Power plant security
Brigade Electronics has been honored with a King’s Award for Enterprise for international trade. Brigade is one of 252 organizations nationally to be recognized with a prestigious King’s Award for Enterprise. Announced on Monday, 6th May, 2024, Brigade Electronics has been chosen for its excellence in international trade. A total of 257 awards were made with five companies being recognized for two awards. Brigade Electronics Employing 154 people in the UK, Brigade Electronics...
Barrier1 Systems, the industry pioneer in perimeter-hardening physical security barriers, is exhibiting a variety of crash-rated vehicle barrier systems at ISC East 2023, at the Javits Center in New York City. Most notably, Barrier1 is demonstrating a selection of high-security bollards, drop arm solutions, and folding gates on the show floor, serving as a testament to its expansive range of perimeter security solutions. Security barriers “Security barriers are no longer perceived as so...
Aiphone, the international manufacturer of intercom, access control, and emergency communication products, announced it has opened a new office in the Tampa, Florida., USA, a further testament to the company's position as an industry pioneer and continued growth within the security industry. The new office marks Aiphone’s first location in the South, and fourth overall in North America. Aiphone currently has offices located in Cherry Hill, N.J., and Laval, QC. The corporate office is loca...
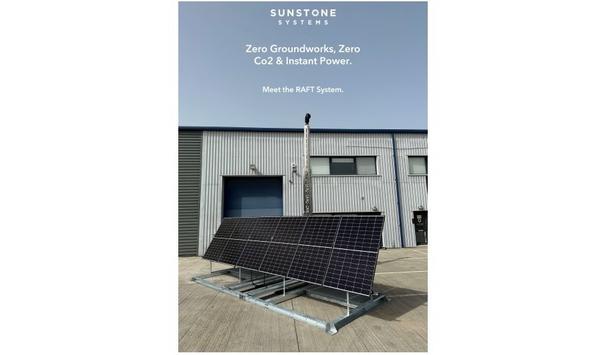
Sunstone Systems, an award-winning innovator in renewable energy and surveillance technology, is proud to announce the groundbreaking launch of the Rapid Autonomous Frontier Technology (RAFT) System. RAFT System This innovative product is set to transform the integration of smart devices, renewable power generation, and connectivity in remote and challenging environments. The RAFT System builds upon the success of Sunstone Systems' range of wireless, clean energy, remote power systems w...
In response to recent growth, Bandweaver, a company providing solutions for security, fire, power, and pipelines, is delighted to welcome Marinus de Heijde to the Bandweaver team as their new Business Development Manager who brings with him 20 years of experience in the fire safety sector. As a key member of the team, Marinus will be responsible for accelerating Bandweaver’s already impressive growth by developing and executing sales strategies and building relationships with key decision...
From 10 to 13 October, the global airport community will gather for the 24th edition of inter airport Europe at the Munich Trade Fair Centre in Germany. The event returns with an impressive line-up of well over 400 airport suppliers from 37 countries, including seven national pavilions and more than 100 new exhibitors. Live exhibits Visitors can look forward to plenty of live exhibits in the halls and Outdoor Area and a new 600 square meter GSE Experience Area. An exciting event program incl...
News
ISS (Intelligent Security Systems), a global provider of video intelligence and data awareness solutions, announced that industry veterans Dennis Connor and Jason Lloyd have joined the company as its new Director of Program Management NA and Regional Business Manager for the Midwest respectively. Dennis Connor's responsibilities Connor, who most recently served as Program/Project Manager for CX (customer experience) Initiatives at ADT, will spearhead the development of new end-user and partner deployment methodologies for ISS. He will simultaneously work with the company’s sales, engineering, manufacturing, and R&D teams to create and foster other customer engagement programs. Work experience Connor has an extensive background in similar initiatives throughout his time in the security industry, beginning in the early 2000s as Program Manager, Returns and Repairs Operations, at Tyco International. He would go on to work at the company in various leadership positions for the next 14 years, overseeing its transition from a Bermuda-domiciled organization with a U.S. headquarters in New Jersey to being a Swiss-based company. AI-powered video analytics ISS is in a tremendous position to take advantage of the third wave of video surveillance innovation" “As the preeminent developer of AI-powered video analytics globally, ISS is in a tremendous position to take advantage of the third wave of video surveillance innovation the industry currently finds itself in,” said Connor. “I have a lot of operational experience to bring to the table and ISS, in a sense, represents just a larger version of what I have gone through in the past establishing program management initiatives at other firms.” Jason Lloyd's responsibilities Lloyd, who most recently served as Regional Sales Manager at Vicon, will be responsible for driving the sales and business development efforts for ISS across the Midwest. Prior to Vicon, Lloyd headed up a low-voltage division at ADT for just over a decade. High-trust video intelligence solutions My goal is to exceed customer expectations and demonstrate how they can leverage our neural network technology" “Being laser-focused on customer service and providing high-trust video intelligence solutions that are solving actual security and business challenges today was one of the factors that most appealed to me about ISS,” said Lloyd. “My goal is to exceed customer expectations and demonstrate how they can leverage our industry-pioneering neural network technology to keep their businesses safe.” Matt comments “ISS is experiencing incredible growth, not only in North America, but globally, and bringing in experienced team members will be critical to our continued growth,” explained Matt Powell, Managing Director for North America at ISS. “With Jason, we gain a well-respected face, and voice of our partners, in the Midwest. And in Dennis, we gain an experienced program manager who will ensure that we speak the language of success to our integration partners and customers alike." Integration in the value chain The experience of both Jason and Dennis shows that we are dedicated to a new approach to the North American market" "Solution creators must strive to do a better job of speaking ‘integration’ to our integrators, pulling them into the value chain instead of pushing them out." "That begins with the relationships we build and our value propositions to our partners and customers. The experience of both Jason and Dennis show that we are dedicated to a new approach to the North American market and continued growth of ISS.” Education Connor, who has a degree in industrial engineering from Virginia Polytechnic Institute and State University and is also Six Sigma/Lean DMAIC Master Black Belt and Scrum Master certified, resides in Orlando. Lloyd, PSP, PMP, who is based in Chicago and holds Lenel Master and Genetec certifications.
The Security Industry Association (SIA) has launched a new learning management system (LMS) – SIAcademy as part of its efforts to advance industry professionalism through premier education and training. SIAcademy SIAcademy is a living library of on-demand training and professional development programs designed to enhance security professionals’ industry knowledge, technical skills, and overall job performance. The new LMS offers a modern, simple, and centralized place to access role-based training, certification prep materials, and other relevant educational content anytime, anywhere, and on any device. Dynamic learning tools It offers immense growth opportunities for those who prioritize their professional development" “The launch of the SIAcademy learning management system and course catalog is a milestone within SIA and for the security industry,” said Dr. Elli Reges, SIA’s director of learning and development. “This robust new platform offers dynamic learning tools to help learners and employers harness and unleash individual performance potential through customizable learning pathways and strategic investments in human capital, and it offers immense growth opportunity for those who prioritize their professional development.” Features of the LMS SIAcademy, powered by the cloud, delivers on-demand e-learning offerings and live online courses. Features of the new system include: Easy accessibility and a mobile-friendly interface. Interactive engagement tools and gamification. Continuing education credits. When accessing SIAcademy, members can find content such as: SIA’s Security Project Management (SPM) training. SIA’s Security Cornerstones series is designed for new employee onboarding. A microlearning series created to propel young professionals’ knowledge and growth. A training course on the federal grants life cycle and security-related grant programs. On-demand SIAcademy LIVE! courses on video security, access control, sales, and more. Materials and guidelines to help members prepare for the Security Industry Cybersecurity Certification (SICC) exam. Key learning objections SIA member companies will be able to create their customizable microsites “I think learners will be very pleased with the new capabilities of SIAcademy! It allows us to facilitate more engagement through discussion boards and other features and reinforce key learning objectives with interactive gamification tools,” said DeAndre Thornton, SIA’s manager of learning and development. Through SIAcademy’s microsite capability, which SIA plans to make available shortly, SIA member companies will be able to create their customizable microsites, on which they can build their own content and license content from SIA’s LMS to develop learning plans for their teams, partners and/or clients. SST Apprenticeship program SIA’s new Security Systems Technician (SST) Apprenticeship program, using the SIAcademy microsite capability, will provide participating employers with access to more than 100 hours of curated e-learning content. SIA members are invited to contribute educational course content that is product-agnostic and vendor-neutral to support apprentice knowledge and skill development in designated competency areas.
Dahua's latest DSS Pro V8.3 enhancement equips security personnel with advanced tools, enabling them to rapidly identify and monitor suspicious individuals' movements in just seconds. It is a cutting-edge Video Management Software (VMS) security solution designed for efficiency and scalability. It leverages users' video security systems to help them make informed decisions quickly and serves as the backbone of the operation. AcuPick Technology The key upgrades primarily focus on integrating Dahua's advanced algorithm, AcuPick Technology, which helps investigators save time in searching for and identifying people of interest. The feature also supports multiple user logins with specific permissions for up to 200 individuals simultaneously. Remote-control capability The company predicts that this upgrade will foster digital transformation across various sectors Another feature is the remote-control capability, which enables security staff to monitor and track events from anywhere, whether they are on the move or at home. The company predicts that this upgrade will foster digital transformation across various sectors and empower stakeholders from retail, residential, and other sectors to become more digital and efficient. Integrated Search Algorithm Traditional security methods demand frame-by-frame analysis of hours of video footage. With AcuPick, all searchable targets can be scanned instantly. The search algorithm breaks up people and vehicle objects into feature values that are sent to the DSS platform for processing. DSS saves these feature values to its database and finds the target object by comparing the feature values. Streamlines the user experience Even without clear details, security staff can find and track a person or vehicle of interest using a single reference image. Upon selecting a person, individuals will instantly see a history of each appearance on all AcuPick-enabled cameras throughout the premises. DSS Pro 8.3 streamlines the user experience, eliminating the need for lengthy training sessions. The process is as simple as installing AcuPick, selecting the target, viewing the desired thumbnails, and receiving video feedback instantly. Enhanced Workflow This allows users to easily see personal assignments for each door and personnel situation DSS Pro V8.3 also introduces a clearer assignment system, simplifying the entire workflow. The workflow is divided into three groups – staff assignment, safeguarding doors, and the routes connecting the two. This allows users to easily see personal assignments for each door and personnel situation. Visualized and intuitive dashboard The company has improved its user interface to offer a more visualized and intuitive dashboard. This upgraded feature provides a comprehensive overview of peak times, equipment status, and other vital information, making it easier for stakeholders to manage their security systems. Existing stakeholders enjoy these updates free of charge. While clients are required to purchase their servers for data storage, data transfer during a DSS Pro upgrade is an additional cost.
Intelligent Security Systems (ISS), a global provider of video intelligence and data awareness solutions, announced that its Managing Director for North America, Matt Powell, has been selected to speak at next month’s Securing New Ground (SNG) conference in New York City. Scheduled to take place from October 17-18 at the InterContinental Times Square, SNG conference brings together executives and entrepreneurs from across the security industry to network and share information on different technology and business trends that are affecting the market. Impact of artificial intelligence Matt’s session entitled, “What AI Means for your Business,” will examine the impact of AI Matt’s session entitled, “What AI Means for your Business,” will examine the impact of artificial intelligence on security applications and how these effects will be felt by firms throughout the industry within the next two to three years. Joining Matt on the panel will be Hamish Dobson, CVP, Product–Enterprise Physical Security Solutions, Motorola Solutions; Jumbi Edulbehram, Global Business Development, Smart Cities and Spaces, NVIDIA; and, Kurt Takahashi, CEO, Netwatch Group. AI adoption at an exponential rate “The customers that our industry serves are adopting AI at an exponential rate for all aspects of their businesses. Answering the question of how to utilize AI in a business, or how to become part of the value chain that is AI, is fast becoming the dominant conversation across every market sector,” explained Matt Powell. He adds, “Our panel draws from a cross-section of the industry, bringing incredible insights based on experience to this important topic. If I were attending and wanting to understand the most important aspects of artificial intelligence and augmented intelligence in our industry, this is a panel I would not want to miss.” ISS analytics With over three million devices running ISS analytics in 56 countries around the world Matt has over two decades of experience in security and transportation technologies and brings a lessons-learned approach to AI and advanced technology deployments. Matt joined ISS in 2022, combining his manufacturing knowledge with his integration experience to help bring the expertise of the company to the North American market. With over three million devices running ISS analytics in 56 countries around the world, ISS is the largest video analytics provider. Prior roles of Matt Matt formerly served as Principal–Transportation Markets and Principal-Infrastructure Markets at systems integrator Convergint where he set the strategy for business development and professional services that led the company from a handful of airports to 60-plus aviation deployments, including some of the world’s largest airports and airlines. He has overseen technology deployments including video management, access control, analytics, and AI, as well as developed methodologies for deployment used for complex systems, such as identity management and single pane of glass solutions. Prior to Convergint, Matt was the developer of transportation market strategies for Moog and Videolarm.
Allegion U.S., a provider of security products and solutions, unveiled the results of a new multifamily living trends survey that provides insight into the preferences and expectations of the current renters. New technologies, amenities The report, “2023 Multifamily Living Trends: A Study on What Multifamily Renters Desire, Expect and Will Pay More For in Their Residences,” analyses input from over 1,000 survey respondents who currently rent or own multifamily residences or plan to in the next two years. Beyond the value of safety, residents’ peace of mind, and the rise of mobile access control, the survey shows how COVID-19 and the influx in Proptech have accelerated the adoption of new technologies and amenities designed to enhance the lifestyles of current renters. The changing multifamily landscape Increased adoption of smart home technology, re-prioritization of amenities, and new preferences In 2019, Allegion conducted a similar study, providing a benchmark for living trends among millennial renters. Over the last four years, the multifamily landscape has changed in significant ways both for renters and property owners, alike: the increased adoption of smart home technology, re-prioritization of amenities, and new preferences in leasing and communication are evident. Impact of Proptech adoption, lifestyle changes “Multifamily has always been a dynamic market as a result of changing lifestyle behaviors and introduction of new property technologies,” said Connie Alexander, senior manager for primary research & insights at Allegion. “Our research reveals that we are witnessing the impact of Proptech adoption and lifestyle changes following the pandemic. Property owners need to take note of these shifts to best allocate short- and long-term investments in their properties that will help attract and retain quality residents.” Key trends and challenges The key trends and challenges examined in the report are outlined below: 1) Impact of Proptech on Multifamily Residences - In 2021, $24.3B was invested into Proptech companies globally, with a focus on the multifamily market. Proptech can help attract responsible, high-quality residents and provide enhanced and safer cross-property amenities, lower operating costs and increase revenue. 61% of survey respondents said they are comfortable using Proptech. Smart locks, resident portals, and cameras were included in these preferences. According to the survey results, 51% of renters who make more than $100,000 per year view smart home technology as a need-to-have amenity and 48% of those same renters view Proptech as a must-have. More than one in two respondents would be willing to pay one to 10% more for property technology and nearly three in 10 would pay at least 11% more. 2) The Rise of Mobile Access Control - With most of the population having access to smartphones the rise of mobile access control provides renters with a convenient and secure way to access different parts of their multifamily property. Over 59% of respondents would likely select a future place of residence if it had mobile access control offered as an amenity. Compared to the 2019 study, there was an 82% increase (to 34% from 19%) in the number of respondents who would be willing to pay more for mobile access control that would allow them to remotely monitor entry of their home and give access to guests and others. 3) Amenities That Attract Based on New Behaviours - COVID-19 had a profound and lasting effect on consumer behavior and lifestyles. Multifamily residents are no different. According to Pew Research, 70% of individuals will continue with the at-home habits they adopted during the pandemic. When asked about considerations for a future place of residence, respondents ranked free Wi-Fi as the most important amenity, behind affordability and proximity to work and school. Among those working remotely (15% remote, 20% hybrid work lifestyles among respondents), fast and reliable Wi-Fi is the most important factor when looking for a place of residence. Home security systems, smart home technologies, and upgraded building materials ranked more important overall than fitness centers and pools. 4) Value of Safety and Resident Peace of Mind - According to the 2021 World Risk Poll by the LP Foundation, 37% of people in the U.S. feel less safe than they did just three years ago. Fewer than one in three respondents feel secure in all areas of their home, and about one in five do not feel secure in the basement, living room, and/or patio. Up to 140% from 2019, 22% of respondents currently use electronic door locks that are connected to the internet. And up 91% from 2019, 23% of respondents currently use electronic door locks that are not connected to the internet. More than one in three respondents would be willing to pay more for smart doorbells with video, outdoor cameras, and mobile access control. Six in 10 would pay between one and 10% more per month for these added security features. Only 19% of respondents are comfortable giving their family and friends access codes or keys to their unit. However, 47% are comfortable hiding keys to their apartment around the exterior of their home in the event they get locked out. 5) Leasing Preferences That Convert - A survey released from the National Apartment Association’s Apartmentalise 2022 conference found over 60% of property managers cite creating efficient day-to-day operations as one of their top three challenges. Efficient communication with prospective and current residents can enable a positive ROI and a differentiating experience for renters that results in increased attraction and retention. 16% of respondents noted inattentive property management as a top three dealbreaker when considering a future place of residence. More than three in four respondents are at least somewhat comfortable with all four self-guided tour scenarios below, and less than 10% are either somewhat or very uncomfortable with them. Take a self-guided tour that allows users to freely explore a community. Take a self-guided tour with detailed instructions on what users can explore. Living in a community that allows potential tenants to explore the area on a self-guided tour. Taking a self-guided tour and having the ability to immediately sign a lease before leaving. According to the survey, residents with incomes of over $100,000 per year are statistically more comfortable navigating self-guided tours and signing a lease directly following. When asked how valuable different amenities were in a future residence, a streamlined resident portal app was ranked number one with 39% of respondents saying it was a must-have and 50% a nice-to-have.
Teledyne FLIR, part of Teledyne Technologies Incorporated announced the release of its new FLIR FC-Series AI, the latest model in its signature fixed camera (FC) series. The FC-Series AI is a thermal security camera with onboard AI analytics that accurately classifies humans and vehicles for early intrusion detection for perimeter protection and remote site monitoring. FC-Series AI With video analytics that combine deep neural network (DNN)- and motion-based analytics, the FC-Series AI offers industry-pioneering intrusion detection, enabling users to expand situational awareness and make better-informed decisions that increase safety and improve coordination and efficiency. Featuring a premium thermal sensor with 640 × 512 full resolution, the FC-Series AI camera creates images based on the heat emitted by humans and objects, rather than relying solely on visible light. Thermal security camera features FC-Series AI enables security operators to see and detect intruders, even in complete darkness, rain, fog, and smoke The thermal imager supports an industry-pioneering thermal sensitivity of <25 milliKelvin (mK), one of the best Noise Equivalent Temperature Difference (NETD) values on the market, enabling the sensor to outperform other thermal cameras whose visibility and detection rates decrease in adverse conditions. Offering eight, high-performance lenses ranging from an 8.6° × 6.6° to a 90° × 69° field of view, the FC-Series AI enables security operators to see and detect intruders, even in complete darkness, rain, fog, and smoke. DNN- and motion-based video analytics The FC-Series AI also combines DNN- and motion-based video analytics for reliable detection, empowering security managers to differentiate between true threats and nuisance alarms. Using FLIR’s curated library of thousands of thermal images, FLIR DNN analytics are trained to classify objects in real-world situations where humans or vehicles may be slightly obscured or challenging to identify or if an intruder attempts to deceive the system. The FC-Series AI also offers target geolocation capabilities and precise handoff to a pan-tilt-zoom device for streamlined target tracking. Perimeter protection, cybersecure solution FC-Series AI camera offers security professionals a high-performing, dependable, and cybersecure solution" “Our new FC-Series AI cameras elevate the possibilities for customers to tighten their perimeter protection strategy,” said Seetha Sasikala, Global Product Solutions Manager at Teledyne FLIR. “Combining DNN- and motion detection-based analytics, industry-pioneering thermal sensitivity, and the widest range of high-performance lenses on the market, the FC-Series AI camera offers security professionals a high-performing, dependable and cybersecure solution for intrusion detection.” NDAA-compliant, IK-10 rated device Designed to maximize the performance of new and existing multilayered physical security systems, the FC-Series AI camera tightly integrates with FLIR UVMS, as well as other third-party video management systems, and is supported by FLIR Nexus software. As an NDAA-compliant device, the FC-Series AI camera offers security professionals extensive cyber protection and peace of mind. With rugged, weatherproof IP66 and IP67 and vandal-proof IK10 ratings, the FC-Series AI provides durable housing.


Expert commentary
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realize, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionizing the overnight security business. Minimizing criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilizes a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimize the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is Remote Guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilize a combination of methods to effectively analyze potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyze the situation in real time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command center, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customized remote guarding When properly deployed, remote guarding systems are also customized to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional Security Shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A Bounty of Benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
It’s no secret that the data security sector is constantly changing. It has an annual CGR of about 12.3%. Future trends in data security Much of this has to do with the rise of cybercrime in recent years, with reports showing that cyberattacks happen as often as every 39 seconds. To combat the growing rate of cybercrime, data security has been on the rise. As we journey further into this era, it becomes evident that a spectrum of significant trends is molding the future of data security. This exploration delves into a selection of these trends, unraveling their importance and the potential implications they carry 1. AI security tools will increase Artificial Intelligence is also being used in the development of smart attacks and malware The introduction of Artificial Intelligence in the data security industry brought significant changes, especially in cybersecurity. AI has been the golden standard for face detection, natural language processing, automated threat detection, and automated security systems. Additionally, Artificial Intelligence is also being used in the development of smart attacks and malware, bypassing even the latest security protocols in data control. And as time progresses, AI security tools will flourish and dominate the scene. Let’s take a more in-depth look at three of the top AI security tools. Targeted attack analysis tool Manufacturers utilize targeted attack analysis tools to uncover targeted and stealthy attacks. Artificial Intelligence can be applied to the program’s capabilities, processes, and knowledge. For instance, Symantec launched this tool to combat the Dragon 2.0 attack in 2022. The phishing attack reprimanded multiple energy companies while trying to gain access to their operational networks. Targeted Attack Analysis Tools can analyze incidents and look for similarities from previous situations. They also help detect suspicious activities and collect all the necessary data to determine whether a specific action is malicious. Intercept X tool Results from the Intercept X Tool feature high accuracy and a low false positive rate Sophos, a British security hardware and software company, launched the Intercept X Tool. It engages a neural network that records and analyses data like a human brain. Sophos’ Intercept X Tool can extract features from a single file and perform a deep analysis. It detects malicious activities within 20 milliseconds. Plus, it’s also trained to work on bi-directional sharing and real-world feedback of threat intelligence. Results from the Intercept X Tool feature high accuracy and a low false positive rate. IBM Watson Technology IBM’s QRadar Advisor uses IBM Watson Technology, a unique AI tool for fighting cyber attacks. Artificial Intelligence can auto-investigate activities and indicators for potential exploitation or compromise. With cognitive reasoning, IBM Watson Technology can present critical insights to accelerate the response cycle. Security analysts can utilize this technology to search for threat incidents, reducing the risk of letting them fly under the radar. 2. Blockchain as a security solution It guarantees no points of failure or hackable entrances that can expose datasets inside the system Blockchain is a type of distributed ledger technology (DLT) that aims to establish trust within an untrusting ecosystem. Today it’s one of the most robust cybersecurity technologies in the industry. Blockchain utilizes a decentralized ledger system, but your team members can still gain access to transparent information in the cloud. Members can also record, pass along, and view necessary transactional data in the blockchain. The entire blockchain process maintains data integrity within the system while establishing trust among team members. It guarantees no points of failure or hackable entrances that can expose datasets inside the system. Cybersecurity, biometrics Cybersecurity primarily benefits from these features because blockchain can create a secure and robust wall between data and hackers. On top of that, blockchain ledgers can include biometrics like fingerprints and retina scans. These prevent hackers from accessing any private data. Because blockchain is decentralized, it also limits hackable data. Together with the technology’s record-keeping system, each node is provided insight into data manipulation exposing real-time cybercrime attempts. 3. Increased and widened access control Without access control, expect your company to be open to security issues, including theft, data loss, and breach of data Access control is critical in data security. More than a valuable security tool, business leaders can use access control to regulate people accessing any given resource. A company with an IT security setting can control who has the liberty to edit certain files. One of the primary goals of access control is to minimize threats or attacks to organizations and businesses to keep people and data secure. Without access control, expect your company to be open to security issues, including theft, data loss, and breach of data protection laws. Benefits The benefits of increased and widened access control include: Identifying who can access and control your data at specific time intervals. Protecting data from overwriting, accidental deletion, and malicious intent. User permissions that can be readily changed. Compliance and regulation with data privacy laws. Central management of access to data through a reporting portal or a dashboard. Multi-factor authentication Access control comes in various types and systems, so it’s critical to know the features of what you’re looking for. The most common type is multi-factor authentication or MFA. It involves multiple steps before logging in, requiring the user to enter other relevant information besides the password. Some other examples of information include biometrics, answering a security question, or entering a code sent to the user’s email address. Two-factor authentication, role-based access control Two-factor authentication further prevents unauthorized entries that can result in unnecessary data possession Two-factor authentication further prevents unauthorized entries that can result in unnecessary data possession. Another type of access control is role-based access control. In this setup, only one individual can set up access guidelines and grant permissions to specific team members within an organization. 4. Greater use of the zero-trust security model The zero-trust security model is a framework that requires every user within and outside the organization to undergo authentication, authorization, and validation. These are all essential to ensure proper security configuration before access is granted to the company’s applications and data. A zero-trust model assumes that anyone can cause data breaches and that a traditional network edge is not taken into effect. Moreover, it addresses the following modern-day challenges: Hybrid cloud environments. Security of remote workers. Ransomware threats. This framework utilizes the combination of multiple advanced technologies, including: A risk-based multi-factor authentication. Endpoint security. Identity protection. Cloud workload technology. The zero-trust model uses all these innovative tools for system identification, user verification, access consideration, and system security maintenance. Constant validation and monitoring Enforcing strict policies and compliance with data privacy laws are also essential Additionally, it also considers data encryption, email security, and asset verification before establishing connections with applications. The architecture of a zero-trust framework requires constant validation and monitoring of the users and the devices they are using. Enforcing strict policies and compliance with data privacy laws are also essential. More importantly, the zero trust architecture requires all organizations to be aware of all their available services and accounts to gain complete control of data handling and manipulation. 5. Increased privacy regulations Privacy regulations and policies guide organizations in proper data control, handling, and security. These policies guide organizations in proper data control, handling, and security. As a responsible business owner, you must comply with these regulations to avoid legal issues. With cybersecurity attacks becoming common, expect increased and stricter privacy regulations to be released in the next few years. While current policies are still taken into effect, various modifications and adjustments will occur to compete with the rising numbers of data breaches, thefts, data loss, and more. California Privacy Rights Act (CPRA) Currently, the California Privacy Rights Act (CPRA) is the most comprehensive legislation on state data privacy. It only started to take effect on January 1, 2023. The CPRA introduces the following principles: Broad individual consumer rights. Significant duties of people who need to collect sensitive and personal information. Additional definitions of data privacy and security. An individual’s duties include releasing information about data collection to concerned data subjects and proper access, correction, and deletion of information. Final thoughts 2023 is a big year for data security. Trends such as increased adoption of zero-trust policies, a greater reliance on AI security tools, and the implementation of blockchain as a security solution are all things we expect to see shortly. Staying up-to-date with these trends is important for keeping your business current and ensuring that you’re adhering to new and changing regulations. Doing so can give you an edge over the competition and keep you out of legal hot water.
Security systems represent a significant investment, yet many organizations still only use a small percentage of their physical security systems’ capabilities. That’s before we even begin to consider the different ways that the likes of video, access control, and ANPR can add additional value beyond security by serving the needs of other business functions. Whether that be to obtain additional insight, streamline compliance, or drive operational efficiencies. Consumption gap When users aren’t tapping into the full power of the solution they bought, they aren’t realizing their full return on investment. This creates a consumption gap. It’s a situation that has the potential to go in one of two very different directions. A misunderstanding of a system, its capabilities and functionality can quickly result in user dissatisfaction Left unchecked a consumption gap can create frustration for system integrators, manufacturers, and end users alike. A misunderstanding of a system, its capabilities and functionality can quickly result in user dissatisfaction. Leading to a greater likelihood that they’ll look to change or focus investment into overlapping and likely competing solutions. Customers’ security goals Addressed appropriately it can help manufacturers, system integrators, and end users to build trusted partnerships in which everybody wins. Understandably, systems integrators are primarily focused on installation—delivering reliable solutions that meet customers’ security goals to ensure their long-term success. However, engagement can go beyond deployment. Closing the consumption gap can be a strategic way to differentiate yourself from competitors. The deeper you understand your customer’s business, the better advice you’re able to offer—and the stronger the partnership you form. Why do consumption gaps exist? For customers, finding the time to learn multiple capabilities of a security system can be time-consuming. Often, taking advantage of new tools and solutions takes a backseat to the urgency of daily tasks. Often, taking advantage of new tools and solutions takes a backseat to the urgency of daily tasks There are many reasons why customers may not be taking full advantage of the features available to them in their security platform. They may feel overwhelmed by a steep learning curve after deployment and might delay diving into the additional system features. Sometimes, there might be a lack of awareness of the technology’s full capabilities, and despite a willingness to learn, there are few options for training. Often, it can simply be they are not aware of the benefits of their system or are too busy with day-to-day and urgent tasks to learn other features. Bridging the consumption gap Systems are built to deal with a wide variety of use cases and broaden market appeal, but the goal isn’t to get everyone to use all the features of every product. You want to guide your customers toward the features and functionality that best meet their needs. This could entail reducing the friction they experience in their day-to-day operations, solving unique issues related to their business, or addressing their most important challenges. Having these conversations with your customers deepens your relationship and can organically open up new revenue streams. Continuous engagement allows you to recommend other relevant products or services that they may find helpful. Customized training plan Customers can learn at their own pace and gradually expand their understanding of their system Furthermore, customers are often not able to implement all features at once. You can help by proposing a plan to gradually evolve systems and processes over time. This could include a customized training plan to get the most value from their investment. Some manufacturers are also now providing learning management tools that system integrators can pass on to their customers. Customers can learn at their own pace and gradually expand their understanding of their system in accordance with their bandwidth. This allows them to get more out of their system. Simplifying deployment With the right software partners, systems integrators can focus on solving customer problems, not reactively troubleshooting issues. Look for manufacturers who offer good support systems for integrators. This includes not only quality technical support but also configuration and training services you can build on. Look for partners that offer tools and consultation services you can use to complement your value-added services, either to spend less time on the basics or for specialized expertise on complex projects. Beyond support and services, one telling sign is the configuration interface and tools that you as an integrator will primarily interact with. Ask yourself whether the manufacturer invests in their back-end tools and their primary user interface. Is there a noticeable difference between these two interfaces in terms of look and feel? Does one feel more dated? Widening consumption gap The harder it is to implement upgrades, the more reticent customers are to make the changes If the end user interface is easy to use but changes on the back end are difficult, the resulting friction can contribute to the widening consumption gap. It can become too time-consuming or difficult to upgrade or make changes to the system. The harder it is to implement upgrades, the more reticent customers are to make the changes. Configuration should be painless. If the system has a solid graphical user interface, you’ll be able to interact with the software in a fluid and intuitive way. When the system is intuitive for both you and your customers, you spend less time on setup and training. You can invest more attention in value-added activities. Conclusion A consumption gap could be a sign that technological innovation is outpacing people's ability to implement them in their day-to-day lives. You can work with your customers to simplify the adoption of the innovations so they can more easily implement them and realize the full value of their investment. By reviewing opportunities to bridge the consumption gap for your customers, you increase the likelihood of growing and renewing your system and service contracts. You also build relationships as a trusted partner. Customers will turn to you when looking to expand their security system and proactively solve new and incipient problems.
Security beat
The trend of video customers moving to the cloud has reached a tipping point. At the same time, artificial intelligence (AI) is being adopted on a massive scale. Combining the two trends adds a higher level of value than either component individually. Merging the power of AI and the cloud is a driving force behind cloud surveillance company Eagle Eye Networks’ acquisition of Uncanny Vision, an AI and video analytics company headquartered in Bangalore, India. Expensive AI resources Cloud systems empower customers to leverage AI without having to install and program complicated and expensive hardware, in effect stripping away the barriers to entry that customers face when seeking to embrace AI. The cloud also enables customers to share expensive AI resources. One of the key components is ease of deployment – click, click and turn on the AI for any camera" Simplicity of implementation is crucial to the combined value proposition of Eagle Eye Networks and Uncanny Vision. “One of the key components is ease of deployment – click, click and turn on the AI for any camera (in a cloud system),” says Dean Drako, Eagle Eye Networks CEO. There is also a benefit of having AI systems networked, enabling 25 banks to perform facial recognition of customers from a single cloud-based system, he adds. A transition is also under way in the perception of AI. Video surveillance applications While previously it was seen as an add-on to surveillance systems, now it is seen as a very desirable feature on any system. “Centralized management of the cloud benefits the AI database,” says Drako. “In a project built around license plate recognition (LPR), for example, all the data goes up to the cloud into a single database, and the customer can get a mobile view of everything going on across the world. You can’t do that without the cloud. And AI for LPR is more accurate.” Uncanny Vision’s targeted focus on AI for video surveillance applications was one factor that attracted Eagle Eye Networks to make the acquisition, says Drako. In contrast, some other companies have embraced broader applications of video AI. Uncanny Vision also has more customers using their system in real-world applications than competitors. Finally, the acquisition will help to expand Eagle Eye Networks’ presence in the LPR market, where Uncanny Vision is especially strong. Improving business operations The 60 employees at Uncanny Vision are mostly engineers and programmers Uncanny Vision’s deep learning algorithms enable recognition, identification, and prediction, improving business operations, customer service, and site safety. Applications include smart parking, retail, smart cities, ATM monitoring, worker safety and perimeter security. The 60 employees at Uncanny Vision are mostly engineers and programmers. “These guys understand how to translate AI algorithms to run very efficiently on various types of hardware,” says Drako. “They optimize how they get the code to run so we can implement in the cloud cost-effectively. They do it at a modest cost to make it more accessible. They understand how to deploy software for high performance on low-cost hardware.” For Uncanny Vision, the new ownership provides more reach. “We have a huge channel and a huge brand,” says Drako. “They are strong technical guys who need a sales and solution channel.” Video analytics solutions Even in light of the acquisition, Eagle Eye Networks will continue to provide a selection of third-party AI and video analytics solutions to customers. Use of AI and video analytics is specific to the application and business needs of each customer. Use of AI and video analytics is specific to the application and business needs of each customer In addition to AI functionality, systems need a ‘business logic’ component that drives how that capability is integrated into a system. System needs vary widely by vertical market, and many third-party vendors are focused on a specific vertical and how AI can benefit that market. Recurring monthly revenue “Third parties can provide analytics and the business logic, which is different for a factory, an office building or for a drive-thru restaurant,” says Drako. “The market is looking for many solutions, and one company couldn’t own a majority of them.” To ensure flexibility, Eagle Eye Networks will accommodate third party solutions, deploy their own analytics, or leverage analytics embedded in cameras. For Eagle Eye Networks’ dealer and integrator customers, the expansion into AI presents a new opportunity for recurring monthly revenue (RMR) and provides greater value to customers. Drako says the impact of the acquisition will be global as AI applications grow in popularity worldwide.
The mission of the North American Electric Reliability Corporation (NERC) is to ensure the reliability of the North American bulk power system (BPS). While electric utility companies are responsible for administering the day-to-day operations of the electric grid, regulators such as NERC and the Federal Energy Regulatory Commission (FERC) are charged with the overall responsibility of ensuring reliability and security. NERC develops and enforces Reliability Standards, annually assesses seasonal and long-term reliability, monitors the bulk power system through system awareness, operates the Electricity Information Sharing and Analysis Center (E-ISAC) and educates, trains and certifies industry personnel. Normal everyday operations of the system are the responsibility of utility owners and operators. Protecting critical infrastructure An attack by a disgruntled former employee, ideologically motivated activist, or a criminal could inflict significant damage Currently, a significant reliability threat to the U.S. grid is associated with squirrels and balloons, and not religiously inspired terrorists. However – and more applicable to grid operators – we have recently seen noteworthy interest in disabling or destroying critical infrastructure. Coordinated attacks can target the grid, and an attack by a disgruntled former employee, ideologically motivated activist, or a criminal stumbling across a “soft target,” could inflict significant damage. With an interconnected grid of over 450,000 miles of high voltage transmission lines (100 kV and higher) and over 55,000 substations (100 kV and larger), the targets of opportunity are endless. Data capture form to appear here! According to the Department of Energy, the number-one cause of most power outages in the U.S. is bad weather, which costs the economy between $18 billion and $33 billion every year in lost output and wages, spoiled inventory, delayed production and damage to grid infrastructure. The number-one cause of most power outages in the U.S. is bad weather, which costs the economy between $18 billion and $33 billion every year Large power transformers A large power transformer (LPT) is an enormous, custom-built piece of equipment tailored to customers’ specifications. They usually are not interchangeable with each other, and they are not produced for spare-part inventories; so if one blows, a lot of companies and homes could be without power for more than six months. They are not cheap, either. According to EEP (Electrical Engineering Portal), $10 million is a fairly average cost, but that doesn’t include transporting the gargantuan piece of equipment or installing it, which usually adds an additional 35 percent to the bill. Protecting power grids is essential to deliver electricity that serves millions of consumers. Transmission substations are a component of the power infrastructure that presents unique security challenges. These important facilities often sit out in the open, in remote locations, and were historically protected by little more than cameras or chain-link fences. According to EEP, $10 million is a fairly average cost for a large power transformer NERC/CIP guidelines The North American Electric Reliability Corporation’s Critical Infrastructure Protection (NERC/CIP) guidelines address security needs of electrical substations. Every facility has a baseline requirement for perimeter security protection around the site, although medium- and high-impact sites will have more stringent requirements. The geography surrounding sites – Is it an urban area or rural? Does the surrounding elevation provide additional lines of sight? – also impacts the types of systems they require. Electricity coming from coal, nuclear or hydroelectric plants goes to local utilities The U.S. power grid is divided into three sections: The Eastern Interconnection for states east of the Rocky Mountains, The Western Interconnection for states from the Pacific Ocean to the Rocky Mountains, and the smallest—the Texas Interconnected system—covering most of Texas. Electricity coming from coal, nuclear or hydroelectric plants goes to local utilities and they distribute power to homes and businesses, to millions of personal devices, lights, refrigeration, computers, and to other “loads,” that tap it. Inherited challenges According to the American Society of Civil Engineers (ASCE), the nation’s electric infrastructure is “nothing but a patchwork system” that has evolved wildly since the first substation was erected by Thomas Edison in 1882, on New York City’s Pearl Street. Contributing to the challenges of securing the grid are the crazily disparate ages and capacities of the grid’s equipment. There are many possible targets, too. Approximately 300 control centers around the country monitor voltage and watch the data from SCADA (supervisory control and data acquisition) systems, which are placed at transformers, generators and other critical areas. Ideally, this allows engineers to monitor the data for signs of trouble and then communicate with each other to deal with whatever is happening to the grid, but SCADA has cybersecurity issues.
Unmanned aerial vehicles (UAVs), or drones, present a range of threats, from the careless and clueless to the criminal. While many incidents may seem harmless, the threat to any location at any time depends on a range of factors. Drones are inexpensive for criminals to buy or make, and there are continuously improving battery, airspeed, and payload capabilities. UAVs can also fly without an RF signal to jam or hack. Fortunately, sensor technologies including radar are available for security agencies and personnel to protect assets and the public. Radio-Wave Signals Radar works as a deterrent by sending out a radio-wave signal using a transmitter antenna, and a small portion of that signal reflects off objects in its path and returns to a receiver antenna. The highest performing radars use an antenna technology called Active Electronically Scanning Array (AESA), which enables all-electronic reconfiguration of the antennas. When an AESA radar detects an object, it can ‘focus’ its antennas to track the object, in much the same way as the zoom on a camera does. Multiple objects can be tracked while continuing to scan. Kirkland, WA-based Echodyne offers a radar product that brings these ESA capabilities to non-military security applications at commercial price points. Combining proprietary hardware with intelligent software, Echodyne produces a compact, solid-state, electronically scanning array Echodyne’s ESA Radar Echodyne says they are reinventing radar price-performance for security applications in the ground (people, vehicles) or air (counter-UAS) domains. Combining proprietary hardware with intelligent software, Echodyne produces a compact, solid-state, electronically scanning array (ESA) radar that is affordable for commercial, law enforcement, and governmental customers. The company is backed by high profile investors, including Bill Gates, Madrona Venture Group, Vulcan Capital, NEA, and Lux Capital. “Radar is a sensor,” says Leo McCloskey, Echodyne VP Marketing. “It is most applicable when security professionals can both understand its capabilities and define risk assessment and deployment requirements that call for those capabilities. Our customers are primarily security system integrators and consultancies, which integrate the performance of radar into a sensor array that meets mission requirements.” Radar Technology For Border Surveillance Echodyne was selected by the Science and Technology Directorate of the Department of Homeland Security (DHS) for its Silicon Valley Innovation Program (SVIP) to demonstrate the performance of its radar technology for border surveillance applications. The radar was deployed both in fixed remote surveillance towers and as a lightweight rapid deployment kit for field agents. Able to surveil ground and air domains, the radar combines versatility and commercial price with surveillance capabilities. “We set out to build the world’s best compact, solid-state ESA radar sensor, and we are demonstrating that we’ve reached that objective,” says McCloskey. “We’re excited to introduce these capabilities for other security applications.” Able to surveil ground and air domains, the radar combines versatility and commercial price with surveillance capabilities MESA Technology Echodyne’s proprietary technology provides a small true electronically scanning array (ESA) radar. Unlike expensive Active ESA (AESA) phased array radars, MESA requires no physical phase shifters, thus reducing the cost, size, weight, and power by several orders of magnitude while maintaining all the benefits of fast ESA radar. Echodyne combines its MESA technology with an intelligent software suite, Acuity, to produce a configurable, software-defined radar for commercial, law enforcement, and governmental security applications. The capability is also useful for temporary events such as rallies and marathons, and many other market applications “Technology seems to make everything more available to more people over time,” says McCloskey. “What is a retail product today will be a purchased self-assembly kit tomorrow and an improvised self-made drone the following day. The Federal Aviation Administration (FAA) is diligently at work on creating rules for safe UAV operation, though any final rules remain some distance off. As drone volumes increase, delineating friend from foe in the airspace requires clear legal and regulatory frameworks, which are nascent but would help distinguish the threat of nuisance flyers from illegal overflight.” Radar Sensor For Security Applications “Detecting and tracking airspace objects of interest is imperative for airports, chemical plants, oil and gas installations, refineries, water and energy utilities, stadiums and other public spaces”, says McCloskey. The capability is also useful for temporary events such as rallies and marathons, and many other market applications. “As with any product, our applicability will depend on variables like location, terrain, risk assessment, and existing security technologies,” says McCloskey. “Our mission is to deliver the very best radar sensor for security applications.”
Case studies
Alarming increases in vehicle thefts, unsolved traffic collisions, and stolen cargo in the Mexican State of Tlaxcala, motivated the Executive Commission of the State Public Security System (CESESP) to expand and upgrade its video security system. To counter the rise in crime, the CESESP sought a flexible, scalable, open-platform video management system (VMS) that could seamlessly incorporate existing cameras as well as over 800 new cameras and edge devices from a range of hardware and software providers. Tlaxcala Located in East-Central Mexico, Tlaxcala is one of 32 states within the Federal Entities of Mexico. With a population of approximately 1,343,000, based on the 2020 census, Tlaxcala is the smallest yet one of the most densely populated states in Mexico. The CESESP of Tlaxcala is tasked with safeguarding residents across the state's 60 municipalities. C4 center C4 center has multiple teams of six security professionals who monitor the system around the clock At the core of all security operations, including the 911 emergency response and 089 confidential tip line, is the CESESP's Control, Command, Communications, and Computing Center (C4). The state’s C4 center has multiple teams of six security professionals who monitor the system around the clock on a large, 24-screen video wall. The C4 also houses the system’s HP and Lenovo servers. Flexibility, scalability, and budget “Flexibility, scalability, and strictly adhering to the budget were top requirements for this critical, state-wide project,” said Maximino Hernández Pulido, Executive Commissioner of the State Public Security System. “We considered a variety of proposals and providers, but we ultimately followed the advice of our integrator, Digital Information Systems, and selected XProtect Corporate from Milestone Systems.” XProtect Corporate The new system includes cameras from Hanwha Vision, Bosch Security and Safety Systems, Hikvision, and Pelco The new system includes cameras from Hanwha Vision, Bosch Security and Safety Systems, Hikvision, and Pelco, all integrated within the system and managed by XProtect Corporate VMS from Milestone Systems. The system is also fully integrated with the BriefCam Video Analytics Platform, delivering video intelligence for system managers to identify, monitor, investigate, and visualize incidents plus video data to make smarter decisions. Efficient and cost-effective integration “Because state officials rely on their video system 24/7, the update needed to be gradual with no downtime. As new cameras were integrated into the Milestone platform, the previous system slowly disappeared,” said Isaac Sánchez Morales, an engineer at Digital Information Systems (SDI), an integrating company. “The XProtect Corporate open platform VMS allowed us to leverage our existing cameras and servers, integrate new equipment and devices, making the process very efficient and cost-effective, and we never had a gap in service.” Data-driven video for fast response times BriefCam video analytics technology The solution detects, identifies, and classifies video metadata to drive more efficient investigations The BriefCam video analytics technology seamlessly integrates into Milestone’s XProtect Smart Client. The solution detects, identifies, and classifies video metadata to drive more efficient investigations and business decisions, such as finding missing persons, investigating vandalism, theft, assaults, accidents, injuries, or acts of violence, as well as extracting and analyzing through heatmaps, dashboards, and visualizations. The analytics have proven beneficial in accelerating investigations, attaining situational awareness, and optimizing operational intelligence for enhanced video search, alerting, and data visualization. Real-time alerts, situational awareness “We installed the BriefCam Insights and Investigator products, and regularly use the platform’s RESPOND and RESEARCH capabilities. One of the advantages of all these XProtect-integrated analytics is that operators do not have to open additional windows or enter new credentials to access them,” said Sánchez. “With this integration of technologies, operators can trigger real-time alerts based on complex object classifications and filter combinations to increase situational awareness meaning authorities can react to events as they unfold.” Proactive policing with LPR With the BriefCam RESPOND solution, object characteristics and license plate recognition tools can be used" Sánchez added, "With the BriefCam RESPOND solution, object characteristics such as vehicle, person, or animal, and license plate recognition tools can be used to trigger rule-based alerts." "These tools can help overcome the challenges of urban video surveillance and drive proactive policing in Tlaxcala." Video technologies reduce state crime rates Following the comprehensive expansion of the security infrastructure, statistics from the Executive Secretariat of the National Public Security Systems revealed Tlaxcala boasted the lowest crime rate nationwide. With the modernized system in place, officials documented a 93% reduction in pilfered freight from transport companies. Similarly, vehicle theft declined by 22.5%. A cost-efficient and flexible way Milestone Interconnect provides a cost-efficient and flexible way to gain central surveillance According to Sánchez and the SDI team, it is expected that each municipality within the territory will soon have its own locally focused VMS. With the use of Milestone Interconnect, all the municipality subsystems will integrate directly with the state-wide platform. Milestone Interconnect provides a cost-efficient and flexible way to gain central surveillance of multiple sites spread across a region. C4 video surveillance operation “The integrated solution delivered through Milestone is a robust, efficient, and secure system that provides all the necessary tools for the C4 video surveillance operation,” added Executive Commissioner Hernández-Pulido. “In addition, the excellent technical and post-sales support from Milestone and SDI has led us to meet the system and performance goals we set for ourselves.”
Ipsotek, an Eviden Business at Atos Group, has announced that it was appointed to provide its AI video analytics technology at the soon-to-be-opened new Midfield Terminal Building at Abu Dhabi International Airport, in Abu Dhabi, UAE. Delivered in partnership with Atlas Security, deployment of Ipsotek’s AI video analytics solutions is anticipated to improve operations, security, and safety across various areas of the Midfield Terminal Building, which is renowned for its iconic architecture and recently gained international attention as a filming location for Mission: Impossible - Dead Reckoning Part One. Advanced surveillance capabilities Ipsotek's AI video analytics technology is well-equipped to address these circumstances Safety and security are clearly paramount in any airport environment, and Ipsotek's AI video analytics technology is well-equipped to address these concerns. The advanced surveillance capabilities of the solution enable operators to detect and identify potential threats across various zones of the airport. By leveraging intelligent algorithms and machine learning, the system can recognize suspicious behaviors, unauthorized access attempts, or other pre-defined security risks in real-time, allowing for swift response and mitigation. Ipsotek's AI video analytics By leveraging Ipsotek's cutting-edge video analytics solutions, the airport aims to enhance its security measures by effectively detecting abandoned baggage scenarios. Security teams at the airport will be able to quickly identify and respond to any unattended baggage, reducing potential security risks and ensuring a safe environment for passengers and staff. "The deployment of Ipsotek's AI video analytics solutions at the Midfield Terminal Building signifies a significant leap forward for the aviation industry," said Sophiene Marzouk, Ipsotek’s UAE Country Manager. Sophiene Marzouk adds, "We are proud to collaborate with Atlas Security to deliver state-of-the-art technology that enhances operations, security, and safety in one of the world's most iconic airport buildings." Ipsotek's solutions Ipsotek's solutions also play a crucial role in optimizing que management and crowd control “Atlas Security aspires to implement the best technology for security systems in airports and we therefore look to partner with companies bringing innovation in security applications with Artificial Analytics. One company that brings this cutting-edge technology is Ipsotek and Atlas Security is proud to work in the Midfield Terminal Building with Ipsotek,” said Khizer Rehman, Project and Technical Manager at Atlas Security. Ipsotek's solutions will also play a crucial role in optimizing que management and crowd control throughout the airport. By analyzing video feeds, the software can determine que lengths and alert airport staff to potential bottlenecks. New standards for excellence The intelligent system will empower operators to proactively manage queues, allocate resources effectively, and ensure a smooth flow of passengers. As travelers eagerly anticipate the unveiling of the Midfield Terminal Building, the deployment of Ipsotek's AI video analytics solutions is set to improve the airport experience, from safety to security and operations setting new standards for excellence in the aviation industry and turning an impossible mission into a successful deployment.
In a mountain area in Yunnan Province (China), Dahua Technology safeguards the safe production of a 700+ mu photovoltaic power station, providing intelligent fire prevention and control measures in its vast facilities. The implemented solution significantly increased the accuracy of fire alarms by more than 10 times, as well as the efficiency of fire alarm response by 30%, which help ensure the stable delivery of clean energy to its surrounding areas. Superior Lighting Conditions The advantageous location of the power station provides superior lighting conditions that yield abundant solar energy generation. Covering an area of over 700 acres, the photovoltaic power station produces over 30 million kWh of green electricity annually for its surrounding area. It is equivalent to saving about 370,000 tons of standard coal and reducing carbon dioxide emissions by over 900,000 tons. Pain Point 1: Long Inspection Time During the fire season in summer, the photovoltaic system areas must also be checked regularly During the first few years of its operation, the power station was only manned by 5 people working deep in the mountain. These hardworking personnel were responsible for the stable operation of more than 30 photovoltaic arrays. Their daily tasks include inspecting the main transformer, GIS, switch room, station transformer, SVG room, and other equipment areas of the power plant, with each inspection usually taking 2-3 hours. During the fire season in summer, the photovoltaic system areas must also be checked regularly. Two inspectors must work at least 5-6 hours a day under the hot sun, taking at least one month to complete the comprehensive inspection. Pain Point 2: Mountainous Terrain The distance between these photovoltaic system areas from the power station is generally dozens of kilometers. It can be reached by driving, but some areas are located on steep hillsides. If the car can't reach them, people can only walk or climb to get there. Even if every area is inspected, potential hazards may not be accurately identified due to the inaccuracy of the previous manual monitoring method. Pain Point 3: Manual Monitoring For fire alarms, the location of the fire point is found based on the understanding of the terrain In the past, local villagers serve as important fire "informants", especially in the photovoltaic system in remote areas. When a fire is found, the villagers immediately notify the personnel on duty. The staff then reports to the centralized control center first and cooperates with the forest fire personnel to deal with the fire. For fire alarms, the location of the fire point is found based on the understanding of the terrain. The information flow, instructions delay, and manual positioning of the fire point drastically extend the response time. 24/7 Remote Fire Safety Inspection & Monitoring The fire prevention of photovoltaic power stations requires attention to several aspects, including identifying whether it is a fire in the surrounding forest or a fire on the equipment itself. Failure to accurately detect and respond to this fire emergencies can cause severe damages and loss. Robust system The plant inspection that usually takes 1 month can be completed in less than 10 minutes" Dahua has integrated technology with the inspection mode of the photovoltaic power station to create a robust system that can monitor the fire situation in the power plant and its surrounding areas 24/7 and eliminate unnecessary journeys between mountains during the inspection. The dual-lens cameras installed at high points were configured with cruising paths, enabling them to conduct uninterrupted online inspections of the power plant and display the images through the system. “The plant inspection that usually takes 1 month can be completed in less than 10 minutes. I couldn't even think that it was possible before,” said Mr. Cai, inspector at the power station. Inspection process During the inspection process, algorithms are used to determine whether there is smoke or fire in each area. When a fire is detected, the system will locate the fire source within a range of 3-5 kilometers and find the fire point within 30-50 meters. Improved Fire Response Efficiency By 30% According to Mr. Cai, in addition to eliminating the need for further inspections, improving the efficiency of the overall handling process is another key advantage of this solution. Through integrated communication, the previous reporting and communication methods have been transformed into multi-party terminal equipment discussions. Based on on-site audio and video data, multiple parties can easily communicate and discuss plans and strategies. Real-time information At present, the timely rate of fire alarms in the power plant has increased by over 10 times At the same time, fire alarm information and the fire point location determined by the platform will be sent to relevant personnel in real-time, allowing them to accurately and quickly reach the corresponding location to distinguish the fire. At present, the timely rate of fire alarms in the power plant has increased by over 10 times, and the efficiency of fire alarm response has improved by 30%. Intelligent fire safety solution Fire safety is crucial for production enterprises, especially for photovoltaic power stations. With the advent of technology and innovation, Dahua’s intelligent fire safety solution not only can help protect the power plants and their staff, but also can ensure that thousands of households are provided with green, environmentally friendly, and low-carbon electricity.
The Pearl-Qatar is an artificial island located off the coast of Doha, Qatar, and is known for its luxurious residential apartments, villas, and high-end retail shops. Tower 11 is the only residential tower within its parcel and has the longest driveway that leads to the building. The tower is a testament to modern architecture and offers residents exquisite living spaces with stunning views of the Arabian Gulf and the surrounding area. Tower 11 features an array of amenities including a fitness center, swimming pool, jacuzzi, and 24-hour security. The tower also benefits from its prime location, which allows residents easy access to the island's many dining, entertainment, and shopping attractions. The tower's luxurious apartments are available in a variety of sizes and configurations to meet the diverse needs and tastes of its residents. Upgrade to a newer system This outdated system is no longer efficient for meeting the needs of the residents or users of the facility Tower 11 was completed in 2012. The building has been utilizing an old intercom system for years, and as technology has advanced, this outdated system is no longer efficient for meeting the needs of the residents or users of the facility. Due to wear and tear, the system has been prone to occasional malfunctions, which have resulted in delays and frustrations when entering the building or communicating with other residents. As a result, an upgrade to a newer system would not only ensure reliability and enhance the user experience, but it would also provide added security to the building by allowing for better monitoring of who enters and leaves the premises. The solution Whereas 2-wire systems only facilitate calls between two points, IP platforms connect all intercom units and allow communication across the network. Transitioning to IP provides safety, security, and convenience benefits far beyond basic point-to-point calling. However re-cabling for an all-new network would require substantial time, budget, and labor. Rather than replacing cabling to upgrade intercoms, the 2-wire-IP intercom system can leverage current wiring to modernize infrastructure at a lower cost. This optimizes initial investments while transforming capabilities. DNAKE's 2-wire-IP intercom system was chosen as the replacement for the previous intercom setup, providing an advanced communication platform for 166 apartments. At the concierge service center, the IP door station 902D-B9 acts as a smart security and communication hub for residents or tenants with benefits for door control, monitoring, management, elevator control connectivity, and more. User-friendly interface Residents can answer the call, grant access to visitors, and unlock doors using the unlock button The 7-inch indoor monitor (2-wire version), 290M-S8, was installed in every apartment to enable video communication, unlock doors, view video surveillance, and even trigger emergency alerts at the touch of the screen. For communication, a visitor at the concierge service center initiates a call by pressing the call button on the door station. The indoor monitor rings to alert residents about incoming calls. Residents can answer the call, grant access to visitors, and unlock doors using the unlock button. The indoor monitor can incorporate an intercom function, IP camera display, and emergency notification features accessible all through its user-friendly interface. The benefits DNAKE 2-wire-IP intercom system offers features far beyond just fostering direct calls between two intercom devices. Door control, emergency notification, and security camera integration provide value-added benefits for safety, security, and convenience. Other benefits of using the DNAKE 2-wire-IP intercom system include: Easy installation: It's simple to set up with the existing 2-wire cabling, which reduces complexity and costs for installation in both new construction and retrofit applications. Integration with other devices: The intercom system can integrate with other security systems, such as IP cameras or smart home sensors, to manage home security. Remote access: Remote control of the intercom system is ideal for managing property access and visitors. Cost-effective: The 2-wire-IP intercom solution is affordable and allows users to experience modern technology without infrastructure transformation. Scalability: The system can easily be expanded to accommodate new entry points or additional capabilities. New door stations, indoor monitors, or other devices can be added without rewiring, allowing the system to upgrade over time.
Residents at Chapel View can receive and answer door entry requests via mobile while granting temporary access using QR codes, due to Comelit-PAC’s dedicated mobile app and use of the latest security technology. Chapel View Set in the quaint village of Gildersome in Leeds, Chapel View is an exclusive housing development, presenting seven residential homes in a discreet cul-de-sac, all secured with a communal gate. The community featured a legacy door entry system that required an upgrade to ensure the security of residents. Comelit-PAC worked with local installation specialists AC Secure from the initial design process, through the works programme to project completion. Door entry Each house has its licence and users can use the feature-rich Comelit app to control the gate Door entry, via Comelit-PAC’s VIP system, was specified, utilizing its stylish Ultra door entry solution, to enable control of the gate to the housing estate. Each house has its license and users can use the feature-rich Comelit app to control the gate while also creating QR codes to allow temporary access for visitors. Says David of the resident’s association of Chapel View, “With high expectations for our residents to deliver ultimate security, every element of the new door entry system also had to be considered from a convenience perspective, to enable them to answer door entry requests remotely, from their smartphone." Additional benefits “AC Secure worked with us right from the specification process and took the time to understand these requirements, before recommending Comelit-PAC as an ideal solution." "The additional benefits of utilizing app technology to present door entry and QR codes for temporary access to visitors immediately appealed. And the system was installed with minimal disruption and a great benefit to our community." Smart home security systems Adam Cousens, Managing Director at AC Secure added, “Chapel View has the look and feel of a quaint village community where security and door entry is a high priority. All the smart home security systems had to be stylish and futureproof to suit the requirements of the community, whilst also ensuring ease of installation and simple use." “Comelit-PAC’s Ultra system with VIP technology, coordinating with its dedicated app was the natural choice for door entry." Ultra digital entrance panel The system enables new residents to grant access through the vehicle gates using Comelit’s dedicated mobile app "Residents love the sleek design and the VIP technology is easy to use and allows them the convenience to receive calls and see visitors from anywhere. The combination has truly elevated the door entry experience.” The entrance to Chapel View has been enhanced with Comelit-PAC’s stylish, flush-mounted Ultra digital entrance panel. The system enables new residents to grant access through the vehicle gates using Comelit’s dedicated mobile app. Mobile-first solution Stephen Wragg, Business Development Manager for Comelit-PAC concluded, "What our work with AC Secure at Chapel View demonstrates is how Comelit-PAC is ‘with you always.” There is no project too big or too small for us to work with our installers and partners to provide smart, yet stylish door entry solutions for residents to benefit from the latest in smart access control." "Ultra, together with VIP presents a powerful mobile-first solution that can ensure the ultimate security for this residential community.”
More than 2,000 innovative Safetyflex anti-terrorist bollards have now been installed in the heart of Melbourne, Australia, as part of a local government scheme launched in response to a fatal vehicle attack. Coventry-based Safetyflex Barriers has installed its spring steel bollard system across the Melbourne Central Business District (CBD) with the help of its Australian distributer, Ezi Security Systems. Most prominent pedestrian The city was rocked by a vehicle attack in January 2017 when a car was deliberately driven into pedestrians along Bourke Street, killing six people and leaving 27 seriously injured. In the aftermath, a AUS$52.5 million security upgrade at Melbourne's busiest and most prominent pedestrian sites was commissioned by The City of Melbourne, with hostile vehicle mitigation predominantly featuring Safetyflex’s advanced spring steel bollards. More than 2,000 of the slimline bollards have now been installed across key sites within the CBD, in addition to further sites in Australia, helping to keep high-risk crowded places safe from the threat of vehicle attacks. Anti-terrorist bollard system The unique thing about our bollards is they only require shallow foundations around 200mm deep" Marcus Gerrard, Director at Safetyflex Barriers, said: “Our patented anti-terrorist bollard system has been game-changing, providing unprecedented crash test certified performance in an attractive, slimline design. We are the only company in the world to use this type of technology in anti-terrorist bollards and crash rated street furniture.” He adds, “The unique thing about our bollards is they only require shallow foundations around 200mm deep, which is key in helping cities such as Melbourne navigate around in-ground obstructions, while still providing high-level security systems. The installation of the 2,000th spring steel bollard is of great satisfaction and pride, and reflects our strong experience and expertise in securing busy cities and centers worldwide. Our bollards will help ensure the safety of residents and visitors to Melbourne and Australia for years to come.” Stopping vehicle attacks The spring steel technology means the bollards can be installed in fixed, removable or retractable versions, while the elegant stainless-streel shrouds are also fitted with reflective bands to provide night-time visibility. The bollards have already proved their worth in stopping vehicle attacks, when in 2021 a stolen car fleeing police in Melbourne CBD was halted in its tracks by a Safetyflex bollard before the drivers could inflict any damage. Pedestrians were able to retreat to the protection offered by the line of Safetyflex bollards, ensuring nobody was hurt. Safetyflex has now become one of the biggest suppliers of anti-terrorist bollards in Australia, protecting high-profile locations in Brisbane, Melbourne and Sydney from the threat of vehicle attacks.


Round table discussion
Headlines of violence in our schools are a reminder of the need to keep educational institutions safe. In fact, if there is a positive aspect to the constant bombardment of headlines, it is that it keeps our attention perpetually focused on how to improve school security. But what is the role of physical security systems? As the new school year begins, we asked this week’s Expert Panel Roundtable: Are schools safer because of physical security systems? Why or why not?
As physical security technologies become more complex, it is incumbent on the dealer/integrator to have the skills and expertise needed to ensure that a system operates smoothly. The value of integrators increasingly rests on the skill sets they bring to bear when installing a system. If the skills are missing, there is a problem. We asked this week’s Expert Panel Roundtable: What missing skills among security integrators can cause problems for customers?
Driving the smart homes market is the convenience of simple technology solutions. Almost every home now has a “smart speaker” that makes it easier than ever for homeowners to interface and control their technology. But where does security fit into the new landscape of smart home systems? We asked this week’s Expert Panel Roundtable: What’s new in smart homes and residential security systems?