Perimeter security
Rhombus, a pioneer in cloud-managed physical security, announced the availability of two additions to its comprehensive lineup of security solutions: the R600 Multisensor Camera and the E50 Environmental Sensor. The two new products streamline operations, create safer environments, and offer scalable solutions for meeting the critical physical security requirements in industries including education, food and beverage, healthcare, manufacturing, retail, and storage and warehousing. Rhombu...
Comcast Smart Solutions, a division of Comcast Cable that specializes in smart technologies for businesses and communities, expanded its offerings to include smart access control. Comcast Smart Solutions is now offering cutting-edge smart access management solutions to its customers from Brivo, a global pioneer in cloud-based access control and physical security technologies. Advanced control panels Comcast Smart Solutions clients have access to a broader suite of keys that help provide secur...
Direct costs such as purchase price and maintenance are important elements in the total cost of ownership (TCO). However, there are others. Elements such as opportunity costs of lost revenue or hidden costs of energy consumption and environmental consequences can also impact the measure of TCO. Costs of training, integration, support, and scalability can also be examined. Considering the security industry impact of TCO, we asked this week's Expert Panel Roundtable: How does/should total cos...
Dallmeier, one of the pioneering providers of professional video surveillance solutions, presents the new Panomera® S4 Perimeter. The “Perimeter Panomera®” combines four sensors in one optical unit. This provides a resolution of 200 effective megapixels – MPe – per camera. Combined with an AI object classification system specially trained for perimeter requirements, and AI tamper detection also optimized for this purpose, the result is an extremely powerful solut...
Huffmaster Management (Huffmaster), the provider of choice for Fortune 500 companies seeking strike services, industrial and healthcare staffing, security services, and more, announced the internal promotion of Margaret Sanders to Director of Operations within the company’s Protective Services Group, a division responsible for ensuring the safety and security of Huffmaster clients. In her new position, Sanders will work closely with the company’s Manned Guar...
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the introduction of a new I/O module to its portfolio of high-assurance access control system offerings. Developed by STid, a pioneering manufacturer of highly secure access control technologies, the new I/O module enables European customers to meet the most stringent cybersecurity compliance regulations. Cybersecurity capabilities From the creden...
News
Allied Universal®, the globally renowned provider of security solutions for the government sector, provides critical security planning and mitigation recommendations for the upcoming debates in its recently released special report titled Physical Security During an Election: Expect the Unexpected and Prepare for it All. According to Allied Universal’s experienced team of security and intelligence professionals, a wide range of security measures must be planned, reviewed, revised as needed, and then reviewed again prior to and on the day of the much-anticipated debates between U.S. Vice President Kamala Harris and former U.S. President Donald J. Trump and Vice President candidates Tim Walz and JD Vance. Physical and cyber security threats The report identifies potential physical and cyber security threats that could impact the safety The Allied Universal report leverages intelligence and expertise from the company’s more than 60 years of experience in the security industry, as well as insight from its team of veteran intelligence and security experts. The report identifies potential physical and cyber security threats that could impact the safety of the presidential nominees, debate moderators, audience members and the general public on Sept 10. “Presidential debates are pivotal events in the election cycle that draw significant attention from the public, the media, and bad actors. The politically charged atmosphere of debates can heighten the potential for security issues,” said Allied Universal Global Chairman and CEO, Steve Jones. Potential security issues Steve Jones added: “By outlining potential security considerations, threat mitigation techniques and insights on contingency planning, our hope is that debate organizers and security personnel find the report a valuable tool offering suggestions and examples that support the deployment of comprehensive security strategies.” In addition to presidential debates, the report addresses security strategies and tactics for other election year events including election day and the presidential inauguration. Potential security issues are addressed in the report and include civil unrest, active shooter, crowd control, insider threats, infrastructure attacks, cyber threats, domestic extremism, and the spread of misinformation. Mitigation approaches are also included in the report.
Signo Express and Seos Essentials provide a comprehensive, affordable access control solution designed for small to mid-sized businesses. This suite maximizes security and flexibility without complexity. Affordable access control solution This new offering contains everything end customers need to implement secure, modern access control, including: HID Signo™ Express Reader: High-security RFID & Bluetooth ® capabilities, easy install, mobile-ready. Seos Essentials Cards: Preconfigured cards, fobs, and mobile credentials, compatible with and PACS system. HID Mobile Access®: Sustainable, efficient mobile technology, instant over-the-air credential management. HID Signo Express and Seos Essentials are the simplest way to upgrade the access control experience and migrate away from insecure, legacy technology.
Award-winning, global security manufacturer, Gallagher Security, is kicking off International Women’s Day by announcing that Natalie Bannon, Director of Strategic Alliances, has been included in the 2024 honoree list for the SIA Women in Security Forum Power 100 (SIA WISF Power 100). This initiative annually honors 100 inspiring women who actively advance diversity, inclusion, innovation, and leadership in the security industry. Gallagher’s Consultant Program Natalie included in the SIA WISF Power 100 for cultivating an environment where innovation welcomed Among her many achievements - such as initiating Gallagher’s Consultant Program and consistently earning the praise of customers - Natalie has been included in the SIA WISF Power 100 for cultivating an environment where innovation, risk-taking, and diversity of thought are welcomed and encouraged. “I can’t stand it when leaders sleep on their teams and tell them no,” Natalie says emphatically. “I believe in empowering my team to be bold and fostering an environment where innovative ideas flourish. I wholeheartedly believe in not limiting people or questioning their capability until they've been given the opportunity to try. Entrusting my team to be daring with their ideas is crucial in my leadership style.” Gallagher Security’s products While Natalie might tell them that she’s led by her team, others within Gallagher say that her strategic, creative thinking and propensity for innovation inspire them to follow her. “I’m consistently surprised by what Natalie brings to the table,” says Melissa Vidakovic, Director of Marketing. “She solves problems on the spot with these incredibly creative solutions, like putting our door readers on heavy machinery to enforce safety and regulations, or wiring cars with disturbance sensors you’d normally use for perimeter fencing to prevent theft. She has a remarkable understanding of Gallagher Security’s products and sees their potential to solve customer problems in ways other people wouldn’t think of, and they’re always thrilled with the results.” End Users with right solutions Natalie has made via her work, Executive VP - Americas, Scott Elliott, directly points to her happy clients When asked about the impact Natalie has made through her work, Executive Vice President - Americas, Scott Elliott, immediately points to her many happy customers. “Natalie has a unique ability to thoroughly understand clients and their needs, which results in extremely happy customers,” Scott says. “I’ve had multiple customers tell me that they chose Gallagher because of Natalie and that they stick with us because of her, too. She intuitively knows how to connect our End Users with the right solutions to solve their individual problems, no matter how complex, and as a result she earns their trust.” SIA Women in Security Forum event It’s that outside-the-box thinking and empowerment attitude that makes Natalie stand out as a pioneer in the security industry and earned her a spot in this year’s WISF Power 100. Natalie and her fellow honorees will be recognized at a special SIA Women in Security Forum event at this year’s ISC West exposition taking place in Las Vegas April 9-12. She will also be available for conversations and congratulations at the Gallagher Security booth (#27099) throughout the event.
Scandit, the pioneer in smart data capture, announces the asset acquisition of shelf audit automation technology from MarketLab, a Polish image recognition and AI software company specializing in the retail industry. As part of the transaction, MarketLab's expert team will join Scandit to build and expand the new offering. MarketLab's expertise in fixed camera solutions complements Scandit's existing ShelfView mobile capture approach to provide a hybrid data capture shelf intelligence solution for retailers. The global retail sector loses approximately $634 billion annually due to problems with on-shelf availability alone, according to research from IHL Group. Optimal store conditions The new hybrid solution will enable retailers to gain insights into on-shelf availability Delivering increased workforce efficiency and automating time-intensive store operations processes, the new hybrid solution will enable retailers to gain insights into on-shelf availability, planogram compliance, pricing issues, and more to maintain optimal store conditions, maximize sales, and reduce lost revenues due to stockouts, particularly in high-SKU volume environments like grocery stores. It will also provide AI-enabled notifications to improve store key performance indicators and flag issues in near-real time to store associates and management. "The acquisition marks a new milestone in Scandit's evolution as we continue to broaden our smart data capture capabilities for the wider retail industry. Integrating MarketLab's fixed camera-based shelf recognition experience and technology into ShelfView strengthens our ability to empower retailers to enhance their overall store performance, boost store associate efficiency and optimize the monetization of shelf data with CPG partners," said Samuel Mueller, CEO and Co-Founder of Scandit. Accurate stock availability "We are delighted to join forces with Scandit. Combining our complementary technologies, we look forward to delivering additional value, ROI, and insights to grocery retailers globally so they can benefit from increased visibility into their shelves, ensure accurate stock availability, and ultimately enhance the customer experience," said Piotr Wardaszko, CEO of MarketLab. Leveraging the strengths of mobile capture and fixed cameras offers retailers a complete, scalable, and flexible solution for all store formats, with a seamless path to more efficient and cost-effective shelf management. Mobile capture, via smartphones or handheld computers, is easily deployable using existing devices, adaptable to different store environments and can be scaled quickly. The addition of fixed cameras provides continuous high frequency data capture for near-real-time shelf monitoring, while freeing up store associates to devote their time to higher-value tasks, such as customer engagement. Cost-effective shelf management The acquisition strengthens Scandit's retail shelf management and analytics solution, ShelfView The acquisition strengthens Scandit's retail shelf management and analytics solution, ShelfView, which leverages object recognition, augmented reality and other advanced computer vision technology to process images for more intelligent and efficient store operations. Thanks to Scandit's AI and machine learning capabilities, ShelfView delivers alert accuracy at 99.7% — crucial for delivering reliable insights quickly in rapidly changing shelf situations. With Scandit's large existing retail customer base, including eight out of the top ten US grocers plus MarketLab's existing accounts including Carrefour Poland, Scandit is well positioned to drive further growth and retail innovation. Providing valuable insights The acquisition opens new routes to market by providing valuable insights to consumer packaged goods (CPGs) and merchandizing agencies to maximize revenues through higher on-shelf availability, accurate pricing, promotions and planogram compliance as agreed with their retail partners. Beyond the retail sector, Scandit sees future potential in fixed camera deployments in other environments, such as warehousing to automate logistics workflows. The acquisition of MarketLab signals a new phase of growth for Scandit and advancement as the smart data capture leader. Today's announcement follows Scandit's $150m Series D investment in 2022, which has helped accelerate its R&D, with a focus on AI/ML capabilities, reflected in recent product developments such as ID Validate, ID Bolt, MatrixScan Find and more.
ISS (Intelligent Security Systems), a pioneering provider of video intelligence and data awareness solutions, has launched Intellisection, a new turnkey solution for automated intersection monitoring. Intellisection leverages artificial intelligence and advanced neural network training technology to enhance road safety and efficiency, enabling federal, state, and local agencies to create a comprehensive traffic management solution. The state-of-the-art neural network technology autonomously monitors vehicle flow, detects accidents, classifies vehicles, and provides real-time data to optimize traffic signals, ensuring smooth and safe traffic movement. Embedded at the core of the system, it combines proactive monitoring, real-time analysis, and configurable notification mechanisms to optimize the reliability, stability, and performance of all components. Key benefits Enhanced Road User Detection: Accurately detect, count, and classify all road users, including vehicle types as well as pedestrians, bicyclists, and mobility devices like wheelchairs and scooters. Improved Safety Measures: Enhance road safety with features like near-miss analysis, red-light violation monitoring, wrong-way driver detection, speeding alerts, and crash detection, helping to prevent accidents and manage incidents effectively. Real-Time Notifications: Email, text, and in-browser alerts ensure that relevant stakeholders are promptly informed about critical incidents, enabling quicker responses. Multi-Lane Monitoring: The system can detect multiple vehicles approaching or departing in multiple lanes simultaneously, making it suitable for complex intersections. High Reliability: Rated NEMA TS-2, the product is built to meet high standards of reliability and durability in various environmental conditions. Operational Insights and Reporting: The system provides operational dashboards summarizing key events, turning movements, and vehicle classifications at intersections. Detailed event statistic reports help in analyzing traffic patterns and making informed decisions. Insights for incident detection “As technology continually gets adopted into the ITS marketplace, we have seen a hammer-to-nail approach to its deployment. With Intellisection’s launch, we are providing a platform that allows agencies to optimize signalized intersection performance while offering the most feature-rich insights for incident detection – accidents, near misses, wrong-way driving, etc. – as well as traffic flow estimations, including average speed, density, vehicle classification, and beyond,” said Joe Harvey ITS Market Sector Pioneer, ISS. “Additionally, by leveraging our software platform, we enable agencies to gain comprehensive insights throughout their entire system, enhancing decision-making, improving safety, and increasing efficiency across all levels of traffic management.” Future-proof solution “Releasing a new product is never an easy process and for nearly two years our team has worked tirelessly to create a solution in Intellisection that is the nexus of roadway analytics, decision management, and data analysis,” added Matt Powell, Managing Director, North America, ISS. “I am extremely excited for us to launch this product and thankful to the communities that have worked with us in deploying Intellisection to ensure it works in the real world. Intellisection is an incredible product, built on two decades of our experience with vehicle analytics, and will grow in capability year after year to ensure a future-proof solution for creating safer, more efficient roadways.”
Waterfall Security is delighted to announce the launch of HERA™-Hardware Enforced Remote Access, a new technology designed to enable safe and secure remote access into cyber-physical systems and OT networks. HERA allows organizations to reap the operational and economical value of remotely accessing and controlling OT devices and workstations, without introducing the risks that come with external connectivity. Remote access is one of the weakest links when it comes to OT cybersecurity. For cyber-physical systems and OT environments, "opening up" the OT network to external internet connectivity to enable remote access, is below the bar required to keep operations safe and secure. Waterfall's new HERA solution HERA physically maintains network segmentation, keeping OT environments safe and secured With Waterfall's new HERA solution, enterprise-grade remote access capabilities are enabled and secured with engineering-grade security. Leveraging Waterfall's battle-tested hardware platform, HERA physically maintains network segmentation, keeping OT environments safe and secured. "HERA represents a giant leap in how the industry approaches remote access into OT environments," explains Lior Frenkel, CEO and Co-founder of Waterfall Security. "By applying physical cybersecurity over cyber-physical systems, Waterfall Security's solutions enable zero compromise between industrial cybersecurity and functionality." HERA's patented technology Frenkel added: "Together with our market-pioneering Unidirectional Gateway technology, Waterfall Security provides a holistic solution for customers with OT environments and cyber-physical assets." HERA's patented technology has been designed from the ground up with OT cybersecurity in mind. It harnesses decades of know-how, expertise, and field-tested technology to deliver the safest solution to remotely access OT networks.


Expert commentary
Security manufacturers throw around the term “scalable” a lot these days, but few dive into what scalable really means for modern organizations and their security programs. Achieving true scalability, or as I like to refer to as “expandable with a purpose,” takes planning and coordination from security pioneers alongside the broader organization. Implementing a flexible strategy is critically important in the age of advancing analytics and intelligence-driven technology. So what exactly do we mean by “scalable”? "Scalable" refers to the capability of a system, process, or technology to handle growth or increased demand without compromising performance, efficiency, or quality. To put it simply, scalability refers to the ability of a solution to expand or adapt to accommodate larger workloads, higher volumes of data, or increased complexity without requiring significant changes to its underlying architecture or design. It’s not enough to create a “fix it and forget it” security program. Not only do the needs of the organizations shift, but growth (or even shrink) is inevitable. How to Approach Growth Pioneers must be prepared to adapt their strategies and approaches to manage security risks For many security pioneers, growth has a trickle-down effect. Expansion through mergers and acquisitions or organic growth, in addition to decreases in facility or employee count, directly impacts the security program. Whether it’s an increase or decrease in size, workload, or scope, these pioneers must be prepared to adapt their strategies and approaches to efficiently manage security risks while maintaining operational efficiency. Here are some ways security pioneers can approach growth: Assess the here and now: Begin by looking at the current state of your security program, including the resources, capabilities, processes, and technology infrastructure. Understanding existing strengths, weaknesses, and areas for improvement can help inform planning for the future. Align with the business: This might be one of the most important considerations to make, but ensuring security pioneers understand the organization’s growth objectives, priorities, and risk tolerance levels is critical to the success of a security program. The most successful security pioneers will be able to align security strategies with business goals to ensure security investments and planning are enabling the company’s growth initiatives. Invest in scalable solutions: Invest in solutions that offer flexibility and can adapt to the changing needs of the organization. Closed systems that can’t integrate fully with new technologies will severely limit the security team’s ability to seamlessly manage the security portfolio. Optimize processes: Reviewing security processes and workflows – or investing in a platform that can streamline this for you – can improve efficiency and effectiveness for your security team. Identifying opportunities for automation and standardization can allow for scaling as business needs change. Collaborate across departments: Preparing for growth initiatives requires extensive communication across departments, including leadership teams, human resources, legal, IT, facilities, and many other stakeholders ensure that security priorities, challenges, and requirements are effectively communicated and integrated. Adopting these approaches helps put security teams in the driver’s seat, effectively managing periods of growth and change without compromising the safety and security of the organization. Technology considerations As security pioneers navigate investments in new technologies that achieve some of the approaches listed above, such as aligning strategy with business goals, optimising processes, and cross-departmental collaboration, there are several considerations to make. Looking at how technology can support (or even hinder) future growth. For example, when making a buying decision around access control systems, security pioneers must consider the number of users, number of credentials, server requirements, facilities, hardware end points, and software features. As these items are being addressed in an RFP or in conversations with a vendor, security pioneers must ask themselves, “Is there a scenario where my program will outgrow the system’s capabilities in any of these areas?” If so, the answer might be to select a different solution. Security pioneers must consider interoperability. We talk a little about this above, but the importance here cannot be overstated: integration is key. The ability to leverage multiple point solutions, such as access control systems and video surveillance cameras – regardless of manufacturer – provides growing companies with the ability to scale quickly and more efficiently than ever before. Centralizing the ability to pull these solutions into a single security operations management platform allows security pioneers a better view of their security programs in a current – and even future – state. Cloud-based solutions can provide the ultimate scalability factor, providing flexibility and accessibility advantages compared to traditional on-premise systems. Cloud-based, or Software-as-a-Service (SaaS) platforms, can easily scale up or down based on changing needs, accommodate distributed environments, and provide remote access and management capabilities, making them well-suited for scalable physical security deployments. Data-driven insights and analytics can drive decision-making beyond security, making technology investments that provide these critical. Automated workflows, event-triggered alerts, and AI-driven analytics can streamline security processes, improve threat detection capabilities, and reduce manual intervention, enabling security teams to manage larger environments more efficiently. Centralised management of technology investments can create cohesion for security teams. Centralised management and monitoring of physical security systems across multiple locations or facilities enables personnel to efficiently oversee and control security operations, access controls, and incident response activities. Being able to manage security in a single platform provides security pioneers with the ability to assess staffing levels, streamline training, allocate resources effectively, and scale to additional sites and/or solutions as needed. Tasked with building a security program that can adapt to the changing needs of the organization, security pioneers must consider a number of factors when setting strategy. First and foremost, taking a close look at the existing program to identify strengths and weaknesses, then truly assessing the technology and processes in place, is the best way to move forward and future-proof the organization.
The days of being reactive are over. That’s right, we as an industry, can no longer afford to be reactive. As threats evolve, the need for proactive security is critical. While traditional methods, including physical barriers and security personnel, are still necessary, the future of our approach is built on the backs of emerging technologies. Substantial vulnerabilities As an industry, we’ve operated reactively for decades, it has been common for security teams to address threats only after they occur. The growing risk landscape proves that this approach has significant limitations. Human oversight, delayed responses, and the inability to monitor large areas have exposed substantial vulnerabilities. Emergence of AI AI enables real-time monitoring, advanced data analysis, and more accurate risk detection Times are changing though and it’s largely due to the emergence of AI. AI is revolutionizing the security landscape by making technology smarter. It enables real-time monitoring, advanced data analysis, and more accurate risk detection. This ensures a higher level of security and safety, minimizing potential incidents' impact while enhancing overall safety. Focus on strategic aspects AI's ability to process vast amounts of data quickly and accurately is, quite frankly, a game-changer. It can identify patterns and anomalies that can provide stakeholders with critical insights to respond in a more prepared manner. By automating routine tasks and highlighting potential issues, AI also allows operators to focus on more complex and strategic aspects of security management, rather than responding to false alarms. The future is AI The future of security lies in AI. The Security Industry Association (SIA) has recognized AI as one of the top security megatrends in 2024. However, the challenge is not adopting AI, it is about effectively using it to enhance security. AI can enhance video surveillance by improving object detection and enabling real-time, informed responses AI systems can easily integrate with existing infrastructures, providing a layered defense that combines traditional methods with more modern technology. For example, AI can enhance video surveillance by improving object detection, reducing false alarms, and enabling real-time, informed responses. This ensures that security measures are adaptive, scalable, and capable of addressing the evolving risk landscape. Don’t react, anticipate One of AI's most significant benefits is its ability to provide proactive insights. AI can predict potential breaches by analyzing behavior patterns and detecting anomalies allowing security pioneers to do something before an event happens. This shift, from reactive to anticipatory measures, marks a significant advancement in asset protection and risk management. AI systems can also continuously analyze data and distinguish between everyday events and real-world threats. It’s AI's continuous learning capabilities that mean the systems can adapt and improve over time to become more accurate and efficient in threat detection and response. Save money, scale on demand Contrary to common belief, adopting AI technologies will not put a security department over budget. It may be surprising, but these solutions offer cost-effective and scalable alternatives to traditional security measures. An initial investment in AI technology can result in substantial long-term savings (and ROI) by reducing the need for physical infrastructure and on-site security personnel. Customizable solutions The ability to scale and customize AI solutions makes them an efficient choice for enhancing perimeter defense AI systems are also inherently scalable and can be tailored to meet the specific needs of different environments. This ensures the system can evolve with emerging threats and technological advancements without requiring a complete system overhaul. The ability to scale and customize AI solutions makes them a practical and efficient choice for enhancing perimeter defense. How’s that for staying within budget? Embrace the possibilities Integrating AI into perimeter security is the future of proactive and intelligent security. As these technologies continue to evolve, we can expect even more refined solutions that are predictive, autonomous, and capable of directly addressing new and emerging threats. We’re experiencing an exhilarating transformation as AI becomes more trusted, precise, and advanced on multiple levels. This evolution is bigger than pilots and small, low-profile deployments. AI in perimeter security For instance, France is preparing to deploy AI-powered video surveillance as it gears up to host the 2024 Olympics, part of its efforts to detect sudden crowd movements, abandoned objects, and suspicious activities. Think about the sheer scale of that project. We’re finally moving forward, and staying one step ahead must be our priority. But this shift requires a significant change in mindset. Are you ready to make the change?
Amidst the challenges of a prevailing economic downturn, the retail sector finds itself grappling with an unparalleled rise in incidents of shoplifting, theft, and burglaries. The disconcerting scenes witnessed on London’s Oxford Street in August 2023, where crowds gathered, looting as many stores as possible, sent shockwaves across the nation’s retailers. This alarming surge in retail crime has put retailers on high alert, as they contend with a rising tide of security concerns. Shoplifting concerns Recent data from the Union of Shop Distributive and Allied Workers (USDAW), has raised alarming concerns: shoplifting rates have surged by an unprecedented 24%. In the first half of 2023 alone, there were approximately 8 million reported shoplifting incidents. With the ongoing burden of the cost of living crisis and the approaching festive season, it is expected that these figures will keep surging. Implementing robust security measures Theft and prevention strategies cost retailers approximately £2 billion in 2021/2022 While more help from the Government to support retail workers and the businesses shoplifters target is certainly needed, the implementation of robust security measures will significantly contribute to deterring these crimes from occurring in the first place. British retailers spend millions on tools to deter and catch shoplifters inside stores, from CCTV and security guards to electronic tagging and alarms. The Grocer reported that theft and prevention strategies cost retailers approximately £2 billion in 2021/2022. Despite these initial costs, other threats are at play beyond the shop floor. Break-ins by criminal gangs For many large town center stores and supermarkets, and units in retail parks, the rear doors and delivery areas are commonly targeted by criminal gangs. It’s not uncommon for thefts to occur from pallets or cages that have been unloaded from lorries and sit waiting to be moved into the building. After-hours break-ins are a risk for all store owners too, particularly over the festive season when a lot of high-value stock has been delivered to shops and supermarkets. Addressing anti-social behaviour The additional fencing was deemed an essential measure to safeguard the community Anti-social behavior also poses a challenge for retailers. In 2022, an Aldi based in Derby invested in security fencing to protect staff and deter loitering groups. The additional fencing was deemed an essential measure to safeguard the community, as dangerous items were frequently found outside the store, including weapons and hypodermic needles. So how do physical security solutions such as fencing and gates help better protect retail establishments such as supermarkets and edge-of-town retail park shops? Fencing and gates: a critical component of retail security 1. Risk assessment and target hardening A thorough risk assessment will identify potential weak spots that require protection. ‘Target hardening’ involves implementing physical security measures that become more robust as they approach the target. This helps deter intruders while ensuring ease of access for customers and staff. 2. Effective perimeter security Opt for difficult-to-climb security fencing that provides a robust obstacle against thieves, vandals, and intruders Selecting fencing solutions according to the potential threats, site characteristics, and topography is crucial. It is important to specify fencing that strikes a balance and maintains a welcoming appearance while safeguarding external areas of the store or warehouse from potential harm and unauthorized access. Solid fencing which provides concealment can help to conceal expensive goods and remove them as a target for opportunistic theft. Opt for difficult-to-climb security fencing that provides a robust obstacle against thieves, vandals, and intruders. I recommend selecting a sufficiently tall and robust fence such as an acoustic barrier. Its noise-reducing properties are often beneficial for these types of sites too. 3. Controlling vehicular speeds and access To enhance security, consider controlling vehicular speeds and access. One effective approach is the installation of bollards at the ends of traditional high streets. This practice is already commonplace as a means of safeguarding against hostile vehicle attacks, but it can also play a pivotal role in preventing quick getaways of vehicles involved in potential heists. Additionally, employing road blockers and sliding gates at the rear entrances of delivery areas would serve to fortify security further. These measures can help in delaying vehicles, allowing for necessary checks to be conducted. 4. Balancing security with aesthetics The presence of high-security fencing can also make a site more of a target for vandals and burglars Another challenge is avoiding creating an imposing presence, especially important for areas situated near residential communities. The presence of high-security fencing can also make a site more of a target for vandals and burglars. To minimize this risk consider specifying timber fencing and traffic barriers to secure car parks, providing both security and a welcoming atmosphere for shoppers. Taking an integrated approach Combine secure perimeter fencing with effective lighting in places with shaded areas and at doors, gates, and shop windows, alongside Perimeter Intrusion Detection Systems (PIDS), and strategically placed CCTV. These measures will hinder unauthorized entry and escape, increasing the likelihood of detection and apprehension. Prioritising employee wellbeing Installing robust security fencing, complemented by CCTV, good lighting, and guarding, creates a safe environment Installing robust security fencing, complemented by CCTV, good lighting, and guarding, creates a safe environment for employees. This not only safeguards their well-being but also provides peace of mind that they are protected effectively in the case of a burglary or crime. When selecting security products for retail sites, it is advisable to opt for items that have undergone rigorous testing and carry relevant certifications for their security level. Each component should meet industry-specific standards for its intended purpose and originate from manufacturers accredited under ISO 9001:2015. This ensures a high standard of quality and reliability in safeguarding the premises. High-quality security fencing As the cost-of-living crisis continues, crime rates increase, and the festive season approaches, the time to act and implement on-site security is now. By investing in comprehensive security measures, retailers can protect their assets, employees, and customers, ensuring a safer and more secure shopping environment for all. High-quality security fencing is also a sound investment, that requires little or no maintenance once installed. The best fencing solutions are extremely weather-resistant, and won’t suffer from rust or corrosion. With all sectors preparing to ride the rapids of recession in the coming year, improving on-site security while selecting cost-effective measures, is one surefire way to protect your people, your property, and your profits from harm.
Security beat
In an emergency, information is pivotal. More information provides better understanding of an emergency and empowers potentially life-saving decision-making. Emergency response teams depend on information to guide their efforts and to deliver targeted assistance. On the front lines of emergency response are 911 and field responder agencies, which must direct reaction to life-or-death situations rapidly and efficiently. Historically, 911 operators had to respond based on very little information, perhaps just a voice on the phone or a location on their screen. Providing critical information Today, there are literally millions of information sources available, ranging from connected buildings to vehicle telematics to live video streams to health information from wearable devices. In fact, there are 540 million connected devices, any one of which could provide critical information in an emergency. But how can those information sources be leveraged to improve emergency response? That’s the mission and value proposition of RapidSOS, an ‘intelligent safety platform’ company that connects 911 operators with the vast universe of information available to promote better and faster emergency response. Highly sophisticated operation The platform is integrated into every major public safety software system and first responder agency “RapidSOS fuses human and artificial intelligence to put critical information from any connected device directly into the existing systems and operating procedures of first responders across the United States,” says Michael Martin, CEO of RapidSOS. RapidSOS is widely used by first responders. The platform is integrated into every major public safety software system and first responder agency. There are more than 4,600 software integrations that serve more than 21,000 first responders and 911 agencies. In 2023, RapidSOS supported the lifesaving work of public safety across 171 million emergencies with 3.3 billion data payloads. The system is adaptable and configurable to support any agency, from a highly sophisticated operation in New York City to a local sheriff running their own 911 center. Intelligent analytics and reporting RapidSOS Unite is the latest evolution of the product, a single solution that includes AI automation, rich content pathways, redundant connection to caller phones, and access to millions of connected devices. In an emergency, Unite intelligently fuses data from among millions of sensor feeds into a unified picture of an incident, allowing public safety officials to view real-time location, health profile, telematics, alarm data, and more. RapidSOS Unite is the latest evolution of the product, a single solution that includes AI automation RapidSOS offers core modules that handle call, text, video, sensor, mapping, and administration tools, and that provide partner data from connected devices. Additional modules provide enhanced geographic information system (GIS) data, and automated translation and transcription. There is also a single sign-on (SSO) upgrade, intelligent analytics and reporting, and seamless integration into field responder applications. Field responder applications Consider how an emergency might unfold and how RapidSOS can help. In a car accident, data from a modern automobile telematics system can alert a 911 operator of the accident as it happens. Data from a passenger’s wearable device might provide information about their health and condition. A nearby video or traffic camera could fill in details of how the accident occurred. Useful information in an emergency might come from any one of thousands of sources, including public safety data, sensor feeds, enterprise security systems, smart phones, etc. In a train derailment, electronic access to the cargo manifest can identify which train cars contain hazardous materials and how to manage the specific type of hazmat. This information could save valuable time when responding to incidents like the Feb. 3, 2023, Norfolk Southern train derailment involving 38 cars in East Palestine, Ohio. Consider how an emergency might unfold and how RapidSOS can help Institutional security partners Norfolk Southern is one of the companies that provides information to first responders using RapidSOS; in effect, the company provides a direct digital link from their rail security operations to any first responder in the United States. Amazon’s global operations centers also interface with RapidSOS to provide critical information to first responders. Partnering with corporate security helps to better support the flow of data from institutional security partners and their solutions. Information can transform and guide emergency responses. For example, in a structure fire, real-time sensor feeds throughout a building can help 911 and first responders understand how the fire is progressing. Real-time security camera footage Having access to live feeds can save lives as 911 provides pre-arrival instructions such as CPR Leading the way to providing video feeds from private camera systems to 911 operators is an agreement between Eagle Eye Networks and RapidSOS, which was announced in April 2024. The agreement allows an enterprise to opt-in to share real-time security camera footage from an Eagle Eye video stream during a live 911 call. Having access to live feeds can save lives as 911 provides pre-arrival instructions such as CPR. “Security cameras are crucial in many locations, including schools, but previously those cameras could not be accessed by 911 during an emergency but were only used for investigation after an incident,” says Martin. Improving fire and life safety systems RapidSOS is also integrated with Honeywell’s Connected Life Safety Services (CLSS) system, a cloud platform that combines software and hardware to improve fire and life safety systems. Technology integrations between the two companies further modernize and digitize the public safety communications process to provide faster, more accurate communications with emergency centers (i.e., 911 agencies). RapidSOS technology securely transmits detailed data about an emergency CLSS provides real-time visibility and connectivity to help systems integrators and facilities managers make informed decisions and manage fire systems more efficiently. When combined with Honeywell's solutions, RapidSOS technology securely transmits detailed data about an emergency, such as the type of hazard, severity, and location within the impacted building, to emergency response centers. Video object detection Rapid SOS’s emerging Harmony artificial intelligence (AI) product serves as a ‘co-pilot’ for 911 operators, helping them manage the high volume of emergencies by making their response more efficient. Harmony pulls all the sensor feeds in an emergency and works to make only the most important information available in the hands of 911 and first responders. Harmony can take key insights from text and video data, use ‘sentiment analysis’ to determine the emotion tone of a message, and help 911 professionals using language translation, keyword alerts and video object detection. Harmony can help local agencies as they address a 25% average staffing shortage by providing additional support to 911 professionals while lessening the workload. Harmony is also working to help RapidSOS expand the ecosystem, stitching more data together and quickly making it more actionable than ever. Emergency response system RapidSOS also interfaces with Iamresponding, a comprehensive end-to-end emergency response system for first responders in the fire and other emergency sectors. Iamresponding’s field responder application is used by RapidSOS to get information out to first responders in the field. More than 650,000 first responders use RapidSOS’s field application RapidSOS’s recent acquisition of Iamresponding helps the company improve the connection with the last mile “in-the-field” piece of the puzzle, ensuring partners across computer-aided dispatch (CAD), integrated applications, mobile data terminals, body cameras and other responders have access to critical data. More than 650,000 first responders use RapidSOS’s field application. Enhancing emergency response RapidSOS’s Safety Pioneer Program formalizes the important partnership between RapidSOS and public safety agencies. Participants in the program receive early access to new platform features, contribute to the platform roadmap, and drive feedback to enhance emergency response. “911 and first responders do incredible lifesaving work,” says Martin. “Everything we have done and built at RapidSOS is a direct result of the engagement, partnerships, inside advice and insight we have gotten from public safety. We have learned from them, developed new technologies and tested them.” Martin adds: “Companies have data and we now know how to make that data actionable into the hands of 911 and first responders to save lives. This is an exciting moment for us continuing our mission in partnership with public safety, and for technology and security companies to have a major hand in that.” {##Poll1719488782 - What is the most valuable benefit of artificial intelligence (AI) in an emergency call center?##}
ISC West 2024 mirrored a vibrant industry on the precipice of accelerated change. Factors such as the cloud, artificial intelligence (AI), edge computing, and biometrics are shaping the future of the security marketplace, and they were front-and-center at the industry’s biggest U.S. show in Las Vegas. Foot traffic was steady and impressive, including more than 29,000 security industry professionals viewing 750 exhibitors. A torrent of eager attendees crowded the lobby on the first day and could not wait for the doors to open. When they were admitted, the wealth of technological innovation and business opportunity did not disappoint. Focus on cloud systems Cloud systems were high-profile at ISC West. Camera manufacturer Axis, for example, introduced their Axis Cloud Connect at a press conference. Meanwhile, Genetec officially launched their Security Center SaaS platform, which aims at eliminating points of friction to enable integrators to easily embrace cloud systems from quoting and ordering to provisioning and installing. Camera manufacturer Axis, for example, introduced their Axis Cloud Connect at a press conference Cloud provider Eagle Eye Networks promoted their new “Eagle Eye 911 Camera Sharing” technology under which both non-Eagle Eye Cloud VMS customers (via Eagle Eye 911 Public Safety Camera Sharing) and Eagle Eye customers can opt to share their video feeds for use by 911 operators in case of emergency. If users opt-in, 911 operators can have access to live video as an emergency unfolds. Eagle Eye Networks provides the feature by integrating with RapidSOS call center software. Camera locations are based on geolocation coordinates, and customers can choose if they want to participate and which cameras they want to share. Biometrics in the mainstream Biometrics were well represented at ISC West, including Alcatraz AI, which introduced an outdoor version of their biometric face recognition product. The Rock X works well despite harsh lighting. Alcatraz’s products do not have to be integrated, they communicate just like a card reader using OSDP or Wiegand protocol. “At the show, customers are excited about moving to a frictionless environment and getting rid of existing credentialing,” said Tina D’Agostin, CEO and co-founder of Alcatraz. “We are making access control frictionless, secure and private. The experience can be as passive as possible – people can just walk in.” Multiple types of authentication, and the ability to detect tailgating and stream video SAFR from Real Networks also featured biometric face recognition, emphasizing feature sets, convenience, and price/performance. They offer multiple types of authentication, and the ability to detect tailgating and stream video. A new device is a small mullion mount that is “approaching the price of a card reader, factoring in the need to purchase cards,” said Brad Donaldson, Vice President and General Manager. SAFR focuses on convenience: You don’t have to take out your phone to pass through a door. Enrollment is easy by incorporating existing databases, and costs are lower than competitors, said Donaldson. The system analyses multiple points on the face, turns it into data and then encrypts it, providing a “unique signature for each person.” Credentials in Apple Wallet and Google Wallet AMAG Technology announced the compatibility of credentials with the Apple Wallet and Google Wallet. The company is also embracing a new strategic direction under President David Sullivan. They launched a new website in January, are developing dynamic resources and a partner page, and they now integrate with 120 tech partners. AMAG Technology Financial Services now enables their channel partners to offer leasing and financing options to customers. The big new booth at ISC West reflected an effort to “market different and look different,” according to the company. The big new booth at ISC West reflected an effort to “market different and look different" The new Symmetry Control Room, a command-and-control system, is a relaunch of an earlier AMAG product with enhanced features. Suitable for large enterprise customers, the software enables a big video wall to display all the various systems and incorporates all the data into a single “pane of glass.” Operators can “draw a lasso” around cameras they want to display on the video wall and can follow action across multiple camera feeds. Navigating megatrends A breakfast meeting for integrators, sponsored by Assa Abloy Opening Solutions, was built around the theme “Navigating Megatrends for Sustainable Growth." The megatrends are artificial intelligence, sustainability and cybersecurity. Related to cybersecurity, there are 350 common vulnerabilities and exposures (CVE) published per week, reflecting the continuing threat to cybersecurity. Physical security has a “data lake” of information from various physical security systems that can be an attractive target for cybersecurity breaches. Data sets can be exploited and/or poisoned. The security industry needs to apply “defense in depth” to the challenges of protecting data. “The threat landscape is always changing, and security technology is an iterative process,” said Antoinette King, i-PRO’s head of cyber convergence, one of the panelists. Natural language systems Natural language systems are a newer approach making an early appearance at ISC West Natural language systems are a newer approach making an early appearance at ISC West. Brivo, for example, has an early prototype of its “natural language search capabilities” that can answer questions such as “Who is in the office?” or “Where is Bob and what has he done?” Brivo also promoted its all-in-one door station device that combines a card reader and a camera (for facial authentication) and serves as a video intercom, thus eliminating the need for multiple devices at the door. Brivo is also emphasizing tailgate prevention, facial authentication, and people counting using AI at the edge. Also promoting natural language systems was Verkada, which unveiled a beta version of its AI Search feature that embraces national language capabilities. With AI Search, users will soon be able to use natural language to search for people or items. For example, a search could be “person climbing over a fence” or “person making phone call” or “person wearing football jersey.” Verkada wants to be thoughtful with the rollout and make sure effective guardrails are implemented to prevent abuse and bias. The release should happen in the coming months. Multi-family applications Allegion is promoting the XE360 hardware lock platform in various formats, including cylindrical lock, mortise lock, deadbolt, and exit trim. At the show, Allegion noted an enthusiasm for multi-family applications. “We have been surprised by the people who want to add electronics and to retrofit existing multi-family facilities to compete with newer facilities,” said Henry “Butch” Holland, Allegion’s Regional Director, Channel Sales East Region. Allegion works with 60 different physical access control software providers, including familiar players such as LenelS2 and Genetec Allegion also offers an “indicator” display on its locks, showing at a glance whether a door is locked or unlocked. The “indicator” might also display “occupied” or “vacant.” Allegion works with 60 different physical access control software providers, including familiar players such as LenelS2 and Genetec. Integrator M&A trends Everon looks for acquisitions in areas where they do not currently have support for national accounts A conversation with Everon at ISC West provided insights into the accelerating trend of mergers and acquisitions among the integrator community. Everon, formerly ADT Commercial, has done six acquisitions of local integrators since they changed their name last year. In targeting companies to acquire, they look for a good company with a good reputation, and they consider how the new company’s competencies complement their own. Some M&A strategy is geographic, as Everon looks for acquisitions in areas where they do not currently have support for national accounts. They also consider density, seeking to add new acquisitions in larger markets where they don’t currently have a big market share. “A lot of investment is coming into security because it is seen by investors as recession-proof,” said Michael Kennedy, VP, Mergers and Acquisitions, for Everon. Kennedy met with 95 businesses last year for possible acquisition, and the company only finalized a handful – reflecting that Everon is selective and careful that corporate cultures are aligned. “With an acquisition, the goal is to keep every customer and every employee,” said Kennedy. Voice of the customer ISC West provides an opportunity for manufacturers to listen to the “voice of the customer;” in person, no less. “We have every kind of problem come to the booth,” commented Heather Torrey, Honeywell’s General Manager, Commercial Security, Americas. “People are passionate, interested and very specific with their questions and comments,” she said. “We are driving a complete system, but we are flexible, helping our customers to meet their needs and not try to fit every foot into the same shoe. Sometimes meeting customer needs involves working with competitors," Torrey commented. “It truly comes back to listening to the customer, not just ‘this is what we have to offer,’” she adds. ISC West provides an opportunity for manufacturers to listen to the “voice of the customer;” in person, no less. Edge applications are everywhere at ISC West, and one company is promoting a new approach to expand functionality at the edge. Camera company i-PRO advocates the use of the “Docker” platform for app development, an option they offer on their cameras. Docker “containers” package deep-learning algorithms to make it easier to embed software into edge devices. Anyone can run Docker apps on i-PRO cameras that use the powerful Ambarella chip. A Docker “swarm” can combine multiple edge devices to work together and share resources. For example, the approach can increase computing power at the edge to increase the capabilities of instant analytics. It’s faster and provides better redundancies. A “distributed computing platform” ensures less latency than communicating analytics to a central server. Unification of capabilities Johnson Controls (JCI) also promotes the trend of combining multiple systems into a single pane of glass. Their “Open Blue” platform, with a security version unveiled at the show, integrates various security systems into one, combining data and monitoring device health. Basically, the system manages all resources holistically. JCI also notes a trend toward “unification of capabilities,” e.g., combining access control and video. “The scope of security is evolving from a focus on protection to a broader focus on operations,” commented Julie M. Brandt, JCI’s President, Building Solutions North America.
As the physical security and cybersecurity worlds converge, many industry professionals are finding themselves moving from one realm to the other. Or, more likely, they are embracing both disciplines as integral to the future of security as a whole. One security professional bringing her cybersecurity expertise to the physical security market is Wendy Hoey, Director of Sales, US Sales Leadership, North America, for Milestone Systems. With more than 23 years of experience in cybersecurity, Wendy Hoey now works with a global company dedicated to empowering people, businesses and societies with data-driven video technology. Author's quote Caught up with Wendy Hoey to discuss how the security market can harness innovation “I'm thrilled to be joining the physical security industry at this transformative time when there's such tremendous potential to update legacy systems with pioneering technologies like AI and the Internet of Things,” says Hoey. “I'm energized by the chance to collaborate with colleagues to help transform physical security, enhance predictive capabilities, and realize a shared vision of seamless protection across the digital and physical realms.” Caught up with Wendy Hoey to discuss how the security market can harness innovation to make the world safer and more secure. “The future is bright, and I'm honored to be part of this community,” says Hoey. Q: What can physical security learn from the world of cybersecurity? Hoey: Physical security can learn a great deal from the world of cybersecurity. With the rise of IoT and IP-connected devices, the lines between physical and digital security are blurring. Like cybersecurity, physical security needs to take a proactive approach to protecting core systems and perimeter access points. Understanding potential vulnerabilities and attacks is key. Physical security pros should continuously educate themselves on emerging technologies and threats and stay up to date on best practices. Adopting a customer-centric mindset is also critical. Rather than just selling technologies, physical security providers should focus on understanding clients' unique risks, objectives, and pain points. By taking cues from cybersecurity, the physical security industry can transform itself, innovate, and provide smarter solutions. Q: How is physical security a unique application for IT? How do physical security (and/or video) systems differ from “other” IT systems? Hoey: Physical security has unique challenges compared to traditional IT systems, but also shares some commonalities. At its core, physical security relies on networked hardware like cameras, access control and detectors that must be online and recording effectively at all times. This is like IT infrastructure in that uptime and availability are critical. With the rise of IoT, cyber and physical security are converging. Physical security systems have vulnerabilities that didn't exist before everything became IP-connected. Staying on top of emerging technologies and threats is crucial. At the end of the day, both physical and cyber security share the goal of minimizing organizational risk, and both disciplines must come together and cooperate to optimize security and safety. Q: How can security integrators ensure their workforce (i.e., installers) have the required IT skills to address the needs of the physical security market? Hoey: As security networks converge more deeply with IT infrastructure, integrators must invest in training to ensure their installers have the required skills. Whether pursuing vendor certifications, in-house training programs, or partnerships with IT services firms, integrators must recognize that security solutions require IT fluency. A willingness to upskill installers and keep pace with technological change will prepare integrators to deliver the solutions end users demand in an increasingly connected physical security ecosystem. Q: What is the role of the manufacturer to ease the application of IT technologies to the physical security market? Hoey: The role of the security manufacturer is to simplify and facilitate the application of IT technologies by serving as a trusted advisor and educator. Manufacturers must provide guidance, case studies, and domain expertise to help partners and end users understand the full capabilities of technologies and how they can be leveraged most effectively. Rather than just promoting a specific product, manufacturers should always take an active role in informing the channel and customers on available possibilities, bringing real partnership through tailored advice and solutions. Q: What challenges remain relating to implementing IT technologies in the physical security industry? How will new technologies (e.g., AI) transform the IT environment for physical security now and in the future? Hoey: When implemented thoughtfully, AI has enormous potential to transform physical security by helping security professionals identify anomalies and patterns in data to enable predictive analytics. With the right solutions, AI can act as a force multiplier by monitoring behaviors and giving security teams advance warnings before incidents occur. As AI and other emerging technologies mature, they will bring the industry in line with the most advanced security tools available. The future looks bright for a truly integrated physical and digital security environment with AI pioneering the charge.
Case studies
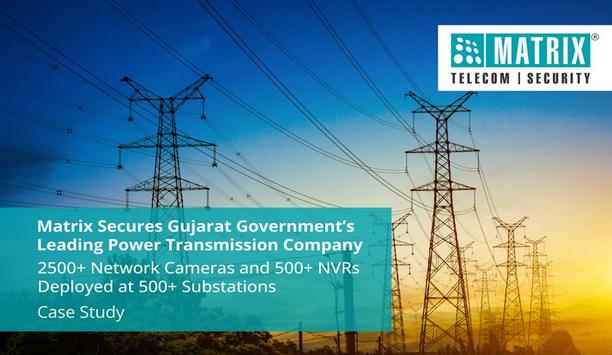
Established in May 1999, this state-owned electric power transmission company operates under the Gujarat Electricity Industry Act, of 2003. It ensures a reliable power supply across Gujarat through an extensive network of high-voltage transmission lines and substations. Emphasizing advanced technologies and innovative practices enhances grid stability and performance. With a focus on sustainable development and renewable energy integration, it supports Gujarat's economic growth by providing a resilient power transmission framework, playing a crucial role in the state's energy landscape. Business scenario The absence of a video surveillance monitoring system presented significant security challenges for the power transmission company. With over 60,000 km of transmission lines and 500 substations, the lack of continuous monitoring and recording left the infrastructure vulnerable to theft, equipment tampering, and unauthorized access. Manual inspections were time-consuming and insufficient for real-time threat detection, leading to frequent operational disruptions and increased maintenance costs. Without a proper video surveillance monitoring system, the ability to respond swiftly to emergencies was compromised, jeopardizing the safety of the state's power transmission network. Challenges faced The power plants and substations in the power transmission company had critical infrastructure components that were vulnerable to security threats like vandalism, tampering, and theft. Susceptibility to EMI/EMC Issues They needed a video surveillance monitoring system that could comply with EMI/EMC standards Operations in the power plant are susceptible to Electromagnetic interference (EMI) and Electromagnetic Compatibility (EMC) issues, which can pose safety risks. They needed a video surveillance monitoring system that could comply with EMI/EMC standards to ensure reliable operation. Harsh Environmental Conditions Being in remote areas, power plants and substations often face harsh weather conditions, necessitating weatherproof network cameras to ensure continuous and reliable surveillance. Workplace Safety and Occupational Health The impact of workplace accidents, injuries, and occupational illnesses on employee health, productivity, and morale was significant due to inadequate surveillance coverage. They needed a video surveillance monitoring system with incident reporting capabilities to enhance workplace safety, prevent accidents, and ensure compliance with occupational health and safety regulations. Data Protection Compliance They required a video surveillance monitoring system that could comply with data protection regulations governing the collection, storage, and sharing of surveillance footage to safeguard sensitive information and ensure regulatory compliance. Inefficient Manual Inspections Relying solely on manual inspections for monitoring proved inefficient and prone to oversight Relying solely on manual inspections for monitoring proved inefficient and prone to oversight. This delay in identifying issues led to extended downtime and potentially escalating problems, compromising overall operational efficiency. Slower Emergency Response In the event of an emergency, such as equipment failure or natural disaster, the lack of real-time surveillance delayed response times, increasing the risk of prolonged outages and damage, which could have been mitigated with a more responsive video surveillance monitoring system. Matrix solution To enhance security across 500 substations, Matrix Network Cameras and Network Video Recorders (NVRs) were strategically deployed to ensure comprehensive surveillance. Each substation was equipped with a Matrix 2MP PTZ Camera, strategically positioned to detect threats from a distance. These cameras provided enhanced perimeter security by offering high-resolution zoom capabilities and 360-degree coverage, allowing for the identification and tracking of potential intruders. Bullet Network Cameras Three to four Bullet Network Cameras were installed both inside the substations and around the periphery. These cameras ensured thorough surveillance coverage by capturing high-definition video of key areas, including entrances, exits, and critical infrastructure components. NVRs The NVRs were connected to TV screens in the control rooms, enabling security personnel to monitor live feeds Each substation was equipped with an NVR to record and store the feeds from the network cameras. These NVRs were configured to provide continuous recording, ensuring that all activities were documented. The NVRs were connected to TV screens in the control rooms, enabling security personnel to monitor live feeds and review recorded footage. Security personnel could access and review recordings locally on individual stations using the device client installed on the NVR. This allowed for quick retrieval of footage in case of incidents or investigations. Video surveillance monitoring system The video surveillance monitoring system was enhanced with basic Intelligent Video Analytics features, such as tripwire detection, motion detection, and intrusion detection. These features automatically analyze video feeds to identify and alert suspicious activities. Video pop-up notifications were configured to alert security personnel in real time. When an IVA event was triggered, such as an unauthorized entry or unusual movement, a notification would appear on the monitoring screens, prompting immediate attention and response. Products Offered SATATYA PZCR20ML33CWP P2 (36 Nos.) 2MP IP PTZ Camera with 33x Zoom SATATYA CIBR20FL36CWS P2 (2682 Nos.) 2MP IR Bullet Fixed 3.6mm Lens SATATYA NVR1602X P2 (33 Nos.) 16 Channel NVR with 2 SATA Ports SATATYA NVR0801X P2 (487 Nos.) 8 Channel NVR with 1 SATA Port Benefits Matrix Network Cameras adhere to OWASP ASVS 4.0 L2 data protection norms Continuous 24/7 surveillance with Matrix Network Cameras and NVRs reduced risks of theft, tampering, and vandalism. Real-time alerts and video pop-up notifications ensured prompt response to potential threats. Matrix video surveillance monitoring system complies with EMI/EMC standards, ensuring safe and reliable operations in power plants. Matrix Network Cameras adhere to OWASP ASVS 4.0 L2 data protection norms, safeguarding sensitive information and ensuring legal compliance. Adaptive Streaming and SATATYA SIGHT Matrix Network Cameras have an Adaptive Streaming feature. This allows recording at a higher bitrate during activity periods and a lower bitrate during no-activity periods. This aided in saving on storage space. Matrix NVRs have the mobile app - SATATYA SIGHT, which allows users to monitor network cameras from any location, at any time.
The perimeter of a small and medium-sized business (SMB) property is its first line of defense against intruders. It keeps the premises away from theft, property loss, and security incidents. Having said that, traditional methods of surveillance cannot fully catch up with the round-the-clock monitoring requirement of the scenario and unable to dispatch security personnel in time to handle abnormal situations, especially during night time. Backtracking to locate the cause of the event is deemed too difficult due to the lack of visual evidence. Dahua’s AI solution To address these challenges, Dahua Technology developed an AI Perimeter Protection Solution that can realize 24/7 perimeter protection, enabling accurate detection of intrusion events, active deterrence, and notification of security personnel in time when an intrusion is detected. It also provides a clear video recording of the incident that can serve as valid evidence in case of further investigation. In terms of benefits, Dahua’s AI Perimeter Protection Solution has a variety of options tailored to the actual needs of customers based on their application scenarios: Basic: This option offers a 15-meter perimeter protection coverage and round-the-clock video recording of evidence. Advanced (TiOC): With Dahua’s Three-in-One Camera (TiOC), this option also offers a 15-meter perimeter protection coverage, combined with accurate AI-powered detection of intrusion, focusing on real threats in the monitored scene. It can perform real-time processing of events using active deterrence and provide instant notification through the DMSS app for quick response to prevent any loss. What’s more, a clear video recording of intrusion evidence is also available in case of an investigation. Advanced (Thermal + Visual Dual Lens): This particular option offers a longer perimeter protection coverage of 50 meters. It provides precise intrusion detection powered by AI, with instant notifications via the DMSS app to enable security personnel to respond in time when an intrusion is detected. For evidence, clear video footages can also be retrieved, thanks to the intelligent camera equipped with thermal and visual dual lens. Dahua’s AI Perimeter Protection Solution Topology AI-powered security solution Overall, Dahua’s AI Perimeter Protection Solution is a complete AI-powered security solution that offers 24/7 accurate detection, timely processing of intrusion events, and clear intrusion evidence in case of a security breach, making it suitable for a wide range of SMB scenarios such as factory, apartment complex, construction site, school, hotel, and more.
Jacksons Fencing has recently completed a project with the Kingdom Hall in Hoddesdon, striving to enhance both the safety and visual appeal of its premises. As a place of worship for Jehovah’s Witnesses, the Kingdom Hall is meticulously maintained by its congregants to embody modesty and purpose. Enhancing security and esthetics The primary goal was to bolster security against unauthorized access, vandalism, and theft, while also complementing the dignified exterior of the place of worship. Recognizing the importance of creating a secure yet welcoming environment for congregation members and visitors alike, Jacksons Fencing was entrusted to install vertical bar railings around the building’s perimeter. These railings, coated in black architectural grade polyester powder, were chosen for their security features and aesthetic compatibility with the existing brick façade. The solution The black polyester powder-coated finish was chosen for its longevity and low maintenance The selection of a black polyester powder coating not only ensures durability and weather resistance, but also aligns with the hall’s commitment to sustainability and environmental stewardship, by minimizing maintenance needs. Safety and security were paramount concerns for the premises. To prevent unauthorized access, vandalism, and theft, and to safeguard everyone within the premises, the installation of vertical bar railings was deemed essential. Additionally, enhancing the building's exterior esthetics was a key consideration. The decision to use black polyester powder-coated railings was driven by the ability to harmonize with the brick façade, thereby enhancing the overall sophistication of the hall’s appearance. Jacksons Fencing’s experienced installation team anchored the Barbican Imperial® vertical bar railings to the brick wall, utilizing cranked posts for added stability. The black polyester powder-coated finish was chosen for its longevity and low maintenance, reflecting Jehovah’s Witnesses' emphasis on sustainable practices and responsible investments. Ensuring sustainability Environmental stewardship is at the heart of Jehovah’s Witnesses teachings, and this principle guided every aspect of the project. Emphasizing quality and longevity reduces lifetime costs and environmental impact by decreasing waste and the need for replacements. Jacksons Fencing’s 25-year guarantee on both steel and timber products further ensured that the fencing and gates were an ideal fit for this project. The power of protection Project not only managed the useful needs of the flock but also enhanced the visual harmony The installation of the vertical bar railings not only delineated clear boundaries but also effectively deterred unauthorized access, ensuring unobstructed views from inside the building to the surroundings and contributing to a safer environment. Through detailed planning, bespoke design, and precise execution, the Kingdom Hall achieved significant advancements in both security and esthetics. This project not only addressed the practical needs of the congregation but also enhanced the visual harmony of the premises, creating a secure and welcoming environment for all. Well-being of congregation members Peter Jackson, Managing Director, Jacksons Fencing, says “We are proud to have contributed to creating a secure and welcoming environment for the Kingdom Hall in Hoddesdon. In today’s world, ensuring the safety and well-being of congregation members and visitors is more important than ever." "We have worked closely with the congregation to ensure the final solution is fit for purpose now and well into the future. Our products aim to help the community feel safe and secure as they worship and gather.”
In the rich tapestry of Chigwell School's heritage, dating back to its founding year in 1629, 2013 marked a vibrant thread with the unveiling of a gleaming new pre-Prep School. Fast forward to now, and the campus expands further with its largest project to date, a state-of-the-art Sport and Wellness Center. Alongside these updates, the school recognized the need for increased security around the Drama Center. Situated in leafy Essex, Chigwell School, renowned for its nurturing environment, commitment to lifelong learning, and extensive 100-acre site, wished to enhance its site security without disrupting the daily school activities. After careful planning and collaboration with a trusted contractor, a phased approach was taken. Initial installations of timber Playtime® fencing and gates were completed in October 2022. A great performance Jacksons Fencing has installed its EuroGuard® Regular fencing and Flatform gates Jacksons Fencing has installed its EuroGuard® Regular fencing and EuroGuard® Flatform gates. Made from high-quality steel and galvanized to prevent rust and wear, these durable barriers provide long-lasting protection. The EuroGuard Regular fencing provides an unparalleled level of security while integrating with the school’s Drama Center's traditional and modern styles. Guarding creativity The EuroGuard Flatform single and double leaf gates, featuring twin wire construction and a sleek black polyester powder coating, offer secure pedestrian and vehicular access, ensuring the safety and convenience of students, staff, and visitors alike. Installation of new fencing and dedicated entrances not only protects the pupils during school hours The mesh fencing system, with its tamper-proof clips and fixings, forms an impenetrable barrier while providing visibility through to the entrance, ensuring security and surveillance. These gates serve as a testament to Chigwell School’s unwavering commitment to creating a safe and welcoming environment for all. Moreover, the installation of new fencing and dedicated entrances not only protects the pupils during school hours, but also addresses the need for security during use of the Drama Center outside of school hours and for after-hours events in the Sport and Wellness Center. Scene change With a steadfast dedication to sustainability and quality, Jacksons Fencing’s EuroGuard fencing and gates come with the assurance of a 25-year guarantee, reflecting the school's focus on sustainability and quality. These security solutions also support the school’s goal of making positive changes by using high-quality, sustainable products. Commenting on the project, Peter Jackson, Managing Director of Jacksons Fencing, said: "The meticulous planning and implementation of these security fencing and gates, in collaboration with our trusted contractor has helped set up security solutions that meet Chigwell School’s current and future needs.” He continues: “This project is about creating a place where everyone feels welcome and secure. By investing in high-quality, sustainable products, the school not only enhances security but also aligns with its values of environmental stewardship and lifelong learning.”
The airport, named after a notable historical figure, serves as a key transportation hub for both domestic and seasonal international flights in its region. Serving over 11 lakh passengers a year, it ranks as one of the busiest airports in terms of passenger and aircraft movements. The terminal building at this airport is spread over 26,936 square meters and has 14 check-in counters, four immigration counters for departures, and six immigration counters for arrivals. Located near major transportation arteries, it offers convenient access to travelers from various directions. Business scenario They required a robust video surveillance solution that could ensure 24x7 recording capabilities With a growing number of passengers and flights at the airport, a new terminal was recently constructed at this airport. To facilitate the security of passengers and staff at this terminal building, they required a robust video surveillance solution that could ensure 24x7 recording capabilities. Without adequate surveillance coverage, this airport was vulnerable to security threats such as perimeter breaches, theft, vandalism, and terrorist activities. Challenges Ensuring passenger and staff safety: Being one of the busiest airports in the state, the absence of a video surveillance system was risking the safety of passengers and staff from potential threats like theft of personal belongings or other such criminal activities. Continuous monitoring with redundancy: The airport wanted continuous 24x7 monitoring with a dual setup ensuring that surveillance operations continued uninterrupted even in the event of equipment failure or maintenance downtime. Ensuring cargo safety: The airport faced challenges in ensuring the safety and security of cargo pioneering to risks such as theft, tampering, and damage during handling and transportation processes. Regulatory non-compliance risk: Without adequate surveillance systems, the airport was facing the risk of non-compliance with security regulations, which could lead to penalties and legal liabilities. Solution The entire airport terminal was covered with Matrix Project Series Bullet, Dome, and PTZ Cameras to provide extensive coverage. Matrix Project Series Bullet IP Cameras were deployed in/at: Outdoor public spaces such as drop-off zones and walkways: To monitor crowd movements and enhance overall security. Cargo handling areas: To monitor the loading and unloading of cargo and ensure compliance with security protocols. Matrix Project Series Dome IP Cameras were deployed in/at: Main entrances and exits: To monitor the flow of passengers and detect any suspicious behavior. Check-in counters: To oversee passenger interactions and baggage handling. Baggage claim areas: To monitor baggage claim areas and prevent theft or tampering of luggage. Retail areas: Placed in retail shops and duty-free zones to deter shoplifting and ensure security for both customers and staff. Matrix PTZ Cameras were deployed at: Elevated structures overlooking runways and aprons: To provide a panoramic view enabling operators to zoom in on specific aircraft or incidents. These cameras also aided in monitoring critical infrastructure such as control towers, fueling stations, and power substations, providing close-up views for detailed inspection and surveillance. Monitoring and managing video surveillance SATATYA SAMAS - Video Management Software was deployed at two sites within the terminal Matrix SATATYA SAMAS - Video Management Software was deployed at two locations within the terminal. The first location served as a primary control center for monitoring and managing video surveillance feeds, and coordinating security responses. The second location served as a secondary control center. This could be used in case of failures or emergencies at the primary control center, ensuring the continuity of surveillance operations. Also, different users at two different locations could manage and monitor the camera streams, if needed. Products Offered SATATYA SAMAS PLT (1 No.): Enterprise Video Management Software Matrix License Dongle 200 (1 No.): USB Dongle to Run Matrix SATATYA SAMAS SATATYA SAMAS CAM20 (3 Nos.): License for Adding 20 Additional Cameras SATATYA SAMAS CAM5 (2 Nos.): License for Adding five Additional Cameras SATATYA SAMAS USER10 (1 No.): Three Concurrent User Licenses for Smart Client and Mobile Client SATATYA CIDR20MVL12CWP (52 Nos.): 2MP IR Dome Motorized Varifocal 2.8-12 mm with Audio SATATYA CIBR20MVL12CWP (14 Nos.): 2MP IR Bullet Motorized Varifocal 2.8-12 mm with Audio SATATYA PZCR20ML33CWP (9 Nos.): 2MP PTZ Camera 33x Zoom with Audio Benefits The superior image quality enabled security personnel to identify potential threats quickly Matrix IP Cameras provided full coverage at the new terminal building. The superior image quality enabled security personnel to identify potential threats quickly. The motorized varifocal lens in Matrix IP Cameras enabled zooming in for specific details when required. Matrix PTZ IP Cameras provided 360° surveillance and up to 33x zoom, providing perimeter security at the airport. Matrix IP Cameras are cyber-secure, complying with the OWASP ASVS 4.0 L2 norms, certified by STQC, Delhi. This helps in safeguarding sensitive surveillance footage, maintaining network integrity, and complying with stringent cybersecurity regulations. Matrix IP cameras are also NDAA compliant, which helped in meeting the regulatory standard requirements at the Airport. The dual setup of Matrix Video Management Software helped in providing redundancy to the surveillance system, ensuring continuous monitoring and recording even in the event of equipment failures, network disruptions, or other unforeseen circumstances. It also allowed for distributed monitoring and management capabilities, enhancing overall surveillance effectiveness. Features like Day Highlights and Time-lapse in Matrix Video Management Software aided airport security teams in leveraging intelligent search functionalities to conduct thorough investigations quickly.
The University of California San Diego (UCSD) Police Department is a full-fledged law enforcement agency responsible for patrolling, investigating, and preventing crime within its jurisdiction. Spanning over 1,200 acres and comprising 900 buildings, UCSD’s campus presents unique challenges for law enforcement. The department’s Communications Division serves as the nerve center, coordinating responses to emergencies, managing communications, and ensuring coordination among officers. Garrett Williams, a seasoned Sergeant at the University of California San Diego (UCSD) Police Department, oversees the Communications Division. With over two decades of experience, Williams understands the critical role technology can play in public safety. The challenge Before partnering with RGB Spectrum, UCSD faced significant obstacles in its dispatch operations Before partnering with RGB Spectrum, UCSD faced significant obstacles in its dispatch operations. Dispatchers juggled multiple computers, including a CAD, radio, and phone computer, each requiring separate keyboards and mice. “I didn’t look to RGB to solve all my problems. However, I understood all that could be accomplished once the team showed us how the technology operated and what was possible,” Garrett Williams, Sergeant, University of California San Diego Police Department. “Three separate mice and operators constantly moving side to side to look from one to the other and then having to move their hands back and forth between control devices - anytime they have to do that, it’s slowing their workflow down; we figured there had to be a better solution,” shared Williams. “And up to 25% of our operators were suffering from repetitive movement and neck Injuries, resulting in downtime and light duty restrictions.” Why UCSD chose XtendPoint KVM-over-IP UCSD wanted a seamless KVM solution that integrated multiple systems over IP under a unified interface. It explored various options before discovering RGB Spectrum’s XtendPoint™ solution, which provides local and remote access to source computers, consolidates separate monitors into multi-view displays, and unifies control for more streamlined operation and enhanced efficiency. With RGB’s XtendPoint KVM system, UCSD grew access to the fire alarm system at each operator’s station UCSD’s key selling point was its ergonomic benefits. It offered a solution to the ergonomic challenges plaguing dispatchers by minimizing the need for multiple keyboards and mice. So did replacing monitor clutter. With the XtendPoint solution, single-signal monitors are consolidated on each console using multiview displays that can handle up to four computer signals each or up to eight signals displayed on just two pieces of glass. A notable feature of this solution is the ability to offer each operator customized display viewing, even in a multi-shift operation. A KVM-over-IP backbone offers additional benefits. Before, only one dispatcher station could see the fire alarm system. With RGB’s XtendPoint KVM system, UCSD expanded access to the fire alarm system at each operator’s station. Now, no matter where dispatchers are seated, they have access to all needed systems. How UCSD uses RGB’s solution The RGB Spectrum solution marked a significant turning point for UCSD’s dispatch operations. Dispatchers experienced a dramatic improvement in efficiency, ergonomics, and situational awareness. Gone are the days of dispatchers juggling multiple control devices. With a unified interface, dispatchers can control all systems from a single keyboard and mouse. A streamlined workflow accelerated response times and reduced errors. Video integration proved invaluable. Dispatchers can now access live video feeds and additional mission-critical systems directly within one system interface, providing them with real-time visual information as required. With a unified interface, dispatchers can control all systems from a single keyboard and mouse Additionally, support for video integration with a video wall provided opportunities for enhanced collaboration and situational awareness. Commented Williams, “The flexibility of the RGB system also allowed UCSD dispatchers to leverage video wall capabilities. They can easily share critical information and task lists with colleagues. A more collaborative environment has facilitated communication and coordination among dispatchers, ensuring that tasks are efficiently managed and prioritized during high-stress situations. We can use the RGB system to throw things up on the wall so other dispatchers can see what’s happening and interact as needed.” “In addition," said Williams, “the resilience of the RGB XtendPoint system is invaluable in maintaining operational continuity. For example, in the event of a problem at a station, technicians can work on the issue while the dispatcher moves to a backup computer or station, allowing dispatchers to continue critical work without interruption. This proactive approach to system maintainability and resilience saves time and resources and ensures that dispatch operations remain fully functional at all times.” The result The impact of XtendPoint KVM-over-IP on UCSD’s dispatch operations has been profound. UCSD witnessed significant improvements in efficiency, ergonomics, and situational awareness. Efficiency soared as dispatchers seamlessly controlled multiple systems from a single interface. Ergonomic issues were mitigated, and dispatcher morale improved, enabling dispatchers to respond more effectively to emergencies. Future plans with RGB Spectrum Williams is enthusiastic about the wraparound monitors RGB has announced Looking ahead, UCSD sees opportunities to leverage RGB Spectrum’s technology further to enhance operations. RGB system’s versatility also enables UCSD to adapt to evolving threats and emergencies. In the event of, say, a building evacuation or siege, for example, UCSD could almost immediately establish a satellite facility. Williams is enthusiastic about the wraparound monitors RGB has announced. “We are looking at RGB’s new, yet to come to market, 43-inch curved monitors that will be the finishing touch for even better ergonomics and a customized workspace.” Another potential interest is a “flyaway” kit, a transportable command-and-control system with integral radio access. This mobile system would enable UCSD to monitor special events, such as festivals, where real-time situational awareness is crucial for ensuring the safety of attendees and staff. Williams notes, “We can have a mobile command post set up near a festival or special event, take one of our dispatch systems and put it there without having to move a lot of equipment or figuring out how to get it on the network.” Implementing RGB Spectrum’s solutions UCSD also aims to extend the reach of its dispatch operations by providing in-the-field personnel with access to real-time information. By equipping mobile units with RGB’s AV-over-IP systems via smartphones, police officers could receive critical updates and better collaborate with dispatchers to respond to incidents. “If you think of the unthinkable, like a school shooting, it would be ideal to share live coverage of what’s happening, detailed building schematics, and info on weapons the assailant might be using. Who doesn’t want to know what’s potentially happening behind closed doors before walking in? It’s situational awareness on a whole new level,” commented Williams. The partnership between the UCSD Police Department and RGB Spectrum has proven successful. By implementing RGB Spectrum’s solutions, UCSD transformed its dispatch operations to achieve unprecedented levels of efficiency, ergonomics, and situational awareness. And it is just a start.


Round table discussion
By linking human resource (HR) systems to physical security, access control systems can automatically update permissions based on employee changes, such as promotions, terminations, or department transfers. In fact, connecting HR and information technology (IT) systems to physical security can provide many significant benefits in terms of access control, incident response, compliance, cost savings, and employee experience. We asked this week’s Expert Panel Roundtable: How can organizations integrate physical security with other systems, such as IT and HR?
When it comes to protecting the environment, the security industry has historically been perched on the sidelines. For instance, the amount of electricity that physical security systems use is minimal when compared to the total energy usage in a typical building. However, as awareness of environmental issues has surged, and as some of the "low-hanging fruit" has been harvested, attention has come back to opportunities for additional, if small, savings. The lifecycles of security products are also being more closely examined, including the environmental impact of using plastics and other chemicals. We asked this week's Expert Panel Roundtable: How can the security industry contribute to protecting the environment?
There is a complex and interdependent relationship between security and productivity. Good security is needed to make productivity possible, but security measures could, in some instances, hinder workplace efficiency. New technologies are enabling security systems to have a more profound and positive impact on productivity by yielding better intelligence to guide the improvement of workplace practices. Multiple systems that work together, rather than separately, improve the productivity of security processes. We asked this week’s Expert Panel Roundtable: How can physical security systems contribute to productivity?
Products


White papers

Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Access management in higher education
Download
School Security Checklist
Download
Leveling Up With Campus Safety
Download
Smart Surveillance In The Workplace
Download
How To Ramp Up Perimeter Security With License Plate Reader Technology
Download
Thermal Cameras: Can They Accurately Detect Body Temperatures?
Download
How Plate Reader Technology Increases Your Perimeter Security
Download

Videos
Perimeter security: Manufacturers & Suppliers
- Senstar Perimeter security
- OPTEX Perimeter security
- DSC Perimeter security
- Dahua Technology Perimeter security
- eneo Perimeter security
- Climax Technology Perimeter security
- Axis Communications Perimeter security
- RISCO Group Perimeter security
- Bosch Perimeter security
- Aritech Perimeter security
- SightLogix Perimeter security