Biometric Security
HOLOWITS successfully held the Autumn 2024 New Product Launch on September 20, 2024, in Shanghai. At the event, HOLOWITS showcased various kinds of cutting-edge products as well as innovative security solutions, drawing the attention of numerous industry pioneers and partners. Embracing Al in security Under the theme Embracing AI era of Security Industry, Neko Wong, Marketing Director of HOLOWITS, led the event and presented the latest advancements in AIoT technology. During the presentation...
Highly satisfied visitors, a significant 25 percent increase in exhibitors, and countless successful discussions at the trade fair stand: After four intensive days, the pioneering trade fair for the security industry, Security Essen, has come to a successful close. With more than 500 exhibitors from 36 nations and over 20,000 trade visitors - an increase of 17 percent - from 86 nations, the trade fair offered a comprehensive platform for innovations and future trends relating to secur...
ASSA ABLOY Opening Solutions returns to Global Security Exchange (GSX) for 2024's powerhouse get-together of security professionals from around the world. Digital access control Attendees can visit the ASSA ABLOY booth 1434 from September 23-25 at the Orange County Convention Center in Orlando, Florida. The company will showcase its latest innovations in comprehensive door security and digital access control, featuring products and solutions to protect lives, assets, data, and more. Fu...
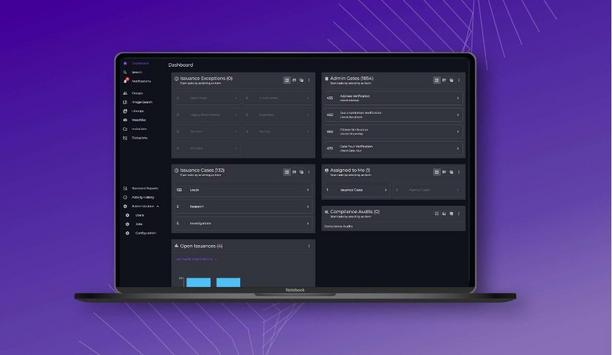
IDEMIA Public Security North America, the provider of convenient and trusted biometric-based solutions, has launched its newest product, ID2Issuance, a cloud native credential issuance and management system that Motor Vehicle Agencies can use to quickly validate applicants’ photos and signatures, perform one-to-many (1:N) facial and fingerprint biometric matching, and document management for driver licenses and/or ID cards, all while keeping individuals’ Personal Identifiable Informa...
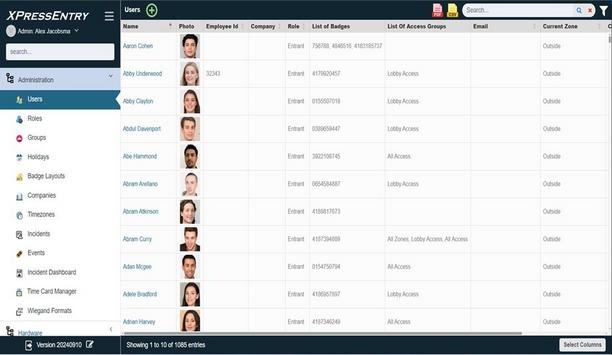
Telaeris, Inc., a global pioneer of handheld solutions for Physical Access Control Systems (PACS), announces its next-generation XPressEntry Admin Console at GSX 2024 (Global Security Exchange). New admin console The new admin console provides physical security and safety professionals a more efficient, web-accessible platform for managing XPressEntry including handheld badge verification, emergency mustering, events & training, biometric verification, entry/exit tracking, and much more.&n...
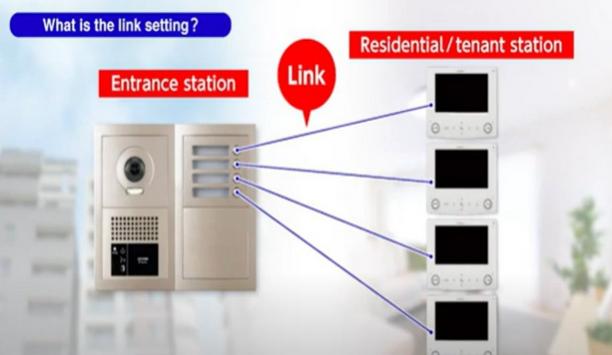
Hikvision, a major manufacturer and supplier of security products and solutions that deliver the ideal combination of high performance and extreme value is excited to announce the release of the DS-KIS600 Intercom Kit, designed to deliver advanced home security in a compact package. Two-way communication Featuring the DS-KV6113-WPE1 door station, this kit offers crystal-clear two-way communication with a noise-reducing microphone, perfect for narrow door frames. With the Hik-Connect App, home...
News
Matrix is gearing up for its participation in the 6th edition of Intersec Saudi Arabia, to be held from 1st to 3rd October 2024. This esteemed event serves as a platform for Matrix to showcase its extensive security offerings, spanning IP Video Surveillance, Access Control, and Time-Attendance solutions. Next-generation security solutions At Intersec Saudi Arabia, 2024, Matrix will present its NDAA-compliant security portfolio, designed to meet the diverse needs of modern enterprises. Matrix is one of the first Indian companies to deliver end-to-end cyber-secure video surveillance solutions, ensuring comprehensive protection from capture to monitoring. VMS, bullet, and dome cameras Aligned with OWASP ASVS 4.0 L2 standards, these cameras also hold UL and CE certifications, setting a benchmark Its Video Management Software (VMS) recently earned cybersecurity certification, fully compliant with the OWASP Top 10 Desktop Security Risks. At Intersec Saudi Arabia, Matrix will proudly showcase its Project Series and Professional Series Bullet and Dome Cameras, renowned for their robust cybersecurity features. Aligned with OWASP ASVS 4.0 L2 standards, these cameras also hold UL and CE certifications, setting a benchmark in secure, high-performance surveillance. NVRs, VMSP, and All Color Network Cameras The exhibit will also feature a variety of Network Video Recorders and the newly launched Video Management Software Platform (VMSP), which integrates NVR, server, and VMS. Visitors will also get a chance to see Matrix All Color Network Cameras in action, which provide superior quality color images in low-light or no-light conditions. Access Control and Time-Attendance solutions Matrix will showcase its GDPR-compliant Access Control and Time-Attendance solutions, featuring WhatsApp Integration Matrix’s Access Control and Time-Attendance solutions provide a unified system for managing physical security and workforce operations, ensuring accurate time tracking and access control. At Intersec Saudi Arabia 2024, Matrix will showcase its GDPR-compliant Access Control and Time-Attendance solutions, featuring the latest WhatsApp Integration, which allows users to receive real-time alerts and notifications directly through the app. COSEC ARGO FACE200T Matrix will also unveil its state-of-the-art facial recognition time-attendance terminal, the COSEC ARGO FACE200T, renowned for its exceptional accuracy, fast identification speed, and high user capacity. This advanced device supports seamless connectivity through PoE and Ethernet, ensuring smooth integration. Enterprise-grade telecom solutions Matrix, a veteran pioneer in the telecom industry, will present its latest Telecom Solutions at the summit. Its range of IP-PBX systems, Unified Communication servers, and VoIP gateways is designed to enhance business communication and improve operational efficiency. As businesses grow, Matrix’s telecom solutions are built to scale, providing a dependable, robust, and high-quality communication infrastructure. Intersec KSA Intersec KSA unites industry pioneers in security, emergency response, and safety, from all corners of the world Strengthening Market Presence in Riyadh, Kingdom of Saudia Arabia Matrix has consistently portrayed its potential for growth in the region with its commitment to delivering high-quality, reliable, and scalable solutions. Intersec KSA unites industry pioneers in security, emergency response, and safety, from all corners of the world. From groundbreaking advancements to revolutionary technologies, the security and safety industry has been a hub of innovation. Matrix yearns for vital discussions on future foresight, featuring prominent global experts, concerning Security and Safety industry. Advanced, cyber-secure solutions Tarun Sharma, Marketing Head at Matrix Comsec, expressed his enthusiasm for the upcoming event, "Intersec Saudi Arabia is a pivotal opportunity for Matrix to engage with industry pioneers across the Middle East, a region with unique security challenges." "As infrastructure projects grow and critical assets expand, the demand for advanced, cyber-secure solutions has never been greater. We are eager to demonstrate how Matrix’s comprehensive security offerings, from robust video surveillance to intelligent access control, can enhance the safety and efficiency of enterprises across the region." Safeguarding assets and data "Our goal is to understand the specific needs of Middle Eastern organizations and provide solutions that safeguard both their physical assets and sensitive data with the highest level of protection." Visit Booth 1-D34 to learn more about Matrix offerings at Intersec Saudi Arabia 2024, from 1st to 3rd October 2024.
HID®, a worldwide pioneer in trusted identity solutions announces the launch of the next-generation FARGO® HDP5000e designed to deliver vibrant, high-definition cards and IDs. HID's Isaac Young, VP & Head of FARGO, stated, "The HDP5000e is where unparalleled reliability meets exceptional usability and performance setting a new standard for the everyday retransfer card printing experience." FARGO HDP5000e ID card printer Built on the rock-solid foundation of the renowned HDP5000 printer series and proven retransfer technology over the last 25 years. The HID FARGO HDP5000e ID card printer emerges as the next iteration of this market-pioneering solution, poised to redefine the standards of reliability, usability, and printing excellence. Seventh-generation retransfer technology Engineered for universities, medium-to-large businesses, healthcare facilities, and government agencies who need retransfer printing technology to effectively personalize contactless cards and for any organization looking to switch from a higher-end, direct-to-card printer to a retransfer printing solution for improved image quality, the feature-rich FARGO HDP5000e is ideal. Young concluded, “The HID FARGO HDP5000e card printer offers seventh-generation retransfer technology for every need, from sharp and vibrant photo ID cards to multi-functional, high-security ID badge and card applications, the customer-inspired FARGO HDP5000e is the solution of choice for superior image quality, ease-of-use, and printer reliability.” Key benefits of FARGO HDP5000e High-level performance - With an increased card throughput and greater Ethernet speed than its HDP5000-series predecessors, the HDP5000e also boasts an advanced electronics platform ensuring faster and more precise control over the printing process, resulting in crisper text and more vivid imagery. Additionally, the printer’s enhanced memory and processing capabilities allow for more efficient handling of print jobs, especially in high-volume environments. Exceptional reliability - From its reinforced connection points to its streamlined module attachment, the HDP5000e is designed for dependability inside and out. The printer’s connectivity reinforcements strengthen and protect USB, Ethernet, and power cable connection points while the printer’s streamlined module attachment helps eliminate common issues such as internal card jams and misalignment. Usability enhancements at every turn - The HDP5000e’s user-friendly SmartScreen™ interface in high-definition, graphical OLED provides easy-to-understand notifications and helpful, walk-through prompts for setup, maintenance, and troubleshooting. What’s more, the printer’s Workbench™ diagnostic utility with its color Assist spot-color matching tool is conveniently built right into the printer driver so users have immediate access to everything they need via a single driver download. Should maintenance be required, the HDP5000e’s thoughtful design allows for easy, hassle-free access to the card path, main board, and film and ribbon drawer assemblies without the need for tools or special expertise. Security from end to end - The printer’s unique and inclusive resin scramble data protection feature effectively scrambles and subsequently conceals information printed with a resin panel. Used ribbon panels are thus rendered indecipherable, safeguarding cardholder data from fraudulent use. Moreover, the HDP5000e includes built-in AES-256 data encryption, support for UV printing, and optional locks for additional peace of mind.
RecFaces, in collaboration with Startologic, successfully hosted its three-city ‘Project Day’ event, held in Delhi on September 12, Bengaluru on September 5, and Mumbai on August 29. The event provided an in-depth exploration of cutting-edge facial recognition technologies, highlighting how these solutions can revolutionize security systems across industries. Project Day events The Project Day events brought together system integrators, technology partners, and industry professionals, all eager to explore the latest advancements in facial recognition technology. Attendees were enthusiastic about the potential of these solutions to transform security frameworks across various sectors, including critical infrastructure, finance, transportation, and enterprise operations. Id-Guard and Id-Gate Facial recognition technology can enhance security operations, minimize risks RecFaces experts, Oleg Kurochkin, Business Development Director for Asia-Pacific, and Mohammed Bajarsh, VP of Product for the MENA region, led detailed discussions on the company’s flagship products, such as Id-Guard and Id-Gate. Their presentations showcased the real-time capabilities of these solutions, emphasizing how facial recognition technology can significantly enhance security operations, minimize risks, and streamline project workflows. Customized project solutions Shashi Kumar Yadav, CEO of Startologic spoke about the overall potential of this technology, highlighting its transformative impact on security systems and project management. The event underscored the importance of creating customized project solutions tailored to the unique needs of end users. By integrating facial recognition technology into existing systems, businesses can streamline security processes, reduce human error, and substantially improve project outcomes. Operational efficiency Attendees participated in hands-on demonstrations of RecFaces’ facial recognition solutions, with Id-Guard and Id-Gate impressing them through their precision, speed, and flexibility. Participants explored how these technologies could enhance their security operations by improving efficiency, reducing risks, and offering tailored solutions to meet specific requirements. "With RecFaces Facial Recognition Solutions, we're providing businesses with the tools they need to enhance operational efficiency and minimize risks while delivering customized solutions that address their unique challenges," said Sukrit Varma, Global Marketing Partner, RecFaces.
Pre-registration is now open for C-Touch & Display Shenzhen 2024, organized by RX Kuozhan, scheduled to take place from November 6-8 at the Shenzhen World Exhibition and Convention Center (Bao'an) at Hall 10/12/14. Three-day event As Asia's premier B2B technology trade show for advanced display and smart touch solutions, C-Touch & Display Shenzhen leverages global resources to help display and smart touch manufacturers expand their brand influence and seize global business opportunities. The three-day event will welcome over 150,000 industry professionals to explore innovations from more than 3,500 suppliers, driving new industrial development trends in displays, smart touches, and terminal applications on a global scale. Register now for C-Touch & Display Shenzhen 2024 and save the USD 15 entry fee. New features at C-Touch & Display 2024 These innovation zones will not only provide insights into the latest technological advancements C-Touch & Display Shenzhen 2024 will introduce two major innovation zones: Technological Innovation and Application Scenario Innovation. The Technological Innovation Zone will include the Mini/Micro LED Display Technology Zone, Flexible Display Technology Zone, and E-paper Technology Zone. The Application Scenario Innovation Zone will feature the Smart Cockpit and In-Vehicle Display Zone, VR/AR Innovative Application Zone, and Smart Office and Education Innovation Zone. These innovation zones will not only provide insights into the latest technological advancements but also outline a blueprint for the future development of the display and smart touch industry. Innovative exhibition areas and forums Smart Cockpit and In-Vehicle Display: Reshaping the driving experience With the accelerated pace of automotive intelligence, Smart Cockpits and In-Vehicle Display technologies are becoming industry focal points. From large-screen entertainment systems to advanced navigation interfaces, C-Touch & Display Shenzhen 2024 will showcase the latest in-vehicle display technologies and smart cockpit solutions, offering an immersive driving experience. Commercial displays: Illuminating public spaces Commercial display technology plays a vital role in conference rooms, exhibition halls, shopping centers, and other public spaces. This year, the event will bring together commercial display screens of various sizes and forms, showcasing efficient and convenient solutions to enhance visual effects and interactive experiences in public spaces. Automation and industrial control displays: Meeting harsh environments Products meet stringent industrial ideals and lead industry trends with their clever technologies In the rapidly developing fields of industrial automation and intelligent manufacturing, industrial control display technology plays a crucial role. Its high reliability and durability ensure stable operation in various extreme and complex environments. C-Touch & Display Shenzhen 2024 will focus on cutting-edge industrial displays designed for industrial automation, process control, and monitoring systems. These products meet stringent industrial standards and lead industry trends with their innovative technologies and outstanding performance. E-paper technology: Pioneering green reading E-paper, an energy-saving and environmentally friendly display technology, is gradually transforming reading habits. The E-paper Exhibition Area is a key part of the green sustainable development theme of C-Touch & Display Shenzhen 2024, focusing on e-paper display technology and its application products. E-paper, with features such as low power consumption, high resolution, and flexibility, is widely used in e-books, e-tags, smart logistics, and other fields. E-paper Technology Zone Visitors will have the opportunity to learn about the latest advancements in e-paper technology In the E-paper Technology Zone, exhibitors will showcase e-paper displays of various sizes and forms, including black-and-white and color displays. Visitors will have the opportunity to learn about the latest advancements in e-paper technology, such as reflective display principles and ink screen technology, and explore innovative applications in education, retail, logistics, and other sectors. Flexible displays: Breaking traditional constraints As new models are introduced and prices decrease, OLED technology is expected to achieve rapid growth, particularly in foldable phones. C-Touch & Display Shenzhen 2024 will feature the latest advancements in flexible display technology, exploring innovative applications in smartphones, smartwatches, and other terminal devices. MLED: Pioneer of Next-generation Display Technology The MLED Technology Exhibition Area will highlight the latest research and development achievements and processes in MLED technology. It will showcase the manufacturing technology of Mini LED and Micro LED, high-brightness display technology, and high-reliability packaging technology in high-end televisions, monitors, commercial advertising, smart wearables, and other scenarios, envisioning the infinite possibilities of future display technology. Latest technologies and solutions Additionally, more than 80 themed forums will be held concurrently, bringing together experts and visionaries to provide insights into the latest technologies and solutions in Display and Touchscreen, Smart Cockpit and In-Vehicle Display, Electronic Paper, OLED, AR/VR, Commercial Display, and more. Visitors will have the opportunity to deeply exchange ideas with industry pioneers and peers, jointly promoting the progress and application expansion of new touch and display technology. View the agenda of onsite events: Shenzhen International Display and Touchscreen Elite Summit 2024 Shenzhen International Mini/Micro LED Industrial Chain Innovation and Development Summit Forum 2024 Shenzhen International OLED Industrial Chain Development Seminar 2024 Shenzhen International Commercial Display Elite Summit 2024 Shenzhen Ultra HD Display Summit Forum 2024 Shenzhen International Intelligent Cockpit and Vehicle Display Summit Forum 2024 AI Security and Smart Commercial Display Innovation and Development Summit Forum 2024 Micro OLED & Si-Display Forum 2024 8th Enabling | AR/VR Cross-Border Integration Innovation Forum Global Electronic Paper Technology and Application Summit Forum and Industry Research Conference 2024 The 6 connected shows: a mega feast of innovation C-Touch & Display Shenzhen 2024 will be held concurrently with the FILM & TAPE EXPO, Automotive World China, AMTS & AHTE South China, NEPCON Asia, and the Electronics Sourcing Show. Together at China's innovation hub, with over 160,000 sqm and 3,500 exhibitors and brands gathering, the six flagship shows covering automotive, electronics, display, and new materials will connect attendees across key industries in advanced manufacturing, providing industry practitioners with an unparalleled exhibition experience.
Kon Pak is an experienced sales professional with a diverse background in several industries, ranging from electrical engineering to retail. With a BBA in Marketing from Kennesaw State University and four years of sales experience under his belt, he will bring a wealth of experience in relationship-building and problem-solving to Speco’s customers across Alabama, Georgia, Mississippi, and Tennessee. Adaptable and knowledgeable “For each of our regional sales teams, we make sure we hire employees that are as adaptable as they are knowledgeable,” said Todd Keller, President and CEO of Speco Technologies, adding “Kon Pak represents the perfect middle ground between those two qualities: He’s a quick learner, but he’s also a genuinely enthusiastic and professional representative of the Speco team.” Though he was raised in Columbus, Georgia, Kon has lived in the Atlanta metropolitan area for the past 16 years and is a devoted fan of the Georgia Bulldogs. He lives with his fiancé, Nicole, two dogs, and one cat.
Wavelynx Technologies, a trailblazer in advanced, secure, and versatile reader and credential solutions, announced the launch of its industry-first app, Configure by Wavelynx, to revolutionize the way businesses approach security and badge reader management. With Configure, integrators, and partners can simplify the installation, customization, and on-site updates of Wavelynx readers - all from their mobile devices. Configure Configure brings a new standard to how readers are maintained and installed. It not only eliminates the need for a traditional configuration card but creates a seamless path to enabling wallet credentials. The company will showcase Configure at the Global Security Exchange (GSX) trade show in Orlando, FL September 23-25, 2024. Access control and security “As the industry is moving to mobile-first solutions, Configure represents a significant leap forward within access control and security management,” said Rob Lydic, President of Wavelynx Technologies. “By addressing the needs of installers, partners, and facility owners alike, we are setting a new standard for efficiency, security, and ease of use in the industry.” Secure updates and seamless interoperability Coupled with a secure key management process, users take comfort in knowing that with Configure Configure employs state-of-the-art encryption to ensure the secure transmission of data while implementing stringent authentication protocols to safeguard against unauthorized access. Coupled with a secure key management process, users take comfort in knowing that with Configure, their keys are protected, they can add a new device at any point and they can run a field upgrade securely in minutes. User-friendly configuration and management Wavelynx’s latest offering is centered on its intuitive toolset and user interface, allowing quick setup and real-time adjustments. Configure empowers users with on-demand updates and management capabilities, streamlining the entire configuration process from a single, handheld mobile device and interface. Intuitive mobile experience Configure is available immediately for deployment across various sectors, including commercial “Our customers love the simple and straightforward nature of implementing our solutions,” said Lydic. “We consistently hear positive feedback about our readers and Configure takes it to the next level with its intuitive mobile experience, saving ample time for integrators out in the field.” Configure is available immediately for deployment across various sectors, including commercial, industrial, and institutional facilities. Meet with Wavelynx at GSX At GSX, Wavelynx will collaborate with more than a dozen partners including AlertEnterprise (booth #1709), RightCrowd (booth #2243), and others, in showcasing the solutions modernizing the access control industry. In addition to Configure, Wavelynx will also showcase: Ethos™ readers: engineered with interoperability in mind to implement existing access control systems simple and secure. The Wavelynx Wallet: paves the way for digital credential systems as the industry moves toward mobile and unlocks more modern, secure, and interoperable access control solutions. Accelerate by Wavelynx: accelerates adoption of modern access control systems by providing a cost-effective path to secure wallet credentialing solutions.


Expert commentary
The European Union’s GDPR (General Data Protection Regulation) framework represents some of the toughest and most secure privacy laws in the world. Their creation signaled the EU’s dedication to individual privacy rights and generated new standards and requirements for an organization inside or outside of the EU wanting to do business in the region. This privacy stance raises an interesting question: to what extent (if any) will France be utilizing AI-assisted security and biometrics - at the upcoming Paris Summer Olympic Games? AI-assisted security systems As France prepares to host this global event, certain AI-assisted security systems like algorithmic video monitoring have been tested and are planned to be in use. The country also passed a law with a legal framework for addressing provisions of hosting the Games in their country, Law No. 2023-380. These technologies will support the police and security efforts to detect sudden crowd movements, irregular vehicle, and pedestrian movements, abandoned objects, people lying on the ground, and more, any of which could indicate an attack. Local connectivity One recent French poll found that an overwhelming number of respondents support the use of smart cameras Such technologies, which can be connected directly to localized command centers and police departments, provide an opportunity to prevent deadly incidents like the bombing at the 1996 Summer Olympics in Atlanta, GA. There are signs that citizens of the EU are becoming more receptive to such measures, with one recent French poll finding that an overwhelming number of respondents (89 percent) support the use of smart cameras in stadiums for this purpose. Biometric technology The general public and private use of biometric technology (face matching, face liveness, and other biometric modalities), on the other hand, continues to run into challenges with adoption in this privacy-focused region. For the most part, laws ban facial recognition, permitting its use only once someone has been convicted or is suspected of having committed a serious crime. Limitations of video surveillance Limiting the utility of biometrics to only video surveillance for an event of the Paris Olympics’ magnitude is not the best approach. The ability to quickly identify or de-identify possible suspects from regular attendees greatly strengthens the activities of the police and helps protect the rights of regular attendees. Consider the example of New York City detectives using facial recognition to identify a man who, in 2019, left a pair of potential bombs in the Fulton Street subway station. Benefits of facial recognition technology Many believe that the use of facial recognition could have expedited and solved the Boston Marathon bombing tragedy With facial recognition technology, it took only one hour to identify the suspect - a process that previously would have taken several hours or even days, leaving the possibility of further damage unresolved. Citing yet another example, many believe that the use of facial recognition could have expedited and solved the Boston Marathon bombing tragedy much sooner and more efficiently, aiding investigators who reportedly had to sift through 120,000 photos and nearly 13,000 videos before identifying the perpetrator. Need for real-time video With an estimated 16 million visitors expected to descend upon France for the Games - and an environment that is harder to protect from bad actors - is limiting the use of biometrics to video surveillance the most effective? In our minds, in certain high-urgency cases, such as tracking kidnapping cases or possible terrorism activity, it should be permissible for facial recognition to be applied to recorded video in real-time and without delay. Public safety Beyond this obvious good that biometrics can bring from a public safety perspective, there are other ways that biometrics can be woven into the fabric of the Summer Olympics to support a faster, more enjoyable experience for all. Consider queue management. In a few weeks, an estimated 2.3 to 3.1 million ticket holders will form lines to access Olympic events. Fingerprint scanning technology People could pass through lines in mere fractions of a second, versus having to fumble for a paper ticket If fingerprints were captured at the point of ticket purchase and fingerprint scanning technologies made available on-site, people could pass through lines in mere fractions of a second, versus having to fumble for a paper ticket that may be torn or damaged, or an e-ticket on a phone with a dead battery. This would speed up the processing of queues tremendously. Olympics-focused gambling activity Another area where biometrics can be beneficial is in Olympics-focused gambling activity, which is expected to gain steam as the Games get underway. Biometrics can be used to match facial images with legal documentation for age verification, and then combined with geofencing to ensure gambling participants are of legal age, depending on where they are physically based. Biometrics also makes it possible to identify, beyond the shadow of a doubt, all of the activities of particular individuals, which can help track nefarious activities like money laundering. Evolution of privacy and security We believe biometrics can be a force for major good in our society and around various facets of the upcoming Paris Olympics, most notably public safety. It will be interesting to watch both the 2024 Summer Olympics and the ongoing evolution of privacy and security laws and practices in France and the European Union.
As city managers, law enforcement agencies, and first responders face mounting pressure to combat crime and respond to emergencies with limited resources, real-time crime centers empowered by a new generation of data-driven technologies are emerging as an effective force multiplier. Real-time crime centers Real-time crime centers (RTCCs) serve as centralized hubs where dedicated personnel leverage pioneering-edge technologies to analyze diverse data streams and provide critical support to law enforcement and emergency operations. These 24/7 facilities are transforming how agencies gather, process, and act upon information, enabling more proactive and efficient policing strategies. The core functions of RTCCs These centers provide officers with unprecedented situational awareness and real-time intelligence At their core, RTCCs are tasked with three primary objectives: enhancing safety, facilitating identification, and supporting apprehension. By integrating data from a wide range of data sources, these centers provide officers with unprecedented situational awareness and real-time intelligence. Integrated data approach This integrated data approach allows RTCCs to alert officers to potential threats, quickly identify suspects, and guide responders during critical incidents. For instance, in the event of a robbery, RTCC operators can rapidly search camera and license plate data to track suspect vehicles, significantly improving the chances of a swift arrest. According to the Bureau of Justice Assistance at the U.S. Department of Justice, the mission of an RTCC is to centralize a broad range of current and evolving technologies, coordinate sworn and non-sworn human resources, and direct the attention to high-crime areas, active crimes in progress, high-profile or highly recidivistic offenders, and large-scale public events that may require law enforcement presence or response. The technology powering RTCCs The effectiveness of an RTCC hinges on its ability to seamlessly integrate a wide array of technologies: Open Platform Video Technology: At the heart of many crime centers is an open platform video management software (VMS) that serves as the central nervous system, unifying diverse data streams into a cohesive operational picture. By leveraging open APIs and SDKs, the VMS can incorporate a wide range of cameras, sensors, and analytics tools. This data-driven approach to video technology enables seamless alert distribution to both the RTCC and field officers via mobile applications. IP Camera Networks: The eyes of an RTCC, these systems combine fixed, PTZ, multi-sensor, thermal, and other specialty cameras to provide continuous city monitoring. Strategically placed throughout urban areas, cameras offer comprehensive coverage of critical locations such as transportation hubs, commercial districts, and high-crime zones. This network forms the foundation for real-time monitoring and incident response. Sensor Arrays: Beyond visual data, RTCCs employ various sensor technologies. Acoustic sensors can detect sounds such as gunshots, shouts for help, breaking glass, and other sounds instantly alerting officers and cueing nearby cameras. Environmental sensors monitor air quality for gasses, smoke, and other non-visible hazards. License Plate Recognition (LPR): LPR systems act as a force multiplier, continuously scanning for vehicles of interest. By generating real-time alerts for stolen or wanted vehicles, these systems significantly enhance the ability to track suspects and recover stolen property, contributing to reduced auto theft rates. Aerial Surveillance: Many RTCCs incorporate drone technology, providing on-demand aerial perspectives of developing situations. This capability is particularly valuable for monitoring large-scale events, assessing natural disasters, supporting operations in hard-to-reach areas, and serving as a powerful first response for crime scene situational awareness. AI-Powered Analytics: At the heart of many RTCC operations are sophisticated AI algorithms that analyze video data in real-time. These systems can identify a range of suspicious activities, from unattended packages to unauthorized intrusions. By rapidly processing vast amounts of video data, they help operators focus on potential threats and anomalies. Geospatial Mapping: To make sense of the influx of data, RTCCs rely on advanced mapping software. These tools visualize events, alerts, and data streams geographically, allowing operators to quickly identify patterns, clusters of activity, and relationships between incidents. Database Integration: RTCCs maintain direct connections to various law enforcement databases, including local, state, and federal resources like the National Crime Information Center (NCIC). This integration allows for rapid background checks and threat assessments, providing crucial context for ongoing operations. Cloud Infrastructure: The scalability and flexibility of cloud computing are revolutionizing RTCC capabilities. Cloud and hybrid solutions offer secure, off-site storage and facilitate easy data sharing between agencies. This approach not only reduces initial costs but also allows for incremental upgrades, making advanced RTCC functionality accessible even to agencies with limited budgets. Real-world impact RTCC operators tracked shooting suspects via camera feeds, guiding officers to their locationThe proliferation of RTCCs across the United States with over 80 centers in operation speaks to their proven effectiveness. Cities that have implemented these high-tech command centers are reporting significant improvements in response times, clearance rates, and overall public safety. Real-time surveillance In Winston-Salem, North Carolina, the local RTCC leverages over 1,300 live video feeds to provide real-time surveillance across the city. This extensive network, combined with gunshot detection technology and license plate readers, has already demonstrated its value. In a recent incident, RTCC operators were able to track shooting suspects via camera feeds, guiding officers to their location for a quick apprehension. Video analysis by RTCC Similarly, Newport News, Virginia, saw an immediate impact after launching its RTCC in 2021. The center has played a crucial role in solving homicides caught on video and rapidly closing a series of carjacking cases. These success stories underscore the game-changing potential of RTCCs when it comes to solving crimes and gathering evidence. In Memphis, Tennessee, video analysis by RTCC detectives helped identify a shooter in custody following an incident at a community basketball court even when no witnesses had come forward. Identifying suspects with RTCC Officers and analysts can view street and body camera footage to monitor crowds at parades The Jackson Police Department in Mississippi has seen similar benefits since building an RTCC in 2019, part of a broader effort that included deploying 100 cameras and 271 body cams. Officers and analysts can view street and body camera footage to monitor crowds at parades and other events. During pursuits, the cameras provide extra surveillance, allowing officers to identify suspects or witnesses to help solve crimes. Enhancing crime mitigation and emergency response While RTCCs have proven their worth in responding to active incidents, their true potential lies in proactive crime prevention and enhanced emergency preparedness. By leveraging advanced analytics and integrated data sources, RTCCs are evolving into powerful predictive tools for law enforcement. Pattern recognition algorithms For instance, pattern recognition algorithms can analyze historical crime data alongside real-time video feeds to identify potential hotspots for criminal activity. This allows law enforcement to strategically deploy resources, increasing visible presence in high-risk areas before crimes occur. Similarly, anomaly detection systems can alert RTCC operators to unusual behaviors or suspicious activities, enabling early intervention in potentially dangerous situations. Asset and property protection, automated alerts RTCCs can monitor critical infrastructure, government buildings, and other high-value assets 24/7 Asset and property protection is another area where RTCCs excel. By integrating with access control systems and using AI-powered video analytics, RTCCs can monitor critical infrastructure, government buildings, and other high-value assets 24/7. Automated alerts for perimeter breaches, unauthorized access attempts, or suspicious objects left in restricted areas allow for an immediate response, significantly enhancing security postures. Emergency response and preparedness In terms of emergency response and preparedness, RTCCs serve as vital command and coordination centers during crises. Whether facing natural disasters, major accidents, or other large-scale emergencies, RTCCs provide a centralized hub for information gathering and dissemination. Real-time video streams from affected areas, combined with data from environmental sensors and emergency service communications, allow for rapid situational assessment and coordinated response efforts. Post-incident investigation and analysis RTCCs can also play an active role in post-incident investigation and analysis. The ability to quickly compile and analyze vast amounts of data from multiple sources can significantly accelerate case resolution and help identify patterns to prevent future incidents. As RTCCs continue to evolve, their capacity for integrating diverse data streams and leveraging advanced analytics positions them as indispensable tools in modern law enforcement strategy. The future of technology-driven policing The integration of artificial intelligence and machine learning promises to enhance video analytics As RTCCs continue to evolve, they are likely to incorporate even more advanced technologies. The integration of artificial intelligence and machine learning promises to enhance video analytics capabilities, enabling faster and more accurate threat detection. Additionally, the expanding use of drones, subject to FAA regulations, could provide RTCCs with cost-effective aerial surveillance options. Effective and ethical operations However, the implementation of RTCCs is not without challenges. Agencies must navigate issues of privacy, data security, and community trust. Ongoing training for personnel and careful planning are essential to ensure these centers operate effectively and ethically. Data-driven approach Despite these hurdles, the trend toward technology-driven policing shows no signs of slowing. RTCCs represent a shift from reactive to proactive law enforcement strategies, offering a data-driven approach to crime prevention and response. As these centers become more prevalent, they will play an increasingly vital role in helping agencies maximize their resources and make informed decisions, ultimately contributing to safer communities for all.
Choosing the appropriate fingerprint technology for a given application is dependent on factors including the required level of security and matching accuracy, the desired capabilities and features, and the usability to achieve adoption and productivity goals. A successful evaluation process will help ensure that this mature and proven user authentication method performs as expected. Fingerprint biometric advantages The speed, simplicity, accuracy, and cost-effectiveness of the fingerprint method have made it among the most widely used for biometric authentication across industry sectors ranging from banking and finance, retail, and healthcare, to government and law enforcement. It performs biometric technology’s “something you are” function while offering unique characteristics that make it particularly valuable for many applications. Unique identifier The fingerprint biometric has the permanency of being reasonably stable and consistent over time Among these characteristics is the pervasiveness and special nature of the fingerprint -- almost everyone has one, and each is a unique identifier. The fingerprint biometric has the permanency of being reasonably stable and consistent over time. It is also easy to acquire, measure, and process. High adoption rate Another key attribute of a fingerprint biometric is its ability to be protected against threats ranging from abuse and misuse to theft, imitation, and substitution. When it is used with recognition techniques the resulting solution performs with a combination of accuracy, speed, scalability, and ease of use. Fingerprint biometric solutions also have the highest adoption rate among biometric authentication solutions according to an industry report published by Payments Journal. Three interrelated components There are three basic components in any fingerprint biometric system as shown in Figure 1: capture (using a sensor that can capture even the most difficult finger types); liveness detection (using the Presentation Attack Detection – or PAD – technique); and matching (including preventing rejection of a legitimate user). Biometric algorithm The sensor captures and pre-processes the fingerprint data. It must be able to successfully capture fingerprint images for a range of skin types and print conditions under diverse temperatures, humidity, light, surface oil, dust, dirt, and other environmental conditions. A biometric algorithm then extracts minutiae data about the fingerprint ridges (endings, bifurcations, islands, etc.) and their orientation and position. PAD technique Implementing a presentation attack detection (PAD) technique at this stage activates the fingerprint biometric system’s second key element: liveness detection. This verifies the fingerprint’s authenticity and that it belongs to a living person. The system’s third element – matching – occurs after the PAD-verified fingerprint dataset has been securely stored as a record, known as a template, inside an enclave with cryptographic protection. Check for liveness The corresponding template of the legitimate user is then retrieved from secure storage When the fingerprint is presented for matching, it is rechecked for liveness. The corresponding template of the legitimate user is then retrieved from secure storage and the process of matching the fingerprint with this template is executed. This must be completed accurately and without rejecting a legitimate user. Types of fingerprint sensing technologies There are four prevailing categories of sensing technologies used with fingerprint readers: optical, capacitive, thin-film transistor (TFT), and multispectral imaging (MSI). Optical and capacitive method Optical is the most mature sensor technology and offers the benefits of a compact size, good capture Optical is the most mature sensor technology, and offers the benefits of a compact size, good capture and matching performance, a small enough size to fit in most desktop environments or shared workstations, and a high level of accuracy at a cost-effective price point across all use cases. The capacitive method, on the other hand, is less prone to fake finger attempts while also offering a thin and compact size for space-limited applications, the power efficiency to support battery-operated devices, and the ability to handle both indoor and outdoor lighting conditions. TFT technology The third technology goes a step further in capture accuracy. TFT technology can accurately recognize the smallest fingerprint features with ultra-high resolution and is used either as a larger-size matrix capacitive proximity detector (capacitive fingerprint sensor) or a larger-area matrix light detector (optical fingerprint sensor). It is ideal for in-the-field mobile identification applications that require a cost-effective, ultra-slim, and lightweight solution with low power consumption. MSI technology MSI technology differs from all three approaches, projecting multiple colors of light into the finger from different angles to collect both surface and subsurface biometrics data. It captures the most difficult fingerprints of diverse demographics, in a wide range of challenging environments. HID has used this patented technology in fingerprint readers that are compliant with ISO 30107-3 PAD Level 2 for advanced anti-spoofing against fraud. The technology also improves matching and offers sophisticated endpoint security that prohibits cyber criminals from gaining unauthorized access to networks by turning fingerprint readers into secure endpoints. Best practices for technology selection Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership. There are three top considerations: security, suitability, and usability. Each is important and the best approach is to strike a balance between all three. Following are the questions to ask during the selection process: Security: What is the regulatory environment? Financial and government services, healthcare, and law enforcement are some examples of highly regulated sectors with elevated security compliance requirements. Are there mandates in place for advanced capturing and biometric authentication specifications? How important is it to ensure anti-spoofing through liveness detection? Will endpoint security be required so that, if the fingerprint device is hacked, no network, system, or data behind the firewall will be impacted? Suitability: Where will the biometric technology be implemented? There will be additional considerations if it is to be embedded in portable, battery-operated devices that require low power consumption. Where will the technology be used? Will it need to fit into small spaces or be used in challenging indoor or outdoor conditions and environments? Will durability be important? Some deployments will face unpredictable weather and difficult lighting conditions for image capture. Will the technology be used for mission-critical border control or a more common – and less demanding -- commercial use? Usability Is it critical that the technology easily and consistently perform capture and matching? Will there be high volumes of fingerprint captures and matches? Is “friction frustration” a concern? If so, the solution must perform matching quickly and accurately to sustain high levels of user productivity. Will the fingerprint device be used by one person exclusively, or multiple people in a shared workstation setting? How diverse is the user population? Some readers are designed to handle all types of fingerprints and diversified demographics. Different applications Fingerprint biometrics is a proven solution to address real-world challenges, each with its requirements The answers to these questions will help determine the best choice of fingerprint technology. Different applications apply fingerprint biometrics to very different use cases but in all cases. It is a proven solution to address real-world challenges, each with its requirements. For instance, in a healthcare clinician’s terminal area or a similar shared environment with limited space, a durable, low-profile capacitive sensor may be the right answer. For an organization in a highly regulated, mission-critical environment like a bank or border control agency, advanced technologies such as MSI readers may be needed to avoid the serious repercussions of a spoofed identity or the rejection of a legitimate one. Requirements for a biometric solution These are just a few of the requirements to consider when choosing a fingerprint solution. In banking and finance, alone, fingerprint biometrics is used for applications ranging from transacting at the ATM to customer onboarding (eKYC), compliance (AML/KYC), and fraud prevention. The retail sector adds even more, including age verification, loss prevention, point of sale (POS) security, self-service checkout, and secure time and attendance. Law enforcement organizations have their unique requirements, using fingerprint biometrics for background checks, criminal booking, crime investigation, inmate management, mobile identification, and more. For government agencies, typical applications include benefits distribution, border security, citizen ID, employ authentication (SSO/MFA), and voter registration. Each application requires a thorough assessment of the best fingerprint technology for the job. The right touch The right solution will deliver the optimal balance of security, suitability, and usability Fingerprint biometric solutions empower a wide range of use cases with the simple touch of a finger. The right solution will deliver the optimal balance of security, suitability, and usability based on an analysis of criteria including specific application requirements, the characteristics and size of the user population, and challenges posed by environmental conditions. Accuracy, efficiency, and security The world faces increasingly dangerous fraud, account takeover, and impersonation threats. As industries and enterprises work to improve and evolve their identity and access strategies to combat these threats, fingerprint biometrics continue to prove their value through solutions that meet the key selection criteria while delivering the highest levels of accuracy, efficiency, and security.
Security beat
In an emergency, information is pivotal. More information provides better understanding of an emergency and empowers potentially life-saving decision-making. Emergency response teams depend on information to guide their efforts and to deliver targeted assistance. On the front lines of emergency response are 911 and field responder agencies, which must direct reaction to life-or-death situations rapidly and efficiently. Historically, 911 operators had to respond based on very little information, perhaps just a voice on the phone or a location on their screen. Providing critical information Today, there are literally millions of information sources available, ranging from connected buildings to vehicle telematics to live video streams to health information from wearable devices. In fact, there are 540 million connected devices, any one of which could provide critical information in an emergency. But how can those information sources be leveraged to improve emergency response? That’s the mission and value proposition of RapidSOS, an ‘intelligent safety platform’ company that connects 911 operators with the vast universe of information available to promote better and faster emergency response. Highly sophisticated operation The platform is integrated into every major public safety software system and first responder agency “RapidSOS fuses human and artificial intelligence to put critical information from any connected device directly into the existing systems and operating procedures of first responders across the United States,” says Michael Martin, CEO of RapidSOS. RapidSOS is widely used by first responders. The platform is integrated into every major public safety software system and first responder agency. There are more than 4,600 software integrations that serve more than 21,000 first responders and 911 agencies. In 2023, RapidSOS supported the lifesaving work of public safety across 171 million emergencies with 3.3 billion data payloads. The system is adaptable and configurable to support any agency, from a highly sophisticated operation in New York City to a local sheriff running their own 911 center. Intelligent analytics and reporting RapidSOS Unite is the latest evolution of the product, a single solution that includes AI automation, rich content pathways, redundant connection to caller phones, and access to millions of connected devices. In an emergency, Unite intelligently fuses data from among millions of sensor feeds into a unified picture of an incident, allowing public safety officials to view real-time location, health profile, telematics, alarm data, and more. RapidSOS Unite is the latest evolution of the product, a single solution that includes AI automation RapidSOS offers core modules that handle call, text, video, sensor, mapping, and administration tools, and that provide partner data from connected devices. Additional modules provide enhanced geographic information system (GIS) data, and automated translation and transcription. There is also a single sign-on (SSO) upgrade, intelligent analytics and reporting, and seamless integration into field responder applications. Field responder applications Consider how an emergency might unfold and how RapidSOS can help. In a car accident, data from a modern automobile telematics system can alert a 911 operator of the accident as it happens. Data from a passenger’s wearable device might provide information about their health and condition. A nearby video or traffic camera could fill in details of how the accident occurred. Useful information in an emergency might come from any one of thousands of sources, including public safety data, sensor feeds, enterprise security systems, smart phones, etc. In a train derailment, electronic access to the cargo manifest can identify which train cars contain hazardous materials and how to manage the specific type of hazmat. This information could save valuable time when responding to incidents like the Feb. 3, 2023, Norfolk Southern train derailment involving 38 cars in East Palestine, Ohio. Consider how an emergency might unfold and how RapidSOS can help Institutional security partners Norfolk Southern is one of the companies that provides information to first responders using RapidSOS; in effect, the company provides a direct digital link from their rail security operations to any first responder in the United States. Amazon’s global operations centers also interface with RapidSOS to provide critical information to first responders. Partnering with corporate security helps to better support the flow of data from institutional security partners and their solutions. Information can transform and guide emergency responses. For example, in a structure fire, real-time sensor feeds throughout a building can help 911 and first responders understand how the fire is progressing. Real-time security camera footage Having access to live feeds can save lives as 911 provides pre-arrival instructions such as CPR Leading the way to providing video feeds from private camera systems to 911 operators is an agreement between Eagle Eye Networks and RapidSOS, which was announced in April 2024. The agreement allows an enterprise to opt-in to share real-time security camera footage from an Eagle Eye video stream during a live 911 call. Having access to live feeds can save lives as 911 provides pre-arrival instructions such as CPR. “Security cameras are crucial in many locations, including schools, but previously those cameras could not be accessed by 911 during an emergency but were only used for investigation after an incident,” says Martin. Improving fire and life safety systems RapidSOS is also integrated with Honeywell’s Connected Life Safety Services (CLSS) system, a cloud platform that combines software and hardware to improve fire and life safety systems. Technology integrations between the two companies further modernize and digitize the public safety communications process to provide faster, more accurate communications with emergency centers (i.e., 911 agencies). RapidSOS technology securely transmits detailed data about an emergency CLSS provides real-time visibility and connectivity to help systems integrators and facilities managers make informed decisions and manage fire systems more efficiently. When combined with Honeywell's solutions, RapidSOS technology securely transmits detailed data about an emergency, such as the type of hazard, severity, and location within the impacted building, to emergency response centers. Video object detection Rapid SOS’s emerging Harmony artificial intelligence (AI) product serves as a ‘co-pilot’ for 911 operators, helping them manage the high volume of emergencies by making their response more efficient. Harmony pulls all the sensor feeds in an emergency and works to make only the most important information available in the hands of 911 and first responders. Harmony can take key insights from text and video data, use ‘sentiment analysis’ to determine the emotion tone of a message, and help 911 professionals using language translation, keyword alerts and video object detection. Harmony can help local agencies as they address a 25% average staffing shortage by providing additional support to 911 professionals while lessening the workload. Harmony is also working to help RapidSOS expand the ecosystem, stitching more data together and quickly making it more actionable than ever. Emergency response system RapidSOS also interfaces with Iamresponding, a comprehensive end-to-end emergency response system for first responders in the fire and other emergency sectors. Iamresponding’s field responder application is used by RapidSOS to get information out to first responders in the field. More than 650,000 first responders use RapidSOS’s field application RapidSOS’s recent acquisition of Iamresponding helps the company improve the connection with the last mile “in-the-field” piece of the puzzle, ensuring partners across computer-aided dispatch (CAD), integrated applications, mobile data terminals, body cameras and other responders have access to critical data. More than 650,000 first responders use RapidSOS’s field application. Enhancing emergency response RapidSOS’s Safety Pioneer Program formalizes the important partnership between RapidSOS and public safety agencies. Participants in the program receive early access to new platform features, contribute to the platform roadmap, and drive feedback to enhance emergency response. “911 and first responders do incredible lifesaving work,” says Martin. “Everything we have done and built at RapidSOS is a direct result of the engagement, partnerships, inside advice and insight we have gotten from public safety. We have learned from them, developed new technologies and tested them.” Martin adds: “Companies have data and we now know how to make that data actionable into the hands of 911 and first responders to save lives. This is an exciting moment for us continuing our mission in partnership with public safety, and for technology and security companies to have a major hand in that.” {##Poll1719488782 - What is the most valuable benefit of artificial intelligence (AI) in an emergency call center?##}
Security professionals are recognizing the intelligence value of leveraging publicly and commercially available information. This information can now be accessed more effectively from typically hard-to-reach regions. Also, the technological capabilities have matured in our age of artificial intelligence, machine learning, and data science. Intelligence has historically been based on classified data. However, today’s unclassified data, including open-source intelligence (OSINT), is increasingly being used to provide context and queuing for other types of intelligence. Advanced identity intelligence Babel Street is a technology company providing advanced identity intelligence and risk operations using an AI-enabled data-to-knowledge platform to unlock insights from a flood of data. The company provides advanced data analytics and intelligence for the world’s most trusted government and commercial organizations. Experts have predicted that by 2025 over 463 exabytes of data will be generated each day globally The sheer volume of data is growing exponentially. Experts have predicted that by 2025 over 463 exabytes of data will be generated each day globally. Not only are we seeing exponential growth in the volume of data, but there is also disparity in the veracity and the variety of data. This is being compounded by the ‘app economy’ in which data is created in a new format for every app added around the globe. Human language technology “The problem is that the data ‘junk’ and the ‘crown jewels’ are in the same bucket, and government and commercial entities need better and faster ways to extract intelligence from these torrents of data,” says Farid Moussa, VP, Strategy & Public Sector, Babel Street. Prior to joining Babel Street, Farid retired from the National Security Agency (NSA). He has guided video, image, speech, and text analytics (VISTA) and developed an appreciation for human language technology. An elusive source of data is the Dark Web, where every user, by design, is attempting to obfuscate their identity, and bad actors are hiding much better. “This presents a cat and mouse game – the cat must be smarter than the mouse, but the mouse is continually getting smarter,” says Moussa. Intelligence tools for data analysis SIGINT and HUMINT – while both vital – are also the most expensive forms of intelligence There are several intelligence tools for analyzing data. One of them is signals intelligence (SIGINT), which refers to electronic transmissions collected by ships, planes, ground sites, or satellites. Another is human intelligence (HUMINT), which is collected in a human-to-human fashion. Open-source intelligence (OSINT) is obtained by searching on topics or entities of interest that are publicly available on the Internet at large. Today, these various categories are often done in ‘silos of excellence.’ However, the best practice is using all forms together in a holistic fashion. SIGINT and HUMINT – while both vital – are also the most expensive forms of intelligence, while OSINT, which is growing in importance, is most cost-effective. All are vital forms of intelligence; OSINT is complementary and crucial to holistic intelligence practices. Holistic intelligence practices When it comes to physical security of people and places, OSINT has become a critical source of actionable information. Security directors leverage Publicly Available Information (PAI) to safeguard against threats to individuals, property, travel routes, and event sites. By monitoring PAI, security teams can detect and respond to potential dangers, including during and after events where thorough preparation is vital. Online information can contain warning signs of impending threats. It informs security professionals in uncovering digital traces, confirming intentions, and addressing risks across language barriers, ensuring proactive risk management for the protection of people and property. Role of Natural Language Processing (NLP) The Internet and social media were mostly English language by default, but that has changed exponentially Natural Language Processing (NLP) is a crucial capability that has evolved to recognize the richness and variety of words and names in multiple languages and scripts, and their use across cultures. Using machine learning and linguistics algorithms, the technology simultaneously considers numerous types of name variations. At one time, the Internet and social media were mostly English language by default, but that has changed exponentially. Babel Street’s world-class entity matching technology measures over 100 features to calculate the similarity of entities across multiple languages. Despite advances in data management and the cloud, there are still multiple challenges and complexities with integration of these data elements. Challenges include spelling variances/phonetics, language translation issues, criminal evasion, human error upon input, typos, etc. Accessing data from a scattered landscape While there have been advancements in cloud technologies, agencies utilizing open-source data are typically working within a highly scattered data landscape and must use a wide array of tools to get at the relevant pieces. This fragmentation makes it difficult to run analytics and apply AI and machine learning at scale in order to derive actionable insights. Unstructured and relationship data are visualised through advanced link analysis As with many disciplines, artificial intelligence (AI) is changing the game when it comes to intelligence. NLP and AI algorithms are employed to enhance datasets for greater quality, usability, and completeness. Unstructured and relationship data are visualized through advanced link analysis, geographic heat maps, influential entity carousels, topic clouds, and patterns by time and day. Geographic heat maps The advanced algorithms accurately score and prioritize critical entities within the relationship network while providing the citations from which an AI/ML-based decision was made. “With the democratization of AI, the world is becoming flat,” says Moussa. “Just like the most prosperous countries, even the poorest countries have the most advanced capabilities to do damage. Third-world economies often present a scenario where the financial gain of nefarious schemes and low-to-no regulation combine to incentivize bad actors.” The Challenges of Name Matching Identity has been an ongoing challenge for intelligence analysis due to the vast complexity of linguistics, spelling and cultural variances, human error, as well as human evasion. Technology and data science approaches are maturing, however machine translation can still struggle with meaning. The best-of-breed natural language processing capabilities run against the data while it still is in its native language. This minimizes the occurrence of analytic errors caused by inaccurate machine translations. This minimizes the occurrence of analytic errors caused by inaccurate machine translations It’s tempting to think that name matching is like doing a keyword search. The complexity of language makes it more challenging. New names are constantly created, with multiple spellings and no set of rules to encompass how names are formed. They are variable across languages, scripts, cultures, and ethnicities. Culturally specific nicknames and aliases add to the complexity. Replacing human involvement The investigation of the Boston Marathon Bombing in 2013 spotlighted an example of the significance of intelligence analysis. Even though the FBI had issued a detain alert for Tamerlan Tsarnaev back in 2011, Tsarnaev managed to travel to Russia in January 2012; and in July 2012, he returned to Boston. He was not detained on either occasion because there were too many names on the lists, and Tsarnaev’s last name had been spelled differently from the way it was on travel documents, thus enabling him to get through security. With the Internet, social media, and the dark web, there’s been an exponential increase in public communications in various languages, adding significantly to the amount of analysis required to keep societies safe. Name matching, using AI, analyses multiple contextual data points across languages to arrive at matches. Name matching, using AI, analyzes multiple contextual data points across languages to arrive at matches A common misconception is that this technology will replace human intelligence. “It’s more accurate to recognize its role as a force-multiplier, allowing humans to focus on the on the harder problems and/or vetting the results of AI,” says Moussa. “The technology can efficiently analyze massive volumes of data and distill it into actionable information in a timely manner. It augments human capabilities, enabling analysis at speed and scale beyond human capacity, without replacing human involvement.” Commercial Technology to the rescue “When it comes to threat and identity intelligence, we face a risk-confidence gap, underscored by the challenge of integrating traditional tactics with the modern digital landscape,” adds Moussa. “We cannot ‘hire’ our way out of this problem. Instead, it is imperative that we adopt technology to scale our efforts and free humans to solve the harder problems that machines cannot solve yet.” The public sector loves to build things, but there are time-to-value and return-on-investment considerations to the ‘build or buy’ decision. When commercial technology can be leveraged by government, it frees resources up to work on problems that the commercial world hasn’t yet figured out, says Moussa. “The public and private sectors need to come together – one team, one nation, working together with mutual trust and collaboration,” he says.
In the competitive world of physical access control, Big Tech companies are seeking to play a larger role. Physical access competition Apple Wallet continues to stake its claim on mobile credentialing. Amazon One Enterprise is pushing a palm-based identity service. Google/Nest offers smart locks for home access control, with identity and access management provided in the Google Cloud. The entry of these big companies in the historically fragmented physical access control market is causing disruption and foreboding new levels of competition. Apple Wallet Impacting Credentialing Trends The popularity of mobile wallets and contactless technologies in general has grown, creating more demand At Apple’s Worldwide Developer Conference in June 2021, the company announced support for home, office, and hotel keys, including corporate badges and student ID cards, in Apple Wallet. Later, the company announced Hyatt as the first hotel partner to support the technology. Since then, the popularity of mobile wallets and contactless technologies in general has grown, creating more demand for a seamless solution such as Apple Wallet. Easy access In 2023, HID Global announced the availability of their employee badge in Apple Wallet, allowing staff and guests to easily access corporate spaces with their iPhone or Apple Watch, including doors, elevators, turnstiles, etc. Employees just need to hold their iPhone or Apple Watch near the reader to unlock. Factors affecting the rate of adoption However, implementing and maintaining an Apple Wallet-based access control system can incur costs for hardware updates, software licensing, and ongoing maintenance. Factors affecting the rate of adoption include the need to upgrade existing infrastructures to accommodate the technology, and the necessity for access control manufacturers to develop and implement integrations with Apple Wallet. Benefits of Adoption Keys in Apple Wallet take full advantage of the privacy and security built into the iPhone and Apple Watch With larger companies leading the way, some smaller ones might take longer to catch up. There is also a need to educate building owners and administrators to see the value and benefits of switching to Apple Wallet-based access control. Convenience and greater security can accelerate adoption. Keys in Apple Wallet take full advantage of the privacy and security built into the iPhone and Apple Watch. Sensitive data protection A compatible app, specific to the building’s access control system, is needed. Once added, credentials are securely stored in the iPhone's Secure Enclave, a dedicated hardware chip designed for sensitive data protection. Holding an iPhone near an NFC-enabled reader enables the transmission of encrypted credentials. In addition to Near Field Communication (NFC), some systems also utilize Bluetooth Low Energy (BLE) for added security, longer read range, and hands-free unlocking. Phones need sufficient battery charge to function. Amazon One Enterprise Enables Palm-Based Biometrics In November 2023, Amazon Web Services Inc. (AWS) announced an identity service providing comprehensive and easy-to-use authentication for physical and digital access control. The system enables users to employ their palm as an access control credential, allowing organizations to provide a fast and contactless experience for employees and others to gain access to physical locations as well as digital assets. Physical and digital locations Physical locations include data centers, office and residential buildings, airports, hotels, resorts Physical locations include data centers, office and residential buildings, airports, hotels, resorts, and educational institutions. IT and security administrators can easily install Amazon One devices and manage users, devices, and software updates using AWS’s Management Console. Elimination of physical credentials An advantage of the Amazon approach is the elimination of physical credentials such as fobs and badges, and digital elements such as personal identification numbers (PINs) and passwords. AWS says security is built into every stage of the service, from multi-layered security controls in the Amazon One device, which is the same technology used in the Amazon Go retail stores, where shoppers can pay for purchases by scanning the palm of their hands. The devices combine palm and vein imagery for biometric matching and deliver an accuracy rate of 99.9999%, which exceeds the accuracy of other biometric alternatives, says the company. AI and ML The palm-recognition technology uses artificial intelligence and machine learning to create a “palm signature” that is associated with identification credentials such as a badge, employee ID, or PIN. Boon Edam, a revolving door and turnstile manufacturer, offers Amazon’s palm biometric technology on its equipment, and IHG Hotels & Resorts uses the technology to provide employees a convenient way to identify themselves and gain access to software systems. Google and Nest Devices in Access Control When the Nest × Yale Lock is connected to the Nest app, a resident can unlock a door from their phone Google’s Nest devices include smart locks for home access control. The Google Nest × Yale Lock allows access control via both physical keys and passcodes accessible through the Google Home app. When the Nest × Yale Lock is connected to the Nest app, a resident can unlock a door from their phone. Passcodes can be created for family, guests, and other trusted persons. Alerts can be provided whenever someone unlocks and locks the door. When Nest “knows” a resident is away, the door can lock automatically. Voice control, Google Home app Voice control, using Google Assistant integrated with various Nest devices, enables the use of voice commands to lock and unlock doors, thus adding another level of convenience. Smart home devices from various manufacturers can be controlled through the Google Home app. SMART Monitoring ADT’s Self Setup smart home security systems integrate Google Nest smart home products with ADT security and life safety technology, including SMART Monitoring technology. Microsoft Azure is another company that could impact access control. The Microsoft Azure Active Directory is an identity and access management platform that could be extended to physical access control, leveraging existing user credentials. Long-Range Impact on the Security Marketplace Big Tech companies are creating platforms for managing access control data, integrating with other security systems Increasingly, Big Tech companies are creating platforms for managing access control data, integrating with other security systems, and offering analytics for optimizing security and building operations. Big Tech is also actively researching and developing new technologies for access control, such as facial recognition, voice authentication, and AI-powered anomaly detection. Access control communication and integration As their involvement in physical access control grows, Big Tech companies could potentially gain more influence in setting industry standards for access control communication and integration, similar to how they have become dominant in other areas such as mobile platforms. Given their expertise in user interface design and data analysis, Big Tech companies could help to direct how future access control systems are managed and how users interact with them, including more intuitive and user-friendly operations. Future of physical access control Existing concerns about privacy, security, and potential dominance by a few Big Tech companies could spill over into physical access control. However, traditional security companies, startups, and industry consortiums are also actively developing innovative solutions. Ultimately, the future of physical access control will likely be shaped by a combination of many different players and technologies – large and small.
Case studies
One of Indonesia’s shopping mall operators, Agung Sedayu Realestat Indonesia (ASRI), is using the latest AI video technology from IDIS to boost profitability and growth. Agung Sedayu Realestat Indonesia ASRI is a subsidiary of the Agung Sedayu Group and operates five shopping and leisure complexes in Jakarta, four residential developments, and three office towers. To improve safety and security across this estate and boost operational efficiency, the company has adopted an end-to-end IDIS video solution that includes highly accurate people counting analysis integrated with ASRI’s centralized database. Surveillance coverage expansion The upgrade integrates legacy third-party cameras to reduce costs and waste while expanding surveillance The upgrade also integrates legacy third-party cameras to reduce costs and waste while expanding surveillance coverage of internal and external areas with the latest high-performance IDIS HD cameras, eliminating blind spots. The contract was awarded to IDIS integration partner PT Mandiri Cipta Integrasi (MCI) following a price-competitive bid and proof of concept demonstration. Intuitive controls The upgraded solution comprises over 250 IDIS 5MP bullet and dome cameras, delivering forensic image capture in all lighting conditions. It also includes intuitive controls for monitoring and managing surveillance operations across all five malls using a third-party video wall from ASRI’s control room. IDIS AI-in-the-Box for retail devices The flexible 4-channel add-on devices deliver actionable insights and make it easy to scale up the power People counting and options to use heat maps, queue management, and occupancy monitoring are provided by fifteen strategically deployed cameras connected to IDIS AI-in-the-Box for Retail devices. These flexible 4-channel add-on devices deliver actionable insights and make it easy to scale up the power of surveillance systems without license fees or the need for costly retail analytics software. IDIS NVR system The video footage and analytics data are stored on eight robust IDIS 64-channel DR-8564 NVRs, which support RAID 5 with eight hot-swappable 10TB HDDs for rapid and efficient maintenance. The IDIS NVR system provides two months of storage, while ASRI backs up data for an additional month, using its own NAS devices to easily and cost-effectively meet the extended three-month retention requirement. Log collector software ASRI and its retail partners improve their consumer offerings and make more informed decisions IDIS also developed log collector software tailored for the project and provided it cost-free to support seamless integration of people counting data from the NVRs to ASRI’s third-party relational database. ASRI Innovation Sales Manager, Roy Wahana, says understanding and measuring customer behaviors and preferences will help ASRI and its retail partners improve their consumer offerings and make more informed decisions about marketing, resource allocation, and business investments. IDIS Solution Suite's flexibility “As we invest in our offering of high-end retail, leisure, residential, and lifestyle venues for discerning consumers, IDIS technology gives us the most dependable, powerful, and sustainable platform for video monitoring and storage." "Our new video infrastructure supports safety, security, and better decision-making across all our malls.” IDIS MEA & Asia Senior Sales Manager, Alex Lee, adds that the IDIS Solution Suite's scalability also ensures future-proofing and flexibility. Video surveillance platform “For the project's next phase, our flexible video surveillance platform will make it easy for ASRI to integrate AI-powered facial recognition software and store video data with a local cloud storage provider." "This will enable even more flexibility in how authorized personnel access and manage footage and analytics data.”
Munich’s Hofbräuhaus enjoys an iconic status, as both a heritage property and a spiritual home for lovers of German beer. “In this historic building is the world’s most famous tavern,” explains its Security Manager, Robert Graßl, adding “The whole world goes in and out. Security is very important.” Bavarian Duke Wilhelm V commissioned Munich’s original Hofbräuhaus in 1589, initially as a brewery to supply the Wittelsbacher Hof. Moved at the end of the 19th century and severely damaged during World War II, it underwent reconstruction in 1958. It now attracts tourists and city locals, seating up to 3,000 guests indoors and a further 400 in the beer garden. Access rights management Digital devices and low-impact skills were needed to assure compliance with origin protection Although the building is an important heritage monument, it requires 21st-century digital access to keep site users safe and streamline day-to-day operations. They wanted fast, secure access rights management for employees and service providers – including up to 100 waiters working each shift – within a unified system that could authorize access at both the Hofbräuhaus and their food production facility in Brunntal. Of course, inobtrusive digital devices and low-impact installation were a necessity to ensure compliance with heritage preservation regulations. Digital access for a famous heritage building Many electronic access products and technologies are not appropriate for historic buildings. An eCLIQ key-based digital access solution is different: eCLIQ cylinders are compatible with the strict monument preservation requirements at the Hofbräuhaus. They have a flush fit, so don’t even appear to be part of an electronic locking system. With wireless installation at the doors, devices blend with the building interior. “We can exchange a mechanical cylinder 1:1 with an eCLIQ cylinder without having to modify anything on the door or install cables,” confirms Miriem Hammoudi, Business Development Manager at ASSA ABLOY Sicherheitstechnik GmbH. ASSA ABLOY fitted around 100 eCLIQ locking cylinders and supplied 340 eCLIQ programmable keys for Hofbräuhaus managers to issue to relevant staff and service contractors. Easy operation for flexible, cost-efficient management Every eCLIQ key has an integrated chip and is programmable individually for the keyholder Every eCLIQ key has an integrated chip and is programmable individually for the keyholder. The versatility of eCLIQ is demonstrated when a key is lost: Access authorizations are removed rapidly – simply by reprogramming cylinders – ensuring security is maintained. The eCLIQ system also helps manage workflows for service providers, such as cleaners: Their access is enabled on a time-limited basis. A standard battery inside each programmable electronic key powers the cylinder or padlock on insertion – and encrypts data transfer between cylinder, key and system – so no external power source or wiring is needed. Scalable web-based platform The Hofbräuhaus team manages their system via a flexible, scalable web-based platform, CLIQ Web Manager: “I can program keys from anywhere or also block them quickly if a key has been lost or if someone is no longer allowed to enter,” says Robert Graßl. He adds, “And I can install any cylinder in any door by adjusting the length. I don’t have to carry extra stock which is really cost effective.” New master key system With the hosting solution chosen, access data is stored securely at ASSA ABLOY, accessible anytime and from any location, which is an ideal configuration for managing large systems or multiple locations. Their system is easy to expand anytime – future-proofing Hofbräuhaus access. “The situation before the new master key system was installed was problematic,” says Robert Graßl, adding “Keys were distributed and nobody knew who held them. Now, everyone carries only one key programmed with details of where and when they can enter. It’s perfect.”
In response to the increased demand for oxygen supplies following the 2020 pandemic and subsequent rise in respiratory-related conditions, Jacksons Fencing completed a key project in 2024 to safeguard vital oxygen storage facilities at a pioneering UK hospital. Addressing the demand The pandemic highlighted the critical role of oxygen in treating patients, causing a surge in its use across hospitals. Some facilities even declared major incidents due to oxygen shortages, prompting a significant government investment of over £15 million to upgrade oxygen supplies and prevent future disruptions. As part of these improvements, many larger hospitals have started to feature on-site liquid oxygen storage facilities, where vast industrial tankers convert liquid oxygen to gas as needed. Securing essential resources Jacksons Fencing provided and installed a comprehensive security solution for a new oxygen storage compound Given the stringent safety requirements associated with liquid oxygen due to its extremely low temperatures, precise pressure needs, and related fire and explosion risks securing and managing these supplies is paramount. To address these needs, Jacksons Fencing provided and installed a comprehensive security solution for a new oxygen storage compound. Robust fencing solutions with invisible screen The installation includes 38 meters of Securi-Mesh® fencing, standing at a robust height of 2.4 meters. This fencing is mounted on concrete hardstanding and is complemented by two cantilever sliding gates and a single-leaf pedestrian gate with a push pad exit and key entry. Securi-Mesh fencing features a tightly woven mesh pattern designed to deter climbing attempts, and its small apertures significantly improve resistance to cutting. Additionally, the mesh provides an ‘invisible screen’ effect that allows for effective surveillance without obstructing views, facilitating quick issue identification. Space efficiency and secure gating Unlike traditional swing gates, these gates slide parallel to the fence line, requiring minimal space The cantilever sliding gates installed are particularly well-suited for the restricted space in front of the facility. Unlike traditional swing gates, these gates slide parallel to the fence line, requiring minimal space both in front of and behind the fence. This design not only maximizes space efficiency but also enhances security with quick operational cycles, allowing for faster vehicle and goods transit, reducing the time the gates remain open, and minimizing security risks. 25-year guarantee with reduced maintenance Furthermore, the absence of ground tracks for the cantilever gates reduces maintenance needs by preventing issues related to debris or track damage, causing fewer repairs, and reduced downtime. In addition to these features, the fencing and gates are backed by a 25-year guarantee, ensuring long-term durability and minimal maintenance. Barbican® vertical bar fan panel The green polyester powder coating chosen for the fencing provides extra corrosion resistance The green polyester powder coating chosen for the fencing provides extra corrosion resistance and contributes to lower long-term costs for the hospital. Sections of the fencing, installed at varying heights, are further secured with a Barbican® vertical bar fan panel, which offers both a physical barrier to intrusion and a visual deterrent. Oxygen storage facility security Peter Jackson, Managing Director, of Jacksons Fencing comments on the success of the project, "Contributing to this vital project, enhancing the security of oxygen storage facilities at a UK hospital, is a significant achievement." "The pandemic highlighted the crucial role of oxygen, we must safeguard these resources effectively." Securi-Mesh® fencing and cantilever sliding gates "The integration of our Securi-Mesh® fencing and cantilever sliding gates reflects our commitment to providing both superior protection and operational efficiency." "By addressing the specific security needs of these vital resources, we help ensure that hospitals can focus on delivering high-quality patient care without disruption.”
About 20 miles northeast of Battle Creek, Michigan, and 30 miles southwest of the state capital of Lansing lies the bucolic city of Olivet, population 1600. Olivet may be small as far as municipalities go, but it knows how to think big when it comes to protecting the safety of the 1250 students enrolled in its three Olivet Community Schools. Schools of Choice program That may sound like a large student body for a town its size until they realize that the district serves a geographic area of over 100 square miles and communities that rely on an economy based primarily on farming, light industry, and the area’s two largest employers – the University of Olivet and the schools themselves. As a participant in the state’s Schools of Choice program, the district can accept pupils from neighboring areas, which make up roughly 33% of the Olivet Community Schools population in addition to the city’s resident students. John Mertz Mertz's career has progressed from teaching to roles such as Director of Instructional Services Guiding school operations is Superintendent John Mertz. With 33 years of public education experience in Michigan, his career has progressed from teaching to roles such as Director of Instructional Services, Assistant Superintendent, and now Superintendent. This is his fifth year in Olivet. “The interesting thing about being a school superintendent is that there are several things I didn’t know were going to come with the job and never received training on,” says Mertz. “And one of the biggest ones is school safety and security.” Video monitors He recalls a Saturday night when he was doing some work in his office while his daughter was attending a school event that evening. When he happened to look up at the large video monitors behind him displaying the schools’ camera feeds, he was surprised to see a lot of people coming and going during that hour. “I thought, who are all these people? Where are they going?” Mertz says when he looked a bit closer, he saw there were kids with backpacks and baseball bats who were all heading to the middle school gym, where they held practice. “I didn’t have any idea how they got in,” he says. “It turns out the coaches had a key that they used to unlock doors whenever they needed to after regular hours.” Unfortunate events He adds that it’s an unfortunate but common fact that many school districts have far more keys in circulation than have been officially issued. “It can be difficult to figure out where the keys are coming from." "Are they being shared, or copied? For me, that was a huge aha moment. I found myself saying we’ve got to do something about this; we’ve got to make sure we’re controlling who is getting into our buildings, for what purpose, and when.” Communication and transparency Mertz and the district to push for major improvements in the school’s safety and security system That’s what compelled Mertz and the district to push for major improvements in the school’s safety and security system. But Mertz says that before the district could even consider who to work with and what to purchase and install, his team had to make its case to the schools’ stakeholders – the staff members, the board of education, and parents. “The community needed to understand the rationale that warranted the upgrades. It’s all about communication and transparency.” Updating the access control systems “The biggest changes we identified meant replacing our outdated and often grainy security cameras with sharper, more advanced units and stepping up the capacity and capabilities of our access control system so we could better schedule and manage access at perimeter doors and for activity spaces." "But what was especially crucial was adding digital access control to our classrooms, which was a priority for further enhancing student and teacher safety.” Fiber connections and wireless networks Mertz adds that before deploying advanced cameras and access control, upgrades to fiber connections and wireless networks also had to be made. “So, we started reaching out to security system integrators and experts in access control like ASSA ABLOY to start figuring out what technology was out there that would be the most advantageous for our district. It was quite a journey.” Relationship, reliability, and response time Ultimately, Mertz says the district issued an RFP. “Along with assessing what we needed and increasing our knowledge of the solutions available, we were also concerned about the kind of partnerships we were going to form with the companies that would be awarded the upgrade project." "We talked about the importance of the relationship, reliability, and response time. We wanted companies that could continue to provide support and be accountable if issues arose after the project was done.” Three key solutions Olivet Community Schools ended up choosing PDT of Byron Center, Michigan to be their systems integrator Upon completing their thorough vetting process, Olivet Community Schools ended up choosing People Driven Technology (PDT) of Byron Center, Michigan to be their systems integrator. PDT Account Executive Charlie Booth explains that gaining a full understanding of Olivet Community Schools’ requirements helped narrow the decision to three key solutions and organizations. Integrating cameras, access control, and analytics “We brought Genetec™ in and did a demo of their Unified Security Solutions platform that integrates cameras, access control, and analytics to make everything work seamlessly together,” says Booth. At the same time, he started talking with ASSA ABLOY Integrated Solutions Specialist David Hood who then facilitated a demo of the SARGENT IN100 Aperio® Wireless Lock. SARGENT IN100 Aperio® Wireless Lock “We chose the Aperio line because the Olivet classroom doors always needed to be online and communicating with Genetec in case global actions were needed to secure doors, like in a lockdown,” explains Booth. “Having IN100 electronic access control locks at each door means the facilities department now just issues keycards to staff instead of brass keys, making it much easier to manage credentials. For the video surveillance upgrade, we specified state-of-the-art i-PRO cameras.” 24/7 door monitoring Superintendent Mertz says, “The integration of the new cameras and access control solution with the Genetec platform and AI analytics allows us to monitor door activity 24/7." "It gives us a keen understanding of who is in the building and when.” He says that along with ensuring only those with card credentials have access, the system also alerts staff if a door has an issue such as a card reader/lock battery that needs replacing. ZeroEyes AI gun detection Mertz adds, “We also incorporated weapons detection software. We received a grant from the state for ZeroEyes AI Gun Detection." "And in a partnership with the City of Olivet, we obtained a grant for our first school resource officer. None of this would have been possible without upgrading our infrastructure, cameras, access control technology, and analytics nor without the support of our school and community stakeholders.” Complement security features Technology features i-PRO cameras district-wide, over a hundred SARGENT IN100 Aperio wireless access control locks Olivet Community Schools’ complement of security technology features i-PRO cameras district-wide, over a hundred SARGENT IN100 Aperio wireless access control locks for classrooms, and the Genetec Security Center unified platform. Christopher Dunn, Public Sector Account Executive for Genetec, further explains the value of his company’s solution, “One of the largest challenges Olivet faced was moving away from the fragmented system of the past where there was one platform for video and a separate one for the limited access control system they had." Human, vehicle, and threat detection "They needed to be able to harness the power of the technology at the edge that the new cameras offer and utilize it with applications that can detect things like the differences between human beings, vehicles, and potential threats.” He adds, “Because of how Genetec is structured and integrates so perfectly with other products, we’re able to bring everything into a ‘single pane of glass’, including analytics. That single pane of glass provides a dashboard that combines video and data feeds from multiple sources into a unified view.” Curb-to-core approach Dunn says that bringing everything together in one platform also eliminates the need for training on multiple systems, which was another highly important priority for Olivet Community Schools. According to David Hood, “ASSA ABLOY takes a curb-to-core approach when working with school districts, starting with the perimeter and then working inwards. Olivet Community Schools has followed that same approach. They have the perimeter protected with access control on every door along with video surveillance, and working inward to offices and classrooms, they now have integrated solutions throughout.” People Driven Technology Hood adds that collaborating with People Driven Technology and Genetec has been outstanding. “People Driven Technology understands our solutions and hardware, and they’re certified on our products." "That’s made installation and integration with i-PRO, Genetec, and analytics applications a seamless process for Olivet Community Schools.” An automatic classroom lockdown “It's all about student safety, staff safety, and community safety,” emphasizes Mertz. “When you have people in your facilities, putting in these extra measures buys extra time." "So, heaven forbid, if there ever is an incident, you're prepared for it, ready to react, ready to swing into action with the systems in place that are going to help you do that, including activating an automatic classroom lockdown if necessary. Safe and secure building “When you look at success, it all comes back to the district and the kids. Now I determine success on whether our kids are safe. Are they happy? Are they healthy? Are they in an environment where they feel comfortable? That's really what it's all about now, especially coming out of COVID." "You need to have kids feel like they're in a place where there are trustworthy adults around them, where the building is safe and secure, and where they feel comfortable to learn.”
HID®, a worldwide pioneer in trusted identity solutions, announced that Baiduri Bank, a member of Baiduri Bank Group and the largest conventional bank in Brunei Darussalam, has implemented the HID Approve™ powered by the HID Authentication Platform across its consumer and corporate banking platforms, offering a single trusted authentication source for customer identity. Protecting customer identity "HID is thrilled to partner with Baiduri Bank to enhance its authentication and security infrastructure," said Lena Abdelahad, VP - Authentication Business Unit, HID. Lena Abdelahad adds, "We are committed to providing solutions that help protect banking customers’ identities all while reducing complexity as part of our dedication to delivering innovative solutions that meet the evolving needs of the industry." Balance between technology and customer experience "Banking is about people and meeting their needs, and at Baiduri Bank, we believe in striking a balance between the use of technology and customer experience," said Simon Hansman, Chief Information Officer of Baiduri Bank. Simon Hansman adds, "Baiduri Bank is proud to be the first bank in Brunei to leverage cloud technology to enhance our customers’ experience." Cloud-based authentication infrastructure HID Approve helps to reduce complexity with standards-based, scalable solutions covering the entire authentication journey Baiduri Bank realized an opportunity to undertake a digital transformation to help ensure the delivery of a smooth customer experience, which entailed updating its digital banking software to build upon a cloud-based authentication infrastructure. Baiduri Bank integrated HID Approve powered by the Authentication Platform across its consumer and corporate banking platforms. Offering a single trusted authentication source for customer identity, HID Approve helps to reduce complexity with standards-based, scalable solutions covering the entire authentication journey. Customizable security policies HID Approve provides mobile authentication and transaction signing with robust security protocols, hardened through standards-based cryptography. Featuring customizable security policies to protect communication channels, HID Approve is backed by rigorous third-party security testing and independent audits. HID Approve helps to deliver a more seamless user experience, simplified compliance, flexible deployment, and lower cost of ownership compared to traditional solutions. Seamless user experience "Given its experience with such projects and because HID Approve was already integrated with our core banking platform of interest, we felt HID was the best vendor for us," said Henry Voon, Head of IT Systems, Baiduri Bank. Henry Voon adds, "HID’s global brand recognition gave us confidence. The level of support HID provided, especially for implementing cloud-based projects, was key for our smooth launch." HID Authentication Platform Baiduri Bank’s corporate and consumer channels are secured with the rigorously tested and highly scalable HID Authentication Platform. The multi-channel, multi-tenant authentication offering is a perfect fit for Baiduri’s needs thanks to HID’s ability to integrate one solution across its whole business.
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure, and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. Mobile-ready HID Signo readers The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over two years by a specialist security installer, Scottish Communications Group. In addition, the University has purchased 10,000 HID Mobile Access licenses to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. Safe and secure modern system “We wanted a modern system which is safe, secure, and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. “Complying with forthcoming legislation was also another important project requirement." "With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we must protect to ensure everyone is safe. The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” University of Dundee A thriving institution with ambitious development plans, it is currently building a new £40 million facility The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering, and life sciences. Based in the heart of the city, it is home to over 16,000 students, and 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organizations flexible laboratory, meeting, and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. Touchless smartphone entry The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP [Open Supervised Device Protocol] and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers thereby speeding up the rollout. University's challenges Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week when some 2,500 – 3,000 undergraduate and postgraduate students enrolled. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Mobile Access Shifting to HID Mobile Access completely changes this and delivers wireless credentialling Shifting to HID Mobile Access – which utilizes cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licensing, allocation of credentials, setting of building access rights, and validating or revoking of IDs – all of which are done virtually and remotely. Mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Dual system approach While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach is to operate a dual system. “We recognize that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO DTC4500e printers FARGO range integrates easily with the AEOS software so that Student Services staff can issue physical IDs Given RFID cards are still required, the University of Dundee utilizes its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. “HID Signo readers are going in now across the main buildings including the Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. Encryption, communications, and authentication standards “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications, and authentication standards." "Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” Motorola MOTORTRBO Ion smart radios In addition, the Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems, and CriticalArc Safezone® App, security staff need to carry only a single device to fulfill their duties.


Products


Round table discussion
There is no shortage of threats facing security professionals, including some that are new and emerging. Understanding various new threats allows individuals and organizations to take proactive steps to protect themselves, but the first step is to identify what those threats are. Early detection of threats can minimize the impact of a successful attack, whatever the vulnerability at issue. We asked this week’s Expert Panel Roundtable: What new and emerging threats will physical security professionals need to be prepared for in the future?
Suddenly, artificial intelligence (AI) is everywhere. The smart technology brings a range of benefits to our lives, from streamlining everyday tasks to making scientific breakthroughs. The advantages of AI and machine learning (ML) also include automating repetitive tasks, analyzing vast amounts of data, and minimizing human error. But how do these benefits apply to the physical security industry, and is there a downside? We asked this week’s Expert Panel Roundtable: What are the benefits, and drawbacks, of using artificial intelligence (AI) in physical security?
The design of buildings encompasses many elements, from the practical to the aesthetic. Well-designed buildings should be functional, and they can also be beautiful and inspiring. But can security systems and building design coexist and complement each other? We asked this week’s Expert Panel Roundtable: How does building design impact physical security systems -- and vice versa?
White papers

The Security Challenges Of Data Centers
Download
Security Practices For Hotels
Download
Access Control System Planning Phase 2
Download
Honeywell GARD USB Threat Report 2024
Download
Access Control System Planning Phase 1
Download
How To Lower Labor Costs When Installing Video Surveillance
Download
Total Cost of Ownership for Video Surveillance
Download
The Truth Behind 9 Mobile Access Myths
Download
5 Surprising Findings From OT Vulnerability Assessments
Download
Guide For HAAS: New Choice Of SMB Security System
Download
Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Integrating IT & Physical Security Teams
Download
Top 7 Trends To Watch In The Physical Security Industry
Download
How Video Technology Is Transforming Loss Prevention, Operations, And Customer Experience In The Retail Sector
Download
2024 Trends In Video Surveillance
Download