Network Video Recorders - Expert commentary
The European Union’s GDPR (General Data Protection Regulation) framework represents some of the toughest and most secure privacy laws in the world. Their creation signaled the EU’s dedication to individual privacy rights and generated new standards and requirements for an organization inside or outside of the EU wanting to do business in the region. This privacy stance raises an interesting question: to what extent (if any) will France be utilizing AI-assisted security and biometri...
Security manufacturers throw around the term “scalable” a lot these days, but few dive into what scalable really means for modern organizations and their security programs. Achieving true scalability, or as I like to refer to as “expandable with a purpose,” takes planning and coordination from security pioneers alongside the broader organization. Implementing a flexible strategy is critically important in the age of advancing analytics and intelligence-driven technology....
The days of being reactive are over. That’s right, we as an industry, can no longer afford to be reactive. As threats evolve, the need for proactive security is critical. While traditional methods, including physical barriers and security personnel, are still necessary, the future of our approach is built on the backs of emerging technologies. Substantial vulnerabilities As an industry, we’ve operated reactively for decades, it has been common for security teams to address...
Educational institutions worldwide increasingly rely on robust wireless networks to enhance academic pursuits, safety measures, and operational efficiency. The campus environment, a complex network of interconnected buildings, and the humans navigating them require innovative technologies to meet these diverse needs. The solution lies in a new wireless protocol that provides an ideal fit for the long-range, low-power connectivity requirements of educational campuses: Wi-Fi-certified HaLow. Wi...
In the realm of physical security, the distinction between being perceived as a security vendor and a security partner holds great importance. While both may seem interchangeable at first glance, how an organization is viewed by its clients can have a huge impact on the success of its security programs. At the heart of this differentiation is the concept of relationships and how they shape the dynamics between providers and their clients. Time, care, and diligence For security vendors s...
Misconceptions about AI and analytics in video security are common due to the rapid evolution of the technology and varying levels of understanding. Artificial Intelligence (AI) and analytics are increasingly used as interchangeable terms when discussing video security cameras. AI v/s analytics While there is some overlap, it is important to articulate the differences between them when speaking to stakeholders or customers. As the myriad types of AI gain more prominence in the global dialog&...
If you were to ask people outside our industry what door and access security entails, chances are their answers would reflect their common encounters with locks, security guards, cameras, and maybe metal detectors, badges, or automatic doors. But if they were curious enough, they’d probably be astounded to learn how extensive, intricate, and interesting the business can be and, of course, how vital it is to life safety, physical security, and cybersecurity. Integrated, inter...
The autumn equinox, which marks the start of autumn, occurs this weekend on Saturday, September 23. With darker evenings ahead, the experts at ADT have shared five ways to maximize your home's security. Author's quote Michele Bennett, General Manager at ADT UK&I comments: “Opportunistic thieves use darkness to their advantage, so it’s no surprise that the number of burglaries committed increases when the darker nights draw in." He adds, "Our 2022 burglary report found that bu...
Daniel May of Consort reviews the integration of access control systems in healthcare settings, outlining the benefits and key considerations decision-makers must make throughout product specifications. From patient safety and traversal to the protection of sensitive data and pharmaceuticals, healthcare environments are faced with several operational challenges. And where security remains at the forefront of decision-making, modern access control systems may often hold the answers. Physi...
Security systems represent a significant investment, yet many organizations still only use a small percentage of their physical security systems’ capabilities. That’s before we even begin to consider the different ways that the likes of video, access control, and ANPR can add additional value beyond security by serving the needs of other business functions. Whether that be to obtain additional insight, streamline compliance, or drive operational efficiencies. Consumption ga...
Global transportation networks are becoming increasingly interconnected, with digital systems playing a crucial role in ensuring the smooth operation of ports and supply chains. However, this reliance on technology can also create vulnerabilities, as demonstrated by the recent ransomware attack on Nagoya Port. As Japan's busiest shipping hub, the port's operations were brought to a standstill for two days, highlighting the potential for significant disruption to national economies and supply cha...
Mass attacks continue to lead the news far too often. All are horrific and disturbing, but the heartbreaking tragedies that have unfolded on school campuses touch us the deepest and have the most profound effects on our communities. NTAC statistics According to a January 2023 report from the United States Secret Service National Threat Assessment Center (NTAC), K-12 events accounted for 6% of all mass attacks in public and semi-public spaces between 2016 and 2020. 6% may strike some as being...
Organizations of all types have made it a priority to better track who is coming and going inside their facilities and on their property. This can include an HVAC technician who needs to be inside a building for several hours to fix a faulty air conditioning unit or a parent who volunteers each week in their child’s school. Technology-based visitor management With considerable advancements in visitor management systems in recent years, organizations are now benefiting from technology-b...
Our recent survey on the state of access control in 2023 showed that HID partners and end users, as well as security and IT professionals, may have varying needs and concerns but nearly all agree on one thing: the need for sustainable solutions. Operational transparency In fact, sustainability was a top issue for almost 90% of our survey respondents. Our end users and their consumers are primarily driving this demand, with ever-increasing numbers asking for operational transparency...
Open platform video technology software is more than just a product; it's a tool that helps customers achieve their desired business outcomes. Safety, round-the-clock security, and increased operational efficiencies are now the norm due to video technology. Responsible Technology Despite humanity’s impressive technological advances, we also recognize the immense responsibility that comes with technological innovation. It's not enough to focus solely on the positive impact video technolo...
There’s been a long history of people thinking of “gates, guards, and guns” when referring to physical security. And for a long time, this was the norm. When analog cameras required significant amounts of wiring and a dedicated guard to watch said feeds (think about any action movie from the 90s), the assumption was that security was protecting assets, but had little to do with the overall business. Defining security with recent advancements Fast forward to more recen...
Keeping people and property safe is the purpose of the entire security industry, and the methods for ensuring safety take numerous forms. From cameras to paging horns to door locks and badge readers, facility managers and security manufacturers must consider multiple factors for securing a building and managing emergencies. Mass notification is critical for many customers to protect a facility and keep people safe. Still, the technology may consist of many elements from one or multiple manufac...
Along with the growing adoption of cloud, SaaS applications have accounted for more than triple of the account-takeover attacks between 2019 and 2021, alone. Any given breach can potentially bankrupt many small businesses, with average costs reaching USD 4.35 million in 2022, according to a 2022 IBM report. Every business, no matter its size, must minimize these risks by deploying a range of cybersecurity tools and procedures. One of the most important elements is multifactor authentication (MF...
Inadequate security measures on your essential infrastructure can have severe consequences. Consequences Consider the rail industry: If a vandal cuts the cables on a vital mechanism that controls train signals, train safety is jeopardized. To avoid train collisions or derailments and thus significant damage to property and potential loss of life, the operating company must shut down the service until the infrastructure is repaired and the network is up and running again. The disru...
Regardless of their experience level or location, there is always a sense from close protection practitioners that there's a hunger to get back into the field and closer to the action. And why not? International travel coupled with diverse and challenging environments is all tied to a sense of mission. This is quintessential for close protection teams and starts with business travel. Travel concerns But, while increasing, it's safe to say that business travel is unlikely to return to...
The security industry is going increasingly digital these days, with more small- and medium-sized businesses joining their global brethren by moving their data to the cloud, leveraging the benefits of artificial intelligence, and embracing more open solutions. Innovation is expected to continue at a rapid pace, thanks in part to the residual effects of the pandemic which has driven changes that might have otherwise taken five years or a decade or more to get into customers’ hands on a glo...
As the cost-of-living crisis intensifies in 2023, owners of construction companies will place a greater emphasis on environmentally-friendly materials, public safety, and strategies to increase value. Physical protection Key events in 2023 will have an impact on the physical protection of people, property, and businesses. King Charles III's coronation in May will be the focus of nationwide large-scale gatherings and celebrations and is already receiving security preparations. Even though this...
The nuances of data privacy continue to bombard organizations from all angles, and, amid the impending sunset of Universal Analytics (UA), it’s time to stop playing catch-up. Instead, by enacting future-proofing strategies around data as a first port of call, long-term compliance can be achieved as an automatic byproduct. Data privacy At data privacy’s ‘sunrise’, companies’ efforts were largely targeted towards the customer, ensuring that the ever-growing extent o...
Video surveillance has become the king of data—and is known to be the largest producer of data in the world. A single day of video surveillance is estimated to produce more than 500 petabytes of data—for context, a single petabyte is equivalent to 1,000 terabytes – and that number is only expected to grow. Why is it expected to grow? The answer lies with new and emerging technology, and the way that technology operates. For physical security teams, the rapid amount of data the...
Residential burglaries and break-ins are a problem for many homeowners. The FBI estimates there were approximately 1,117,696 burglaries in 2019 in the United States, which accounted for 16.1% of property crimes. Having proper home security can not only protect your home and belongings, but it can also keep your family safe. Even if you’re new to the idea of having and using smart home security devices, it’s easy to get started. This guide will provide the information and actionable...
With Black Friday on the horizon and shops and warehouses busier than ever, Elliot Roddy, Operations Director at CDX Security Group has shared some tips on how to keep the must-have gift items safe and secure: Regular monitoring and CCTV, Stock control and audits, and Partner with a trusted security firm. Staying alert with the must-have items Each year, we see certain items gain popularity and become the year's must-haves. This year, social media and the rise of TikTok have accel...
In the past five years, the retail landscape and the relationship between consumers and businesses has shifted drastically. It wasn’t too long ago when shopping at malls was considered a family activity and consumers shopped at local stores where they knew and interacted with sales personnel. Today, however, malls and interactions with employees are relics that accurately portray the way retail used to work. Retail companies have shifted their consumer model to focus on the online market...
There’s a new security paradigm emerging across malls, server farms, smart office buildings, and warehouses, and its advantage over the status quo are so broad they are impossible to ignore. Instead of a lecture, let’s start with a short narrative scenario to illustrate my point. Darryl's work Darryl works as a security guard at the Eastwood Mall. Like any typical evening, tonight’s shift begins at 9:30 PM, as the stores close and the crowds thin. His first task: Ensure that...
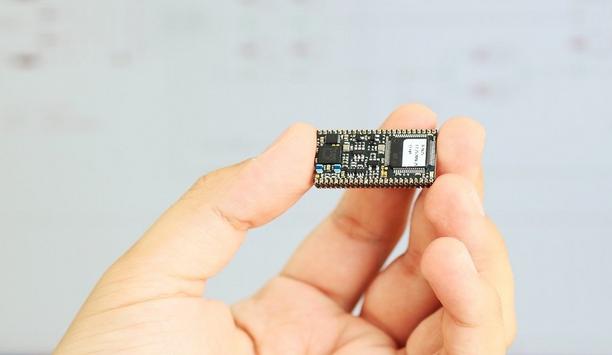
In recent years, multinational corporations such as Cathay Pacific, Facebook, Uber, and numerous others have been heavily fined due to security and data protection violations. This period has seen data protection laws increase as more and more information is gathered and shared online. As such, it becomes crucial to account for security capabilities when choosing an embedded device that touches potentially sensitive data. RFID readers RFID readers very much belong to the ecosystem wherein per...
Although the wider adoption of 5G, together with faster connection speeds and improved bandwidth, opens up new prospects for telecom service providers, it also poses new risks in terms of network security. This article explains how telcos can make their newly-established 5G networks as well as telecom software solutions more impenetrable and secure. Implement robust device authentication protocols 5G is set to spur a wide-scale adoption of connected devices in the business and consumer sphere...