With the release of the Volvo XC90 Armoured, Volvo Cars takes another step as a manufacturer of armored vehicles. The cars are designed and built to provide safe and comfortable travel with a high level of personal protection for the occupants.
"We are proud to be able to offer these armored cars. With our armored cars, we can provide vehicles with a high level of personal security for individuals who require heightened protection," says Stephan Green, Marketing Director at Volvo Cars Special Vehicles.
Volvo XC90 Armoured
XC90 Armoured (heavy) with VR8* protection rating is a car that provides a high level of protection
There is a growing global market for armored vehicles at present, and a large number are manufactured with various protection ratings. Volvo Cars has received numerous requests over the past few years to develop an armoured XC90. Volvo Cars has extensive experience of building police cars, fire engines and diverse special vehicles with high requirements in terms of function, drivability and safety. In fact, the first Volvo police car was delivered back in 1929.
"The XC90 Armoured (heavy) with VR8* protection rating (VPAM BRV 2009/ERV 2010) enables us to offer a car that provides a high level of protection while retaining the car's fundamental properties. Potential customers include security services who would use the car to transport high-profile individuals," says Green.
Armored vehicles
Work to develop a car with a VPAM VR8 protection rating commenced just over two years ago. A certified VPAM VR8 rating means the car has 360-degree ballistic resistance as well as explosive resistance.
The armored car is built on the Inscription version of the Volvo XC90 T6 AWD, which is manufactured at the Torslanda plant in Sweden. The size and nature of the model make it the most suitable vehicle in Volvo Cars' product portfolio for armoring. From Torslanda, the car is sent to TRASCO Bremen GmbH in Germany, a company which has specialized for many years in building high-quality vehicles with high protection ratings.
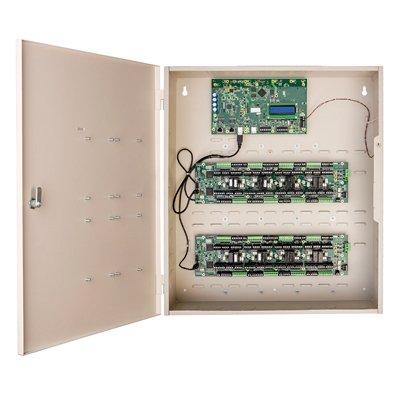
High-strength steel Armor
Production is classified, with stringent procedures and oversight in order to attain the stipulated ballistic requirements"
"Production is classified, with stringent procedures and oversight in place in order to attain the stipulated ballistic requirements," says Green. The high-strength steel armor is 10 millimetres thick, while the thickness of the glass can be up to 50 millimetres. The armor adds approximately 1,400 kilograms to the XC90, which brings the total weight of the car up to 4,490kg (including five occupants). To cope with the increased weight, the car is fitted with uprated suspension and new brakes.
High protection ratings
"Production is carried out with extreme diligence, which is imperative in order to fulfill the exceptionally high requirements placed on this class of security product. We strive to ensure that the car retains its properties despite the extensive armoring. The armor is fitted discreetly to make the car barely distinguishable from a standard XC90. Every customer also has their own unique requirements, which we satisfy by means of customized production," says Green.
The Volvo XC90 Armored (heavy) is available to order now and the first customer deliveries will be made at the end of 2019. Volvo Cars also develops another version of the armored car (light). This means that Volvo Cars has a full portfolio of cars able to offer high personal protection. These cars are built on the XC60 T6 AWD Inscription or XC90 T6 AWD Inscription.
VIP security
These versions are geared towards different clientele than the XC90 Armored (heavy). Users could be individuals or companies requiring a car with a higher level of protection due to a geographical risk or a heightened personal threat. A market for these types of protective vehicles also exists among security services, the police, the diplomatic corps and private individuals.
The cars will undergo a battery of ballistic tests to ensure the required protection rating is fulfilled
The cars are intended for Latin America and Europe. After construction, they are retrofitted in Brazil, where there is considerable demand for these types of cars as well as substantial experience of building them. These vehicles are designed to offer lighter protection compared with the XC90 Armored (heavy).
Protection in active shooter situations
The cars will undergo a battery of ballistic tests to ensure the required protection rating is fulfilled. They primarily provide protection against handguns.
The weight of the car is increased by around 250 kilograms, which is compensated for by upgrading the brakes and suspension. This means that the fundamental properties remain largely unchanged compared to the standard car.
Stay ahead in the era of intelligent security systems powered by Artificial Intelligence with our special e-magazine on AI in security.