The importance of data is ever-growing. For every profession, we’re witnessing the increasing reliance on data and its ability to promote efficiency for corporate decision-makers.
The security industry is no different. The growing reliance on data and technological tools has allowed for a new breed of professionals with specialized skill sets. This evolution reflects the changing nature of security challenges in the digital age.
The new security environment
We know one thing from nearly every post-event analysis of a major security incident. Perpetrators frequently leave significant clues regarding their intentions. But identifying these risks is harder than ever. Security teams must manage greater threat data volumes through a wider range of channels.
Security teams must manage greater threat data volumes through a wider range of channels
Take the manufacturing sector, for example. Before the influx of data and technology, security teams may have been on the lookout for thieves conducting pre-operational surveillance in person at a plant. In the digital age, bad actors use social media to cooperate. In some well-organized theft rings, authorities have indicated that alleged buyers of stolen goods use apps to communicate with prospective thieves to streamline their process.
Social engineering attacks
In July 2020, hackers infiltrated Twitter's internal systems in a brazen cyberattack. Perpetrators tricked Twitter employees into revealing their login credentials via a social engineering technique called "phone spear-phishing."
They compromised over 130 high-profile accounts, including former U.S. President Barack Obama, tech mogul Elon Musk, and Microsoft co-founder Bill Gates. Once inside, they utilized the company's internal tools to gain control of the targeted accounts and posted a series of tweets promoting a Bitcoin scam. The hackers promised to double any Bitcoin sent to a specified address and ultimately stole over $120,000 from unsuspecting users. This incident highlighted the vulnerability of even the most secure platforms to social engineering attacks and underscored the importance of implementing robust cybersecurity measures.
Vast digital territories
Leaders overseeing security and risk functions must establish a diverse team
The rise of hybrid threats and the need to safeguard physical assets and vast digital territories has only expanded the concept of the company's perimeter.
Fortunately, this same digital environment that fosters an expanded threat landscape can also enable security professionals with additional tools for identifying and eliminating risks. Leaders overseeing security and risk functions must establish a diverse team with a range of backgrounds and expertise to effectively utilize security tools and uncover hidden threats. As publisher and entrepreneur Malcolm Forbes eloquently stated, "Diversity is the art of thinking independently together."
Public sector employees
Traditional threats continue to pose a significant challenge, emphasizing the ongoing value of experienced corporate security professionals, such as veterans and public sector employees. However, the emergence of contemporary asymmetric risks necessitates teams with a broader skill set.
The emergence of contemporary asymmetric risks necessitates teams with a broader skill set
The future of security demands a diverse collective of individuals drawing expertise from traditional backgrounds, such as three-letter government agencies, and non-traditional perspectives, such as data analysts. This fusion of diverse experiences and thought processes is crucial for devising holistic solutions to real-world risks.
Traditional and contemporary threats
In organizations I have been involved in, simply understanding our gaps and covering them with needed expertise was efficient in helping meld discussions about security with the language of business, which was a two-way street. Bringing on a program manager who understood the scrum framework made it far easier to align security's conversation and for security to understand the needs of its internal stakeholders.
The security landscape demands individuals who excel in data visualization, metrics analysis, and the ability to communicate security concepts in the language of business effectively. This blend of technical prowess and business acumen is essential for navigating the complexities of the modern security landscape.
By embracing diversity in their security teams, organizations can harness the collective power of independent thinkers working together to address traditional and contemporary threats. This approach will empower organizations to build resilient security teams to safeguard their valuable assets in an ever-evolving threat landscape.
Opening the door to new security talent
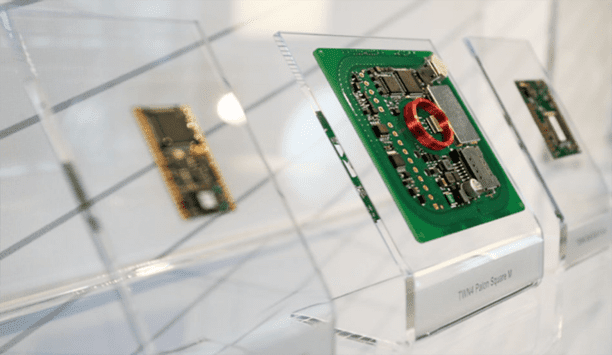
For years, technology and data have grown to play a significant role in how security operates and evolves
For years, technology and data have grown to play a significant role in how security operates and evolves. However, there remains a gap between how to effectively incorporate modern technology into legacy security programs. (There’s been some interesting research on this topic, including research out of the University of South California that identifies a lack of knowledge as a big barrier to using data and metrics by security teams.)
As we transition into 2024 and the following years, developing analytical capabilities will remain essential for implementing and executing a comprehensive security strategy. Incorporating the expertise of digital natives, individuals who have grown up amidst recent technological advancements, or those with specialized knowledge in data visualization and metrics analysis will ensure that this technology is utilized effectively, empowering teams to harness its full potential.
Proactive risk mitigation
Data analysts, for example, with their proficiency in handling large datasets, can play a pivotal role in identifying and mitigating potential security threats by analyzing network traffic patterns, user behavior, and other pertinent data points, enabling proactive risk mitigation through predictive measures.
These professionals play a critical role in translating complex security data into actionable insights
These professionals play a critical role in translating complex security data into actionable insights, measuring the effectiveness of security measures, and aligning security strategies with overarching business goals. Bringing them on board may even create a flywheel effect. When recruiting for new team members, branching out and searching for candidates with non-traditional career backgrounds will open the door for more applicants with diverse and technological skills that fit modern security needs.
Creating a holistic security program
Fusing modern skills with traditional security expertise forms a holistic approach to security. It is a strategy capable of countering threats and demonstrating the tangible value of security investments to stakeholders in our interconnected world. In the same way that many security programs have shifted toward a centralized view of threats and vulnerabilities, teams composed of leaders from diverse backgrounds with modern skills combined with legacy security leaders will allow for a more comprehensive approach to security.
This new security group will break free from the constraints of traditional methodologies and expand its capabilities to encompass a broader spectrum of risks. By combining insights from both seasoned security veterans and innovative digital natives, this team will deliver tangible value to a wider range of departments across the organization. When security can proactively provide solutions and effectively address risks that arise in all corners of the organization, it becomes the cornerstone of overall organizational safety.
Modern security approaches
This collaborative environment will empower the organization to stay ahead of the curve
Fostering a seamless interchange between traditional and modern security approaches will lay the foundation for a robust security program, where knowledge sharing among team members elevates the effectiveness of the entire program. This collaborative environment will empower the organization to stay ahead of the curve and address the ever-evolving challenges of corporate security in a rapidly changing world.
As we witness the future of security teams unfold, we will see a growing number of leaders emerge from the digital realm, bringing with them a deep understanding of risk management, emerging technologies, and data analytics. This infusion of fresh perspectives, coupled with the expertise of legacy leaders, will equip security teams to navigate the complex and ever-evolving landscape of corporate security.
In his book "Risk: A User's Guide," Stanley McChrystal observed, ‘Generals who flawlessly fought the last war typically lose the one they're actually in—because conditions have changed and they haven't.’ This is true for leaders within the risk space, too. The security leaders of tomorrow must embrace change, adapt to new realities, and harness the power of diverse perspectives to safeguard their organizations in an ever-shifting environment.
Discover how AI, biometrics, and analytics are transforming casino security