A recent IHS Markit report predicted that, by 2030, there will be 125 billion Internet-connected devices participating in the now well-known and widespread Internet of Things (IoT). Network surveillance cameras, lifestyle wearables, and smart home devices are all prime examples of IoT solutions that are capturing an unprecedented amount of information.
Now, there are more than three million data centers in the U.S. that are storing, processing and protecting this data. This data has become essential to everyday life for consumers and businesses alike. Consequently, perimeter security for data centers must be taken seriously. It is essential to execute strategies that proactively address security threats and prevent security breaches that would result in the loss of critical information.
Best practices
Here are five best practices for data center perimeter security plans:
- Deter
First, customers need to implement Crime Prevention Through Environmental Design (CPTED) strategies in order to deter physical breach attempts. This includes erecting fences and gates and using barbed wire. It also involves best practices such as planting tall shrubbery to encourage visitors to utilize better-lit and monitored passageways. CPTED strategies can even include designing winding roads, leading up to the data center, to discourage vehicles from approaching at high speeds. - Detect
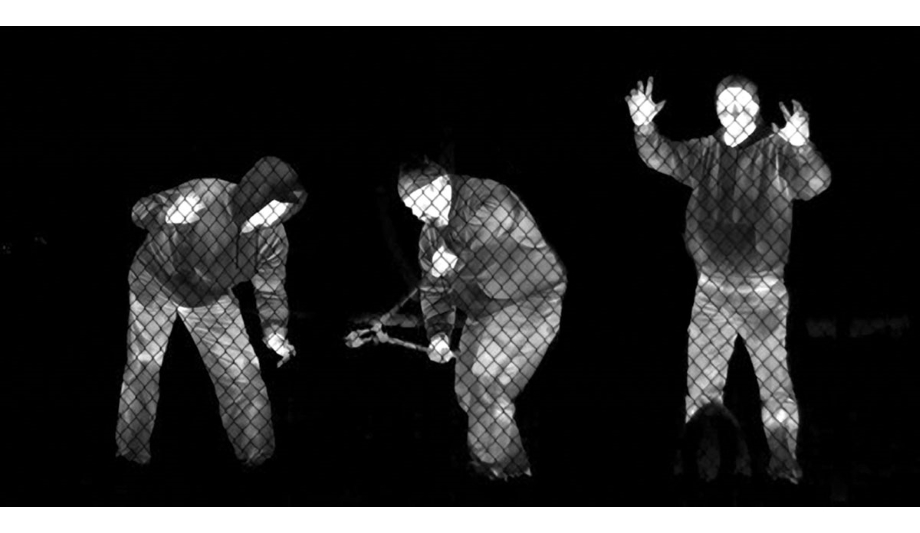
As data centers operate 24/7, customers need to deploy solutions that can monitor the premises and detect threats around the clock. First-class FLIR thermal security cameras with long detection ranges and the ability to yield high-contrast images with rich detail are optimal for data center deployments. These cameras are known for their high-performance even in adverse weather conditions, such as light rain, fog, smoke, or total darkness, that would render a standard video camera ineffective. When integrated with classification analytics, thermal cameras can distinguish between a human or vehicle. When paired with ground-based radar, customers gain redundancy and reduce the likelihood of a false positive. By deploying thermal cameras with HD visible cameras, remote operators can review thermal and visible video streams of the scene for improved alarm verification and intruder identification. - Deny
While video monitoring is one facet of data center protection, it must be complemented by access control systems to deny entry to unauthorized individuals. Deploying technologies such as video intercoms, card readers, biometric technologies, and turnstiles to reduce piggybacking help to ensure only verified employees or visitors can enter the facility. As people walk further into the facility, from escorted areas to data center rooms to the data center cabinet, identity authentication is critical. - Delay
Integrating multiple types of security technologies, from thermal to radar to access control, may necessitate higher-level management software so that operators can have a global view of all threats. With a physical security information management (PSIM) solution, operators can easily track all targets on map displays, send alerts to law enforcement, and if necessary, initiate lockdown procedures to seal off critical areas and isolate an intruder. - Defend
On a digital level, strong perimeter security plans should also account for cyber threats for edge devices. Implementing cyber-hardening technologies such as network monitoring software, end-to-end encryption between archivers and cameras via Transport Layer Security, and the elimination backdoors are a few examples.
Combining these practices to form a single, coherent, and interconnected security strategy ensures data centers are optimally protected.
Understand how converged physical and cybersecurity systems can scale protection.