Technology & Trends - Electronic lock systems
With the rise of organized retail crime (ORC) making headlines, retailers are grappling with the dual challenge of safeguarding both their staff and store assets, while addressing the economic pressures that impact profitability and consumer demand. RFID technology The key lies in identifying effective solutions to counter the current surge in ORC, enabling retailers to secure their vulnerable staff and protect inventory for paying customers. Technology plays a crucial role in supportin...
Amidst the challenges of a prevailing economic downturn, the retail sector finds itself grappling with an unparalleled rise in incidents of shoplifting, theft, and burglaries. The disconcerting scenes witnessed on London’s Oxford Street in August 2023, where crowds gathered, looting as many stores as possible, sent shockwaves across the nation’s retailers. This alarming surge in retail crime has put retailers on high alert, as they contend with a rising tide of security concer...
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realize, however, that some of these traditional security measures are becoming...
Mass attacks continue to lead the news far too often. All are horrific and disturbing, but the heartbreaking tragedies that have unfolded on school campuses touch us the deepest and have the most profound effects on our communities. NTAC statistics According to a January 2023 report from the United States Secret Service National Threat Assessment Center (NTAC), K-12 events accounted for 6% of all mass attacks in public and semi-public spaces between 2016 and 2020. 6% may strike some as being...
We work with and buy from “middlemen” all the time, yet the term remains loaded with negative connotations. It’s telling that the term remains gendered, no one has tried very hard to normalize the term “middleperson” in the same way as “chairperson” or “police officer.” Why? It’s easy to see a middleman as an inconvenience, someone who skims profit off the top while offering no real value to the end customer. Think of the second-hand c...
With Black Friday on the horizon and shops and warehouses busier than ever, Elliot Roddy, Operations Director at CDX Security Group has shared some tips on how to keep the must-have gift items safe and secure: Regular monitoring and CCTV, Stock control and audits, and Partner with a trusted security firm. Staying alert with the must-have items Each year, we see certain items gain popularity and become the year's must-haves. This year, social media and the rise of TikTok have accel...
In the past five years, the retail landscape and the relationship between consumers and businesses has shifted drastically. It wasn’t too long ago when shopping at malls was considered a family activity and consumers shopped at local stores where they knew and interacted with sales personnel. Today, however, malls and interactions with employees are relics that accurately portray the way retail used to work. Retail companies have shifted their consumer model to focus on the online market...
The outlook for advancements in door security solutions is proving to be an extension of the positive trends that have emerged over the past few years and that continue to evolve in exciting new ways. That’s a good sign as we make our way along the road toward an ever-safer world. Improvements in a hybrid workforce Here’s what we’re seeing: More and more companies are rethinking the office space and how electronic access control (EAC) security and data can help better s...
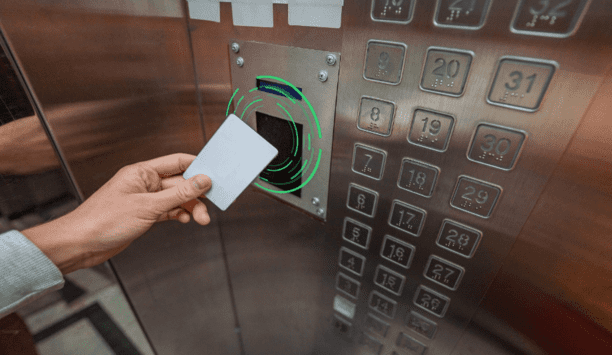
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from building entry to printer access. The right RFID reader can help reduce complexity by migrating diverse older technologies into a single convenient solution. Ways RFID Works Radio-frequency identification (RFID) and smartphone-based credentialling systems using Bluetooth® Low Energy (BLE) or Near-Field Communication...
The world around us is full of technological innovation. Smart locks are commonplace in our homes and control access to buildings, but when it comes to industrial locking and access control for equipment cabinetry, options can seem limited. Equally, there’s not enough accessible information to act as a guide. The development of new technologies and cabinet capabilities feels as though it is being held back. But that doesn’t have to be the case. Common problems are seen across the l...
More and more business security practices are going digital. Mechanical keys are still the backbone of most corporate security plans, and it can be very expensive for companies to switch to electronic access control on a large scale. Therefore, enterprises need to choose the most suitable access control system. What is key management? Key management is the process of protecting, tracking, and scheduling mechanical keys. Why is this important? Because the key carries access to sensitive locatio...
In the field of access control, face recognition has come a long way. Once considered too slow to authenticate people's identities and credentials in high traffic conditions, face recognition technology has evolved to become one of the quickest, most effective access control identity authentication solutions across all industries. Advancements in artificial intelligence and advanced neural network (ANN) technology from industry leaders like Intel have improved the accuracy and efficiency of fa...
Schools were never designed and built with social distancing in mind. So it’s perhaps not surprising that as children returned to schools for the autumn term this year, the prospect of outdoor classes and assemblies was mooted in the media and by the Government. Many in the education sector are making the case that, should there be further COVID-19 outbreaks, in the coming months, it would be better to utilize outside space, rather than resort to closing schools. In the COVID-19 era, head...
Most consumers are enjoying the convenience brought by electronic locks. With the existence of electronic locks, people no longer need to be restricted by keys. There are a variety of unlocking methods and more convenient remote control unlocking options. Suppose, you are going on vacation, and with the presence of an electronic lock, you can easily enter your house with your babysitter, without a spare key. Of course, not only smart homes, but also some infrastructure and commercial buildings...
Household adoption of smart home systems currently sits at 12.1% and is set to grow to 21.4% by 2025, expanding the market from US$ 78.3 billion to US$ 135 billion, in the same period. Although closely linked to the growth of connectivity technologies, including 5G, tech-savvy consumers are also recognizing the benefits of next-generation security systems, to protect and secure their domestic lives. Biometric technologies are already commonplace in our smartphones, PCs and payment cards, enhan...
Access control and management of trusted identities are the building blocks of security, safety, and site management policies for many businesses and organizations. The current pandemic has compounded this with the introduction of new policies and regulations, particularly around social distancing and contact tracing. Most organizations will have some form of legacy access control in place, ranging from the most simplistic options, such as locks and keys, to technology-based systems. The issue...
In daily work and life, various locks have always played the role of protecting asset safety. In different usage scenarios, the most appropriate lock must be selected to maximize benefits. In the past applications, the difficulties encountered by managers are as follows. Unlocking authority is difficult to control, unclear access records, emergency unlocking, and troublesome upgrade and installation. Through the following points, how the key-centric access management system solves such problems...
Whenever you say the word “security” in today’s world of digitalization and technology, minds immediately jump to online security. Encryption, passwords, and website security are all common areas of concern for today’s security teams – so much so that we often pass over physical security installations entirely. But we shouldn’t, because contrary to popular belief, security doors aren’t just for banks and safes. High-security doors are deployed and used...
The 2020s will be a wireless decade in access control, says Russell Wagstaff from ASSA ABLOY Opening Solutions EMEA. He examines the trends data, and looks beyond mobile keys to brand new security roles for the smartphone. The benefits of wire-free electronic access control are well rehearsed. They are also more relevant than ever. A wireless solution gives facility managers deeper, more flexible control over who should have access, where and when, because installing, operating and integrating...
With the continued rolling back of COVID restrictions in the UK, there is a palpable sense of relief. A mixture of mass vaccinations, widespread testing, and track and tracing of the infection is helping to enable a healthy bounce back for businesses – with secure access control taking an important role in facilitating this. However, rather than just being a reaction to the wake of the pandemic, there is every sign that the economy, and consequently the security sector as well, are both r...
Automatic gates remain an increasingly popular security choice for family homes, business premises or public buildings – anywhere that full control over access is needed. While there is much to consider for installers when advising clients on the right solution for their property, from the size, weight and cost of a gate system, it’s useful to be aware of the latest developments in the market, as this can help to find the right option to fit their needs. The need for speed Gates c...
As the vaccine roll-out proceeds, people across the UK are counting the days until we can get back to some kind of ‘new normal’. Just as we’ve seen in education and healthcare, the return to the workplace and other public spaces will be accompanied by enhanced sanitization and social distancing measures. To make the return as swift and safe as possible, those of us involved with managing, building and constructing buildings should consider how we can help facilitate and suppor...
In part one of this feature, we introduced the shotbolt – a solenoid actuator – as the workhorse at the heart of most straightforward electric locking systems. Shotbolts remain at the core of most sophisticated electric locking solutions as well. But they are supplemented by materials and technologies that provide characteristics suited to specialist security applications. Here we look at some more demanding electric locking applications and contemporary solutions. Preventing forced...
A defibrillator can save the life of a person suffering from cardiac arrest – but it is most effective when used in the first few minutes of the patient collapsing. Studies have shown that a shock given within the first three minutes provides the best chance of survival and even one minute of further delay can substantially lower the chances of recovering. Public Access Defibrillators (PADs) were created to allow untrained members of the public to deliver life-saving treatment in those pr...
The experience of the COVID-19 pandemic has made us all more conscious of who is coming and going from our property. Whether it is a family home, business premises or public building, property owners want full control over access for protection and peace of mind. As a provider of access control technologies, we are seeing a growing demand for automated gates with a variety of access control systems. There are a number of considerations that buyers need to make when investing. And as an installe...
The safeguarding of premises through the monitoring of entrance and exit points has traditionally been a very manual aspect of security. Human operators have been relied on to make decisions about who to admit and deny based on levels of authorization and the appropriate credentials. The access control business, like many industries before it, is undergoing its own digital transformation But the access control business, like many industries before it, is undergoing its own digital transformati...
There’s no question that the popularity of Do-It-Yourself (DIY) security and home automation products is on the rise. The reasons for the growth in DIY sales are numerous, including increased awareness of home automation products, fast set-up, limited (if any) installation costs, and interoperability with other smart security products. In fact, with the parallel rise of smart home hubs like Alexa and Google Home, many people are opting to attempt the set-up of smart home devices without an...
The extensive analysis and discussion preceding any decision to implement a new physical security solution – whether it’s hardware, software or a combination of both – often focuses on technology, ROI and effectiveness. When it comes to deciding what type of security entrances to install at your facility, you will almost certainly also consider the aesthetics of the product, along with throughput and, if you’re smart, you’ll also look into service concerns. Each o...
It’s not surprising that people are nervous about the security of newer technologies, many of which are part of the Internet of Things (IoT). While they offer greater efficiency and connectivity, some people still hesitate. After all, there seems to be a constant stream of news stories about multinational corporations being breached or hackers taking control of smart home devices. Both of these scenarios can feel personal. No one likes the idea of their data falling into criminal hands. A...
It amazes me how in a few short years security systems have gone from simple, dumb cameras witnessing events to intelligent eyes, ears, speech and touch solutions that boost situational awareness far beyond human capabilities. It seems the only senses missing from the equation now are smell and taste. And who knows, someone might be working on those in a lab somewhere right now. But what’s really fascinating to me is how the Internet of Things (IoT) has opened a world of possibilities for...
Browse expert commentaries
Related videos
Time Challenge: Installation Of Battery Powered Aperio Cylinder
ABLOY UK : ABLOY Critical Infrastructure
IDIS Launches Efficient AI-Powered Security Camera Range
Verkada TD52 Cloud-Based Video Intercom
exacqVision IP08-64T-R1XW-E X-Series 1U Rdnt IP NVR 64TB RAID5 Windows OS with 8 IP Ent Lic
Climax Technology TouchPanel-3 7” Color Graphic Touchscreen Panel
Multi-Residential Access Management And Security
DownloadGuide For HAAS: New Choice Of SMB Security System
DownloadPrecision And Intelligence: LiDAR's Role In Modern Security Ecosystems
DownloadHikvision: Solar Powered Product Introduction + HCP
DownloadGunshot Detection
Download