Cloud security
White papers

How To Lower Labor Costs When Installing Video Surveillance
Download
Total Cost of Ownership for Video Surveillance
Download
Guide For HAAS: New Choice Of SMB Security System
Download
Integrating IT & Physical Security Teams
Download
Understanding All-In-One Solutions
Download
Top 7 Trends To Watch In The Physical Security Industry
Download
2024 Trends In Video Surveillance
Download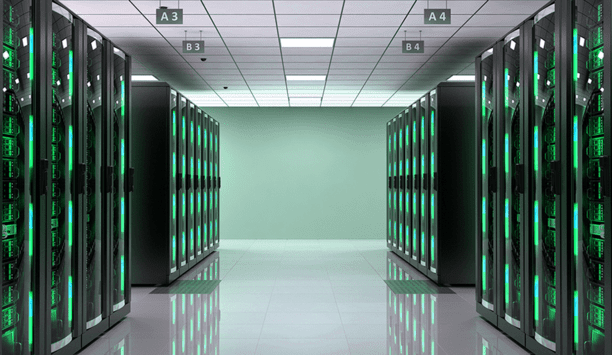
Securing Data Centers: Varied Technologies And Exacting Demands
Download
How To Create A Successful Physical Security Roadmap
Download
The Real Cost Of An Outdated Video Security System
Download
Securing Your Growth With Video Surveillance
Download
The Top 4 Reasons To Upgrade Physical Security With The Cloud
Download
Access Control: The Enterprise Buyer's Guide
Download
Integrating Control Access And Security
Download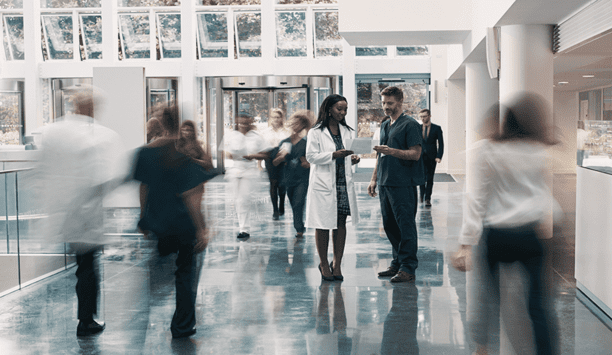
Securing Care Closer To Patients
Download

News
BT Group’s Digital Unit has announced the launch of an innovative internal platform to help the company tap into the power of large language models (LLMs) from providers such as Anthropic, Meta, Claude, Cohere, and Amazon. The GenAI Gateway, built in collaboration with AWS and using Amazon Bedrock, Amazon SageMaker, and AWS Professional Services capabilities, provides secure, private access to a range of natural-language processing and large language models, a critical tool BT Group will use as it embeds AI into the way it runs the business. GenAI Gateway GenAI Gateway gives BT Group protection against ‘lock-in’ to any given LLM if any other issues emerge Ad-hoc use of LLMs, while appropriate for test and development work, is not well suited to large-scale use; cost control, security, and privacy need more careful management. LLM performance also needs to be monitored, for unexpected errors (e.g. “hallucinations”) and model decay over time (where LLMs stop behaving as expected). The GenAI Gateway also gives BT Group protection against ‘lock-in’ to any given LLM if any other issues emerge. Adoption of generative AI The use of the GenAI Gateway platform will encourage BT Group engineers to use the right model for the right use case, at the right price, as it supports per-use case budget tracking. A consolidated platform reduces duplication of effort and resources, as BT Group scales the adoption of generative AI. Application programming interfaces (APIs), security configuration, and infrastructure management, can all be managed centrally, reducing the risk of error and the cost of maintaining separate LLMs for every use case. BT Group’s modular digital architecture GenAI Gateway is accessed via secure APIs, like all the components of BT Group’s modular digital architecture GenAI Gateway, deployed on AWS, is accessed via secure APIs, like all the components of BT Group’s modular digital architecture. GenAI Gateway uses Amazon Bedrock, a fully managed service that offers a choice of high-performing foundation models from pioneering AI companies like AI21 Labs, Anthropic, Cohere, Meta, Mistral AI, Stability AI, and Amazon through a single API; as well as Amazon SageMaker, a fully managed service that brings together a broad set of tools to enable high-performance, low-cost machine learning for any use case. The platform supports prompt security, chat history, FinOps billing per use case, enterprise search, as well as the use of multiple corporate data sources. Isolation of trained models Central privacy controls include separate tenants for each use case, the use of Personal Identifiable Information filters, the location of the data within the UK and the isolation of trained models from each other, protecting data in line with Group policies and relevant regulations. Guardrails are built into the GenAI Gateway, limiting the risk of jailbreaks or toxic interactions, filtering out queries that go beyond the remit of specific applications – ensuring both performance and ethical guardrails are built-in by design. Data management platform Gen AI Gateway is one of the several key enablers they are deploying to enable BT Group Gen AI Gateway is one of the several key enablers they are deploying to enable BT Group as an AI-enabled enterprise, and they will also use the “data fabric” data management platform to help enforce governing policies for how data can be used, as well as to manage access control and data sovereignty restrictions. GenAI Gateway is live with the first beta use cases. A trial in Openreach is summarizing engineering notes on Ethernet and full fiber jobs, helping to simplify processes and boost productivity for its teams and Communications Provider customers. A second use case, supporting contract analysis for the Group’s Business, legal and procurement teams, is also live. Deployment of generative AI use Fabio Cerone, GM EMEA Telco at AWS, said: “The BT Group GenAI Gateway is showcasing how enterprises can effectively deploy generative AI at scale and speed. It’s been a brilliant, pioneering opportunity to collaborate and work backward from the customer to provide a way to accelerate deployment of generative AI use cases into production with embedded security and compliance." "The GenAI Gateway will trigger the flywheel effect in the adoption of generative AI, delivering quicker results for BT Group and its customers.” New set of technologies Deepika Adusumilli, Managing Director, Data & AI, BT Group’s Digital Unit said: “AI is helping us reimagine the future of our company. We believe that where our data is a constant, we need flexibility with our LLMs." "GenAI Gateway allows us to tap into this powerful new set of technologies at scale, in a way that is safe, responsible, flexible, and scalable, delivering the ambition we have for AI to unlock the human potential within BT Group, today and in the future.”
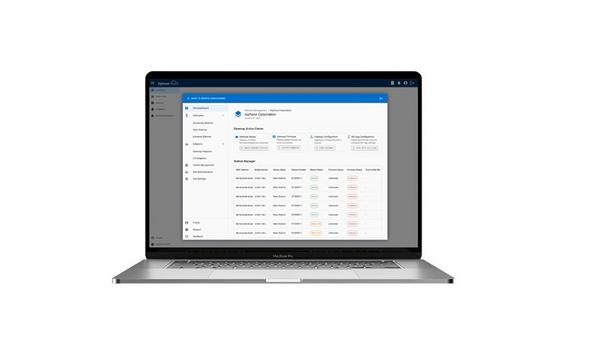
Aiphone, the global pioneer in intercom and security communication, announced the debut of AiphoneCloud and its Remote Management at the Global Security Exchange (GSX) 2024. The cloud platform is set to revolutionize IP intercom management for security integration professionals. AiphoneCloud "We're excited to introduce AiphoneCloud, a platform designed to simplify the work of security integration professionals," said Sean Peterson, Director of Product, Marketing, and Support at Aiphone. "We are committed to continuing the integration and expansion of our offerings and services on the platform to provide our customers with the tools they need to excel in their roles." Simplify security projects with AiphoneCloud The platform streamlines subscription management, providing a centralized hub AiphoneCloud introduces a suite of powerful tools designed to simplify security system management and increase operational efficiency. With Remote Management, security professionals can configure, monitor, and troubleshoot Aiphone IP intercom systems from anywhere at any time. Additionally, AiphoneCloud's on-demand system design tool, QuikSpec, enables security integrators to create customized solutions tailored to their clients' unique needs. The platform streamlines subscription management, providing a centralized hub for the activation and renewal of services. New telephone entry kit The new telephone entry kit simplifies installation by combining key components into a single box set, including an IXG-DM7-HIDA entrance panel, an IXGW-TGW Cloud Gateway, and a SIM card. This kit allows users to communicate and unlock doors remotely via a telephone keypad or the IXG App. By activating the cellular data plan on AiphoneCloud for the Cloud Gateway, security integrators can begin utilizing remote management to service and support their clients’ systems. The AC Series - enterprise-grade access control An intuitive and scalable access management solution for medium-sized businesses In addition to AiphoneCloud, Aiphone is showcasing the AC Nio access control management software at GSX. An intuitive and scalable access management solution for medium-sized businesses seeking enterprise-level features and benefits. Pair with any Aiphone intercom solution for an added layer of protection and control. Visit at GSX 2024 Experience Aiphone solutions, including the IX | IXG Series IP Video Intercom System integration with i-Pro and Genetec, at Booth #1186 during GSX 2024 from September 23rd to 25th. See firsthand how Aiphone can transform security and communication systems.
At GSX 2024, Hanwha Vision (Booth 1701) is highlighting its full range of AI-powered, cloud-connected surveillance solutions, from hardware devices offering 24/7 protection to software-based business intelligence delivering new data-driven business insights. GSX attendees will see new applications of AI in Hanwha Vision’s IP cameras enabling precise detection, robust search, elevated data analysis, and enhanced image quality. New OnCloud VSaaS Hanwha is showing how cloud capabilities enable on-premise and remote surveillance management With the new OnCloud VSaaS and the full ecosystem of cloud-based apps, Hanwha is demonstrating how cloud capabilities enable on-premise and remote surveillance management, giving security professionals the highest level of flexibility for managing their surveillance resources. “The convergence of hardware devices and intelligent software solutions is accelerating, creating new requirements for effective security and surveillance,” said Miguel Lazatin, senior director, marketing, Hanwha Vision America. AI-based security cameras Lazatin added: “The data our cameras capture keeps everyone safe, but it’s also an invaluable source of meaningful and actionable insights to drive informed business decisions about staffing, sales, customer service and any number of business-related functions.” At GSX, Hanwha Vision is featuring its diverse range of AI-based security cameras, including dome and Pan-Tilt-Rotate-Zoom (PTRZ) models, with ongoing demonstrations showcasing precise detection, smart search, data analytics, and enhanced image quality. Video compression technology Most compact 4-channel model open with AI and built-in IR, its versatile design assures seamless integration One highlight is Hanwha Vision’s 4-channel multi-directional camera (PNM-C16013RVQ), boasting a 360-degree wide-angle view. This product is equipped with WiseStream III, a video compression technology that supports AI analytics while reducing bandwidth and storage requirements. Integrated with IR LEDs, it delivers clear images even in low-light conditions. The most compact 4-channel model available with AI and built-in IR, its versatile design ensures seamless integration in various indoor and outdoor environments. NVIDIA Jetson™ platform Hanwha Vision is introducing a new 4-channel AI PTRZ multi-directional camera (PNM-C32084RQZ), built on the NVIDIA Jetson™ platform. This camera provides access to the NVIDIA Jetson module and AI app ecosystem, ensuring superior image quality and flexibility, along with powerful AI-based object detection and classification features. The company is also featuring its AI Box (AIB-800), which allows the easy addition of AI functionalities to standard security cameras without built-in AI. Cloud-based solutions These two solutions are planned for a North American market launch later this year Using Hanwha Vision's proprietary AI algorithms, the AI Box supports real-time AI video analytics across up to eight channels, detecting and classifying people, vehicles, faces, and license plates, while distinguishing between monitoring objects and environmental factors like trees, shadows, and animals to reduce false alarms. Hanwha Vision is also showcasing its cloud-based solutions. These include DMPro, which offers device maintenance and health monitoring, and SightMind, which provides AI-powered data analytics with visualized insights. These two solutions are planned for a North American market launch later this year. Management of video surveillance systems Both DMPro and SightMind enable more intuitive and efficient management of video surveillance systems and support effective data-driven decision-making. Hanwha Vision’s goal is to accelerate its transition to becoming a platform-centric solution provider through these types of innovations. Hanwha Vision is also exhibiting other key cloud-based solutions, such as OnCloud, VSaaS (Video Surveillance as a Service), and FLEX AI, which uses AI to self-learn objects defined by users.
Highly satisfied visitors, a significant 25 percent increase in exhibitors, and countless successful discussions at the trade fair stand: After four intensive days, the pioneering trade fair for the security industry, Security Essen, has come to a successful close. With more than 500 exhibitors from 36 nations and over 20,000 trade visitors - an increase of 17 percent - from 86 nations, the trade fair offered a comprehensive platform for innovations and future trends relating to security solutions for companies, private households, and public spaces. Security Essen 2024 “This strong response impressively underscores the importance of Security Essen as an indispensable platform for the international security industry,” says Oliver P.Kuhrt, CEO of Messe Essen. “This is particularly evident from the fact that decision-makers were here on site. Three out of four visitors are significantly involved in procurement and purchasing decisions in their company - a high-caliber target group.” The exhibitors The demand for security solutions is constantly increasing, which was felt in the exhibition halls The exhibitors – ranging from global market pioneers, niche players, hidden champions, associations, and institutions to start-ups - reported excellent conversations and high-quality contacts at their exhibition stands. The demand for security solutions is constantly increasing, which was felt in the exhibition halls. This also reflects the sector's growing economic significance. In Germany alone, turnover in the security industry has grown by over nine percent more than 31 billion euros within a year. Cloud-based access solutions “We noticed this drive at our stand - especially with the Salto world premiere for cloud-based access solutions,” says Axel Schmidt, Chairman of the Security Essen Advisory Board, Managing Director of Salto Systems, and Chairman of the Board of the BHE Federal Association for Security Technology. “In its 50thanniversary year, Security Essen has once again reaffirmed its position as the pioneering trade fair. Whether it's access control, perimeter protection, video surveillance, or burglary protection: all exhibition areas showcased trends in system integration and AI support.” Stand-alone solutions AI provides support in data analysis, but also in security - for example during patrols Stand-alone solutions are evolving into open products with many interfaces for integrating additional technologies such as alarm systems, and video or fire alarm systems. AI provides support in data analysis, but also in security - for example during patrols. Robot dogs that can also record images, detect gases, or find holes in fences were on display. The focus also extended to personal protection. For example, exhibitors showed personal protective equipment, including discreet sweaters that can withstand knife attacks. Visitors praised the innovations and the supporting program The majority of visitors at Security Essen came from installation companies, security services, and industry, but also from the construction industry and public authorities. They were primarily interested in solutions relating to access control, video surveillance, intrusion, security services, access and entry barriers, and mechanical security technology. Trade visitors were highly satisfied with the innovations on display and the supporting program. With numerous events, the trade fair offered them real added value: Drones are becoming increasingly important in the security industry. At the first European Drone Conference, experts discussed innovative applications and safety aspects of drone technology. Spectacular explosive attacks on financial institutions have made headlines in the past. The New Banks and Savings Banks Day showed how the institutions can protect themselves. There were over 400 registrations for the training and further education day organized by the BDSW Federal Association of the Security Industry. Pupils, students, trainees, and retrainees came to find out about career opportunities in the security industry. The DNS Digital Networking Security Conference focussed on pressing digital security issues. The presentation by intelligence and crime analyst Mark T. Hofmann, who provided insights into the psychology of cybercrime, was particularly well attended. Exhibitors and their products took center stage at the security experts' forum. The Outstanding Security Performance Awards OSPAs honored particularly outstanding achievements for the security industry. Already strong interest in Security Essen 2026 Already, nine out of ten visitors and 86 percent of exhibitors have confirmed their participation 91 percent of visitors praised their visit to the trade fair and recommended pioneering trade fairs for the security industry to others. Already, nine out of ten visitors and 86 percent of exhibitors have confirmed their participation in the next Security Essen, which will take place from September 22 to 25, 2026, at Messe Essen. Company participation “These figures are a compliment, confirmation, and order for us at the same time,” says Oliver P. Kuhrt, CEO of Messe Essen. “We are delighted that during the ongoing trade fair, companies such as Hekatron, NSCSicherheitstechnik, Advancis Software & Services, Deister Electronic, ABI-Sicherheitssysteme, Rohde & Schwarz, and Ajax Systems have already confirmed their participation for Security Essen 2026.” “The industry needs Security Essen” Uli Schunk, Head of Marketing at Advancis, “Our conclusion is very positive, we had many great conversations and more visitors at our stand than last time." "There were many concrete project inquiries - not only from Germany but also from other European countries. We experienced the fair as consistently well-attended, and the atmosphere was excellent.” Scope of Security Essen Thomas Taferner, Head of Sales and Marketing at Telenot Electronic, “The industry needs Security Essen - both now and in the future. It is the only trade fair where the full range of security technology can be experienced." "We are very satisfied with the number of visitors this year and the response to our presence at the fair. Our stand was almost always full and the trade audience was highly qualified." Great feedback "We had many visitors from installation companies, but also large corporations, authorities, and municipalities, including many international representatives. We are looking forward to Security Essen 2026 and have already booked our booth space again.” Andreas Diekmann, CEO of NSC Sicherheitstechnik GmbH, "We are very satisfied with our presence, received great feedback on our booth and had many high-quality conversations. Our booth party was fantastic! We thank all our guests and look forward to Security 2026!”
Expert commentary
As the backbone of community welfare, healthcare facilities cater to crucial public needs from emergency care to specialized medical treatments, and due to its position as a significant facet of the world's critical infrastructure, the healthcare sector faces a multitude of challenges in ensuring patient and visitor security, managing high traffic, and safeguarding sensitive data. Medical sites, such as large hospitals and urgent care clinics, see a wide variety of patients, medical staff, administrative teams, and visitors throughout the day. In addition to protecting patients, visitors, and staff, healthcare environments must protect medical and patient data, ensure immediate response to urgent medical events, and maintain 24/7 operations. Security challenges Cloud-based solutions have made their mark on healthcare security, offering unparalleled scalability Addressing the security challenges presented by 24/7 availability and high patient and visitor traffic calls for a merging of technology, processes, and security strategies that go beyond what a typical security infrastructure would look like. Cloud-based solutions have made their mark on healthcare security, offering unparalleled scalability, accessibility, and integration capabilities. These advancements address the multifaceted demands of healthcare organizations, ensuring seamless around-the-clock operations while prioritizing patient care and safety. Enhancing Operational Efficiency to Save Lives Cloud-based access control solutions have revolutionized how healthcare security professionals approach collaboration within medical facilities. These solutions offer unparalleled accessibility and insight into patient and visitor security information and access logs, improving coordination among security teams and leading to more accurate monitoring and response to developing medical events. By managing and operating access control solutions via the cloud, healthcare facilities can implement effective physical security measures while ensuring seamless collaboration among staff to deliver the highest medical care possible to patients across facilities. Physical access controls Cloud-based access control systems allow users to securely access and manage physical access controls Cloud-based access control systems allow multiple users to securely access and manage physical access controls and visitor management data simultaneously, enabling them to keep track of patient movements as they are transferred throughout the facility or between different facilities. For larger hospitals or medical campuses with multiple facilities hosting access controls via the cloud empowers users with the ability to find patients and patient data in an instant, as well as opening the door to collaborate with teams separated by long distances, ensuring all team members have access to the information they need to continue saving lives. Scaling the way to top-notch care Healthcare institutions are constantly growing and changing in response to evolving industry regulations and standards, and the access control solutions these organizations rely on should be able to scale to meet their changing needs. To ensure their access control systems can keep up with these growing demands, healthcare security professionals can invest in access control solutions hosted in the cloud to avoid the tedious hardware constraints that come with traditional on-premises solutions. Cloud solutions offer significant levels of scalability, enabling healthcare organizations to adjust their storage requirements and computing resources based on changing requirements on the fly. This capability for flexibility ensures users can manage large amounts of data without significant upfront investments in hardware. Cloud-based access control solutions Cloud-based access control solutions provide healthcare organizations with the flexibility they need to expand their access In addition to compliance with changing regulations, cloud-based access control solutions provide healthcare organizations with the flexibility they need to expand their access control platform across a growing campus or multiple buildings. Larger healthcare facilities typically consist of multiple sites of varying sizes across diverse landscapes, each with distinctive security needs. Systems hosted in the cloud provide scalability and flexibility for user organizations, allowing security teams to modify or expand upon their security infrastructure as needed without spending on costly new hardware. This adaptability is crucial for helping address varying risks over multiple sites, providing security personnel the flexibility they need to ensure patient safety over long distances. Ease of use for security teams To truly understand the value of a cloud-based access control system, healthcare security professionals must consider the long-term savings and ROI these solutions provide by bolstering operational efficiencies and enabling unprecedented scalability. These systems ensure compliance with changing standards and deliver a simplified user experience across platforms, prioritizing security and ease of use for security teams across the healthcare sector.
Security manufacturers throw around the term “scalable” a lot these days, but few dive into what scalable really means for modern organizations and their security programs. Achieving true scalability, or as I like to refer to as “expandable with a purpose,” takes planning and coordination from security pioneers alongside the broader organization. Implementing a flexible strategy is critically important in the age of advancing analytics and intelligence-driven technology. So what exactly do we mean by “scalable”? "Scalable" refers to the capability of a system, process, or technology to handle growth or increased demand without compromising performance, efficiency, or quality. To put it simply, scalability refers to the ability of a solution to expand or adapt to accommodate larger workloads, higher volumes of data, or increased complexity without requiring significant changes to its underlying architecture or design. It’s not enough to create a “fix it and forget it” security program. Not only do the needs of the organizations shift, but growth (or even shrink) is inevitable. How to Approach Growth Pioneers must be prepared to adapt their strategies and approaches to manage security risks For many security pioneers, growth has a trickle-down effect. Expansion through mergers and acquisitions or organic growth, in addition to decreases in facility or employee count, directly impacts the security program. Whether it’s an increase or decrease in size, workload, or scope, these pioneers must be prepared to adapt their strategies and approaches to efficiently manage security risks while maintaining operational efficiency. Here are some ways security pioneers can approach growth: Assess the here and now: Begin by looking at the current state of your security program, including the resources, capabilities, processes, and technology infrastructure. Understanding existing strengths, weaknesses, and areas for improvement can help inform planning for the future. Align with the business: This might be one of the most important considerations to make, but ensuring security pioneers understand the organization’s growth objectives, priorities, and risk tolerance levels is critical to the success of a security program. The most successful security pioneers will be able to align security strategies with business goals to ensure security investments and planning are enabling the company’s growth initiatives. Invest in scalable solutions: Invest in solutions that offer flexibility and can adapt to the changing needs of the organization. Closed systems that can’t integrate fully with new technologies will severely limit the security team’s ability to seamlessly manage the security portfolio. Optimize processes: Reviewing security processes and workflows – or investing in a platform that can streamline this for you – can improve efficiency and effectiveness for your security team. Identifying opportunities for automation and standardization can allow for scaling as business needs change. Collaborate across departments: Preparing for growth initiatives requires extensive communication across departments, including leadership teams, human resources, legal, IT, facilities, and many other stakeholders ensure that security priorities, challenges, and requirements are effectively communicated and integrated. Adopting these approaches helps put security teams in the driver’s seat, effectively managing periods of growth and change without compromising the safety and security of the organization. Technology considerations As security pioneers navigate investments in new technologies that achieve some of the approaches listed above, such as aligning strategy with business goals, optimising processes, and cross-departmental collaboration, there are several considerations to make. Looking at how technology can support (or even hinder) future growth. For example, when making a buying decision around access control systems, security pioneers must consider the number of users, number of credentials, server requirements, facilities, hardware end points, and software features. As these items are being addressed in an RFP or in conversations with a vendor, security pioneers must ask themselves, “Is there a scenario where my program will outgrow the system’s capabilities in any of these areas?” If so, the answer might be to select a different solution. Security pioneers must consider interoperability. We talk a little about this above, but the importance here cannot be overstated: integration is key. The ability to leverage multiple point solutions, such as access control systems and video surveillance cameras – regardless of manufacturer – provides growing companies with the ability to scale quickly and more efficiently than ever before. Centralizing the ability to pull these solutions into a single security operations management platform allows security pioneers a better view of their security programs in a current – and even future – state. Cloud-based solutions can provide the ultimate scalability factor, providing flexibility and accessibility advantages compared to traditional on-premise systems. Cloud-based, or Software-as-a-Service (SaaS) platforms, can easily scale up or down based on changing needs, accommodate distributed environments, and provide remote access and management capabilities, making them well-suited for scalable physical security deployments. Data-driven insights and analytics can drive decision-making beyond security, making technology investments that provide these critical. Automated workflows, event-triggered alerts, and AI-driven analytics can streamline security processes, improve threat detection capabilities, and reduce manual intervention, enabling security teams to manage larger environments more efficiently. Centralised management of technology investments can create cohesion for security teams. Centralised management and monitoring of physical security systems across multiple locations or facilities enables personnel to efficiently oversee and control security operations, access controls, and incident response activities. Being able to manage security in a single platform provides security pioneers with the ability to assess staffing levels, streamline training, allocate resources effectively, and scale to additional sites and/or solutions as needed. Tasked with building a security program that can adapt to the changing needs of the organization, security pioneers must consider a number of factors when setting strategy. First and foremost, taking a close look at the existing program to identify strengths and weaknesses, then truly assessing the technology and processes in place, is the best way to move forward and future-proof the organization.
For K12 education pioneers, embarking on a journey to upgrade security controls can present a myriad of questions about finding the best-fit solutions and overcoming funding hurdles. A majority of public-school districts today are faced with outdated infrastructure and security controls, requiring necessary upgrades. By addressing these concerns head on, schools will ensure a safer environment for both students and staff, mitigating risks posed by unforeseen physical and digital threats. Common K12 security pain points There’s no one-size-fits-all solution in school district security. School districts may have big plans to implement upgraded security systems but to set out on the right foot, pioneers must have a clear vision of their long-term strategy. When embarking on their security journey, education pioneers often wonder where to start and what exact steps are they need to be taking to identify and address weaknesses. Local K12 and government pioneers are promoting and mandating security assessments to uncover safety gaps on campuses and mitigate these risks with advanced technology solutions. Not only do assessments provide detailed, customizable roadmaps for district pioneers, but they also recommend technologies and funding opportunities to help close threat gaps. K12 school districts are mainly vulnerable to cyber-attacks due to the sensitive nature of student records In today’s climate, schools face a growing number of physical and digital security threats. From a cybersecurity standpoint, K12 school districts are particularly vulnerable to cyber-attacks due to the sensitive nature of student records. However, only one-third of these districts have adequate staffing to address threats effectively. In addition, according to a recent survey from Johnson Controls and Forrester Consulting, security decision-makers are having trouble receiving actionable insights. Nearly two-thirds of respondents said that they struggle to receive information from all necessary systems regarding their security threats. To gain more clarity into what school districts need in terms of security tools and threat mitigation, implementing system-wide monitoring and optimization can be invaluable. This approach enhances equipment and operational efficiency, while providing necessary resources and expertise for critical patch updates across all systems, strengthening their overall security posture. Achieving a well-rounded security program In the past few years, AI technology has emerged as a trending solution and is generating considerable attention. While the allure of implementing cutting-edge technologies is undeniable, it’s important to recognize that a robust security program hinges on solid access control. Access control technology provides administrators with the means to oversee and regulate entry into facilities, serving as the foundation for basic physical security. The technology helps administrators and staff control access to multiple areas from web-enabled devices, even during lockdowns which is crucial in emergency situations. School district pioneers should utilize available digital risk assessment tools to uncover threat areas Once basic security controls are in place, school districts must address their next set of security pain points and identify which solutions meet their specific needs. This involves identifying and prioritizing the highest need and most cost-effective investments that will have the greatest impact on enhancing security measures. To accurately determine which security solutions are needed for a specific environment, school district pioneers should utilize available digital risk assessment tools to uncover threat areas and determine levels of priority. By focusing on these priority areas, districts can allocate their resources and efforts where they are needed most, ensuring maximum effectiveness in mitigating risks and vulnerabilities. Securing funding before approaching deadlines A major challenge for school districts surrounding campus security is identifying and securing the necessary funding to implement solutions aligned with their goals. Leveraging available funding sources is critical, especially considering certain programs are approaching their deadline, like the Elementary and Secondary School Emergency Relief (ESSER) fund. Announced during the pandemic, ESSER is a funding program that has allocated nearly $190 billion in aid to U.S. public school districts to fund projects benefitting the well-being of occupants. Notable ESSER funding deadlines to keep in mind as the clock winds down include September 30, 2024 Notable ESSER funding deadlines to keep in mind as the clock winds down include September 30, 2024, when schools must attribute all of their funds to assigned contracts. Following this date, pioneers will need to complete all ESSER spending by January 2025 unless approved for an extension into March 2025. As ESSER wanes, school districts are acutely aware of the fiscal cliff in budgets through 2025. However, many states are ramping up grant funding to close the deficit gap. Administrators should become familiar with these grant opportunities at a local and state level. Get started on security plans The time for school district pioneers to act is now. While the safety and well-being of students and staff are always top priorities, it’s crucial to acknowledge that a lack of insight into necessary security upgrades and available funding options will leave districts behind the curve. Seizing the final months of ESSER funding presents an ideal window to address security pain points and build a safer future for K12 facilities. Looking beyond ESSER, pioneers must proactively seek out and leverage other funding avenues to help ensure the continuity of their security efforts and maintain a proactive stance in safeguarding healthy and safe educational environments.
Security beat
The shift from standalone systems to fully integrated solutions is one of the biggest shifts the security industry has experienced in recent years. There is a higher demand for integrated solutions that go beyond just security at the device and software level, and manufacturers have been continuously developing improved application programming interfaces (APIs), and hybrid and cloud-connected solutions. Artificial intelligence (AI) Also, artificial intelligence (AI) plays an important role in modern intrusion systems by helping enable automated threat detection, real-time response, and predictive analysis. AI algorithms can analyze vast amounts of data to identify patterns and anomalies that may indicate security breaches. Security solutions are being developed with a focus on AI and machine learning to provide more proactive and resilient defenses against increasingly sophisticated cyber threats. Benefits of AI AI-driven security solutions can continuously learn and adapt to new threats, providing more robust protection “The practical benefits of AI in security systems include enhanced accuracy in detecting threats, reduced response times through automation, and the capability to anticipate and prevent potential vulnerabilities before they are exploited,” says Sergio Castillejos, President, of Commercial Security at Honeywell. Additionally, AI-driven security solutions can continuously learn and adapt to new threats, providing businesses with more robust and dynamic protection. Unified Intelligent Command user interface Honeywell meets the challenge of better-integrated systems with a unified Intelligent Command user interface (UI). Castillejos says Honeywell continually innovates with the latest analytics and encryption to keep up with evolving threats. Honeywell’s products integrate with many offerings for partners to construct a robust and modern system relevant to their security needs. Advanced cloud-based security Advanced cloud-based security technologies have been developed that offer real-time monitoring, automated threat detection Advanced cloud-based security technologies have been developed that offer real-time monitoring, automated threat detection, and remote management, essential for hybrid work environments, says Castillejos. “These solutions enhance scalability, improve data analytics capabilities, and provide seamless updates reducing significant maintenance costs that help companies to respond swiftly to emerging threats and enable robust, adaptive security measures.” Physical and digital security The best security systems are a combination of physical, digital, and national security, says Castillejos. While Honeywell focuses on providing the best in physical and digital security within their solutions, protecting sensitive and/or personal information must also be within the responsibility of the organizational policy. Cybersecurity for connected devices Some of the challenges in the next five years will likely include integrating advanced technologies Security systems can safeguard this information by being highly configurable while also notifying users of unwanted activity. Sometimes, just restricting access to sensitive areas can be enough. However, in the world of data analysis and machine learning, security systems can audit and report on users who have accessed data to ensure that the protections are in place. Some of the challenges in the next five years will likely include integrating advanced technologies such as AI and the Internet of Things (IoT) while securing cybersecurity for connected devices, notes Castillejos. Balancing act “Additionally, there will be a growing need for skilled professionals to manage and maintain these complex, connected systems,” he says. “Balancing cost-effectiveness with the demand for resilient security solutions will also pose a significant challenge, especially for smaller businesses.” Legacy systems that are susceptible to vulnerabilities like cloning or unauthorized access present the largest challenge to overcome. “However, as technology evolves, it becomes more challenging for a customer to manage a unified security system rather than a collection of unique solutions that all operate independently,” says Castillejos. Disruptive technology But investing in the newest analytics, AI and IoT will not improve a company’s physical security systems if they do nothing with the data. “They are not a replacement for the devices that keep people and property safe,” says Castillejos. “They can enhance a user’s experience and speed up the time to respond when they are planned correctly.” The best security systems will look at disruptive technology as another tool in the overall system. However, the focus should remain on the user experience. If the latest technology is not properly integrated or configured, it will turn into more noise that most operators will ignore. {##Poll1720586145 - Which is the most useful benefit of artificial intelligence (AI) in security systems?##}
Companies at GSX 2023 emphasized new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasizes ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the Mid-Market to the Cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for pure cloud, but there are benefits to be realized from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realize the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘Soft’ Features for Integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organization more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organization more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centers around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasizing performance, protection (cybersecurity), and price, their data centers are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring center where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
A pioneer in the access control sector since 1971, AMAG Technology is looking to the future and the next generation of products that will expand its services to customers. “In our vision, we have advanced approaches that will not only provide our partners with advanced technologies but also ones that are easier to install with tools to expand their services,” says David Sullivan, who was appointed President of the venerable access control company in September 2022. New challenges at AMAG Sullivan brings a new outlook to the AMAG business, a part of Allied Universal, and a new vision to lead the company into the future. We caught up with David Sullivan to discuss his new challenges at AMAG and the journey ahead as the company looks to the future. Q: How does your background inform your approach to leading AMAG? I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry David Sullivan: With the exception of only a few short years, my career has been in access control. I have experience with several systems and have had the privilege to manage several successful access control companies. As a result, I bring a great deal of experience into my role at AMAG. I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry. Q: How would you describe AMAG’s journey over the last several years and how do you see the future? Sullivan: Prior presidents of AMAG always shared their leadership vision and direction with senior leaders located in the United Kingdom. This had an impact on the full direction of the business, sometimes limiting its ultimate success. Before I became a part of AMAG, these senior leaders that were located in the UK retired, placing for the first time the full management responsibilities of the president. This has allowed me to integrate the business into a single team, with single objectives, and a single vision. We expect to begin to reveal this new vision in the coming weeks. We are excited about the future of AMAG and believe we will surprise the industry with our new products and approach in the coming months and years. Q: How important is it that a manufacturer provides both hardware and software solutions? How does AMAG’s approach (in general) differentiate it in the market? We can design the complete solution, providing functionality that others may find more difficult to accomplish Sullivan: Regardless of the manufacturer, we all provide hardware and software. An access control solution is not complete without both. Some of us choose to make our panels, and others do not. Those who are dependent on third-party suppliers are restricted to the developments and direction of that company, and while it might be perceived to be an open technology, it still is proprietary to the hardware manufacturer. AMAG has controlled its manufacturing of panels from day one. The result means that we can design the complete solution, providing functionality that others may find more difficult to accomplish. Q: How does the breadth of AMAG’s product suite provide advantages to customers and/or integrators? Sullivan: AMAG’s product portfolio is unique and provides the end user with an end-to-end identity management solution from one company. Our Control Room PSIM, Symmetry CONNECT Identity Management Solution, Symmetry Access Control, and Symmetry GUEST solutions all integrate to provide the user with a broad set of features and capabilities from a single provider. There is no finger-pointing when we come to support your system. We hold full responsibility for making it work and can quickly provide a resolution to any application difficulties the user may be experiencing. Q: How does AMAG address the divide between on-prem and cloud systems? How do you help customers make the transition and/or plan for the future? We are in the early stages of developing our next generation of access control in which we intend to provide on-prem Sullivan: In our current product portfolio, we have three products that are cloud-based. Our mobile credential platform (Symmetry Mobile), our visitor management solution (Symmetry GUEST), and our physical identity and access management solution (Symmetry CONNECT) are all offerings that operate in the cloud. We are in the early stages of developing our next generation of access control in which we intend to provide on-prem, web client, and cloud-based offerings. One of the primary objectives is to ensure that the large installed base of systems that are out there today will be able to migrate not only to our next generation but as well to the cloud if the client so desires. Q: What is AMAG’s approach to mobile credentialing? Sullivan: As an access control provider, adding Symmetry Mobile credentialing to our portfolio just made sense. We want our customers to have a forward-thinking solution with the opportunity to save money not only on the physical badges but the cost of printing and distributing badges. Mobile credentials can be easily issued and revoked remotely, reducing administrative overhead, and eliminating the need for physical inventory management. Organizations can centrally configure what devices are used and the read range for each type of device and operating system, thus providing flexibility. Symmetry Mobile offers a customized questionnaire that controls access and reduces liabilities. Q: What has surprised you the most in your first year or so leading AMAG? Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company Sullivan: I wouldn’t say I was surprised by this as much as happy to see, but I would say that the quality of our people was a pleasant surprise. As well, the AMAG product offering is broad and has some unique elements. When coupled with the depth of the resources that we have in AMAG, I know that we are second to none. Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company that has so many talented people. Q: Please describe your dealer channel, and how you are seeking to expand it. Sullivan: The AMAG products are sophisticated and typically are installed for higher-end applications. With this sophistication comes a need to be well able to install such a solution. We have a strong group of certified and loyal partners who help us to deliver these enterprise solutions. We desire to provide our existing partners with updated and competitive systems to offer to their end users. Q: What is the security industry’s (and/or AMAG’s) biggest challenge in the next five years? We need to find ways to provide both our channel partners and the customers with solutions that are easily integrated Sullivan: I believe that the advancements that we are seeing in technology provide our industry with the opportunity to truly change how security is provided to our collective customers. As we advance these solutions, we will need to do so responsibly and in a way that helps the channel’s abilities. We need to find ways to train our partners to both install and support these more complex solutions. At the same time, we need to find ways to provide both our channel partners and the customers with solutions that are easily integrated, moving away from proprietary closed systems to open and cohesive solutions. This will ensure that the users get the best, and most complete solutions. Q: What does the industry as a whole misunderstand about AMAG -- time to set the record straight! Sullivan: Well, I am not ready to openly share where we are heading. We are in the process of putting together some advanced approaches to how we will do business with our partners. We are focused on providing tools that will enhance their services to their customers, and with products that are leading edge. I can only state that all should keep their eyes on AMAG, because over the next few years, we are going to surprise some people, and more importantly make our loyal partners quite powerful.
Case studies
Matsuo Sake Brewery in Arita Town, Saga Prefecture, is one of the historic breweries in Japan. Since its founding by the seventh generation head, Matsuo Sake Brewery has been producing sake in the Arita region, which has been blessed with clear water and abundant nature for over 150 years. Cloud-based security In the pursuit of operational excellence, Matsuo Sake Brewery embarked on a transformation journey on physical security by utilizing VIVOTEK’s cloud-based security service - VORTEX. This improvement initiative aims to enhance security measures streamline workflows and maximize operational efficiency, all in pursuit of sustainable improvements for the brewery. Brewery's challenges Before utilizing VORTEX, Matsuo Sake Brewery faced some hurdles and hoped to maximize product safety. Security Risks within the Winery: Concerns existed about security risks such as unauthorized access and theft, particularly regarding protecting valuable wine inventory. Measures were needed to prevent external intrusion and unauthorized access. Real-Time monitoring: In numerous instances, remote monitoring and real-time video retrieval prove challenging, if not entirely unattainable. This lack of real-time access significantly hampers the ability to respond to site conditions promptly. Challenges in Proper Resource Utilization: Insufficient information regarding the proper allocation and utilization of resources, including personnel and equipment, hindered efficient resource utilization. Reasons for VORTEX integration VORTEX can provide comprehensive monitoring capabilities with high-definition video and audio feeds, allowing administrators to remotely monitor the operation of the brewery without interruption. The ability to access live and recorded video footage from smartphones empowers managers to monitor operations from anywhere, at any time, facilitating swift decision-making. Leveraging VORTEX's advanced AI features enhances security measures such as intrusion detection and attribute search, while also improving operational efficiency. Benefits of VORTEX By utilizing VORTEX, Matsuo Sake Brewery streamlines workflows, reducing operational complexities and enhancing productivity. Real-time insights provided by VORTEX empower administrators to make informed decisions promptly, enabling proactive responses to operational challenges. Optimization of resource utilization and streamlined workflows contribute to cost savings, enhancing the brewery's profitability and sustainability. VORTEX's advanced security features, including intrusion detection and real-time alerts, minimize security risks and ensure regulatory compliance. Results and customer feedback The implementation of VORTEX at Matsuo Sake Brewery maximized operational efficiency and optimized workflows. By addressing key challenges and leveraging advanced technology solutions, the brewery enhanced productivity and cost-effectiveness while strengthening security measures. This initiative established a robust foundation for future growth and success in the competitive brewing industry.
The client encountered serious security challenges, particularly the unauthorized entry into the office premises. This breach highlighted the urgent need for a reliable access control solution. With 200 users needing access through different methods such as RFID cards, Bluetooth®, and QR codes, the client sought a comprehensive, cloud-based access control system that could efficiently manage and monitor access, while also being scalable and user-friendly. Challenges The client sought a cloud-based access control system to address the following challenges: Unauthorized Access Unauthorized individuals had entered the office premises, creating a major security threat. This breach not only endangered employee safety but also put sensitive information and office assets at risk. Credential Management Handling multiple credential types for 200 users was a complex task. The client needed a solution that could seamlessly integrate RFID cards, Bluetooth®, and QR codes without complicating user experience or administrative processes. Scalability and Integration The client required a scalable, cloud-managed solution that did not depend on third-party hardware or software integration. They needed a flexible system that could grow with their needs and be managed remotely without additional dependencies. Solution Matrix implemented a comprehensive cloud-based access control system to address the client's challenges by offering the following solutions: Advanced Access Control Matrix installed sophisticated door controllers and readers to ensure only authorized personnel could access the premises. By utilizing COSEC ARC DC200P controllers and COSEC ATOM RD100E readers, the system effectively monitored and controlled access points, significantly reducing the risk of unauthorized entries. Multi-Credential Support Matrix's solution accommodates various credential types, including RFID cards, Bluetooth®, and QR codes. Through its COSEC APTA app, Matrix enabled Bluetooth® and QR codes as access credentials for the client. This facilitated easy management of different credentials, providing a seamless experience for users while maintaining high-security standards. On-Cloud Deployment The implementation of COSEC VYOM ensured a scalable, cloud-based solution. This allowed the client to manage the system remotely without the need for additional hardware or software integrations, offering flexibility and future-proofing the solution. Results The cloud-based deployment offered the needed flexibility and ease of management Matrix effectively resolved the client’s challenges by delivering a robust, multi-credential access control system that ensured both security and scalability. Unauthorized entries were prevented, credential management for users became effortless, and the cloud-based deployment offered the needed flexibility and ease of management. This all-encompassing solution not only enhanced security but also streamlined administrative processes, significantly improving the client’s operations. Products Offered COSEC ARC DC200P: Two Door Controller COSEC PANEL200P: Access Controller Hub COSEC ATOM RD100E: EM Proximity-based Reader with IK07 design COSEC VYOM ACM 10K User Days: Cloud-based Access Control for 10,000 User Days COSEC VYOM ESS 10K User Days: Cloud-based Employee Self Service l for 10,000 User Days This case study illustrates how Matrix's Access Control and Time-Attendance solution successfully tackled and resolved the client’s security issues, ensuring a secure and efficiently managed office environment.
A major European oil and gas company that acquires, explores, produces and supplies chemical and petroleum products had a cybersecurity challenge. Company leadership wanted a better way to quantify and respond to the industry’s increasing levels of cybersecurity risk. Cybersecurity challenges Pioneers were looking for a new way to understand better and improve their company’s OT cybersecurity. As part of this effort, pioneers wanted to compare the company’s current levels of protection against a series of hypothetical attacks to identify gaps. With operations in several locations and a supply chain network of over 1,000 gas stations, auditing and improving the company’s cybersecurity would be no small task. csHAZOP services To help overcome these challenges, the company called in Honeywell and, specifically, its Honeywell Cybersecurity HAZOP (csHAZOP) services team to perform a detailed design evaluation based on OT cybersecurity risk. The Honeywell csHAZOP solution is designed to deliver a comprehensive set of analysis and recommendations – it goes beyond the standard cybersecurity vulnerability assessment or IEC 62443 compliance audit by adding deeper analysis that is designed to: Investigate a significant amount of what can go wrong, including approximately 500+ attack scenarios – evaluating these for multiple threat actors and different consequences. Address – via risk assessments – both the likely risk reduction through the regular IT type of countermeasures (AV, firewall, hardening, etc.) and the consequence severity reduction through the implementation of safeguards (e.g., hardwiring critical control signals). Estimate residual risk for each hazard, allowing identification and quantification, making mitigation actionable. Focus on process automation cybersecurity risk (csHAZOP stage 1) or production process cybersecurity risk (by adding csHAZOP stage 2 vs. cybersecurity production risk) to add a higher level of cybersecurity analysis from an OT perspective unique in the industry. Determining cybersecurity hazards The Honeywell cybersecurity professionals also identified some high-risk design deficiencies For this project, the Honeywell OT cybersecurity professionals used the Honeywell proprietary csHAZOP method to identify several concrete recommendations for immediate remediation and technical design in the company’s ICS to be considered in upcoming migrations. The Honeywell cybersecurity professionals also identified some high-risk design deficiencies. The Honeywell csHAZOP framework was also used to identify levels of residual risk to determine which cybersecurity hazards were more critical to address versus others. Cybersecurity assessments Honeywell provided targeted guidance on several aspects of the study, using experience from real-world cyber attacks in the industry. Honeywell’s csHAZOP service is one of the few cybersecurity assessments available on the market that is designed to apply counterfactual risk analysis. Given a system’s protective measures, this method helps a company evaluate which cyber attacks (based on countermeasures, security protections, and type of threat actor) may succeed. This evaluation directly links OT cybersecurity to loss prevention and process safety. Honeywell’s csHAZOP report for this oil and gas refinery was considered successful by the customer because of its well-defined procedure, the tools Honeywell has specifically designed for OT systems, and the team’s experience and efforts in OT cybersecurity. Customer's quote “The results of the cshazop assessment from Honeywell went beyond our expectations. We have received a detailed and analytical cybersecurity hazard and operability report concerning both identified risks and realistic recommendations for remediation," said a major refinery in Europe. "Additionally, the report is a valuable tool for future upgrades of our systems as well as new projects and the development of an incident response plan. We intend to repeat this assessment periodically, as it is a valuable tool in our continuous efforts to improve security for our systems from the ever-evolving cybersecurity threats.”
Burger King is a global chain of fast-food restaurants, founded in 1954 in Miami, Florida. It has since expanded into one of the world’s largest fast-food chains, with thousands of locations spanning over 100 countries. The company is known for its commitment to quality ingredients, innovative menu items, and iconic marketing campaigns. With a steadfast focus on continual improvement and innovation, Burger King remains at the forefront of ensuring a secure dining experience for its customers across its global network of restaurants. The company prioritizes robust security measures within its restaurants. Challenge Integrate security system and video surveillance across all Burger King branches in Norway. Burger King, like many fast-food businesses, uses security systems and video surveillance to keep their property safe from theft, vandalism, and unauthorized access. This creates an atmosphere where staff and customers feel safe and comfortable. The main aim was to safeguard the buildings, equipment, employees, and customers while causing as little disturbance to the operation of the chain’s restaurants as possible. Solution Wireless security system with easy-to-use mobile management and flexible access control, ensuring seamless integration into daily operations. Hub 2 Plus Jeweller control panel Hub 2 Plus Jeweller control panel supports a great number of security devices and user groups AlarmLink Oslo AS is a security installation company that operates throughout the entire country. The installer has recommended Ajax devices as a professional solution that meets the most stringent security standards. Each restaurant was equipped with a Hub 2 Plus Jeweller control panel. This model supports a great number of security devices and user groups. Ajax Cloud It is crucial for further scaling, as it allows for accommodating expanding security needs without major infrastructure changes. With four communication channels and LTE support, the hub can be connected to two separate Internet providers over Ethernet and Wi-Fi while having two cellular services ready for backup. It guarantees connectivity to Ajax Cloud and the central monitoring station under any conditions. Motion and opening detectors control all possible entries into the building, protecting against intrusion and burglary KeyPad Jeweller Ajax solutions are designed for ease of use. Through the app, restaurant executives with admin rights can manage the security system directly from their smartphones. They receive immediate notifications when someone enters restricted areas, as KeyPad Jeweller is installed at the service premises entrance. Ajax app Restaurant staff smoothly integrated Ajax devices into their routine, using the Ajax app as the primary interface for the system. Managers arm the system when they leave and disarm it upon arrival. They can efficiently control access to restricted areas and receive real-time notifications for any security breaches. This integration not only ensures smooth restaurant operations but also enhances premises security and monitoring at all times. Seamless integration With Ajax technologies, the restaurant chain effortlessly eliminated the need for costly new installations All suggested features were seamlessly integrated with Burger King’s existing video surveillance system because third-party cameras can be easily added to the Ajax app. With Ajax technologies, the restaurant chain effortlessly eliminated the need for costly new installations. This straightforward integration not only enhanced security measures but also saved the company money. Sleek and modern look Additionally, Ajax devices are visually appealing and seamlessly fit into the interior. Ajax Systems offers security solutions that not only keep things safe but also blend in nicely with any environment. Therefore, the sleek and modern look of Ajax products contributes to a welcoming and safe dining experience for customers. Why Ajax Cost savings on installation: In certain countries, such as Norway, installing security devices can be expensive due to taxes and other related costs. Ajax reduced this expense item by half. The devices are ready to use out of the box, easy to install, and can be added to the system by scanning a QR code. Seamless integration with existing security system: Ajax’s partners, specialists from AlarmLink Oslo AS, took a balanced approach and effectively integrated the existing video surveillance system with the Ajax security system. Easy system management: Ajax solutions are excellent for chain companies, as they streamline the application of security features across all locations. Staff can quickly learn to use the system, which is especially important for businesses with high employee turnover rates. Products Hub 2 Plus Jeweller: Security system control panel DoorProtect Jeweller: Wireless opening detector MotionProtect Jeweller: Wireless motion detector KeyPad Jeweller: Wireless wall-mounted keypad MotionCam Jeweller: Motion detector with a photo camera to verify alarms
Round table discussion
The most common wearable device deployed by security professionals is the body-worn camera. Traditionally used by law enforcement professionals, these devices are finding more and more uses in the corporate security world, and even impacting issues such as customer service. However, the term “wearables” also encompasses a range of other devices, including many worn by consumers. We asked this week’s Expert Panel Roundtable: How are wearable technologies impacting the security market?
While technology like cameras, alarms, and access control systems are crucial components, they are only as effective as the people who use and manage them and the systems that deploy them. When installing physical security systems, the focus should be on the holistic operation of the system rather than the functioning of individual components. However, in the end, overlooking critical factors can undermine the totality of system performance. We asked this week's Expert Panel Roundtable: What is the most overlooked factor when installing physical security systems?
Migrating to the Cloud can be a cultural shift for some organizations, especially when it comes to physical security systems. Challenges such as concerns about data security and compliance, cost management, and a skills gap can make adopting the Cloud seem onerous. But the benefits are there, aren't they? We asked this week's Expert Panel Roundtable: Will the impact of the Cloud on physical security integrators be net-positive or net-negative?
Products