointment will cement this position and provide us with a platform for growth. John understands this industry and has the mindset and attitude that we want to take Carlisle forward.” On his appointment, John added: “Since joining Carlisle Support Services in February this year, I have been incredibly impressed at the culture of the business, the professionalism and capability of my colleagues, as well as the strong and often long-term relationships we have built with our customers. To be appointed into the Managing Director role within a business of this quality is an incredibly proud moment for me, and I'm excited for the months and years ahead.”
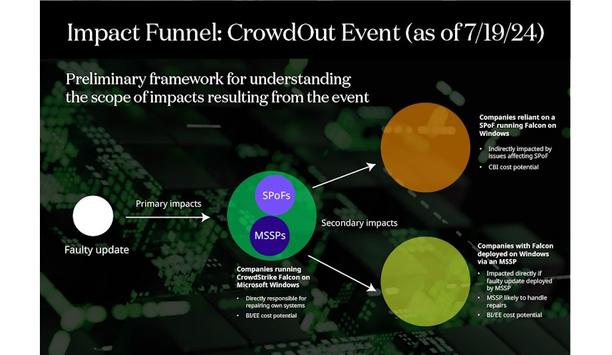
The faulty CrowdStrike Falcon Sensor update and subsequent outage – the CrowdOut Event – underscore the potential for Single Point of Failure (SPoF) technology outages to impact the global digital economy. CyberCube is advising clients on how to use SPoF Intelligence to identify exposed insureds and estimate the exposure footprint of the event. SPoF Intelligence is the definitive source for analyzing a portfolio's digital supply chain, integrated with the industry's pioneering cyber model. What happened? A global IT system outage was triggered by a faulty software update from CrowdStrike, causing widespread disruptions across various Windows operating system (OS) types. The issue originated from a defective kernel driver included in the update, which led to numerous systems crashing globally and displaying the “Blue Screen of Death” (BSoD). The BSoD is a protective measure to prevent further damage to the OS by stopping all operations The issue began with a CrowdStrike update that was intended to enhance security but inadvertently included a logic error in a configuration file. Invalid operations caused by the logic error led to the OS encountering conditions it cannot resolve. This resulted in system crashes, manifesting as the BSoD. The BSoD is a protective measure to prevent further damage to the OS by stopping all operations. Who is impacted? The faulty update affects companies using CrowdStrike’s Falcon software on machines running Windows OS, both desktop (including Windows 10 and 11) and Windows Server. These are the primary companies affected by the event. With its global position in cybersecurity, CrowdStrike’s own customer base includes many other organizations that CyberCube identifies as SPoFs. Companies relying on one of these SPoFs may be secondary victims of the event, even if they do not use CrowdStrike and Windows directly. Additionally, CrowdStrike Falcon is deployed by managed security service providers (MSSPs) on the networks of other – typically smaller – organizations they oversee. These organizations using such MSSPs are also secondary victims of the event. Notably, financial institutions, healthcare providers, and transportation networks have all experienced disruptions. CrowdStrike Falcon and Windows OS CrowdStrike Falcon is at risk of experiencing system crashes and operational disruptions Applying the SPoF Intelligence tool to search for insureds that are dependent on CrowdStrike Falcon, shows it is likely that all users of the core components of the CrowdStrike Falcon platform in conjunction with Windows OS are impacted. Analysis of the count of companies exposed across CyberCube’s US Industry Exposure Database (IED) identifies large companies in Manufacturing, IT, Healthcare, and Financials as the most likely to be exposed. Examination of exposed limits shows an outsize exposure in the Aviation, Banking, and Retail sectors. CyberCube has provided clients with a list of SPoFs that are dependent both on CrowdStrike Falcon and Windows OS. The outage affects various versions of Windows operating systems. This broad scope means that any organization or individual using these operating systems alongside CrowdStrike Falcon is at risk of experiencing system crashes and operational disruptions. Catastrophic loss modeling The primary impacts of the CrowdOut Event closely resemble two scenarios in CyberCube’s Portfolio Manager aggregation model. Modeling scenario classes 41 (operating system disruptions on endpoints) and 42 (operating system disruptions on servers) within CyberCube’s event catalog show the CrowdOut Event to be mainly a system failure or business interruption (BI) event. Customers may share secondary hits by way of extra SPoFs that fall within this prior footprint Customers may experience secondary impacts by way of additional SPoFs that fall within this primary footprint. SPoFs for scenario classes 4, 9, 10, 11, and 18 (mainly related to financial services and payment system technologies) have been observed as users of CrowdStrike and Windows operating systems, exposing companies that rely on these SPoFs to possible contingent business interruption (CBI) outages. What to expect? Affected organizations can expect a series of remediation and recovery efforts to take place immediately. Companies with the IT resources to handle large-scale incidents are expected to recover faster. There may be ongoing disruptions as companies implement patches and verify their systems' stability. Rolling back the update and applying patches requires specialized knowledge Rolling back the update and applying patches requires specialized knowledge. For small and medium-sized companies, a lack of access to IT staff could delay the remediation process. Companies lacking robust contingency or IT backup plans could also face additional disruptions. CyberCube support CyberCube's Cyber Aggregation Event Response Service (CAERS) has been activated as a result of the CrowdStrike event. CAERS provides up-to-date intelligence on major cyber catastrophes worldwide as they unfold to ensure CyberCube clients have the most relevant information. CyberCube will continue to monitor this developing event and provide support for customers in calculating the impact on their own cyber insurance portfolios.
Intellicene, the pioneer in intelligent security management platforms, announced the appointment of Greg Colaluca as General Manager. With more than 20 years of global leadership experience, Colaluca will guide the company into its next growth phase, emphasizing the delivery of intelligent security solutions for mission-critical environments. Colaluca brings a wealth of experience in customer success, growth, profitability, and operational excellence. He leverages vision, analytics, and continuous process improvement to develop successful business models and plans, and his technical background and business development skills ensure focused sales, product development, and service delivery. Delivering innovative technologies “Greg’s experience and proven track record in global leadership and customer-focused solutions will drive a continued focus on market leadership and innovation,” said Becky Stout, Volaris. “We are confident in his ability to lead the company with his extensive experience in delivering innovative technologies, his proven history of program development, and his unwavering commitment to the organization’s mission and values.” Prior roles of Colaluca Colaluca brings extensive experience to his new role as General Manager of Intellicene Colaluca brings extensive experience to his new role as General Manager of Intellicene. At Sensormatic, he led the Global Services team, providing solutions in design, RFID consulting, solutions design/architecture, implementation, and analytics. Before Sensormatic, he led Global Delivery at Astreya Partners, managing network engineering, network operations, and IoT services. At Hewlett Packard Enterprise, he served as Senior Director for the Consumer and Retail Industry, overseeing IT delivery across the Americas, EMEA, and APAC regions. Intelligence and stronger risk mitigation "Intellicene is well-positioned to deliver on its promise of helping organizations achieve greater intelligence and stronger risk mitigation in an evolving business environment,” Colaluca said. “Backed by a world-class team and a robust technology portfolio, I am excited to lead this organization into its next era and help customers around the globe achieve safer and stronger operations.”
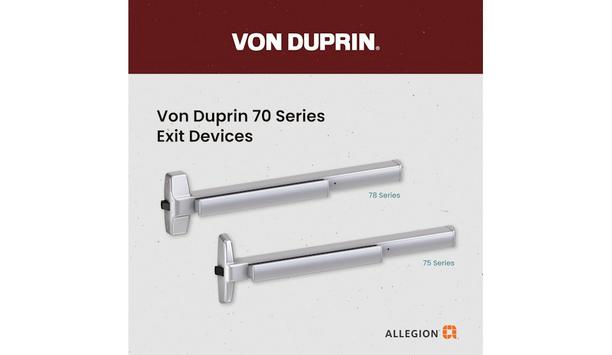
Allegion US, a pioneering provider of security solutions, technology, and services, is excited to announce the launch of the Von Duprin 70 Series Exit Devices. This new product line combines the quality and trust associated with Von Duprin with a medium price point, making it an ideal choice for a wide range of applications including warehouse, industrial, office, multifamily, retail, and hospitality spaces. The Von Duprin 70 Series Exit Devices are ANSI/BHMA Grade 1 certified, ensuring the highest standards of quality. The series offers both panic and fire-rated options that are available in both the 78 series wide stile and the 75 series narrow stile form factors. Rim, surface vertical rod and concealed vertical rod configurations are available for both the 78 and 75 series. Additionally, the 70 series offers a wide range of device lever designs and finishes that suite across the Von Duprin portfolio. Feature of the 70 Series Quick shipping is available for time-sensitive projects, allowing customers to meet their deadlines "The Von Duprin 70 Series Exit Devices serve as a testament to our commitment to delivering durable and high-performance solutions for a diverse range of applications," said Marli Williams, general manager of exits for Allegion US. "We are proud to offer customers the quality and trust they expect from Von Duprin at a medium price point." One standout feature of the 70 Series is the Quiet Electric Latch Retraction (QEL) option, which provides electronic control of an exit device with limited operational noise. This option is particularly beneficial in environments where noise reduction is desired. Furthermore, quick shipping is available for time-sensitive projects, allowing customers to meet their deadlines without compromising on quality. Von Duprin family of products In terms of esthetics, the 70 Series boasts a modern look with harder lines, perfectly complementing the existing Von Duprin family of products. This enables customers to seamlessly incorporate a blend of premium and mid-priced exit devices in their projects, creating a visually captivating and economically sensible space. Von Duprin's commitment to excellence extends beyond the product itself. Supported by a team of experts well-versed in door hardware applications and code compliance, Von Duprin provides unmatched customer support. From expert advice and architectural consulting to specification writing, code and compliance coordination, safety and security consulting, technical support, and training, Von Duprin ensures that customers have the resources they need every step of the way.
Delta Scientific's 50th Anniversary Showcase Event that took place on June 6th was a success, bringing together nearly 100 guests to celebrate this significant milestone. The event was an opportunity to highlight the company's rich history and ongoing innovation in the industry. Attendees were treated to the debut of several new products set to launch later this year, alongside demonstrations of Delta Scientific's extensive current product line. Technology of Delta barriers The event also featured shop tours, offering a behind-the-scenes look at the craftsmanship and the technology of Delta barriers. The anniversary celebration not only honored Delta Scientific's five decades of excellence but also reinforced its commitment to future advancements. Stay tuned for more information on new portable products along with a new high-security speed beam!


Expert commentary
Amidst the challenges of a prevailing economic downturn, the retail sector finds itself grappling with an unparalleled rise in incidents of shoplifting, theft, and burglaries. The disconcerting scenes witnessed on London’s Oxford Street in August 2023, where crowds gathered, looting as many stores as possible, sent shockwaves across the nation’s retailers. This alarming surge in retail crime has put retailers on high alert, as they contend with a rising tide of security concerns. Shoplifting concerns Recent data from the Union of Shop Distributive and Allied Workers (USDAW), has raised alarming concerns: shoplifting rates have surged by an unprecedented 24%. In the first half of 2023 alone, there were approximately 8 million reported shoplifting incidents. With the ongoing burden of the cost of living crisis and the approaching festive season, it is expected that these figures will keep surging. Implementing robust security measures Theft and prevention strategies cost retailers approximately £2 billion in 2021/2022 While more help from the Government to support retail workers and the businesses shoplifters target is certainly needed, the implementation of robust security measures will significantly contribute to deterring these crimes from occurring in the first place. British retailers spend millions on tools to deter and catch shoplifters inside stores, from CCTV and security guards to electronic tagging and alarms. The Grocer reported that theft and prevention strategies cost retailers approximately £2 billion in 2021/2022. Despite these initial costs, other threats are at play beyond the shop floor. Break-ins by criminal gangs For many large town center stores and supermarkets, and units in retail parks, the rear doors and delivery areas are commonly targeted by criminal gangs. It’s not uncommon for thefts to occur from pallets or cages that have been unloaded from lorries and sit waiting to be moved into the building. After-hours break-ins are a risk for all store owners too, particularly over the festive season when a lot of high-value stock has been delivered to shops and supermarkets. Addressing anti-social behaviour The additional fencing was deemed an essential measure to safeguard the community Anti-social behavior also poses a challenge for retailers. In 2022, an Aldi based in Derby invested in security fencing to protect staff and deter loitering groups. The additional fencing was deemed an essential measure to safeguard the community, as dangerous items were frequently found outside the store, including weapons and hypodermic needles. So how do physical security solutions such as fencing and gates help better protect retail establishments such as supermarkets and edge-of-town retail park shops? Fencing and gates: a critical component of retail security 1. Risk assessment and target hardening A thorough risk assessment will identify potential weak spots that require protection. ‘Target hardening’ involves implementing physical security measures that become more robust as they approach the target. This helps deter intruders while ensuring ease of access for customers and staff. 2. Effective perimeter security Opt for difficult-to-climb security fencing that provides a robust obstacle against thieves, vandals, and intruders Selecting fencing solutions according to the potential threats, site characteristics, and topography is crucial. It is important to specify fencing that strikes a balance and maintains a welcoming appearance while safeguarding external areas of the store or warehouse from potential harm and unauthorized access. Solid fencing which provides concealment can help to conceal expensive goods and remove them as a target for opportunistic theft. Opt for difficult-to-climb security fencing that provides a robust obstacle against thieves, vandals, and intruders. I recommend selecting a sufficiently tall and robust fence such as an acoustic barrier. Its noise-reducing properties are often beneficial for these types of sites too. 3. Controlling vehicular speeds and access To enhance security, consider controlling vehicular speeds and access. One effective approach is the installation of bollards at the ends of traditional high streets. This practice is already commonplace as a means of safeguarding against hostile vehicle attacks, but it can also play a pivotal role in preventing quick getaways of vehicles involved in potential heists. Additionally, employing road blockers and sliding gates at the rear entrances of delivery areas would serve to fortify security further. These measures can help in delaying vehicles, allowing for necessary checks to be conducted. 4. Balancing security with aesthetics The presence of high-security fencing can also make a site more of a target for vandals and burglars Another challenge is avoiding creating an imposing presence, especially important for areas situated near residential communities. The presence of high-security fencing can also make a site more of a target for vandals and burglars. To minimize this risk consider specifying timber fencing and traffic barriers to secure car parks, providing both security and a welcoming atmosphere for shoppers. Taking an integrated approach Combine secure perimeter fencing with effective lighting in places with shaded areas and at doors, gates, and shop windows, alongside Perimeter Intrusion Detection Systems (PIDS), and strategically placed CCTV. These measures will hinder unauthorized entry and escape, increasing the likelihood of detection and apprehension. Prioritising employee wellbeing Installing robust security fencing, complemented by CCTV, good lighting, and guarding, creates a safe environment Installing robust security fencing, complemented by CCTV, good lighting, and guarding, creates a safe environment for employees. This not only safeguards their well-being but also provides peace of mind that they are protected effectively in the case of a burglary or crime. When selecting security products for retail sites, it is advisable to opt for items that have undergone rigorous testing and carry relevant certifications for their security level. Each component should meet industry-specific standards for its intended purpose and originate from manufacturers accredited under ISO 9001:2015. This ensures a high standard of quality and reliability in safeguarding the premises. High-quality security fencing As the cost-of-living crisis continues, crime rates increase, and the festive season approaches, the time to act and implement on-site security is now. By investing in comprehensive security measures, retailers can protect their assets, employees, and customers, ensuring a safer and more secure shopping environment for all. High-quality security fencing is also a sound investment, that requires little or no maintenance once installed. The best fencing solutions are extremely weather-resistant, and won’t suffer from rust or corrosion. With all sectors preparing to ride the rapids of recession in the coming year, improving on-site security while selecting cost-effective measures, is one surefire way to protect your people, your property, and your profits from harm.
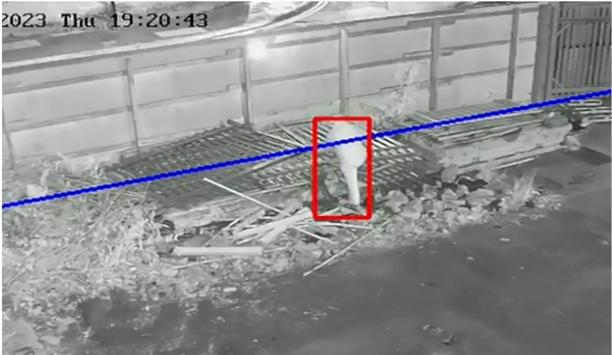
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realize, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionizing the overnight security business. Minimizing criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilizes a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimize the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is Remote Guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilize a combination of methods to effectively analyze potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyze the situation in real time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command center, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customized remote guarding When properly deployed, remote guarding systems are also customized to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional Security Shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A Bounty of Benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
It’s no secret that the data security sector is constantly changing. It has an annual CGR of about 12.3%. Future trends in data security Much of this has to do with the rise of cybercrime in recent years, with reports showing that cyberattacks happen as often as every 39 seconds. To combat the growing rate of cybercrime, data security has been on the rise. As we journey further into this era, it becomes evident that a spectrum of significant trends is molding the future of data security. This exploration delves into a selection of these trends, unraveling their importance and the potential implications they carry 1. AI security tools will increase Artificial Intelligence is also being used in the development of smart attacks and malware The introduction of Artificial Intelligence in the data security industry brought significant changes, especially in cybersecurity. AI has been the golden standard for face detection, natural language processing, automated threat detection, and automated security systems. Additionally, Artificial Intelligence is also being used in the development of smart attacks and malware, bypassing even the latest security protocols in data control. And as time progresses, AI security tools will flourish and dominate the scene. Let’s take a more in-depth look at three of the top AI security tools. Targeted attack analysis tool Manufacturers utilize targeted attack analysis tools to uncover targeted and stealthy attacks. Artificial Intelligence can be applied to the program’s capabilities, processes, and knowledge. For instance, Symantec launched this tool to combat the Dragon 2.0 attack in 2022. The phishing attack reprimanded multiple energy companies while trying to gain access to their operational networks. Targeted Attack Analysis Tools can analyze incidents and look for similarities from previous situations. They also help detect suspicious activities and collect all the necessary data to determine whether a specific action is malicious. Intercept X tool Results from the Intercept X Tool feature high accuracy and a low false positive rate Sophos, a British security hardware and software company, launched the Intercept X Tool. It engages a neural network that records and analyses data like a human brain. Sophos’ Intercept X Tool can extract features from a single file and perform a deep analysis. It detects malicious activities within 20 milliseconds. Plus, it’s also trained to work on bi-directional sharing and real-world feedback of threat intelligence. Results from the Intercept X Tool feature high accuracy and a low false positive rate. IBM Watson Technology IBM’s QRadar Advisor uses IBM Watson Technology, a unique AI tool for fighting cyber attacks. Artificial Intelligence can auto-investigate activities and indicators for potential exploitation or compromise. With cognitive reasoning, IBM Watson Technology can present critical insights to accelerate the response cycle. Security analysts can utilize this technology to search for threat incidents, reducing the risk of letting them fly under the radar. 2. Blockchain as a security solution It guarantees no points of failure or hackable entrances that can expose datasets inside the system Blockchain is a type of distributed ledger technology (DLT) that aims to establish trust within an untrusting ecosystem. Today it’s one of the most robust cybersecurity technologies in the industry. Blockchain utilizes a decentralized ledger system, but your team members can still gain access to transparent information in the cloud. Members can also record, pass along, and view necessary transactional data in the blockchain. The entire blockchain process maintains data integrity within the system while establishing trust among team members. It guarantees no points of failure or hackable entrances that can expose datasets inside the system. Cybersecurity, biometrics Cybersecurity primarily benefits from these features because blockchain can create a secure and robust wall between data and hackers. On top of that, blockchain ledgers can include biometrics like fingerprints and retina scans. These prevent hackers from accessing any private data. Because blockchain is decentralized, it also limits hackable data. Together with the technology’s record-keeping system, each node is provided insight into data manipulation exposing real-time cybercrime attempts. 3. Increased and widened access control Without access control, expect your company to be open to security issues, including theft, data loss, and breach of data Access control is critical in data security. More than a valuable security tool, business leaders can use access control to regulate people accessing any given resource. A company with an IT security setting can control who has the liberty to edit certain files. One of the primary goals of access control is to minimize threats or attacks to organizations and businesses to keep people and data secure. Without access control, expect your company to be open to security issues, including theft, data loss, and breach of data protection laws. Benefits The benefits of increased and widened access control include: Identifying who can access and control your data at specific time intervals. Protecting data from overwriting, accidental deletion, and malicious intent. User permissions that can be readily changed. Compliance and regulation with data privacy laws. Central management of access to data through a reporting portal or a dashboard. Multi-factor authentication Access control comes in various types and systems, so it’s critical to know the features of what you’re looking for. The most common type is multi-factor authentication or MFA. It involves multiple steps before logging in, requiring the user to enter other relevant information besides the password. Some other examples of information include biometrics, answering a security question, or entering a code sent to the user’s email address. Two-factor authentication, role-based access control Two-factor authentication further prevents unauthorized entries that can result in unnecessary data possession Two-factor authentication further prevents unauthorized entries that can result in unnecessary data possession. Another type of access control is role-based access control. In this setup, only one individual can set up access guidelines and grant permissions to specific team members within an organization. 4. Greater use of the zero-trust security model The zero-trust security model is a framework that requires every user within and outside the organization to undergo authentication, authorization, and validation. These are all essential to ensure proper security configuration before access is granted to the company’s applications and data. A zero-trust model assumes that anyone can cause data breaches and that a traditional network edge is not taken into effect. Moreover, it addresses the following modern-day challenges: Hybrid cloud environments. Security of remote workers. Ransomware threats. This framework utilizes the combination of multiple advanced technologies, including: A risk-based multi-factor authentication. Endpoint security. Identity protection. Cloud workload technology. The zero-trust model uses all these innovative tools for system identification, user verification, access consideration, and system security maintenance. Constant validation and monitoring Enforcing strict policies and compliance with data privacy laws are also essential Additionally, it also considers data encryption, email security, and asset verification before establishing connections with applications. The architecture of a zero-trust framework requires constant validation and monitoring of the users and the devices they are using. Enforcing strict policies and compliance with data privacy laws are also essential. More importantly, the zero trust architecture requires all organizations to be aware of all their available services and accounts to gain complete control of data handling and manipulation. 5. Increased privacy regulations Privacy regulations and policies guide organizations in proper data control, handling, and security. These policies guide organizations in proper data control, handling, and security. As a responsible business owner, you must comply with these regulations to avoid legal issues. With cybersecurity attacks becoming common, expect increased and stricter privacy regulations to be released in the next few years. While current policies are still taken into effect, various modifications and adjustments will occur to compete with the rising numbers of data breaches, thefts, data loss, and more. California Privacy Rights Act (CPRA) Currently, the California Privacy Rights Act (CPRA) is the most comprehensive legislation on state data privacy. It only started to take effect on January 1, 2023. The CPRA introduces the following principles: Broad individual consumer rights. Significant duties of people who need to collect sensitive and personal information. Additional definitions of data privacy and security. An individual’s duties include releasing information about data collection to concerned data subjects and proper access, correction, and deletion of information. Final thoughts 2023 is a big year for data security. Trends such as increased adoption of zero-trust policies, a greater reliance on AI security tools, and the implementation of blockchain as a security solution are all things we expect to see shortly. Staying up-to-date with these trends is important for keeping your business current and ensuring that you’re adhering to new and changing regulations. Doing so can give you an edge over the competition and keep you out of legal hot water.
Security beat
Companies at GSX 2023 emphasized new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasizes ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the Mid-Market to the Cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for pure cloud, but there are benefits to be realized from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realize the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘Soft’ Features for Integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organization more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organization more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centers around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasizing performance, protection (cybersecurity), and price, their data centers are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring center where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
When it comes to security cameras, the end user always wants more—more resolution, more artificial intelligence (AI), and more sensors. However, the cameras themselves do not change much from generation to generation; that is, they have the same power budgets, form factors and price. To achieve “more,” the systems-on-chips (SoCs) inside the video cameras must pack more features and integrate systems that would have been separate components in the past. For an update on the latest capabilities of SoCs inside video cameras, we turned to Jérôme Gigot, Senior Director of Marketing for AIoT at Ambarella, a manufacturer of SOCs. AIoT refers to the artificial intelligence of things, the combination of AI and IoT. Author's quote “The AI performance on today’s cameras matches what was typically done on a server just a generation ago,” says Gigot. “And, doing AI on-camera provides the threefold benefits of being able to run algorithms on a higher-resolution input before the video is encoded and transferred to a server, with a faster response time, and with complete privacy.” Added features of the new SOC Ambarella expects the first cameras with the SoC to emerge on the market during early part of 2024 Ambarella’s latest System on Chip (SOC) is the CV72S, which provides 6× the AI performance of the previous generation and supports the newer transformer neural networks. Even with its extra features, the CV72S maintains the same power envelope as the previous-generation SoCs. The CV72S is now available, sampling is underway by camera manufacturers, and Ambarella expects the first cameras with the SoC to emerge on the market during the early part of 2024. Examples of the added features of the new SOC include image processing, video encoders, AI engines, de-warpers for fisheye lenses, general compute cores, along with functions such as processing multiple imagers on a single SoC, fusion among different types of sensors, and the list goes on. This article will summarize new AI capabilities based on information provided by Ambarella. AI inside the cameras Gigot says AI is by far the most in-demand feature of new security camera SoCs. Customers want to run the latest neural network architectures; run more of them in parallel to achieve more functions (e.g., identifying pedestrians while simultaneously flagging suspicious behavior); run them at higher resolutions in order to pick out objects that are farther away from the camera. And they want to do it all faster. Most AI tasks can be split between object detection, object recognition, segmentation and higher-level “scene understanding” types of functions, he says. The latest AI engines support transformer network architectures (versus currently used convolutional neural networks). With enough AI horsepower, all objects in a scene can be uniquely identified and classified with a set of attributes, tracked across time and space, and fed into higher-level AI algorithms that can detect and flag anomalies. However, everything depends on which scene is within the camera’s field of view. “It might be an easy task for a camera in an office corridor to track a person passing by every couple of minutes; while a ceiling camera in an airport might be looking at thousands of people, all constantly moving in different directions and carrying a wide variety of bags,” Gigot says. Changing the configuration of video systems Low-level AI number crunching would typically be done on camera (at the source of the data) Even with more computing capability inside the camera, central video servers still have their place in the overall AI deployment, as they can more easily aggregate and understand information across multiple cameras. Additionally, low-level AI number crunching would typically be done on camera (at the source of the data). However, the increasing performance capabilities of transformer neural network AI inside the camera will reduce the need for a central video server over time. Even so, a server could still be used for higher-level decisions and to provide a representation of the world; along with a user interface for the user to make sense of all the data. Overall, AI-enabled security cameras with transformer network-based functionality will greatly reduce the use of central servers in security systems. This trend will contribute to a reduction in the greenhouse gases produced by data centers. These server farms consume a lot of energy, due to their power-hungry GPU and CPU chips, and those server processors also need to be cooled using air conditioning that emits additional greenhouse gases. New capabilities of transformer neural networks New kinds of AI architectures are being deployed inside cameras. Newer SoCs can accommodate the latest transformer neural networks (NNs), which now outperform currently used convolutional NNs for many vision tasks. Transformer neural networks require more AI processing power to run, compared to most convolutional NNs. Transformers are great for natural language processing (NLP) as they have mechanisms to “make sense” of a seemingly random arrangement of words. Those same properties, when applied to video, make transformers very efficient at understanding the world in 3D. Transformer NNs require more AI processing power to run, compared to most convolutional NNs For example, imagine a multi-imager camera where an object needs to be tracked from one camera to the next. Transformer networks are also great at focusing their attention on specific parts of the scene—just as some words are more important than others in a sentence, some parts of a scene might be more significant from a security perspective. “I believe that we are currently just scratching the surface of what can be done with transformer networks in video security applications,” says Gigot. The first use cases are mainly for object detection and recognition. However, research in neural networks is focusing on these new transformer architectures and their applications. Expanded use cases for multi-image and fisheye cameras For multi-image cameras, again, the strategy is “less is more.” For example, if you need to build a multi-imager with four 4K sensors, then, in essence, you need to have four cameras in one. That means you need four imaging pipelines, four encoders, four AI engines, and four sets of CPUs to run the higher-level software and streaming. Of course, for cost, size, and power reasons, it would be extremely inefficient to have four SoCs to do all this processing. Therefore, the latest SoCs for security need to integrate four times the performance of the last generation’s single-imager 4K cameras, in order to process four sensors on a single SoC with all the associated AI algorithms. And they need to do this within a reasonable size and power budget. The challenge is very similar for fisheye cameras, where the SoC needs to be able to accept very high-resolution sensors (i.e., 12MP, 16MP, and higher), in order to be able to maintain high resolution after de-warping. Additionally, that same SoC must create all the virtual views needed to make one fisheye camera look like multiple physical cameras, and it has to do all of this while running the AI algorithms on every one of those virtual streams at high resolution. The power of ‘sensor fusion’ Sensor fusion is the ability to process multiple sensor types at the same time and correlate all that information Sensor fusion is the ability to process multiple sensor types at the same time (e.g., visual, radar, thermal, and time of flight) and correlate all that information. Performing sensor fusion provides an understanding of the world that is greater than the information that could be obtained from any one sensor type in isolation. In terms of chip design, this means that SoCs must be able to interface with, and natively process, inputs from multiple sensor types. Additionally, they must have the AI and CPU performance required to do either object-level fusion (i.e., matching the different objects identified through the different sensors), or even deep-level fusion. This deep fusion takes the raw data from each sensor and runs AI on that unprocessed data. The result is machine-level insights that are richer than those provided by systems that must first go through an intermediate object representation. In other words, deep fusion eliminates the information loss that comes from preprocessing each individual sensor’s data before fusing it with the data from other sensors, which is what happens in object-level fusion. Better image quality AI can be trained to dramatically improve the quality of images captured by camera sensors in low-light conditions, as well as high dynamic range (HDR) scenes with widely contrasting dark and light areas. Typical image sensors are very noisy at night, and AI algorithms can be trained to perform excellently at removing this noise to provide a clear color picture—even down to 0.1 lux or below. This is called neural network-based image signal processing, or AISP for short. AI can be trained to perform all these functions with much better results than traditional video methods Achieving high image quality under difficult lighting conditions is always a balance among removing noise, not introducing excessive motion blur, and recovering colors. AI can be trained to perform all these functions with much better results than traditional video processing methods can achieve. A key point for video security is that these types of AI algorithms do not “create” data, they just remove noise and clean up the signal. This process allows AI to provide clearer video, even in challenging lighting conditions. The results are better footage for the humans monitoring video security systems, as well as better input for the AI algorithms analyzing those systems, particularly at night and under high dynamic range conditions. A typical example would be a camera that needs to switch to night mode (black and white) when the environmental light falls below a certain lux level. By applying these specially trained AI algorithms, that same camera would be able to stay in color mode and at full frame rate--even at night. This has many advantages, including the ability to see much farther than a typical external illuminator would normally allow, and reduced power consumption. ‘Straight to cloud’ architecture For the cameras themselves, going to the cloud or to a video management system (VMS) might seem like it doesn’t matter, as this is all just streaming video. However, the reality is more complex; especially for cameras going directly to the cloud. When cameras stream to the cloud, there is usually a mix of local, on-camera storage and streaming, in order to save on bandwidth and cloud storage costs. To accomplish this hybrid approach, multiple video-encoding qualities/resolutions are being produced and sent to different places at the same time; and the camera’s AI algorithms are constantly running to optimize bitrates and orchestrate those different video streams. The ability to support all these different streams, in parallel, and to encode them at the lowest bitrate possible, is usually guided by AI algorithms that are constantly analyzing the video feeds. These are just some of the key components needed to accommodate this “straight to cloud” architecture. Keeping cybersecurity top-of-mind Ambarella’s SoCs always implement the latest security mechanisms, both hardware and software Ambarella’s SoCs always implement the latest security mechanisms, both in hardware and software. They accomplish this through a mix of well-known security features, such as ARM trust zones and encryption algorithms, and also by adding another layer of proprietary mechanisms with things like dynamic random access memory (DRAM) scrambling and key management policies. “We take these measures because cybersecurity is of utmost importance when you design an SoC targeted to go into millions of security cameras across the globe,” says Gigot. ‘Eyes of the world’ – and more brains Cameras are “the eyes of the world,” and visual sensors provide the largest portion of that information, by far, compared to other types of sensors. With AI, most security cameras now have a brain behind those eyes. As such, security cameras have the ability to morph from just a reactive and security-focused apparatus to a global sensing infrastructure that can do everything from regulating the AC in offices based on occupancy, to detecting forest fires before anyone sees them, to following weather and world events. AI is the essential ingredient for the innovation that is bringing all those new applications to life, and hopefully leading to a safer and better world.
New buzzwords were abundant in the articles that generated the most clicks on our website in 2022. From the metaverse to the Internet of Things, from frictionless access control to artificial intelligence (AI), the topics most popular among our site’s visitors were at the cutting edge of change and innovation in the physical security marketplace. Here is a review of the Top 10 Articles of 2022, based on reader clicks, including links to the original content: Metaverse will promote collaboration and enable more efficiencies for security Metaverse is a familiar buzzword currently, but few people grasp what it means. In the simplest terms, the metaverse is an online “place” where physical, virtual, and augmented realities are shared. The term, Metaverse, suggests a more immersive online environment that combines elements of augmented reality (AR) and virtual reality (VR). For the physical security industry, the looming creation of a complex online environment offers possibilities and challenges. Establishing identity will be a central principle of the metaverse, and various biometrics are at the core of ensuring the identity of someone interacting in the virtual world. Cybersecurity elements are also key. On the benefits side, the security market is already taking advantage of technologies related to the eventual evolution of the metaverse. For example, the industry has deployed AR to provide information about a door lock’s status on a screen, headset, or smart glasses as a patrolling guard walks by. What are the security challenges of the transportation industry? Because transit agencies rely on several IoT devices, they get exposed to higher cybersecurity risks Rapid technological advancement, increasing urbanization, and the growing expectations of commuters and governments are pressuring transit industry players to modernize. Commuters, urban planners, first responders, and other stakeholders want to use transit data to support their decision-making. Transit agencies’ security and operations teams need closer collaboration to stay ahead. However, for many years, most transit agencies have relied on siloed, proprietary systems. Because transit agencies rely on an ever-growing number of Internet of Things (IoT) devices, they also get exposed to higher cybersecurity risks as there are more network access points to manage. The future is here: ADT’s innovation lab evaluating robots and indoor drones New robots and indoor drones for security applications are on the horizon, based on the work of ADT Commercials’ Innovation Lab, which is evaluating the latest technologies’ value to customers and some typical use cases. The ideal use of humanoid robots is to perform jobs that are considered repetitive, dirty, dangerous, and/or mundane. In security, that describes most security guard positions. As the name implies, autonomous indoor drones are focused on flying indoors versus the outdoor environment, which is heavily regulated by the U.S. Federal Aviation Administration (FAA). Flying autonomously indoors not only eliminates FAA oversight but also will enable ADT Commercial to offer another choice to customers to further reduce their dependencies on and costs of human guards. Innovative security: the key to business efficiency, cost savings, and more Organizations have shifted business focus countless times since the onset of the pandemic. While many leaders have been primarily concerned with the immediate health and safety of their customers and employees, 2022 has given rise to a new trend. More than ever, business leaders are seeking security solutions that increase operational efficiency and cost savings as well as improve logistics and business insight. As working environments become more complex, organizations looking to drive higher productivity and profitability margins should consider security upgrades that prioritize integrated analytics and automation. Shoplifting today is more sophisticated, and so are the tools to fight it One tool to fight shoplifting is analytics, which can be used to determine where shrink is occurring Shoplifting is often viewed as petty theft by individuals, but that is not always the case. Overall, shoplifting is becoming more sophisticated and coordinated. Traditional “shoplifting” has two major differences when compared to organized retail crime (ORC). The differences are numbers and motivation. ORC consists of groups working together to monetize theft, very different than an individual taking an item they need. One tool to fight to shoplift is analytics, which can be used to determine where shrink is occurring. Understanding where crimes take place helps retailers make strategic decisions about where to place their loss prevention efforts. Oosto offers 10 reasons to switch to frictionless access control in commercial buildings Access control for buildings is nothing new. It’s only in recent years that the urgency to implement smarter, more efficient, and more convenient forms of access control has increased, in the context of public and private sector digital transformation. Upheavals from the COVID-19 pandemic have forced organizations to re-think, pivot, and invest in new technology solutions that will incorporate Artificial Intelligence (AI) and Machine Learning, to gain speed in their operations, glean actionable insights from their video analytics, and enhance productivity with their teams. Which security trend is here to stay? Technologies and trends in the security marketplace come and go with some regularity. But how can you tell which trends are gaining traction and which amount to “the flavor of the month.” For example, while many physical security departments were hesitant to consider cloud-connected solutions in the past, they now better understand the benefits these solutions bring and how they can help them utilize their resources to achieve business goals while minimizing overall operational complexity. Other technologies mentioned in the article include mobile credentials, AI-based analytics, video management systems, cybersecurity, and a new emphasis on data. What do these technology trends have in common? They are opening new possibilities for greater system efficiency and functionality. In short, they are playing a role in transforming our industry. GSX 2022 reflects changing technologies and evolving role of security The role of the security director increasingly will encompass facets of cybersecurity and physical security GSX 2022 in Atlanta highlighted the changing role of security in the enterprise. The role of the security director increasingly will encompass facets of cybersecurity as well as physical security. Transitioning to an operation that incorporates both disciplines requires a workforce that embraces education and building new skills. Education and the opportunity to build new skills are evident everywhere at GSX, including in the hundreds of education sessions and also in the knowledge shared on the show floor in the exhibit hall. Consolidation changing the face of the security market Consolidation is a dominant trend in the security marketplace. Large companies typically swallow up smaller companies as a means of expanding both their technology portfolios and their geographic reach. Sometimes a big fish is swallowed up by an even bigger fish. Despite the pandemic and resulting economic challenges, the security market has continued to be a desirable environment for both big players and startups, which then provide abundant acquisition targets for larger companies. This article highlighted recent mergers and acquisition news. Six trends at the intersection of video and AI Video has evolved beyond the capabilities of advanced imaging and performance to include another level: Artificial Intelligence. Video imaging technology combines with AI, delivers a wealth of new data, not just for traditional physical security applications, but for a much deeper analysis of past, present, and even future events across the enterprise. This is more than a big development for the physical security industry; it is a monumental paradigm shift that is changing how security system models are envisioned, designed, and deployed. Much of the heightened demand for advanced video analytics is being driven by six prevalent industry trends.
Case studies
Geekplus, the global pioneer in mobile robot and smart logistics solutions, has deployed the first Shelf-to-Person PopPick project in the Nordics for one of the biggest online pharmacy wholesalers in the region, Med24.dk. System Teknik partnered on the Denmark project, which includes three PopPick stations and 30 Shelf-to-Person robots, bringing a flexible solution to a region where fixed automation still dominates. "With the rise of e-commerce, Med24.dk had been struggling with huge sales growth coupled with fast delivery demands from customers in Denmark, Norway, Sweden searching for pharmacy, health and beauty products. Peak season events had also caused considerable strain to their operations," said Blond Shkodrani, channel partner manager for the Nordics at Geekplus. "Due to their overwhelming success, Med24.dk needed a modular, automated order fulfillment solution for fast, efficient order fulfillment." Order fulfillment challenges Shelf-to-Person takes goods of all sizes while removing the need for infrastructure investment The Geekplus modular Shelf-to-Person solution optimizes warehouse operations using mobile robots to transport shelves. In a region where fixed and cubic solutions have been the trend during recent years, Shelf-to-Person handles goods of all sizes while removing the need for infrastructure investment, making it the most flexible response to order fulfillment challenges. PopPick workstations use two retrieval arms and four presentation locations to present pickers with multiple, moveable 78-tote racks at one time, resulting in an industry-pioneering throughput of 450 totes per hour. PopPick can store goods of all types and sizes; the solution is not limited to small pieces and improves ergonomics for workers while picking. It also takes up less space than traditional systems, so customers can use more stations without adding facility space. Mobile order fulfillment solutions "We are very pleased to invest in flooring robots from Geekplus," said Med24.dk CEO Nils Træholt. "We believe that this new and innovative technology can help us realize our growth ambitions, while maintaining good delivery times for the benefit of our customers." Morten Kirch, System Teknik's CSO, added: "Due to Med24.dk's growth, we are thrilled to be able to deliver a tailor-made, automated solution that matches their needs." Geekplus offers a suite of Goods-to-Person mobile order fulfillment solutions-the only comprehensive robotic offering controlled by a single software platform. "Through trusted partners like System Teknik, we're showing customers all over Europe that Geekplus truly is a one-stop shop for modular warehouse automation," Shkodrani said.
A damning new report shows theft from construction sites is surging nationwide, detrimentally affecting projects, firms and employees. Key findings Spike in cases: Two-thirds of respondents say the rate of theft increased in 2023, as the resale value of goods reached record levels. Criminals are getting smarter: one in three believe crime, including theft, physical violence, harassment and vandalism, is becoming more sophisticated. It comes as reports of criminals using drones to target sites become more frequent. A hidden productivity drain: A third of projects have been delayed due to crime, with copper and cable topping the tables as the most frequently targeted goods–delaying the development of critical infrastructure, such as railways. Workers bear the brunt of poor security: one in four workers have been left out of pocket, after having to replace stolen tools, and say being robbed is their “biggest fear.” However, security is seen as a “low priority” on sites they work on (30%). Underestimation of the risks BauWatch, examines the senses of building workers, to understand their incidents of theft at work The “Unseen Threats: 2024 Construction Crime Index,” from pioneering site-security provider, BauWatch, examines insights from construction workers, to understand their experience of theft at work. It suggests a “perfect storm” of factors, including goods inflation, increasingly sophisticated criminal tactics, and a general underestimation of the risks, are making sites vulnerable to crime, in turn causing major delays to projects, as well as denting staff morale. It also identifies the types of perpetrators that might pose a threat, including opportunists, professional gangs, and “insiders” (criminals posing as legitimate personnel), and outlines a list of best practice measures that can be immediately employed to minimize the risk of a robbery. BauWatch’s crime index We’ve observed that, since the Government removed the construction industry’s access to red diesel Rico Wojtulewicz, Head of Policy and Market Insight at the National Federation of Builders said: “We’ve observed that, since the Government removed the construction industry’s access to red diesel, fuel theft has risen, as indicated by responses in BauWatch’s crime index. CCTV has therefore become an even more important tool to help tackle site crime, not only because it acts as a deterrent and helps collect video evidence but as it also offers an insight into how and where a site might be better protected.” With criminals seemingly becoming more brazen, BauWatch, which supplies CCTV security to over 5000 active Construction sites across the UK and Europe, and the National Federation of Builders, are calling for firms to take extra preventative action against thieves, rather than taking a “wait and see” approach. Author's quote “Construction sites have always attracted thieves, but with the resale value of goods going through the roof, they’re now prime targets. So, it’s worrying to see that some workers don’t feel confident about on-site security,” said Alexis Potter, BauWatch’s Managing Director. Potter added: “Repeated incidents, even small ones, have huge repercussions if left unchecked as we can see in this report. The best way to minimize the impact of theft is to deter criminals from entering at all, so we are advocating for the adoption of preventative security measures to protect staff, safeguard investments and maintain project schedules.”
The Body Shop has installed bespoke Traka RFID locker solutions at its main distribution center to ensure intelligent management and accountability of assets, enhance security, and streamline operations. As a global pioneer in ethical and sustainable beauty products, The Body Shop recognizes the importance of responsible resource management, business practices, and asset security. Traka intelligent locker systems At its main distribution center in Littlehampton, three large-scale Traka intelligent locker systems have been installed to manage different devices. The first uses Traka’s multi-bay cradle locker solution to manage 30 VoCollect voice-picking devices and Bluetooth headsets, all charged and ready to operate. Three large-scale Traka intelligent locker systems have been installed to manage different devices The second houses 40 Falcon handheld scanners, managed by Traka’s specialist Asset Master Locker range with charging and battery points located. The final system presents secure storage for a kit of equipment, specifically designed for the forklift truck drivers, with each locker compartment containing a Falcon scanner, Radio and Printer. Each intelligent locker solution is offered with RFID asset detection and specialist TrakaWEB software, to provide managers with instant audit control capability to establish exact times when physical devices are removed and returned to lockers. New standards in design Says The Shift Manager, responsible for the project: “To keep up with high demands, our distribution center operates 24/7. It is constantly evolving, driving new standards in design and use of technology to ensure our products reach our stores to meet our loyal customer demands." “To operate at maximum capacity, we need to make it as simple and as quick as possible for authorized colleagues to not only gain access to the devices they need but also ensure they are operational and in good working order. With the introduction of Traka, we have eliminated manual control, plus we have a complete audit on all devices that we can access from anywhere. We have already noted increased accountability, traceability and fault logging, all coming together to reduce lost time and enhance operational efficiency.” Net 2 access control cards Access to other assets and tools can only be granted to authorized personnel for their job specification The three locker solutions have been installed in two separate locations around the distribution center, to ensure staff can easily access equipment in their work area. Eliminating the need to travel to a central location and queue to access or organize equipment has led to improved productivity at the start and end of shift periods. Traka has also ensured all systems operate using existing Paxton Net 2 access control cards to minimize facility disruption during or after installation. Access to different assets and equipment can only be granted to authorized personnel for their identified job specification, with staff only able to take one device or kit at a time. Author's quote Lee Payne, Traka Business Development Manager added: “The introduction of Traka systems to a global distribution center such as The Body Shop demonstrates how simple process enhancements can make a significant difference. From the initial brief through to implementation, we worked closely with the team to identify the exact requirements for each site and the accessibility needs for staff." “We understood the need for curfew notifications, fault logging and careful authorized access control. We planned with the team to separate out the systems into specific work areas and use the Traka orange to help the locker systems stand out, all to ensure vital time could be saved for staff and management. The result is a smoother, more efficient operation throughout the supply chain, helping The Body Shop continue its mission of delivering its best-loved ethical beauty products."
Genetec Inc., a technology provider of unified security, public safety, operations, and business intelligence solutions, announced that the Yorkdale Shopping Center in Toronto, Canada, has unified its security operations based on Genetec™ Security Center, Sipelia™, AutoVu™, and Mission Control™. With the Genetec platform, the security team at Yorkdale has been able to enhance operational efficiency, better collaborate with local police, and take a more proactive security stance. Yorkdale Shopping Center With over two million square feet of retail space and 270 stores, Yorkdale Shopping Center offers the country’s largest collection of designer labels and luxury brands. Managed by Oxford Properties Group, it goes beyond shopping, offering visitors valet services, a museum-quality art collection, and 24/7 on-site security. Breaking out of proprietary system limitations Additionally, having a closed security solution held them back from exploring new technologies With their proprietary video system and standalone access control solution, searching for information required the security operations team to navigate between the two systems, which slowed investigations and incident response. Additionally, having a closed security solution held them back from exploring new technologies such as cutting-edge cameras or system integrations. Genetec™ Security Center and Omnicast™ The search for a new video management system (VMS) led them to Genetec™ Security Center and Omnicast™, which not only provided state-of-the-art video management, but unified video, access control, and data from other sensors into one system. The Genetec solutions enhanced the team's ability to manage security policies, monitor events, and run investigations. Since it is an open platform, Yorkdale can expand the system with new technology as it emerges. A comprehensive view of mall security With Security Center, we’re shaving valuable time from investigations and response" Since implementing the Security Center, the Yorkdale team has been able to significantly enhance operational efficiencies. If an incident is underway, operators can see what’s happening and act fast from one unified view. “With Security Center, we’re shaving valuable time from investigations and response," said Luca Aiello, Security Manager at Oxford Properties. Enhanced guest experience “Our security operators can identify potential risks, retrieve critical information, and deploy on-foot officers faster within the shopping center." "Overall, we’ve become far more proactive and efficient in handling anything that comes up. That ensures we keep providing an exceptional guest experience.” Sipelia™ intercom module Sipelia allows them to initiate two-way conversations across 150 intercom stations Operators manage over 750 cameras, 500 access control readers, and 2000 cardholders using the Security Center. They’ve also deployed the Sipelia™ intercom module. Sipelia allows them to initiate two-way conversations across 150 intercom stations located in parking garages, entrances, and other areas. AutoVu™ ALPR system The team also added the AutoVu™ automatic license plate recognition (ALPR) system, the Genetec Mission Control™ decision management system, and other technologies within the platform. All video, data, and calls come back into a state-of-the-art command center, where security operators keep the shopping center running smoothly. Security managers can also use the Genetec Mobile app on their phones to check in on situations from anywhere in the mall. Operational efficiencies, enhancing public safety To streamline incident response, the Yorkdale team implemented Genetec Mission Control™ Ensuring security operators can quickly respond and resolve the issues is critical to maintaining a five-star shopping experience. To empower their operators and streamline incident response, the Yorkdale team implemented Genetec Mission Control™. The collaborative decision management system helps operators better understand unfolding events and guides them through the best course of action according to SOPs. Proactive security approach Genetec AutoVu™ has been a key component in fostering a proactive security approach. With 52 AutoVu automatic license plate recognition (ALPR) cameras deployed, they’ve been able to extend security to their property’s perimeter, enhance vehicle-related investigations, and help serve the community. For example, if local police are searching for a vehicle of interest, Yorkdale can put that vehicle information into their AutoVu system, and if the vehicle comes onto their property, police are notified. Responsive to theft-related incidents As incidents of vehicle and/or retail theft rise, the AutoVu ALPR system has also become a deterrent As incidents of vehicle and/or retail theft rise, the AutoVu ALPR system has also become a deterrent. Said Bob Vounotripidis, Senior Operations Manager at Yorkdale Shopping Center, “Since implementing the AutoVu ALPR system, we’ve become significantly more responsive to theft-related incidents and investigations. Word has gotten out–Yorkdale is a property that takes security seriously, and the perpetrators will be caught.” Planning for future expansions The Yorkdale team is looking ahead to other technologies that can expand their security approach and system, such as deploying body-wearable technology and integrating video from those devices into the unified platform. They are also exploring using Genetec Clearance™ digital evidence management system to streamline evidence sharing with law enforcement. Said Aiello, “More shopping centers should be using Genetec Security center. This security platform not only helps our team operate more efficiently, but we’re also evolving our deployment using the best technologies out there.”
Required a reliable Indian brand that could provide pre and post-sales support throughout India. Matrix’s competitor brands had failed to provide tech support in some remote locations in India Need for effective monitoring in critical areas of the store: Entrances, Exits, Aisles, Cash Counters, and Inventory Need for a solution that provided valuable video evidence for dispute resolution and liability claims Required efficient monitoring at night to mitigate the risk of thefts Solution offered With growing stores across India, they chose Matrix again due to satisfactory results in the past The eyewear chain relied on Matrix for its video surveillance needs as they were highly satisfied with Matrix Access Control and Matrix Telecom solutions, previously. Earlier, they had installed Matrix IP Cameras, Video Recorders, and Matrix Video Management Software for centralized monitoring. With expanding stores across India, they chose Matrix again due to satisfactory results in the past. 1500+ store locations pan India were secured with Matrix IP Cameras and NVRs. A typical deployment in the store included installing 4 to 5 Matrix Professional Series Dome IP Cameras inside the store. Placement of the camera locations The cameras were strategically placed at the following locations: Outside the Store Premises Entry/ Exit of the Store Product Display Aisle to Monitor Customer Interactions Cash Counters Inventory In the Store Matrix SATATYA SAMAS VMS An 8-channel Matrix NVR with 1 SATA Port was installed within each store to record and store video footage from these IP cameras. A particular location in South India required a centralized monitoring solution. For this purpose, Matrix SATATYA SAMAS, Enterprise Video Management Software (VMS) was provided. With the help of this solution, various multi-location cameras could be centrally monitored from a single location. Products Offered SATATYA MIDR20FL36CWS (5000+): 2MP IR Dome Camera with 3.6 mm Fixed Lens SATATYA NVR0801X (1000+): 8 Channel NVR with 1 SATA Port Support SATATYA MIBR20FL28CWS: 2MP IR Bullet Camera with 2.8mm Fixed Lens SATATYA CIBR50FL28CWS (10+): 5MP IR Bullet Camera with 2.8mm Fixed Lens SATATYA PZCR20ML33CWP: 2MP PTZ Cameras with 33x Optical Zoom SATATYA NVR6408X: 64 Channel NVR with 8 SATA Ports Matrix License Dongle 200: USB Dongle to Run License VMS Application SATATYA SAMAS PLT: Enterprise Video Management Software SATATYA SAMAS CAM100 (3 Nos.): 100 Camera License for Enterprise VMS Solution diagram Benefits Pan India Pre and Post-Sales Support: The team at Matrix ensured seamless deployment of cameras and NVRs even in the most remote locations of India. Further, the eyewear chain was assured of technical support whenever required. Comprehensive Security: Matrix IP Cameras and Network Video Recorders ensured robust security coverage for the brand’s retail outlets throughout India. Preventive Crime Measures: Intelligent Video Analytics and Instant Notifications played a crucial role in deterring and preventing shoplifting, vandalism, etc. Enhanced Nighttime Security: The Motion Detection IVA feature in Matrix IP Cameras specifically addressed heightened security concerns during store closure. It triggered instant SMS and email notifications to relevant staff upon detecting motion, proactively preventing incidents even after closing hours. Efficient Bandwidth and Storage: The Adaptive Streaming and Smart Streaming Feature in Matrix IP Cameras intelligently managed bandwidth and storage usage, optimizing resources. Customized Recording Retention: Matrix NVRs have camera-wise recording retention, enabling tailored storage duration for each camera’s recordings and backups, further enhancing storage efficiency.
IDIS, the largest manufacturer of trusted South Korean-made video tech, has partnered with French cosmetic and beauty brand Yves Rocher to help them expand their growing network of stores in shopping malls, tourist hotspots, and prime retail locations. Key to Yves Rocher’s profitability is advanced remote monitoring and business intelligence analytics to give its central management team greater understanding and control over branch operations. Need for a video solution The company needed a robust video solution to reduce shrinkage, improve customer service, drive sales, and improve staff performance. This was challenging, though, because a wide array of existing analog and IP cameras was in place, as well as an inflexible VMS. Cameras were obtrusive and did not provide comprehensive coverage in HD quality. IDIS video tech solutions The system had no analytics functionality, so a labor-intensive people-counting solution was used And the system had no analytics functionality, so a labor-intensive people-counting solution was being used which was driving up operating costs. Yves Rocher turned to trusted and proven IDIS video tech solutions to solve all these challenges. NDAA-compliant single-camera solution IDIS, together with Secom Türkiye, replaced the existing mix-and-match system with a powerful, NDAA-compliant 5MP IR fisheye camera (DC-Y6516WRX-A), managed and controlled via cost-free IDIS Center in the stores, and IDIS Solution Suite (ISS) Expert VMS at Yves Rocher’s head office. The footage is recorded locally on a 4-channel IDIS DR-2504P NDAA-compliant NVR. The single-camera solution simplifies and streamlines system operation for retail staff and ensures HD coverage of the whole store, without blind spots. IDIS AI box for retail Each store is also equipped with a compact IDIS AI Box for Retail (DV-304), to deliver a wider range of powerful analytics functions, including people counting, queue monitoring, heat mapping, and occupancy monitoring. People counting data from all the stores is transmitted to the ISS server, then collected in Yves Rocher’s SQL server for sharing with the NEBİM retail ERP solution. This enables Yves Rocher to analyze daily, weekly, or monthly sales turnover and visitor numbers, comparing sales campaign periods against regular periods, and allowing an accurate evaluation of marketing. Streamlined monitoring and operational efficiency The IDIS solution delivers streamlined monitoring, improved store coverage, and advanced video analytics. As Can Egemen Yalçın, IT Manager for Yves Rocher points out, “Yves Rocher’s global success is built on outstanding customer service, focused management, and operational efficiency. Our new, advanced video and analytics solution from IDIS now gives us an exciting foundation for further innovation.”


Round table discussion
Headlines of violence in our schools are a reminder of the need to keep educational institutions safe. In fact, if there is a positive aspect to the constant bombardment of headlines, it is that it keeps our attention perpetually focused on how to improve school security. But what is the role of physical security systems? As the new school year begins, we asked this week’s Expert Panel Roundtable: Are schools safer because of physical security systems? Why or why not?
As physical security technologies become more complex, it is incumbent on the dealer/integrator to have the skills and expertise needed to ensure that a system operates smoothly. The value of integrators increasingly rests on the skill sets they bring to bear when installing a system. If the skills are missing, there is a problem. We asked this week’s Expert Panel Roundtable: What missing skills among security integrators can cause problems for customers?
Driving the smart homes market is the convenience of simple technology solutions. Almost every home now has a “smart speaker” that makes it easier than ever for homeowners to interface and control their technology. But where does security fit into the new landscape of smart home systems? We asked this week’s Expert Panel Roundtable: What’s new in smart homes and residential security systems?
Products


White papers
Understanding All-In-One Solutions
Download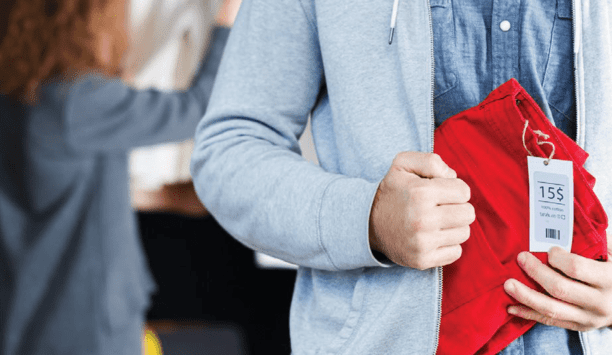
How Video Technology Is Transforming Loss Prevention, Operations, And Customer Experience In The Retail Sector
Download
Why SAAS Security Platform Is More Popular In American SMEs
Download
A Guide To Moving Physical Security Into The Cloud
Download
Intelligent Video Security Solutions
Download
Security Investments Retailers Should Consider For Their 2021 Budget
Download
Smart Security Cameras: Excellence in Retail
Download
11 Considerations For Embedded System RFID Readers
Download
Nine Ways To Make Your Retail Security System Work Harder
Download
Loss Prevention and Beyond: How Video Innovation Enriches Retailers
Download