Wireless security
Exabeam, a global cybersecurity pioneer that delivers AI-driven security operations, announced Investigation Timelines™ within the Exabeam Search™ application, a powerful new capability on the Exabeam Security Operations Platform™. An industry-first, Investigation Timelines break down silos and simplify investigations for security analysts with integrated cross-platform workflows. Designed to empower security teams amid growing threats and skills shortages, this innovative cap...
VIPRE Security Group, a global pioneer and award-winning cybersecurity, privacy, and data protection company, released its Q1 2024 Email Threat Trends report, based on an analysis of 1.8 billion emails. The findings reveal the evolving landscape of email-based threats and emerging tactics malicious actors are employing. The US, UK, Ireland, and Japan top the spam sources list. The report identifies the US as the top source of spam emails globally, followed by the U.K., Ireland, and Japan. The U...
A wider group of customers can now experience the benefits of Dicentis Hybrid Meetings with the latest rollout of this cloud-hosted end-to-end hybrid conference solution. The technology update is part of an ongoing mission of Bosch Building Technologies to meet the rapidly evolving needs of the modern professional conferencing environment. Hybrid meeting environment Dicentis Hybrid Meetings is a fully native end-to-end solution that ticks all the boxes for highly efficient, legally compliant...
Sweden's Södra Älvsborgs Rescue Service Association, (SÄRF) has increased its deployment of LiveU's real-time video transmission solutions, adding recording capabilities to create a complete 'live and store' video set-up for situational awareness and use in training scenarios. This significantly strengthens its decision-making, responsiveness, and preparedness to deal with fires and accidents. Headquartered in Boras, the regional rescue organization runs rescue services in...
The British Security Industry Association (BSIA) has announced its regional security personnel winners for 2024, recognizing frontline security officers across the United Kingdom for their commitment to keeping people, property, and places professionally protected. The BSIA’s regional security personnel awards are part of the Association’s British Security Awards, which will be held from 2024 at the Royal Lancaster London. All regional winners will now go forward as national finalis...
Financial landscape is growing expeditiously, offering new opportunities of economic and commercial growth. And experts suggest that facial recognition can be uniquely profiting to lever and protect this growth. RecFaces, an international facial recognition software vendor, is excited to announce their upcoming webinar focusing on the transformative role of Facial Recognition Systems in the Banking Sector. The webinar, titled ‘Facial Recognition In Banks: A Win-Win Game To Improve Securi...
News
Milestone Systems, a global pioneer in video technology, is at the forefront of the video security industry, emphasizing responsible technology innovation across its operations. The company will host this free, one-day event on May 7 in Toronto. Geared to IT pioneers and security professionals, the day will feature engaging presentations from Milestone's technology partners across key industries such as education, healthcare, city surveillance, and hospitality. Attendees will gain insights into the latest developments in AI technologies, cloud video strategies, and Milestone's newest product offerings. Reshaping the future of security A keynote session from renowned AI expert Steve Brown promises to be a highlight of the event A keynote session from renowned AI expert Steve Brown promises to be a highlight of the event. Brown, a former executive at Google Deepmind and Intel, and an advisor to Fortune 100 pioneers on how to innovate with AI, will share his insights on how artificial intelligence is transforming video technologies and reshaping the future of security and business operations. "We are excited to bring together security professionals from across Canada to explore the cutting-edge video technologies that are shaping the future of our industry," said Peter Lintzeris, Director of Sales, Canada, at Milestone Systems. "The Toronto XPerience Day offers a unique opportunity to learn from experts, network with peers, and discover how Milestone's open platform solutions can help organizations optimize safety and efficiency." Video management innovations The event will be held at Steam Whistle Brewing in the heart of downtown Toronto. Following the day's presentations, attendees are invited to network with fellow security professionals and speak one-on-one with Milestone experts during a relaxed social hour. "Milestone is committed to empowering our partners with the knowledge and tools they need to succeed in today's fast-paced security landscape," said Lintzeris. "We look forward to an engaging and informative event, and to continuing to support the Canadian security community with our open platform video management innovations."
Quanergy Solutions, Inc., continues to gain momentum since reformulating its business operations to focus exclusively on physical security and business intelligence applications. Quanergy’s groundbreaking 3D LiDAR (Light Detection and Ranging) solutions provide users with real-time data to detect potential threats and abnormalities for immediate remediation with unparalleled levels of precision and range in virtually any environment or operating conditions. Accelerate Quanergy’s growth Quanergy has recently announced new-generation sensors to track people and vehicles across every zone of protection from the perimeter to close interior locations, dramatically increasing security and operational efficiency. The new expanded portfolio will further accelerate Quanergy’s growth in existing and new markets, which is forecast to exceed three million sensors representing approximately $6 billion USD in revenue by 2030 according to an independent study conducted by ABI Research. Quanergy projects year-over-year growth of approximately 300% in fiscal 2024 supported by the expansion of the company’s new product offering, and sales and marketing operations across the U.S. and in select regions in the EU and APAC. Quanergy 3D LiDAR solutions Quanergy 3D LiDAR solutions are driving the next generation of physical security solutions" “Public and private organizations alike need to urgently address increasingly sophisticated threats while improving their operational and capital efficiency,” said Enzo Signore, CEO, Quanergy. “Quanergy 3D LiDAR solutions are driving the next generation of physical security solutions with 20 times higher accuracy at less than half the cost of legacy technologies.” An increased market demand for cost-efficient and accurate Perimeter Intrusion Detection (PID) solutions continues to drive high interest in Quanergy 3D LiDAR solutions. This applies not only for specialized critical infrastructure applications such as energy and water utilities, data centers, airports, and various government installations, but also for mainstream physical security and business intelligence applications at corporate enterprises, warehousing, and logistics operations, and so much more. Future business intelligence applications Quanergy also recently entered a partnership with Convergint A recent deployment of Quanergy 3D LiDAR is at San Jose Water for Enterprise Security Risk Management (ESRM), initially for automated Perimeter Intrusion Detection and to generate data for future business intelligence applications. Quanergy also recently entered a partnership with Convergint, a global pioneer in service-based systems integration to design, engineer, and implement physical security solutions that provide early detection with hyper accuracy and faster response times. “Quanergy’s solutions have been chosen by some of the largest data centers, utilities and distribution centers in the world, and we are committed to helping customers around the globe benefit from the power of 3D LiDAR.” continued Signore.
Hikvision, a world-pioneering manufacturer and supplier of security products and solutions that deliver the ideal combination of high performance and extreme value, will proudly unveil its Solar Solutions lineup at a May 23 webinar, showcasing this unprecedented solution to security challenges in standalone sites and hard to reach remote locations. Attendees will receive a 50% discount on the 4 MP Kit DS-2XS2T47G1-LDH/4G/C18S40 when purchased within 30 days of the webinar. Solar Kits with ColorVu technology “From highly affordable 4 MP Solar Kits with ColorVu technology to options with 8 MP resolution and features like License Plate Recognition, Hikvision is bringing unmatched technology to remote and hard-to-reach locations, everywhere from rural farms to urban parking lots,” said John Xiao, Vice President of Marketing, Hikvision USA. Unlike rival products, Hikvision offers a complete system, ready to deploy, with all parts included “In an era where sustainability meets innovation, Hikvision is driving the charge, with competitive technology that is easy to deploy and ready to solve end-user challenges.” Unlike competitor products, Hikvision offers a complete system, ready to deploy, with all components included. It is easy to select the best model and install it, and the entire system has been tested for safety and reliability. Six models with a broad feature Hikvision’s Solar Solutions include six models with broad feature sets for various applications: The 4 MP ColorVu Solar-Powered Security System features 24/7 full-color with ColorVu technology, human detection, and two-way audio for real-time deterrence. The 4 MP Motorized Varifocal Bullet Solar Kit is available in two models: the DS-2XS6A47G1-IZS/C36S80 2.8-12 mm (focal length/FOV) and 8-32 mm. Both feature an 80-watt solar panel and 360 WH chargeable lithium battery. Other technology includes WDR, deep-learning human and vehicle target classification, smart battery management, and a high-capacity 1TB built-in SSD. The 4 MP ANPR License Plate Recognition (LPR) Bullet Camera Solar System is available in two versions: 2.8-12 mm focal length/FOV and 8-32 mm. Each one boasts all the features of the motorized varifocal model above delivering valuable license plate recognition and road traffic controls where wired network and electric supply lines are impractical or otherwise impossible. The 8 MP ColorVu Fixed Bullet Solar-Powered Camera System has 24/7 colorful video with ColorVu, WDR technology, deep-learning human and vehicle target classification, and smart battery management. It boasts a larger 80-watt solar panel and 360 WH chargeable lithium battery. By harnessing the power of the sun, Hikvision empowers businesses to improve ROI, eliminate power cords, and bid farewell to internet cables. The Solar-Powered Camera Kits deliver full-color video security, anytime, anywhere, without the need for a traditional power supply or internet connection.
Sensera Systems, a provider of solutions for real-time jobsite intelligence, announced the launch of its complete site security solution. The full solution includes the compact solar-powered SiteWatch Pro3 camera, the newly released TalkDown deterrence kit, and professional monitoring services all enabled through Sensera’s SiteCloud software. Sensera Systems now offers comprehensive jobsite security coverage and meets risk compliance for projects of any size. Sensera's energy-efficient solution “Construction costs continue to rise across the board — and tools, materials, and equipment must be protected on the jobsite," said Robert Garber, CEO Sensera Systems. He adds, "General contractors and project managers need the power of jobsite intelligence to meet builder's risk insurance requirements and give their customers peace of mind. Sensera Systems’ energy-efficient solution, complemented by our cloud-based technology, provides contractors with the simple-to-deploy monitoring and security they’ve been asking for." Sensera Systems’ complete security solution Sensera Systems’ skilled security monitoring gives structure site experts confidence According to industry estimates, construction theft costs hundreds of millions of dollars a year. Furthermore, fluctuating material costs and evolving project complexity continue to stress builders’ risk insurance policies, pioneering to rising premium costs. As a result, site security, real-time site monitoring, and verified security dispatch have become immediate priorities for construction professionals. Sensera Systems’ complete security solution brings together detection, deterrence, and response in one flexible, reliable, and affordable offering. This means simplified site coverage and a lower cost of implementation for contractors, eliminating complexities that can result from patching disparate security features together. Sensera Systems’ professional security monitoring gives construction site professionals confidence in protecting their assets while meeting builder’s risk insurance requirements. Benefits of Sensera Systems’ complete site security Sensera Systems’ complete site security offering delivers the following benefits to customers: Complete monitoring support through the combination of video, audio, and automation technology alongside human interactivity. Sustainable construction practices through solar power, preventing the need to run costly trenches along a site for power. Flexibility and portability through simplified setup, requiring no professional installation of cameras during construction. Central command and control through integration with SiteCloud. Reduced dispatch costs through thermal sensing, threat verification, and TalkDown deterrence.
Barracuda Networks, Inc., a trusted partner and major provider of cloud-first security solutions, announced that Neal Bradbury has been elevated to the role of Chief Product Officer. In this new role, Neal will lead a unified product, engineering, and advanced technology team to steer the vision for Barracuda’s comprehensive cybersecurity platform and drive customer-centric innovation across the entire portfolio. The platform is designed to protect customers across all attack surfaces including email, networks, data, and applications. Neal’s leadership “Neal’s business leadership skills and his deep understanding of our products, technology, business processes, and market strategy make him uniquely positioned to lead our product organization and guide our platform strategy as Chief Product Officer,” said Barracuda President and CEO, Hatem Naguib. Hatem Naguib adds, “I’m confident that under Neal’s leadership, we will continue to find new ways to meet customers’ evolving business needs for scalable security and help our partners to safeguard their customers' SaaS applications, prioritize data protection, and improve efficiencies in the face of ever-evolving threats.” Roles in operations and technical support Neal has been with Barracuda for nine years, most recently as the SVP of Barracuda’s Managed Service Provider business. In this role, Neal led all functions, including product development, sales, and marketing. Before joining Barracuda, Neal worked at Intronis, which he co-founded in 2003. Between 2003 and 2013, Neal served as Vice President of Systems Engineering before moving on to a succession of roles in operations and technical support. In 2013, Neal became Vice President of Channel Development, where he was part of the team that led the company to a successful acquisition by Barracuda in 2015.
Intelligent power management company Eaton participated in The White House Office of the National Cyber Director’s Convening on Cyber Workforce event on April 29 to underscore its commitment to cybersecurity training across industries. The company’s vice president of engineering and technology, Luiz Fernando Huet de Bacellar participated in the roundtable discussion with U.S. business, government, and community pioneers. Eaton’s multipronged efforts The need for cybersecurity professionals is projected to grow by 32% by 2032 and Eaton’s multipronged efforts are strengthening the talent pipeline for the cybersecurity workforce. With more than 27,000 employees in the U.S., Eaton provides in-depth cybersecurity education for its workforce across all levels of its business to help customers build safer, more cybersecure electrical networks. Eaton is expanding its U.S. manufacturing and providing cybersecurity training for new employees Further, Eaton is expanding its U.S. manufacturing and providing cybersecurity training for new employees; the company announced more than $200 million in manufacturing investments and the addition of over 800 jobs in Texas and Wisconsin in 2023. Long-running Eaton collaborations with pioneering universities and industry organizations are attracting and preparing the next generation of cybersecurity professionals. Cybersecurity education “As digital threats continue to evolve and proliferate, and critical systems become more connected and digitalized, more skilled cybersecurity professionals are needed across every industry and sector,” said Luiz Fernando Huet de Bacellar, PhD, Eaton’s vice president, engineering and technology. “At Eaton, we believe developing cybersecurity professionals is essential to ensure a safe and secure future. We’re taking steps within and outside of our organization to instill cybersecurity education at every level to create trusted environments." Cybersecurity education and research Eaton has contributed over $460,000 to support collaborative cybersecurity research and education The company contributed over $1 million to provide real-world cybersecurity experience for students at the Eaton Cybersecurity SAFE (Security Assessment and Forensic Examination) Lab at Rochester Institute of Technology (RIT) and will invest more than $500,000 over the next three years to facilitate ongoing education and training at RIT’s ESL Global Cybersecurity Institute. Eaton also collaborates with Carnegie Mellon University (CMU) to advance cybersecurity education and research. As a Partner Member of CMU's CyLab Security and Privacy Institute, Eaton has contributed over $460,000 to support collaborative cybersecurity research and education. Adoption of global cybersecurity Eaton's Product Cybersecurity Center of Excellence and secure-by-design philosophy ensure that its products meet rigorous cybersecurity and safety design standards. Over 95% of its product development teams have participated in cybersecurity training. The company's cybersecurity experts integrate cybersecurity processes and a secure development lifecycle into every stage of product development. Further, Eaton works closely with industry organizations such as the National Electrical Manufacturers Association (NEMA), the U.S. Cybersecurity and Infrastructure Security Agency (CISA), Microsoft, TechAccord, UL, the International Society of Automation (ISA) Global Cybersecurity Alliance (ISAGCA) and others to drive the development and adoption of global cybersecurity standards and technology breakthroughs. Perspectives virtual learning forum Cybersecurity Perspectives virtual learning panel has brought jointly more than 5,000 noted attendees The company’s Cybersecurity Perspectives virtual learning forum has brought together more than 5,000 registered attendees with experts from around the world for nearly five years to advance a more cybersecure future. Eaton is an intelligent power management company dedicated to protecting the environment and improving the quality of life for people everywhere. They make products for the data center, utility, industrial, commercial, machine building, residential, aerospace, and mobility markets. They are guided by the commitment to do business right, to operate sustainably, and to help the customers manage power ─ and well into the future. Trends of electrification and digitalization By capitalizing on the global growth trends of electrification and digitalization, they’re accelerating the planet’s transition to renewable energy sources, helping to solve the world’s most urgent power management challenges, and building a more sustainable society for people and generations to come. Eaton was founded in 1911 and has been listed on the New York Stock Exchange for more than a century. They reported revenues of $23.2 billion in 2023 and serve customers in more than 160 countries.


Expert commentary
For K12 education pioneers, embarking on a journey to upgrade security controls can present a myriad of questions about finding the best-fit solutions and overcoming funding hurdles. A majority of public-school districts today are faced with outdated infrastructure and security controls, requiring necessary upgrades. By addressing these concerns head on, schools will ensure a safer environment for both students and staff, mitigating risks posed by unforeseen physical and digital threats. Common K12 security pain points There’s no one-size-fits-all solution in school district security. School districts may have big plans to implement upgraded security systems but to set out on the right foot, pioneers must have a clear vision of their long-term strategy. When embarking on their security journey, education pioneers often wonder where to start and what exact steps are they need to be taking to identify and address weaknesses. Local K12 and government pioneers are promoting and mandating security assessments to uncover safety gaps on campuses and mitigate these risks with advanced technology solutions. Not only do assessments provide detailed, customizable roadmaps for district pioneers, but they also recommend technologies and funding opportunities to help close threat gaps. K12 school districts are mainly vulnerable to cyber-attacks due to the sensitive nature of student records In today’s climate, schools face a growing number of physical and digital security threats. From a cybersecurity standpoint, K12 school districts are particularly vulnerable to cyber-attacks due to the sensitive nature of student records. However, only one-third of these districts have adequate staffing to address threats effectively. In addition, according to a recent survey from Johnson Controls and Forrester Consulting, security decision-makers are having trouble receiving actionable insights. Nearly two-thirds of respondents said that they struggle to receive information from all necessary systems regarding their security threats. To gain more clarity into what school districts need in terms of security tools and threat mitigation, implementing system-wide monitoring and optimization can be invaluable. This approach enhances equipment and operational efficiency, while providing necessary resources and expertise for critical patch updates across all systems, strengthening their overall security posture. Achieving a well-rounded security program In the past few years, AI technology has emerged as a trending solution and is generating considerable attention. While the allure of implementing cutting-edge technologies is undeniable, it’s important to recognize that a robust security program hinges on solid access control. Access control technology provides administrators with the means to oversee and regulate entry into facilities, serving as the foundation for basic physical security. The technology helps administrators and staff control access to multiple areas from web-enabled devices, even during lockdowns which is crucial in emergency situations. School district pioneers should utilize available digital risk assessment tools to uncover threat areas Once basic security controls are in place, school districts must address their next set of security pain points and identify which solutions meet their specific needs. This involves identifying and prioritizing the highest need and most cost-effective investments that will have the greatest impact on enhancing security measures. To accurately determine which security solutions are needed for a specific environment, school district pioneers should utilize available digital risk assessment tools to uncover threat areas and determine levels of priority. By focusing on these priority areas, districts can allocate their resources and efforts where they are needed most, ensuring maximum effectiveness in mitigating risks and vulnerabilities. Securing funding before approaching deadlines A major challenge for school districts surrounding campus security is identifying and securing the necessary funding to implement solutions aligned with their goals. Leveraging available funding sources is critical, especially considering certain programs are approaching their deadline, like the Elementary and Secondary School Emergency Relief (ESSER) fund. Announced during the pandemic, ESSER is a funding program that has allocated nearly $190 billion in aid to U.S. public school districts to fund projects benefitting the well-being of occupants. Notable ESSER funding deadlines to keep in mind as the clock winds down include September 30, 2024 Notable ESSER funding deadlines to keep in mind as the clock winds down include September 30, 2024, when schools must attribute all of their funds to assigned contracts. Following this date, pioneers will need to complete all ESSER spending by January 2025 unless approved for an extension into March 2025. As ESSER wanes, school districts are acutely aware of the fiscal cliff in budgets through 2025. However, many states are ramping up grant funding to close the deficit gap. Administrators should become familiar with these grant opportunities at a local and state level. Get started on security plans The time for school district pioneers to act is now. While the safety and well-being of students and staff are always top priorities, it’s crucial to acknowledge that a lack of insight into necessary security upgrades and available funding options will leave districts behind the curve. Seizing the final months of ESSER funding presents an ideal window to address security pain points and build a safer future for K12 facilities. Looking beyond ESSER, pioneers must proactively seek out and leverage other funding avenues to help ensure the continuity of their security efforts and maintain a proactive stance in safeguarding healthy and safe educational environments.
Educational institutions worldwide increasingly rely on robust wireless networks to enhance academic pursuits, safety measures, and operational efficiency. The campus environment, a complex network of interconnected buildings, and the humans navigating them require innovative technologies to meet these diverse needs. The solution lies in a new wireless protocol that provides an ideal fit for the long-range, low-power connectivity requirements of educational campuses: Wi-Fi-certified HaLow. Wi-Fi HaLow: Wi-Fi HaLow, a new Wi-Fi certification released by the Wi-Fi Alliance in November 2021 and incorporating the IEEE 802.11ah standard, is optimized for the unique requirements of Internet of Things (IoT) applications. Wi-Fi HaLow provides a reliable and robust wireless solution that overcomes the trade-offs Its combination of long-range connectivity, low power consumption, advanced Wi-Fi CERTIFIED WPA3 security features, and the ability to connect more than 8,000 devices from a single access point makes the protocol a game changer for campus environments. Wi-Fi HaLow provides a reliable and robust wireless solution that overcomes the trade-offs between range and speed that limit the effectiveness of conventional Wi-Fi in the 2.4, 5, and 6 GHz frequency bands for campus applications. Robust, secure connections for access control Operating at sub-GHz frequencies, the Wi-Fi HaLow protocol's unparalleled ability to penetrate physical barriers and its advanced security features make it an ideal wireless technology for supporting access control systems throughout campuses. Credential systems for students, badge scanners, cameras, and dormitory door locks can work efficiently and securely in hard-to-reach locations, providing an interconnected and safe environment for the campus community. Enhancing safety through improved connectivity Body-worn cameras used by public safety officers can remain connected to the wireless local-area network The low-power and long-range attributes of Wi-Fi HaLow can play a significant role in strengthening campus safety systems. Body-worn cameras used by public safety officers can remain connected to the wireless local-area network (WLAN) or mobile router in their patrol vehicles even at a long distance, reducing the need to consume cellular data. Wi-Fi HaLow enables the development of robust wireless networks that can reliably support campus-wide, two-way video intercoms, potentially enhancing response times and safety measures. Streamlining outdoor equipment automation Outdoor equipment automation, such as irrigation systems, smart lighting, and robotic lawnmowers, can leverage Wi-Fi HaLow's power efficiency, and long-range and expansive coverage. Automation of these systems with such efficient wireless connectivity can lead to significant energy savings, improved productivity, and reduced operational costs. Delivering superior speed and range 8 MHz capable device using 64 QAM modulation can transmit at speeds of up to 32 megabits per second A Wi-Fi HaLow network shatters the traditional tradeoff of wireless communications between speed and range. A single-stream, 8 MHz capable device using 64 QAM modulation can transmit at speeds of up to 32 megabits per second at sub-GHz frequencies, enabling live streaming on large screens, connecting multiple real-time AI edge cameras, as well as thousands of low-power IoT devices, all connected without compromising on range. Wi-Fi HaLow signals can extend beyond 1 kilometer, up to 10 times farther than traditional forms of Wi-Fi in the 2.4, 5, and 6 GHz frequency bands, and are capable of connecting far-flung devices and systems across campus environments. Setting a new standard for campus connectivity By addressing the connectivity needs of modern campuses, Wi-Fi HaLow paves the way for future campus applications. As we navigate the digital era, Wi-Fi HaLow presents a compelling solution that significantly enhances connectivity, safety, and efficiency. This leap in wireless capabilities isn’t merely incremental; it represents a transformative stride toward a smarter, more connected future. Wide-reaching wireless network Educational institutions can leverage Wi-Fi HaLow to create safer, more efficient, and interconnected campus environments. By providing a robust, reliable, and wide-reaching wireless network, Wi-Fi HaLow enables campuses everywhere to fulfill their diverse connectivity needs without compromise.
When a bomb detonated in the Port of Beirut, I had hundreds of employees under my care inside the blast zone. Within just two hours, I was able to determine who was impacted, understand their safety conditions, and share resources for on-the-ground support—all thanks to mobile technology. For Chief Security Officers, receiving calls like these launches a variety of protocols and necessary decision-making with the safety and security of people and assets as a top priority. And these calls are only becoming more common. Dependence on threat intelligence Mobile phones have dominated the post-COVID environment where people work from anywhere Threats ranging from natural disasters to geopolitical conflicts are becoming more frequent and complicate the responsibility organizations have in keeping their people safe. To meet these needs CSO’s are staying ahead of negative outcomes through creating a greater dependence on threat intelligence. In these times, effective, real-time risk management depends on hyper-local data from technology that is accessible, portable, and dynamic – such as cell phones. Mobile phones have revolutionized the way people live and work. They allow us all to walk around with a computer in our pocket, bringing the world to our fingertips and eliminating digital borders for over 90% of the world's population. Mobile phones have dominated the post-COVID environment where people work from anywhere and have geographically distributed teams but are also more vulnerable to threatening events. Mobile-friendly risk management platforms Mobile technology assigns workers with easy entry to data that can help keep them and their teams safe As we approach 2024, many organizations are adopting comprehensive risk management tools that empower personnel across the organization with the intelligence and knowledge they need to stay safe wherever they are. Mobile-friendly risk management platforms, such as Crisis24 Horizon, provide always-on awareness, on-hand threat intelligence, and immediate communications and distress signaling through location monitoring. Users receive location risk assessments and push notifications directly to their devices about nearby issues and threats no matter if they are on or off the job. While only select risk managers have complete control of the platform and all sensitive employee data is protected through encryption, the app distributes critical intel to foster a culture of shared awareness and responsibility. Thus, mobile technology empowers employees with easy access to information that can help keep them and their teams safe. Creating a culture of mobile technology adoption In the last few years, the world has proven the importance of being well-informed of risks and mitigation plans to minimize harm. However, psychological barriers tend to trump physical barriers when it comes to accessing the vast array of tools our mobile devices offer. World has proven the matter of being well-informed of risks and relief plans to minimize harm Adopting this technology and establishing a culture that enforces risk management across an organization is a daunting challenge that demands substantial commitment from leadership to be successful. Some companies have tackled this challenge by positioning security technology as part of the organization’s employee benefits package, such as commuter benefits and health insurance, to encourage people to take advantage of these resources and learn how to use them. Cohesive risk management culture Technology is only as effective as the people whose actions it informs, which is why adoption and integration are so important. When a cohesive risk management culture meets a powerful technology platform, individuals are enabled to receive threat alerts and counter their impacts, letting others know when and how to take the necessary precautions to protect themselves and their team. For more information on mobile technology and other security trends, check out the Global Risk Forecast, an annual report by Crisis24 that provides a comprehensive analysis of key events around the world most likely to affect operations in the coming year.
Security beat
Fueled by mounting concerns about the cybersecurity vulnerability of U.S. ports, President Joe Biden has signed an Executive Order aimed at shoring up defenses against cyberattacks. Cybersecurity initiative The cybersecurity initiative marks a significant shift in policy, empowering key agencies and outlining concrete actions to bolster defenses. By empowering agencies, establishing clear standards, and fostering collaboration, the initiative aims to strengthen U.S. ports against the evolving threat of cyberattacks, safeguarding the nation's maritime economy and national security. Expanded authority for DHS The proactive approach aims to prevent incidents before they occur The Executive Order grants expanded authority to the Department of Homeland Security (DHS) and the Coast Guard to address maritime cyber threats. DHS gains the power to directly tackle these challenges, while the Coast Guard receives specific tools. The Coast Guard can compel vessels and waterfront facilities to address cyber vulnerabilities that endanger safety. The proactive approach aims to prevent incidents before they occur. Real-time information sharing Reporting any cyber threats or incidents targeting ports and harbors becomes mandatory. This real-time information sharing allows for swifter response and mitigation efforts. The Coast Guard also gains the authority to restrict the movement of vessels suspected of posing cyber threats. Inspections can be conducted on vessels and facilities deemed risky. Mandatory cybersecurity standards The standardization aims to eliminate weak links in the chain and prevent attackers from exploiting Beyond these broad powers, the Executive Order establishes foundational elements for improved cybersecurity. Mandatory cybersecurity standards will be implemented for U.S. ports' networks and systems, ensuring a baseline level of protection across the board. This standardization aims to eliminate weak links in the chain and prevent attackers from exploiting individual vulnerabilities. Importance of collaboration and transparency Furthermore, the initiative emphasizes the importance of collaboration and information sharing. Mandatory reporting of cyber incidents fosters transparency and allows government agencies and private sector partners to work together in mitigating threats. Additionally, the Executive Order encourages increased information sharing among all stakeholders, facilitating a unified response to potential attacks. Maritime Security Directive The Executive Order encourages investment in research and development for innovative cybersecurity solutions To address specific concerns, the Coast Guard will issue a Maritime Security Directive targeting operators of Chinese-manufactured ship-to-shore cranes. This directive outlines risk management strategies to address identified vulnerabilities in these critical pieces of port infrastructure. The long-term success of this initiative hinges on effective implementation. The Executive Order encourages investment in research and development for innovative cybersecurity solutions, recognizing the need for continuous improvement and adaptation to evolving threats. Recognizing the urgency of cyber threats The initiative has been met with widespread support from port authorities, industry stakeholders, and cybersecurity experts who recognize the urgency of addressing cyber threats. However, some concerns exist regarding the potential burden of complying with new regulations for smaller port operators. Effective communication, resource allocation, and collaboration among all stakeholders will be crucial to ensure the successful implementation of this comprehensive plan. Enhancing cybersecurity The more impactful and noteworthy piece is the associated NPRM from the U.S. Coast Guard (USCG) “This Executive Order is a positive move that will give the U.S. Coast Guard (USCG) additional authority to enhance cybersecurity within the marine transportation system and respond to cyber incidents,” comments Josh Kolleda, practice director, transport at NCC Group, a cybersecurity consulting firm. The more impactful and noteworthy piece is the associated Notice of Proposed Rulemaking (NPRM) from the U.S. Coast Guard (USCG) on “Cybersecurity in the Marine Transportation System,” adds Kolleda. Portions of the notice of proposed rulemaking (NPRM) look similar to the Transportation Security Administration (TSA) Security Directive for the rail industry and the Emergency Amendment for the aviation industry. Coordinating with TSA on lessons learned The USCG should be coordinating with TSA on lessons learned and incorporating them into additional guidance to stakeholders and processes to review plans and overall compliance, says Kolleda. “At first glance, the NPRM provides a great roadmap to increase cybersecurity posture across the various stakeholders, but it underestimates the cost to private companies in meeting the requirements, particularly in areas such as penetration testing,” says Kolleda. Cyber espionage and threats The focus is on PRC because nearly 80% of cranes operated at U.S. ports are manufactured there “It is unclear if or how the federal government will provide support for compliance efforts. As this seems to be an unfunded mandate, many private companies will opt for the bare minimum in compliance.” “Cyber espionage and threats have been reported by the Director of National Intelligence from multiple nation-states including China, Russia, and Iran,” adds Paul Kingsbury, principal security consultant & North America Maritime Lead at NCC Group. The focus here is on the People’s Republic of China (PRC) because nearly 80% of cranes operated at U.S. ports are manufactured there, he says. Destructive malware “The state-sponsored cyber actors’ goal is to disrupt critical functions by deploying destructive malware resulting in disruption to the U.S. supply chain,” says Kingsbury. “These threat actors do not only originate in China or other nation-states but also include advanced persistent threats (APTs) operated by criminal syndicates seeking financial gain from such disruptions." "The threat actors don’t care where the crane was manufactured but rather seek targets with limited protections and defenses. The minimum cyber security requirements outlined within the NPRM should be adopted by all crane operators and all cranes, regardless of where they are manufactured.” PRC-manufactured cranes Kingsbury adds, “The pioneering risk outlined in the briefing is that these cranes (PRC manufactured) are controlled, serviced, and programmed from remote locations in China." "While this is a valid concern and should be assessed, there are certainly instances where PRC-manufactured cranes do not have control systems manufactured in PRC. For example, there are situations in maritime transportation system facilities where older cranes have been retrofitted with control systems of European Union or Japanese origin.” Monitoring wireless threats “The Biden Administration’s recent Executive Order is a critical step forward in protecting U.S. ports from cyberattacks and securing America’s supply chains,” says Dr. Brett Walkenhorst, CTO at Bastille, a wireless threat intelligence technology company. “To ensure proper defense against malicious actors accessing port-side networks, attention must also be paid to common wireless vulnerabilities." "Attacks leveraging Wi-Fi, Bluetooth, and IoT protocols may be used to access authorized infrastructure including IT and OT systems. Monitoring such wireless threats is an important element in a comprehensive approach to upgrading the defenses of our nation’s critical infrastructure.”
Already a strong player, particularly in New Zealand and Australia, Gallagher is still climbing in the U.S. market, which it sees as a big opportunity to invest in the company. Active in the United States for 10 years, Gallagher undertook a more aggressive growth strategy about five years ago. There are 52 employees in Gallagher’s U.S. security business, and about half the workforce has been hired in the last couple of years. They have grown from three sales territories to 16, operated by a full sales and engineering staff. Culture of innovation sets As it happens, Gallagher’s U.S. headquarters is located a short drive from my home office in the wider vicinity of Atlanta. I missed seeing them at GSX in Dallas, so we scheduled an in-person visit to catch up on their company. Gallagher’s strong culture of innovation sets them apart, as does their “people-first” commitment, says Scott Elliott, Gallagher’s Executive Vice-President, The Americas. “We have intentionally recruited for a diversity of thought that drives the business,” says Elliott. “We are a people business.” Melissa Vidakovic, Director of Marketing, Americas; and Scott Elliott, Executive VP, Americas, at Gallagher Security's office in Canton, GA. Unified approach An advantage Gallagher has in the market is total ownership of their supply chain; it manufactures each of the hundreds of products used across their solutions, from plastic components to readers to controllers to their own software systems. Among other advantages, the unified approach enables tighter control from a hardening and cybersecurity perspective, enabling them to minimize any threat vectors or vulnerabilities. The strategy also avoids dependence on third-party suppliers, which was a huge advantage during recent supply chain disruptions. While competitors struggled with availability issues related to third-party manufacturers, Gallagher’s supply was uninterrupted. Gallagher’s commitment Gallagher uses the same norms as the nation and subjects its effects to inner and outer penetration As a manufacturer serving a broad spectrum of markets, it’s Gallagher’s commitment to the high end of the market (e.g., high-security applications), where the company incorporates core tenets such as authentication and encryption. Gallagher uses some of the same standards as the government and subjects its products to internal and external penetration testing. These core strengths are also integral to Gallagher’s complete product line. “If it’s good enough for a high-level customer, it’s good enough for Mr. Business Owner,” says Elliott. The New Zealand company was founded in 1938 and was the first company to commercialize the electric fence, which it still uses for its agriculture business sector, separate from the security business. Gallagher entered the access control business 35 years ago in 1988 when a product used to restrict access to fuel pumps evolved into broader access control. Gallagher platform In the intervening years, the product has grown into a unified platform that incorporates access control, intrusion detection, and perimeter detection in a single ecosystem. “The platform is all-encompassing,” says Elliott. “No other platform does all three.” Augmenting access control, intrusion, and perimeter protection, there are other applications available in the Gallagher platform, such as workforce management, health and safety functions, and a spectrum of features useful to a wider stakeholder community. Fatigue management applications For example, Gallagher can implement routine randomized checks to proactively mitigate potential risks such as drug or alcohol abuse, thus ensuring workers are fit to work, to operate various machinery and that they do not pose a threat to fellow employees or the company. “Fatigue management” applications can monitor the use of equipment to avoid repetitive injuries or manage how long an employee works at a job site, requiring a worker to swipe or tap a card to a reader mounted on a machine to monitor and limit the time they operate that machine. Mobile mustering provides location and identification of evacuees in case of an emergency. Impact of digital transformation Gallagher’s “Better Ways of Working” concept zeroes in on the impact of digital transformation Gallagher is also embracing the “digital transformation” of the industry. Security companies must adapt to a more agile workforce and shifting processes, says Elliott. Gallagher’s “Better Ways of Working” concept zeroes in on the impact of digital transformation on their workforce. They also seek to address the changing workforce, where Gen-Z’ers work side-by-side with tenured, experienced workers, and where creating trust is the best approach to closing the generational gap. Gallagher also seeks to educate the market on trends such as artificial intelligence (AI), machine learning, cloud adoption, various service delivery models, and other issues. Industry consolidation Gallagher has more than 1,200 employees; operates in 140 countries, from South America to Canada, Europe to the Asia-Pacific and Australia; and serves almost 16,000 customers. Gallagher is part of New Zealand’s growing technology export sector, which is growing 30% faster than the overall economy and is now the second-largest export sector in New Zealand. In an age of industry consolidation and a market dominated by corporate conglomerates, Gallagher is a privately held organization seeking to be agile and innovative, and to deliver customer value more quickly. Gallagher re-invests about 15% of its profits into research and development. “Our customer service is the primary reason people buy from us,” says Elliott. Security integrators Security integrators quickly appreciate the breadth and strength of the product line Gallagher positions itself as an alternative in a market in the midst of disruption. Brand awareness continues to be a challenge in the United States, and the sales team often hears the question: “Who is Gallagher?” Once the introduction is made, security integrators quickly appreciate the breadth and strength of the product line, says Elliott. “We allow our customers to select among best-of-breed platforms, and [using open systems,] we are not limited by the technology we offer,” says Elliott. “Our value proposition to the integrator channel is our focus on the relationship,” says Elliott. Supporting end users through an authorized, certified channel, Gallagher also emphasizes value, cost-competitiveness, and cybersecurity. “Our partner relationships are built around cultural alignment,” says Elliott. Product innovation perspective What’s ahead for Gallagher and for the industry as a whole? Hard to say, notes Elliott, given the unfolding of unpredictable geopolitical and financial trends. However, from a product innovation perspective, Gallagher will continue to evolve, balancing a dependence on “cash cow” legacy product lines with investment in leapfrog innovations such as frictionless access control, cloud platforms, and mobile systems. In general, Elliott predicts AI will yield an opportunity to analyze a person’s pattern of behavior and intent, thus enabling a security system to adapt down the road. “With the ability to predict with some degree of certainty what might happen, these capabilities will evolve,” says Elliott.
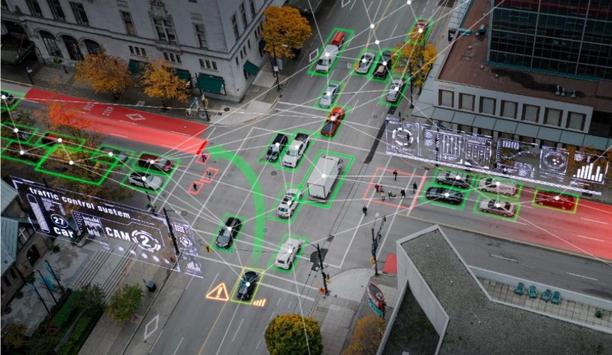
Companies at GSX 2023 emphasized new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasizes ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the Mid-Market to the Cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for pure cloud, but there are benefits to be realized from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realize the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘Soft’ Features for Integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organization more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organization more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centers around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasizing performance, protection (cybersecurity), and price, their data centers are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring center where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
Case studies
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the US Department of Homeland Security SAFETY Act Designation, announced that its solution has been selected by Iowa’s Murray Community School District to identify illegally brandished guns on campus and help protect students and faculty against gun-related violence. Murray Community School District serves 300 students in Murray, Iowa in grades pre-K-12. The district provides an educational environment that challenges the status quo and makes it its mission to clear away any roadblocks that constrain creativity and innovation. New layer of security “While we are a small, rural community, if there is anything we have learned it’s that gun-related violence can happen anywhere,” said Tim Kuehl, superintendent of Murray Community School District. “We are prioritizing the safety and security of our students and faculty, and ZeroEyes ensures that our campus is protected from gun-related threats 24/7. We are proud to add this new layer of security to make our community safer.” Existing digital security cameras ZeroEyes' AI gun detection and clever situational grasp software layers onto security cameras ZeroEyes' AI gun detection and intelligent situational awareness software layers onto existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Center (ZOC), staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence — including visual description, gun type, and last known location — to local law enforcement and school staff as quickly as three to five seconds from detection. AI gun detection solution “Gun-related violence in school communities is far too common,” said Mike Lahiff, CEO and co-founder of ZeroEyes. “Murray Community School District is addressing this problem head-on by adopting our AI gun detection solution. We are grateful to have the opportunity to proactively combat this issue and alert local authorities of a potential threat before it happens.”
In the heart of Aalborg is a lovely and well-kept private home. Here lives a family of five who in 2016 would rent out their basement to utilize the home’s square metres. WHY – To access the basement, the tenants must go through the back door. The family and the tenants thus share the same entrance at the back of the house. Therefore, the family was looking for a solution on how they could give the tenants access to the basement without them also having access to the family’s private residence. WHAT – It was important for the family to keep the architectural style of the house. However, it was not entirely straightforward to find an access control solution where the solution only sat on one side of the door, says Michael Goth-Rindal. Together with CONLAN’s CEO, Ejner Hansen, the family found a solution where they could both preserve the old door and at the same time avoid pulling wires for electricity. Tenants keyless access The keyboard can go through many cycles before the battery needs to be replaced The CT1000 keypad is installed on the back door of the house, giving both family and tenants keyless access to the house. In addition, the C1000LP keypad is installed on the front door of the private home, where the solution is only visible from the side of the staircase. From the inside of the house, they can not see that the door is powered by a keypad. The keypad on the front door of the private residence is battery-powered, meaning the old door could remain, without the pull of wires. As the keypad is a low-power device, the keyboard can go through many cycles before the battery needs to be replaced. The family changes the battery themselves, and the keyboard tells when it’s time. Keypad’s daycode function This allows them to create a code for, e.g., the cleaning, which only works the one-day Benefits - With this solution, the family can access their home, completely without the need for keys. “We are really happy with our solution. It works and is a flexible system that we can easily handle ourselves,” says Michael Goth-Rindal. In addition, the family also uses the keypad’s daycode function. This allows them to create a code for, e.g., the cleaning, which only works the one day. With this, the family has full control over who has access to the house and when. Low power consumption CT1000 reader on the back door – A standalone reader with code. Possibility of up to 28 user codes. The keypad can also be connected to the alarm, so that the alarm is switched off at the same time as the door is unlocked. C1000LP reader on the entrance door for the private home – Reader with code and low power consumption for access control. Several options for access with codes, including one-time, day and period codes that are active from one to 28 days. In addition, the keypad can be powered by both battery or wired power.
The Transportation Services and Mobility department for the city of Grand Prairie, Texas recently completed a substantial project to replace the locks on their Intelligent Traffic Cabinets with a better and more secure choice. Turns out what they needed was only a few miles away with ALCEA’s Traffic Cabinet Locking Solution powered by ABLOY technology. ALCEA is the brand formerly known as ASSA ABLOY Global Solutions - Critical Infrastructure. The ALCEA Traffic Cabinet Locking Solution has gained traction with transportation infrastructure departments in major cities across the United States. It was developed by Jerry Burhans, managing director for North America, and Michael Woody, manager of the ALCEA Competence Center in Irving, which shares a border with Grand Prairie. Now this access management solution is beginning to impact medium-sized communities like them. Proactive cybersecurity measures Perez said this skill project will save all city signal cabinets from tampering and unauthorized key Raul Perez, a 13-year transportation industry veteran who has served as Grand Prairie’s ITS Specialist for 2-1/2 years, said this installation project will protect all city signal cabinets from tampering and unauthorized access. Involving 240 smart locks, 210 high-security mechanical locks, and padlocks on all city traffic cabinets plus 10 message boards, 191 mechanical locks for all school flashing sign cabinets, and 20 Bluetooth keys is in step with the city’s policy of adopting proactive cybersecurity measures. “Having control over who has access and when to our traffic cabinets was a major driver for this project,” he acknowledged. “We have not had people trying to force their entry into our cabinets, but we did have several occasions where contractors were gaining access to them without permission or notice. ALCEA was the clear choice for our smart lock needs, offering a solution that aligns with our requirements.” Substantial growth and the need to safeguard assets Grand Prairie has a long history associated with technology. Located in the Dallas-Fort Worth metroplex, it is the sixteenth largest city in Texas with a population of more than 207,000 people. During World War I and since, it began an association with the defense and aviation industries and served as an aircraft production site. The city sits 12 miles west of downtown Dallas and is only 10 minutes south of the Dallas-Fort Worth International Airport. With rail lines and major interstates 20 and 30 running through it, Grand Prairie has become a well-established distribution center. The majority of the Great Southwest Industrial District’s approximately 80 million square feet of space is in the city. State’s transportation infrastructure Grand Prairie’s growth resembles the rest of Texas, the largest of the 48 continuous states Combine major attractions like the Lone Star Park horse racetrack and Epic Waters, one of the largest indoor waterparks in Texas, and the city’s 81 square miles of road experience heavy traffic activity all day long. Grand Prairie’s growth resembles the rest of Texas, the largest of the 48 continuous states. After an unprecedented boom, the U.S. Census Bureau declared it is now home to more than 30 million residents following a 43% increase from 2020 to 2022. That development in part led to the Texas Department of Transportation announcing a $142 billion investment in the state’s transportation infrastructure last August as part of a 10-year state roadways plan. About the same time the announcement was made is when the city of Grand Prairie began researching options for a separately funded project to increase cybersecurity preparedness. Flexibility of a Hybrid Locking Solution “I started looking for smart locks and found ALCEA’s mechanical lock with a high-security key during an online search. I was intrigued so I contacted them, inquired about their product and arranged a visit to their office for a presentation,” said Perez, who also evaluated the offerings of three other vendors. “It was then I learned about the capability of unlocking both the electronic and mechanical locks – including padlocks – and the versatility of their keys. I was very impressed by the user-friendly design of their Bluetooth smart key,” he said in reference to the ABLOY PROTEC2 CLIQÔ system. Mechanical and electromechanical locks Remote access control system mixes the parts of robotic and electromechanical locks The remote access management system combines the best characteristics of mechanical and electromechanical locks. After the initial meeting with ALCEA, Perez said he was convinced of the value of this hybrid solution but had to secure buy-in from his supervisor and department director. “Working with the ALCEA team, we tailored a price quote aimed at convincing our department director to allocate funds for this investment. The initiative was successfully integrated into our budget by the end of 2023, and the purchase order was placed in mid-January.” Demonstrated by the ALCEA team The city of Grand Prairie chose ALCEA for several key reasons. “Their product offered the advantage of securing all our enclosures with a single key, with efficiency and convenience,” said Perez. “The versatility of giving us the capability to integrate both mechanical and electronic locks, as well as padlocks, contributed to a more cost-effective final solution. The user-friendly key system, coupled with the security features, ensures ease of use without compromising safety." “The expertise, customer service, and professionalism demonstrated by the ALCEA team added confidence in our decision-making process,” added Perez. “Being a local company, they are able to provide localized support.” Common problems with #2 keys protecting roadside equipment The mechanical lock series that was installed contains ABLOY’s unique high-security cylinder The mechanical lock series that was installed contains ABLOY’s unique high-security cylinder. The electromechanical locks support electronic access control, key tracking, and audit trails with CLIQ Web Manager software. Perez says it instantly solves a problem that existed with their old system. “The challenges we encountered before are widespread in the transportation industry. Many traffic enclosures are accessible with a #2 key, which is impossible to track and makes unauthorized access a potential risk,” he explained. “Anyone can buy that type of key for a couple of dollars. This lack of accountability is a significant security concern, particularly with the increasing prevalence of cyber threats targeting government agencies.” Open cabinet locks and padlocks Perez says the ALCEA solution gives Grand Prairie continuity for its program. “Given the critical nature of our infrastructure and the investment in our high-tech signal control devices, protecting our assets is a top priority,” he acknowledged. “We now have versatility where the same key will open cabinet locks and padlocks, and it can be updated by using the CLIQ app, which is convenient for everyone on our team. Technicians and supervisors wiil be using most of the keys, and the others are for the contractors who need access to the traffic cabinets on an occasional basis.”
Comcast Smart Solutions, a division of Comcast Corporation that specializes in smart technology solutions for businesses and communities, announced that it will provide the Town of Braselton, Georgia, with smart video camera technology with AI capabilities to improve public safety and emergency response. The deployment of smart video camera technology at the Town Green and Braselton Park will provide the town with real-time visibility into its community spaces, and insights into traffic patterns during events, and will increase peace of mind for residents. New technology nonprofit The town saw it as a natural progression to continue upgrading the area with technology “These advanced cameras will play a vital role in bolstering safety efforts within our town and surrounding municipalities,” said Jennifer Scott, Braselton Town Manager and Clerk. “With real-time monitoring and intelligent analytics, this technology presents an efficient and cost-effective approach to creating safer public spaces and fostering a stronger sense of security for our community members." The Town of Braselton has a history of embracing smart technology, evidenced by its support of a new technology nonprofit that provides startup incubator space in partnership with local community members and a technology-focused university. Given this background, the town saw it as a natural progression to continue upgrading the area with technology. AI video analytics solution These cameras are planned to minimize false alarms and provide quick and valid forensic hunts Now, at the Town Green, multiple smart video cameras will oversee the parking lot and areas behind the concession stands. Additionally, smart video cameras at Braselton Park will monitor the playground and parking lot near the park’s tennis courts. Equipped with multi-sensor and multi-directional capabilities and AI video analytics, these cameras are designed to minimize false alarms and provide quick and accurate forensic searches. The video information captured, along with the AI video analytics solution will integrate seamlessly into a cloud-based application, providing the town with actionable data insights, including alerts for suspicious activity and recommendations based on traffic patterns. Smart video camera solution In collaboration with Comcast Smart Solutions, Braselton will receive comprehensive project management and continuous support. This includes a dedicated Comcast Smart Solutions project manager overseeing installations, conducting analyses, providing product training, and maintaining an ongoing support team to assist Braselton. “Delivering a seamless and reliable solution was essential to assist the Town of Braselton in enhancing safety and revitalizing communal areas,” said Mike McArdle, Senior Regional Vice President, Comcast. “We’re excited to not only provide a comprehensive smart video camera solution but also offer continuous support, ensuring that Braselton residents can enjoy their parks with confidence and peace of mind.”
Riga Sports Arena is a municipal facility maintained by the city of Riga, Latvia. Covering a total area of 21,821 square meters, the arena accommodates 2,500 spectator seats. It houses several training halls, including a large athletics arena, a training and warm-up hall, a weightlifting hall, and a sports field. Challenge Enhance security by replacing inefficient guards with technical equipment Riga sports arena faced a significant security challenge, relying on two guards who worked only night shifts. Depending on just one person was insufficient to ensure the safety of the complex, given its substantial size. The guards struggled to effectively cover all areas, leaving the arena vulnerable to security risks. Moreover, the financial burden of employing guards strained the city’s budget. There was a need to enhance security while eliminating the human factor and optimizing associated costs. Moreover, the financial burden of employing guards strained the city’s budget The client required a professional security system that could be implemented without extensive construction work or the need to lay a substantial number of cables throughout the building. They sought an effective and easily installable system that would enhance security without compromising the integrity of the facility. Solution Cost-effective wireless solution reinforcing security for a large municipal facility Considering the building’s size and recent reconstruction work, the installation of a traditional wired security solution was deemed impractical. This option would have required several months to complete and additional renovation work after installation. Moreover, the presence of many oversized windows, each requiring protection with detectors, made cable-based solutions even more impractical. GRIFS AG proposed an Ajax wireless solution that can be quickly installed without damaging the walls, allowing for complete control and management of the system through a mobile app. To streamline control without the need for multiple hubs, Hub 2 Plus Jeweler was selected In total, 115 devices were installed throughout the building to ensure comprehensive security coverage. To streamline control without the need for multiple hubs, Hub 2 Plus Jeweler was selected. This hub can control up to 200 devices, managing 25 security groups with a total of 200 users. This feature aligns with the client’s requirements, given the installation of many devices and the need to manage security modes for separate premises, all in the Ajax app. For example, it allows keeping employees’ offices in armed mode while conducting training sessions in the main hall. GRIFS AG installed DoorProtect Jeweler Given that the sports complex spans three floors and considering the need for the hub signal to pass through two reinforced concrete floors, the decision was made to enhance its communication range. To ensure stable communication between all 115 detectors and the hub, the ReX 2 Jeweler radio signal range extender was installed. This guarantees a reliable connection between all system components, ensuring seamless communication even in areas with challenging signal transmission conditions. For comprehensive security, GRIFS AG installed DoorProtect Jeweler opening detectors to oversee For comprehensive security coverage, GRIFS AG installed DoorProtect Jeweler opening detectors to oversee all doors. Additionally, MotionProtect Curtain Jeweler, with a narrow viewing angle and a maximum detection range of up to 15 meters, protects the large windows in corridors and sports halls. The challenge with large windows was that glass break detectors may be positioned far away from the hit spot, making it difficult to detect glass breakage. However, MotionProtect Curtain Jeweler, equipped with PIR sensors, instantly reacts to movement within its detection zone along the whole length of a window. Notably, the detector catches movement only if a person enters its field of view, allowing for protection even when a cleaner is working nearby, or a staff member is walking around. In addition, MotionProtect Jeweler detectors were installed throughout all entrance groups, major corridors, and stairwells to promptly notify the owner and the security company in case of any detected motion. Multiple HomeSiren Jeweler devices To facilitate arming and disarming of the security system for numerous employees in the sports complex, a wireless touch KeyPad Jeweler was installed. By entering a code, the device can activate the full security mode and automatically blocks itself if an incorrect code is entered multiple times. KeyPad Jeweler supports up to 99 codes, each corresponding to a separate user, making it suitable for enterprises with many employees. HomeSiren Jeweler devices were installed indoors throughout the skill to provide loud signs For rapid security response, the wireless alarm Button Jeweler was installed, enabling quick notification of the security company in case of intrusion. Furthermore, multiple HomeSiren Jeweler devices were installed indoors throughout the building to provide audible warnings in case of danger or deter potential intruders. These sirens emit loud sounds up to 105 dB to prominently signal a breach, effectively preventing unauthorized individuals and enhancing overall security. The arena management plans to automate evacuation doors using the Relay Jeweler system soon, enhancing safety and security by allowing remote door opening during emergencies. Why Ajax Cost-saving security solution. Customers can experience significant savings by opting for Ajax. The costs of the Ajax system installation were approximately equal to the expenses for security guards’ salaries per year. However, starting from the second year, the Municipality of Riga can achieve significant savings by paying only a low monthly fee for monitoring. Easily scalable future-proof system. With Ajax, the security system is easily scalable, allowing for future expansion and the implementation of additional functionality as needed. For instance, Hub 2 Plus Jeweler, already installed, supports the addition of up to 200 detectors, including MotionCam Jeweler detectors for photo verification of alarms, without requiring any system reorganization. This enables seamless integration for enhanced security measures, ensuring the system can adapt and grow with changing security requirements and evolving customer needs. Effortless wireless installation. Ajax offers a wireless solution, eliminating the need to lay cables in walls or undergo extensive repairs. This allows for quick and efficient installation without the limitations of wired infrastructure. After implementing the Ajax security system at the sports arena, the center’s management noted its convenience and decided to install Ajax in their homes.
Wetlands, the "kidneys of the Earth", are considered one of the three major ecosystems on Earth, along with forests and oceans. Hosting a diverse range of terrestrial and aquatic plant and animal species, wetlands serve as crucial habitats for numerous bird species. Red-crowned cranes Beautiful Wetlands vs Critically Endangered Cranes The Red-crowned Crane is considered as the "God of Wetlands" and is highly sensitive to environmental changes. It is one of 14 bird species in China classified as critically endangered, with only around 2,000 wild Red-crowned Cranes remaining worldwide. Monitoring these rare bird species not only aids in their effective protection but also reflects changes in the wetland ecosystem to some extent. Red-crowned Cranes migrate between the regions of East China and Northeast China In China, during spring and autumn seasons, Red-crowned Cranes migrate between the regions of East China and Northeast China, requiring wetland management personnel to make all necessary preparations in advance every year. Recording and tracking data (e.g. time of arrival/departure, and total number) play a significant role in monitoring both the Red-crowned Cranes and the wetland ecosystem. Hence, monitoring rare bird species is essential not only for their conservation but also for understanding the changes in wetland ecological environments. Vigilant cranes, eager for improved, smarter observation However, Red-crowned Cranes have extremely strong vigilance. Even while foraging or resting, there are often adult birds designated to be on alert, making warning calls and taking flight if any danger is detected. Therefore, it becomes challenging for monitoring personnel to observe them up close, as they need to maintain a distance of several hundred meters using binoculars to avoid disturbing the cranes. Such limitations in observation pose difficulties in monitoring the population distribution and activities of Red-crowned Cranes. To achieve efficient and intelligent monitoring while minimizing human interference, many wetlands have enlisted the assistance of an intelligent "avian expert". Dahua: the guardian of cranes with smart technologies In recent years, avian intelligent recognition systems have been increasingly applied in wetland monitoring. Dahua Technology actively explores the integration of technology and wetland conservation to support the monitoring and protection of bird species across multiple wetlands. Rare bird species like the Red-crowned Crane can be automatically identified and counted By employing high-point video footage combined with avian intelligent recognition algorithms, rare bird species like the Red-crowned Crane can be automatically identified and counted. This allows monitoring personnel to discover and observe various bird species clearly and promptly without disturbing them. Additionally, techniques such as background removal and contour deformation processing help reduce the interference caused by lighting conditions and backgrounds, ensuring that the footage presents the identifying characteristics, location, and time for each bird. With this approach, comprehensive and accurate data recording and result analysis can be achieved without disturbing the Red-crowned Cranes up close. A brighter future for biodiversity using intelligent analysis In addition to population counting, vocalizations play a crucial role in bird research. By utilizing voiceprint recognition, it becomes possible to track and study the population distribution of rare bird species. Many regions have established and improved databases of avian vocalizations, creating a foundation for biodiversity monitoring and analysis. These databases, combined with visual identification, are being cataloged in order to facilitate more comprehensive research and analysis, optimize timely conservation measures, and enhance dynamic and diverse science communication and education. Dahua Technology continues to empower biodiversity conservation through technology. The Dahua AI platform enables continuous algorithm training that helps reduce the development cycle of recognition algorithms for specific species. At present, Dahua has developed over 800 bird recognition algorithms, with more than 500 focused on waterfowl and migratory birds primarily inhabiting wetland environments. This extensive collection of algorithms greatly supports and contributes to biodiversity conservation efforts around the globe.


Round table discussion
Technological leaps in the last several decades have revolutionised biometrics. The technologies are constantly evolving, spanning facial recognition to iris scanning to fingerprints, to provide new levels of security and convenience. Biometrics are everywhere, from smartphones to border control, constantly evolving to meet the needs of our increasingly digital world. They are also more accurate and easier to use than ever. We asked this week's Expert Panel Roundtable: What’s new with biometrics?
In the complex world of physical security systems, standards can enable disparate systems to be combined to function together as a cohesive whole. Standards help to ensure that all the “pieces” fit together to create a clear, unified picture. More broadly speaking, standards also play a role in ensuring best practices are deployed in a range of security-related situations. We asked this week’s Expert Panel Roundtable: Which standards have had the greatest positive impact on physical security?
Frictionless systems provide access to a building without interfering at all with a user’s entry experience. Frictionless access means you can automatically pass through a gate without showing a credential or otherwise engaging, and with the system recognizing who you are and allowing you to pass. In true frictionless access, everything works seamlessly, with unauthorized people obviously barred. But how close are we to realizing frictionless access control? We asked this week’s Expert Panel Roundtable: Is frictionless access control a reality or an empty promise?
Products


White papers

Access Control: The Enterprise Buyer's Guide
Download
A Step-By-Step Checklist for Choosing an Intercom System
Download
The Wireless Access Control Report 2023
DownloadCybersecurity in Keyless Access Management
Download
Wireless Access Control eBook
Download
Wireless Security: Cut Costs Without Cutting Corners
Download
Making Your Surveillance Cyber Secure
Download
How To Keep Students Safe On Campus
Download
Network Security Redefined: IP-Enabled Access Control
Download
Mobile Access - What You Need To Know
Download
The Evolution Of Cards And Credentials In Physical Access
Download

Videos
Wireless security: Manufacturers & Suppliers
- ASSA ABLOY - Aperio® Wireless security
- CLIQ - ASSA ABLOY Wireless security
- Honeywell Security Wireless security
- DSC Wireless security
- Climax Technology Wireless security
- Ajax Wireless security
- Dahua Technology Wireless security
- Senstar Wireless security
- Vanderbilt Wireless security
- Visonic Wireless security
- ASSA ABLOY Wireless security
- OPTEX Wireless security
- Pyronix Wireless security
- Verkada Wireless security
- Bosch Wireless security
- RISCO Group Wireless security
- Kantech Wireless security
- Paxton Access Wireless security
- D-Link Wireless security

Multi-Residential Access Management And Security
Download
Guide For HAAS: New Choice Of SMB Security System
Download
Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Hikvision: Solar Powered Product Introduction + HCP
Download
Artificial Intelligence
Download