Technology & Trends - Access control cards/ tags/ fobs
In today's rapidly evolving security landscape, facial recognition has become a buzzword that often triggers privacy and data protection concerns. However, many security professionals may not realize that "facial recognition" is an umbrella term encompassing various technologies, each with distinct applications and privacy implications. Let's dive into what these technologies really mean for security system resellers, integrators, and end-users. Facial recognition tech At its core, faci...
A survey conducted by Blackhawk Network finds the average shopper plans to spend almost half of their holiday budget to buy gift cards this year versus only 39% in 2023. The global gift card market was valued at $1.3 billion USD in 2023, and it is projected to reach more than $5.2 billion USD by 2032. Fraud - a growing concern While gift cards continue to be top of mind for consumers for streamlined gifting, gift card fraud is a growing concern for consumers and businesses alike. Accordin...
The European Union’s GDPR (General Data Protection Regulation) framework represents some of the toughest and most secure privacy laws in the world. Their creation signaled the EU’s dedication to individual privacy rights and generated new standards and requirements for an organization inside or outside of the EU wanting to do business in the region. This privacy stance raises an interesting question: to what extent (if any) will France be utilizing AI-assisted security and biometri...
With the rise of organized retail crime (ORC) making headlines, retailers are grappling with the dual challenge of safeguarding both their staff and store assets, while addressing the economic pressures that impact profitability and consumer demand. RFID technology The key lies in identifying effective solutions to counter the current surge in ORC, enabling retailers to secure their vulnerable staff and protect inventory for paying customers. Technology plays a crucial role in supportin...
It’s no secret that the data security sector is constantly changing. It has an annual CGR of about 12.3%. Future trends in data security Much of this has to do with the rise of cybercrime in recent years, with reports showing that cyberattacks happen as often as every 39 seconds. To combat the growing rate of cybercrime, data security has been on the rise. As we journey further into this era, it becomes evident that a spectrum of significant trends is molding the future of data se...
Physical security is essential for a modern production facility, users don’t want just anyone entering the building or accessing secure areas. But what about production machinery? Machine authentication is often a missing link in the security plan for manufacturers. Why machine authentication? Most manufacturers have made significant investments in physical access control (PAC) for production facilities. Few shops currently hand out physical keys to employees or leave the building...
Mass attacks continue to lead the news far too often. All are horrific and disturbing, but the heartbreaking tragedies that have unfolded on school campuses touch us the deepest and have the most profound effects on our communities. NTAC statistics According to a January 2023 report from the United States Secret Service National Threat Assessment Center (NTAC), K-12 events accounted for 6% of all mass attacks in public and semi-public spaces between 2016 and 2020. 6% may strike some as being...
Organizations of all types have made it a priority to better track who is coming and going inside their facilities and on their property. This can include an HVAC technician who needs to be inside a building for several hours to fix a faulty air conditioning unit or a parent who volunteers each week in their child’s school. Technology-based visitor management With considerable advancements in visitor management systems in recent years, organizations are now benefiting from technology-b...
Our recent survey on the state of access control in 2023 showed that HID partners and end users, as well as security and IT professionals, may have varying needs and concerns but nearly all agree on one thing: the need for sustainable solutions. Operational transparency In fact, sustainability was a top issue for almost 90% of our survey respondents. Our end users and their consumers are primarily driving this demand, with ever-increasing numbers asking for operational transparency...
Open platform video technology software is more than just a product; it's a tool that helps customers achieve their desired business outcomes. Safety, round-the-clock security, and increased operational efficiencies are now the norm due to video technology. Responsible Technology Despite humanity’s impressive technological advances, we also recognize the immense responsibility that comes with technological innovation. It's not enough to focus solely on the positive impact video technolo...
Inadequate security measures on your essential infrastructure can have severe consequences. Consequences Consider the rail industry: If a vandal cuts the cables on a vital mechanism that controls train signals, train safety is jeopardized. To avoid train collisions or derailments and thus significant damage to property and potential loss of life, the operating company must shut down the service until the infrastructure is repaired and the network is up and running again. The disru...
With shoplifting up, 21% in 2022, Peter Jackson, managing director of Jacksons Fencing explores how retail businesses can better protect their premises from opportunistic thieves. We think of shoplifting as people walking out of a store, pockets bulging with unpaid-for goods. However, in town centers and retail parks, the rear doors of shops and delivery areas can be an opportunity for theft on a much grander scale. Thefts and break-ins It’s not uncommon for thefts to be perpetrated fr...
Residential burglaries and break-ins are a problem for many homeowners. The FBI estimates there were approximately 1,117,696 burglaries in 2019 in the United States, which accounted for 16.1% of property crimes. Having proper home security can not only protect your home and belongings, but it can also keep your family safe. Even if you’re new to the idea of having and using smart home security devices, it’s easy to get started. This guide will provide the information and actionable...
For both employers and employees, a safe workplace is crucial. But what about the security of those who keep us safe? Worker safety The physical security industry and its personnel are not only valuable but also indispensable assets in workplaces. Most private and public sectors rely on it to keep their respective communities and stakeholders safe. Hence, it is extremely crucial to ensure the safety of physical security workers. The security industry, regardless of size, must prioritize safet...
With Black Friday on the horizon and shops and warehouses busier than ever, Elliot Roddy, Operations Director at CDX Security Group has shared some tips on how to keep the must-have gift items safe and secure: Regular monitoring and CCTV, Stock control and audits, and Partner with a trusted security firm. Staying alert with the must-have items Each year, we see certain items gain popularity and become the year's must-haves. This year, social media and the rise of TikTok have accel...
In the past five years, the retail landscape and the relationship between consumers and businesses has shifted drastically. It wasn’t too long ago when shopping at malls was considered a family activity and consumers shopped at local stores where they knew and interacted with sales personnel. Today, however, malls and interactions with employees are relics that accurately portray the way retail used to work. Retail companies have shifted their consumer model to focus on the online market...
Redevelopment, restoration, retrofit. No longer are these terms modestly viewed as construction buzzwords. Across the world, there’s an increasing appreciation and a budding culture that maintaining older buildings is the way forward for the planet and its people. Globally, cities are said to be responsible for 78% of the energy consumption, of which, buildings account for around a third of the total. And when users consider that up to 80% of the current buildings are expected to still be...
The outlook for advancements in door security solutions is proving to be an extension of the positive trends that have emerged over the past few years and that continue to evolve in exciting new ways. That’s a good sign as we make our way along the road toward an ever-safer world. Improvements in a hybrid workforce Here’s what we’re seeing: More and more companies are rethinking the office space and how electronic access control (EAC) security and data can help better s...
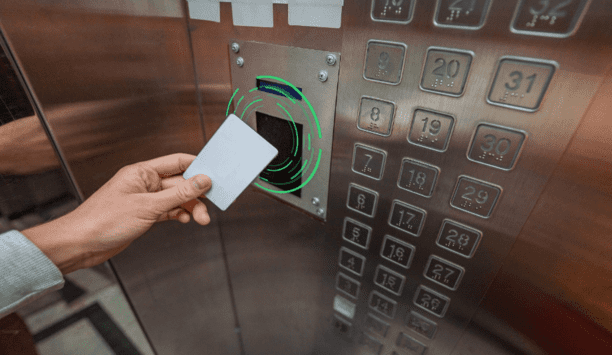
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from building entry to printer access. The right RFID reader can help reduce complexity by migrating diverse older technologies into a single convenient solution. Ways RFID Works Radio-frequency identification (RFID) and smartphone-based credentialling systems using Bluetooth® Low Energy (BLE) or Near-Field Communication...
Although the wider adoption of 5G, together with faster connection speeds and improved bandwidth, opens up new prospects for telecom service providers, it also poses new risks in terms of network security. This article explains how telcos can make their newly-established 5G networks as well as telecom software solutions more impenetrable and secure. Implement robust device authentication protocols 5G is set to spur a wide-scale adoption of connected devices in the business and consumer sphere...
The growing mobile ownership rate, the emergence of more user-friendly banking apps, the tech-native younger generation, and, of late, the pandemic-induced shift to online, all create a fertile ground for mobile banking. Unfortunately, the acceleration of banking app adoption today goes hand in hand with the increase of targeted security threats. In 2022, a month wouldn’t go by without a headline-making mobile banking attack or incident that resulted in stolen funds and sensitive personal...
The smartphone is an integral part of our daily routines. The communication and entertainment device of yesteryear has become a serious player with which we increasingly handle sensitive processes, such as payment transactions. BLE or NFC authentication At the supermarket checkout, more and more customers are pulling out their smartphones instead of their wallets. Apple Pay, Google Pay, or specific banking apps make it possible: to hold the smartphone in front of the reader of the checkout sys...
One of the biggest security trends in the last two years has been the adoption of cloud-based services, spearheaded mainly by an increasing number of video surveillance-as-a-service (VSaaS) offerings. VSaaS market value According to MarketsandMarkets Research, the global VSaaS market value is expected to reach $6.2 billion by 2026. This growth is propelled by demand for remote access video services, less local hardware to maintain, new internet-enabled devices, and a lower total cost of owners...
Organizations have shifted business focus countless times since the onset of the pandemic. While many leaders have been primarily concerned with the immediate health and safety of their customers and employees, 2022 has given rise to a new trend: More than ever, business leaders are seeking security solutions that increase operational efficiency and cost savings as well as improve logistics and business insight. As working environments become more complex, organizations looking to drive higher...
One key aspect of hardware design is choosing an appropriate form factor for your product. In today's world, form factor not only defines your product's size and shape but also includes its aesthetic appeal. While size and shape are important, another aspect that is prominent when dealing with RFID card readers (including NFC and BLE mobile credential readers) is the reader's location within the end device and the size of the RF antenna. This article focuses on some key considerations relating...
With increasing security and public health concerns, contactless credentials are gaining more and more importance. Contactless credentials can be divided into two main categories: soft credentials that include mobile phone applications that tap into their BLE/NFC hardware and transmit the data, and hard credentials that typically include low frequency (125 kHz) and high frequency (13.56MHz) based passive RFID transponders. With the help of these credentials, organizations can tackle safety conc...
As a result of COVID-19, artificial intelligence (AI) has become table stakes for factories. Google’s 2021 Cloud Manufacturing Report found that 76% of manufacturing executives increased their adoption of disruptive technologies, including AI, during the pandemic. AI-based facial recognition technology AI has long been used in the sector to monitor the pace of work and anticipate machine failures, a trend that is expected to continue this year as factories look to optimize operations. Ho...
Technology has certainly become an intrinsic part of our day-to-day lives, from the retail industry, to food and beverage outlets, and even within the health and fitness industry. It’s all around us, in varying formats, making processes more efficient. It has refined some of our older approaches, and in the hospitality industry, this is certainly true. Technological advances are leading the way forward for the future of hotels, and with the sector now free from COVID-19 restrictions, venu...
More and more business security practices are going digital. Mechanical keys are still the backbone of most corporate security plans, and it can be very expensive for companies to switch to electronic access control on a large scale. Therefore, enterprises need to choose the most suitable access control system. What is key management? Key management is the process of protecting, tracking, and scheduling mechanical keys. Why is this important? Because the key carries access to sensitive locatio...
If you’re a security or facilities manager, you may already be aware of the quiet revolution that’s taking place across businesses and organizations up and down the country. By the end of 2020, 20% of all ID and access control systems featured mobile capability, and this is set to increase by a further 34% over the next three years. There’s no doubt that using a smartphone or mobile device in place of traditional credential and access control is a growing trend that’s o...
Browse expert commentaries
Related videos
CLIQ Connect
DNAKE Access Control Terminals: Minimalist Design, Maximum Security!
Unlock the Future with Abloy Pulse: Keyless, Energy-Efficient Security Systems
Climax Mobile Lite: Advanced Personal Emergency Response System (PERS)
Hanwha Vision OnCAFE: Cloud-Based Access Control for Modern Enterprises
Delta Scientific MP100 Portable Barricade Solution
The Key To Unlocking K12 School Safety Grants
DownloadHoneywell GARD USB Threat Report 2024
DownloadPhysical Access Control
DownloadThe 2024 State Of Physical Access Trend Report
DownloadThe Security Challenges Of Data Centers
Download- Access control cards/ tags/ fobs
- Honeywell Security Access control cards/ tags/ fobs
- Paxton Access Access control cards/ tags/ fobs
- PAC Access control cards/ tags/ fobs
- Schlage (Allegion) Access control cards/ tags/ fobs
- Keyscan Access control cards/ tags/ fobs
- All Access control card/ tag/ fob brands