Scantronic Intruder Alarms: Communicators & Communication Systems (7)
Browse Intruder Alarms: Communicators & Communication Systems
- Digital Communicators
- Yes
- Transmission Media
- IP / GPRS
- TCP / IP / GPRS
- GSM / GPRS
- GSM
- ISDN
- View more
- Voice Diallers
- Yes
- Make
- Scantronic
- Other Scantronic products
- Scantronic Intruder alarm system control panels & accessories
- Scantronic Intruder detectors
Intruder alarm communicator products updated recently
Intruder alarm communicators - Expert commentary

The number of cyber attacks around the world has been steadily increasing year after year; for example, in 2022, the weekly rate of attacks on corporate networks was 38% higher tha...

Are we doing enough to protect our vital infrastructure and commercial properties? This is one of the key issues the sector is currently dealing with. Crime rates have been rising...

We believe in integrated security solutions, so while a solid gate could prevent sight lines from the house, combining it with other measures such as alarms, motion sensing lightin...
Latest Eaton news

Skills for Security is proud to announce a new partnership with Eaton, a global pioneer in power management solutions. Eaton has joined Skills for Security as a Platinum Sponsor, m...

Intelligent power management company Eaton participated in The White House Office of the National Cyber Director’s Convening on Cyber Workforce event on April 29 to underscor...

Intelligent power management company Eaton announced the North American launch of an innovative new modular data center solution for organizations seeking to rapidly meet the growi...
Related white papers
Preparing Your Organization With Quality Situational Awareness
Mobile access articles
Zenitel, a provider of intelligent communication solutions, announced the launch of two new door entry intercoms: the Turbine Extended Intercoms TEIV1+ and the TEIV4+. The new products display Zenite...
Physical security is essential for a modern production facility, users don’t want just anyone entering the building or accessing secure areas. But what about production machinery? Machine authe...
Munich’s Hofbräuhaus enjoys an iconic status, as both a heritage property and a spiritual home for lovers of German beer. “In this historic building is the world’s most famous t...
Radiofrequency (RF) technology specialists, SPX Communication Technologies launched Evenlode Lite, an entry-level video downlink system designed for regions new to airborne surveillance or those looki...
Wavelynx Technologies, a trailblazer in advanced, secure, and versatile reader and credential solutions, announced the launch of its industry-first app, Configure by Wavelynx, to revolutionize th...
HID, a worldwide pioneer in trusted identity solutions, announces the expansion of its signature line of Signo™ Readers to include models that meet varying customer needs–from harsh condit...
HID, a worldwide pioneer in trusted identity solutions, announces the expansion of its signature line of Signo™ Readers to include models that meet varying customer needs – from harsh cond...
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the launch of Operations Center, a cloud-based work m...
Hanwha Vision, the global vision solution provider, has released the XRN-426S-1T recorder - a compact NVR with a built-in 1TB solid-state drive (SSD). The 4-channel recorder supports AI search, when...
Fences, gates, storage cages, racks, containers, tool cabinets, and other non-standard openings often require restricted access and greater control. In many cases, they are secured with mechanical loc...
IDEMIA Public Security North America, the global provider of convenient and trusted biometric-based solutions, including physical and digital secure credentialing in the U.S, is partnering with My Fam...
ABLOY rose to the top of the list as Finland’s most valued brand of 2024, according to an annual survey by pollster Taloustutkimus. Market research company - Taloustutkimus surveys Finnish consu...
Signo Express and Seos Essentials provide a comprehensive, affordable access control solution designed for small to mid-sized businesses. This suite maximizes security and flexibility without complex...
Award-winning security manufacturer, Gallagher, has announced the appointment of Merv Williams as Chief Marketing Officer (CMO). Williams will lead the development and delivery of Gallagher Security&r...
Level Home, Inc., the company redefining the smart home, announced the release of professional installer editions of its industry-renowned, award-winning smart locks, Level Bolt and Level Lock+ includ...
Healthcare security articles
Rapid technological advancement, artificial intelligence (AI) and machine learning (ML) are revolutionizing traditional on-premises video security systems. These next-level tools are not just enhancin...
Milestone Systems, a global pioneer in video technology, is at the forefront of the video security industry, emphasizing responsible technology innovation across its operations. The company will host...
i-PRO Co., Ltd. (formerly Panasonic Security), a global pioneer in professional security solutions for video protection and public safety announced the establishment of a comprehensive AI governance f...
Gcore, the global edge AI, cloud, network, and security solutions provider announced the launch of Gcore WAAP, its end-to-end web application and API protection solution. Gcore WAAP Leveraging advan...
Barco, a global pioneer in visualization and collaboration solutions, is proud to announce its pivotal role in shaping the visitor experience for the Belgian pavilion at Expo 2025 in Osaka. Bar...
King Faisal Specialist Hospital & Research Center (KFSHRC) is at the forefront of the healthcare AI revolution. Since 2019, the hospital's dedicated AI center has been developing innovative applic...
Convergint, a global pioneer in service-based systems integration, today announced that it has acquired Esscoe, a premier provider of mission-critical security and fire and life safety systems in the...
Huffmaster Management (Huffmaster), the provider of choice for Fortune 500 companies seeking strike services, industrial and healthcare staffing, security services, and more, announced the intern...
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the introduction of a new I/O module to its portfolio of h...
Konica Minolta Europe and Kepler Vision Technologies announce European cooperation in the healthcare sector. Kepler has developed the AI-based Night Nurse solution used in Konica Minolta’s MOBOT...
ST Engineering spotlighted over 20 AI-powered solutions at its InnoTech Conference 2024, expanding AI’s uses and benefits for businesses and critical sectors. Notable AI applications include adv...
Fake videos of celebrities, politicians, and business pioneers have morphed from an amusing novelty on social media to a pervasive threat across all digital platforms that can potentially impact marke...
With cybercrime rising and new cybersecurity legislation tabled by the UK government, BM TRADA is encouraging businesses to achieve ISO 27001 certification sooner rather than later to safeguard inform...
Tquila Automation, an emerging technology consultancy specializing in intelligent automation, is thrilled to announce its expansion into data and artificial intelligence services. This marks a signifi...
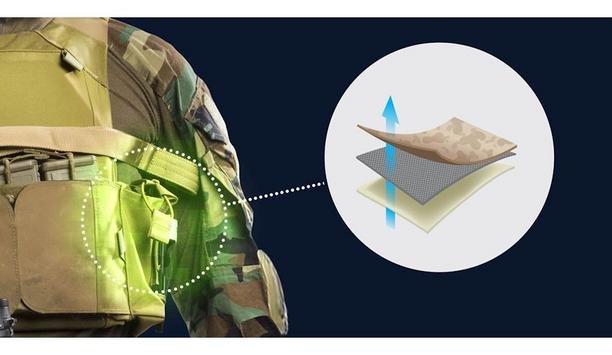
FLIR Systems, Inc. announced it has won a contract with the Defense Advanced Research Projects Agency (DARPA) to rapidly develop novel fabrics with embedded catalysts and chemistries that can fight an...