Cellphone device and app security provider Trustonic announces that its Trusted Execution Environment (TEE) solution is the first hardware-backed TEE to complete the EMVCo Software-Based Cellphone Payments security evaluation process. EMVCo is the global technical body that facilitates the worldwide interoperability and acceptance of secure payment transactions. As such, this evaluation process confirms that the Trustonic TEE provides a robust security foundation that meets the requirements of software-based cellphone payment (SBMP) and acceptance solutions.
“This technology is already protecting payment apps from small startups through to some of the largest OEMs and cellphone payment providers in the world; all via a simple SDK,” comments Dan Rawlings, CCO, Trustonic.
Trustonic Application Protection
“This certification, and the adoption of Trustonic Application Protection in the financial sector, confirms what many fintechs, banks, payment schemes and mPOS developers already know. Trust, credibility and confidence are built and maintained with high levels of assurance, and combining software and hardware-backed security is the only way to achieve that when the stakes are high.”
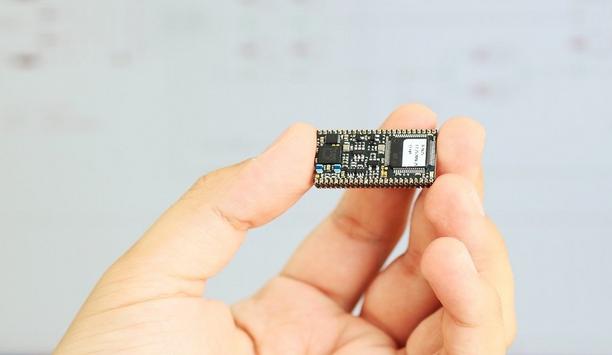
The Trustonic Application Protection (TAP) development toolkit enables developers to easily build and deploy a range of secure financial applications including cellphone payment, banking, and acceptance use cases like cellphone point of sale (mPOS), ‘tap on phone’ and software-based PIN entry on COTS (SPoC). This protects cellphone applications by securing sensitive code, data and processes in Trustonic’s heavily protected TEE.
Software security technologies
The environment continuously upgrades over the course of an app’s lifecycle to take advantage of the most advanced hardware and software security technologies available on smartphones. The platform includes Trustonic’s Trusted User Interface (TUI), which isolates and protects sensitive input and display user interactions from the device operating system – like PIN entry – in app user interfaces.
Hardware-backed TEE technology plays a big role in enabling the cellphone financial ecosystem to achieve its potential
“Hardware-backed TEE technology plays a big role in enabling the cellphone financial ecosystem to mature and achieve its potential,” adds Tim Hartog, Director Cellphone Payments at Riscure, the independent security test laboratory that performed the security evaluation. “This is because hardware-backed TEE technology, like Trustonic’s TEE, can protect apps even if attackers have root privileges on the device."
Secure PIN entry
"With Trustonic providing access to the TEE through TAP, solution developers are now able to effectively secure PIN entry on smartphones. This is a key enabler for using smartphones as acceptance devices.”
Dan Rawlings concludes: “The payments and banking ecosystems are leading the way when it comes to securing apps and data. As regulations like PSD2, SCA and GDPR evolve, privacy is pushed into the consumer domain, security is becoming a differentiator. Developers need to know that hardware no longer limits innovation and user experience, the flexibility of TEE security is nuanced and can be used to deliver simpler, richer and faster user experiences.”
Stay ahead in the era of intelligent security systems powered by Artificial Intelligence with our special e-magazine on AI in security.