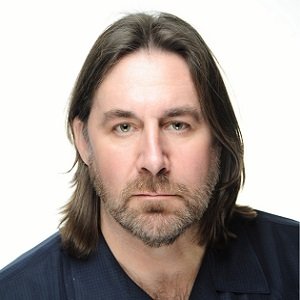
Bernard Parsons

Bernard Parsons
Bernard Parsons is the CEO and Co-founder of Becrypt Ltd. He has over 25 years of experience in software companies spanning robotics, embedded systems, and telecommunications. Bernard is also the Chairman at High Assurance UK - Cyber Industry Association and member of Cyber Security Management Commitee at techUK. He holds a MSc degree in Microelectronics from Middlesex University and has also done PhD in Mechatronics, Robotics and Automation Engineering from the same institute.
Articles by Bernard Parsons
Today, customers are demanding immediacy, personalization and seamless services from their providers and our desire for instant gratification means that those servicing the public need to provide easy...
News mentions
Becrypt, a trusted provider of endpoint cybersecurity software solutions, announced the launch of Paradox Edge, a desktop-as-a-service or secure ‘cloud client’ platform that is optimized f...