Expert commentary
As the technology in omnidirectional cameras continues to improve, they are becoming increasingly more affordable to a wider segment of the video surveillance market Just a few years ago, omnidirectional cameras were a novelty. Today, however, this technology has taken the leap to the mainstream. Think about how ubiquitous Google’s Street View is, and you can gain a better idea of the power of omnidirectional cameras. Even consumers are starting to see many forms of omn...
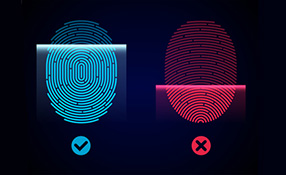
Awareness against fake fingerprints prevent fingerprint from becomingthe choice of biometrics despite their benefits Apple’s refusal to the US government’s request to unlock Syed Rizwan Farook’s iPhone has triggered public interests in personal and information security. Ever since the introduction of Touch ID by Apple, fingerprint technology has been implemented into more and more mobile devices by different manufacturers. It is being adopted as the authentic...
PIAM solutions ensure that credentials are onboarded to all the right systems The number of credentials people are carrying is on the rise. At any given time, an individual may be carrying badges, cards or other ID devices for their office, the gym, public transit and more, not to mention credit cards and government-issued identification. The more credentials people carry, the greater the challenge of managing and tracking these credentials poses, and the more likely that they...
Stringent security policies are necessary in an organization to prevent incidentsof misplaced trust leading to an attack from intruders Trust is a word closely associated with both physical and logical security, after all, knowing who to trust is a key part of any security policy. However, when trust is wrongly assumed it rapidly becomes a key problem and a significant weakness in the security regime. Often the weak link is human nature itself. This means that to begin...
Nationally from 2012 - 2015, there has been a decrease in the money spent on theinstallation, monitoring and maintenance of CCTV compared to the period 2009-2012 The UK has often been referred to as the world’s most watched country in terms of the scale of CCTV surveillance. But a new report claims that UK local authorities have reduced spending on the installation, maintenance and monitoring of public space CCTV systems, while the number of cameras being used is also do...
What effect will the attacks in Brussels have on aviation security? Screenings inpre-security airport areas have been uncommon, but may become standard practice Will the Brussels airport attack herald a new era of aviation security? Like the bombing of Moscow’s Domodedovo Airport in 2011, the Brussels attack took place “landside”, meaning that security precautions would have been low-key and limited to spot checks and the general watchfulness of police office...
ISE’s research shows that healthcare facilities & hospitals security programsto ward off determined attackers going after specific targets A well-known security axiom posits that an effective security program can discourage would-be attackers, causing them to move on in search of softer targets. But it doesn’t always work that way. Take healthcare facilities such as hospitals, for example. Prospective attackers with no particular target in mind may see a w...
Access control and visitor management are evolving and becoming more rooted in an organization’s overall physical security structure Government regulations are driving increased security levels for visitor management. Private industry, where the need to manage and monitor visitors is an equally high security priority, is following suit. As a result, access control and visitor management are evolving and becoming more rooted in an organization’s overall physical sec...
Customer service is a vital part of any vendor’s business approach – from theplanning stages, to installation to maintenance of the access control system In today’s highly competitive and technology-rich security marketplace, an organization’s customer service is as important as the product solution they offer. Let’s face it, you will always remember if the customer service was terrible – or if it was great. Do they go the extra mile or do t...
Portable crash barriers & traffic access control systems allow security integrators to expand their deployments for municipal surveillance and critical infrastructure The Pope does it. The Democratic and Republican National Conventions do it. Leading universities and police departments do it. Just what does this diverse list of people and organizations have in common? They have all used high-security portable barriers at their events with good success. According to manufa...
ASSA ABLOY door handles with built in reader, strike, request-to-exit sensorand door contacts help maintain sterile environment of stainless steel rooms Access control technology has been around for a long time, but security professionals still run into weird problems when designing and installing systems. For example, when a hospital discovered that it was losing $4,000 per patient bed annually in medicines and other supplies, it asked ASSA ABLOY for an access control solutio...
Accurately confirming a person’s identity is one key to improving security forour workplaces, communities, and our nation Perhaps I’m sensitized to the term, but it seems to me that I’m hearing the word “identity” a lot lately. Identity comes up in current news stories about Syrian refugees, for example. Candidates for the U.S. presidency debate how long it should take to confirm the identity of immigrants before allowing them to ent...
ISC West has seen manufacturers' efforts to simplify the installation, serviceand deployment of security solutions for systems integrators Efficiencies come in all shapes and forms for systems integrators in the security industry, and ISC West 2016 was a testament to manufacturers' efforts to simplify installation, service, maintenance and deployment of IP video specifications for installers. GURU Smartphone App With Audit Reporting Capabilities March Networks, Ottawa, Canad...
IP hardware is enabling customers to break free from proprietary security systems,to embrace the system integration available on open platforms Proprietary, closed systems are the bane of security. Yet they still exist. Robert (Rob) G. Lydic, Global Vice President of Sales for ISONAS, Boulder, Colorado, addresses the importance of open platforms in access control and what it means to systems integration in this exclusive Q&A. Trends In Access Control Technology SourceSec...
Access control now includes a strong focus on the data integration sideof the business, as showcased at this year’s ISC West When the category of physical security emerged many decades ago, it was literally all about locks, hardware and creating barriers such as fences to keep people out. Fast forward to ISC West 2016 in Las Vegas this week, where the focus is on intelligent solutions, smart data, cloud-based access control and incorporating audio, video and a wide r...
Many transformations have occurred that have caused PSIM’s true definition to be misunderstood and miscategorized The evolution of Physical Security Information Management (PSIM) over the past ten years has been rapid and transformative. In fact, according to a recent report from marketsandmarkets.com, the global physical security market, estimated to be $65.41 billion in 2015, is expected to reach $105.26 billion by the year 2020. At the forefront of this movement...
UK citizens will vote on June 23rd 2016 on whether to remain within the European Union A significant aspect of the four-month operation leading to the capture in March of Salah Abdeslam, Europe’s most wanted man, is that French and Belgian police worked alongside each other with minimal protocol complications since the countries are not only geographical neighbours but members of the European Union. Abdeslam was arrested for his alleged involvement in the Paris attacks o...
ISC West educational sessions bring into focus some of the challenges, issues and opportunities faced by systems integrators What will be the hot technology at ISC West 2016 this year? Devices to detect drones, more affordable biometrics, or cameras with 360 degrees of clear vision? You’ll probably see some of the above and much more if you’re attending the security industry’s largest trade show, scheduled for April 6 through 8 at the Sands Expo Center in Las...
Working with accurate and detailed product specifications saves time andreduces the possibility of errors throughout a project They’re coming from every angle. Things that zap your company’s profitability: lower hardware margins, escalating labor costs, simply the cost of doing business. So systems integrators have been looking — and finding — new ways to increase revenues. New sources of revenue are emerging from services and even the administration...
Pre-existing networks are not usually designed to support IP video cameras, so aparallel network for their exclusive use is best when it comes to storage The video storage boom shows no signs of slowing down. The talk is not typically how much storage; but where and how to store. Locally-housed (on-premises) storage continues to be the most cost-effective, along with providing the most control over your data. However, prior to considering the storage, it is important to look a...
Energy efficiency extends beyond a company’s running costs vs. its carbonfootprint, to using security technological intelligently to the company’senvironmental advantage Even as manufacturers are becoming greener and innovation is reducing our industry’s carbon footprint , is there more we could be doing? Can we adapt our general operational methods to be smarter and help save the planet? Are we learning from other industries, do we absorb things quickly...
Barriers certified by the U.S. Department of State can be trusted to withstand specified weights and speeds This time of year, in the early spring, there pops up a plethora of trade shows in which security vendors can present their newest marvels to potential customers. Not to be outdone are the barriers manufacturers. Their products will range from a large metal planter to be placed in an area where no traffic is allowed to movable barriers which lower to let a car drive over...
Temperature, dusty and dirty conditions, along with limited access to networkingmakes remote location video surveillance extremely challenging Properly conducting video surveillance for any organization comes with several challenges. Not the least of which is how to architect a system that finds the right balance between quality, cost and bandwidth impact. This becomes even more challenging in non-traditional, demanding environments that are uncontrolled or highly dispersed, w...
Organizations need to protect their properties and people by securing entranceswith security systems and policies Most criminals gain access to a business or organization the same way honest people do – they walk through a door. That door may be left unlocked. It may be propped open. Poor locks may be easily defeated or the door may be inadequately constructed and offer little resistance when attacked. Focus On Multiple-Layered Security It seems obvious the path to...
According to Merit LILIN, the UAE will be a thriving new and potential market in 2016since Europe’s economy is still sluggish The global Chinese community recently welcomed the year of the Fire Monkey with a two-week celebration, concluding with the lantern festival at the end of February. According to Chinese astrology, we are now in the year of the Fire Monkey. What’s in store for businesses around the world? Global economic growth is predicted for the ye...
Festivals bring together a huge number of people, often to large open areas andvenues, which requires a high level of security and protection fromthe organizers Festivals might be all about fun, but the fact that festival goers are out for a good time is an extra reason why the responsibility for safety and security lies predominantly with the organizers. Security during festivals plays an important role in ensuring safety of citizens. Since festivals witness congregation of...
Thermal cameras with video analytics detect with great accuracy in bright sun,fog, rain and other conditions Smart thermal cameras are rapidly becoming the intruder detection solution of choice for securing outdoor assets. Whether for smaller-range applications like protecting entranceways or gates, or securing large perimeters around energy, utility, chemical, or transportation assets, thermal cameras paired with video analytics offer an accurate detection solution that provi...
It can be taken as proven that the trends in urbanization, the mobility of the population and the demographics, have had and will continue to have tremendous impact on our daily lives. These impacts were and are supported by disruptive technology changes (such as the evolution of the internet and mobile communication) and result in higher dependencies of almost all economic and social processes. Compared with former generations, we are spending most of our time in buildings or closed mobile con...
Important biometric capabilities include multispectral imaging, superior liveness detection, and tamper resistance Technology developments are enabling a range of new functionality for biometrics in the security market. Early biometrics solutions had poor performance (high failures during enrollment or acquisition that meant significant percentages of users could not use biometrics), says Phil Scarfo, VP worldwide marketing, biometrics, HID Global. Early solutions were not abl...
The PASS guidelines don’t just point to specific technologies; they address securityissues and help guide school administrators to make their schools safer and more secure From K-12 to college campuses, schools need integrated solutions and proactive measures to lessen the potential of active shooters while targeting general loss prevention and security. The good news is that technology is available to address nearly every threat and challenge, and systems integrator...
Browse expert commentaries
Expert Section
Related videos
CLIQ Connect
DNAKE Access Control Terminals: Minimalist Design, Maximum Security!
Unlock the Future with Abloy Pulse: Keyless, Energy-Efficient Security Systems