Technology & Trends - Access Control
DIY—the fastest-growing segment of the residential alarm market—has evolved from a niche trend into a major event in which the big dealers are “in” but the small dealers are not. But the good news is that new partnership programmes emerging from central stations are leveling the field so that even the smallest dealers can get themselves an “in.” Why board the DIY train in the first place? It’s become clear the DIY craze is here to stay, with capital inv...
It is more complicated to search through video compared to text-based data Since the launch of Google’s search engine in 1998, Internet search has grown and expanded from desktops to mobile devices, generating over 3.5 billion searches of text, images and videos per day. One likely reason for this popularity is the search engine’s ability to immediately produce relevant results based on search criteria. The security industry, in contrast, has not always taken adv...
Revolving doors have been around for well over 100 years since their invention by Theophilus Van Kannel in 1888. As the story goes, Van Kannel, working in a lobby during a cold winter in Philadelphia, complained about the unpleasant effects of the swing door at the main entrance: “Every person passing through [the exterior door] first brings a chilling gust of wind with its snow or rain, and the noise of the street; then comes the unwelcome bang!” Van Kannel decided to do something...
Part 1 of our Security in Healthcare series Hospitals have a continuous need for security, to update their systems,and to make repairs The healthcare vertical provides plenty of opportunities for security integrator companies. A single large hospital system can supply a dependable ongoing source of revenue to integrator companies, says David Alessandrini, Vice President, Pasek Corp., an integrator. Hospitals have a continuous need for security, to update their...
Angela White was sworn in as President-elect of ESA at the ESX show in June and will take office July 1 The Electronic Security Association (ESA) wrapped up its annual ESX conference June 8-10 at a new location in Fort Worth, Texas, with keynote speakers, educational sessions, networking events, exhibitions, awards and the installation of new officers. Logging its ninth year, ESX is jointly owned and sponsored by ESA and the Central Station Alarm Association (CSAA). This year&...
H.265 compression continued to be a popular topic from exhibitors on the second day of IFSEC Video beyond security, compression, HD over analog and integration were on the lips of several exhibitors at IFSEC International 2016. Strangely for a security exhibition, there were plenty of exhibitors talking about non-security applications on the second day of IFSEC International in London. For Axis Communications, Atul Rajput, Regional Director for Northern Europe, said the...
H.265 compression, apps and the inherent security of security systems were some of the themes to be gleaned on the first day of IFSEC International. Almost every video exhibitor I saw on day one of the show mentioned that many of their products use H.265 compression in these days of high definition, bandwidth-hungry cameras. Over at Vivotek’s stand, for example, Emilio Sanchez, project consultant, spoke of the company’s H.265 Smart Stream compression algorithm. He said this saves an...
There is a contrast between high levels of security inside Westminster and little to no security outside the safe environment The fatal attack on 41-year-old Jo Cox, a Labour member of the British Parliament, on the street in her district in West Yorkshire in Northern England, is increasing calls for greater security of Members of Parliament (MPs). Cox was stabbed and shot to death June 16th outside a library in Birstall, where she was meeting with constituents. There have be...
A public facility with too much security or the wrong kind of security can discourage the public from visiting (Photo credit: Steve Williams Photography) The lethal November 2015 terrorist attacks against several soft targets in Paris have inspired changes in security at facilities considered soft targets across the United States and around the world. Today’s security directors well understand that “it can happen here.” To be clear, it probably won’t....
ONVIF's 1.0 Core Specification debuted in 2008 at Security Essen The adoption of the ONVIF protocol by manufacturers continues to grow. Last year, the number of member companies in the ONVIF forum exceeded 500 and more than 5,000 products are currently certified on the ONVIF website. How did ONVIF achieve this amazing result and experience this wild adoption? More than a decade ago, every manufacturer was defining their own protocols and pushing for Video Management Software...
The landscape for end-to-end solutions is not designed to address thelong-term evolving needs of customers The video surveillance industry has reached an important crossroads where manufacturers can choose to continue in one direction that solely focuses on their own products and profits, or to move forward in another direction that emphasises building partnerships for the greater good of the community. On one side lies the short road of end-to-end, proprietary solutions fro...
There are resources to help guide an organization’s management of cybersecurity risks, most prominently from the National Institute of Standards and Technology (NIST) and the U.S. Department of Homeland Security. NIST defines cybersecurity as "the activity or process, ability or capability, or state whereby information and communications systems and the information contained therein are protected from and/or defended against damage, unauthorized use or modification, or exploitation.&rdquo...
Cloud connectivity can provide a linkage between the mobile users and the facilities and systems they want to interact with From enterprise applications to small businesses, schools, health care facilities and beyond, investments in physical security systems provide valuable resources to help protect people, property and assets – and ultimately the financial security and well-being of the organization. As need and demand for better security has dramatically increased ove...
Drones can satisfy five commercial needs, today: surveillance, patrolling,incident response, mapping and site assessment The military uses drones. So do the police. Drones serve as weapons and surveillance tools.Today, businesses and institutions are applying drone technology to a variety of private security surveillance challenges. Private uses include patrolling facilities and installations such as pipelines from the sky. To be sure, private contractors sometimes weaponize d...
Systems may be reliable and performing as originally intended, but can also beoutdated in comparison to current technology offerings Let’s start by defining what a legacy system is in the context of a security control system. Legacy refers to an installed and operating security control system made up of numerous components, both hardware and software, that have been eclipsed by newer technologies. A shortage of parts and pieces may be creeping in, and it’s also li...
It’s the 21st century already. Isn’t it time we all lived in smart homes? For technophiles everywhere, the smart home can’t come soon enough. The same might be said for the security marketplace, which is well positioned to thrive in the coming era of home automation. The wait could be shorter than we think, given some recent trends and events we are seeing in the home automation market. Let’s consider several of them: 1. Home Automation Is Getting Attention From Silic...
PSIM systems extend their value beyond emergencies by including routinemanagement tools, that provide value during daily operations, such as automatingmaintenance activities Physical Security Information Management (PSIM), an acronym termed to describe a family of software platforms that claim to replace traditional command and control (C&C) systems, primarily used to provide situation awareness in control and monitoring centers of Critical Facilities. Traditional C...
Technology solutions enhance and make manned guarding moreeffective and efficient the quickest way Most companies believe manned guards can help mitigate disturbances and neutralize situations, while at the same time reducing the chance of criminal activities and/or accidents occurring. However, people cannot be omnipresent or always be in the right place at the right time. When combining manned guards with the power of today’s technology, the results are unmatched. Dev...
If anyone tells you that the use of Mass Notification Systems (MNS) is a new trend, it is likely that they do not fully understand it. You have been impacted by mass notification your whole life. Surprised? Every time there is a fire drill at an elementary school, or a bell chimes noon or a blinking light announces a snow-related parking ban, an MNS is being deployed. Ultimately, mass notification is just mass communications. What has changed is the distribution methodology, the granularity and...
Many operators don’t know what’s actually transpiring on their OT networkand, even if hacked, have no knowledge of the assault Innovation in the oil and gas, utility, healthcare and transportation industries is heavily reliant on connectivity - between devices and systems, machines and data, people and processes. This connectivity is great for productivity upstream, mid-stream and downstream, but is also exposes these systems to greater cyber threat. Furthermore, a...
The report says almost 50% of the public transport organizations are willingto broaden the type of video analytics used A detailed survey of public transport operators shows a growing demand for networked/IP systems and video analytics to help cope with the requirements of large surveillance systems. The report, Video Surveillance in Public Transport, published by the international public transport association UITP and Axis Communications, is based on 74 respondents across 30...
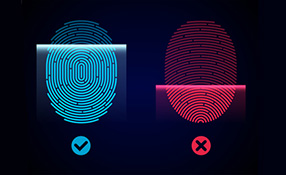
Awareness against fake fingerprints prevent fingerprint from becomingthe choice of biometrics despite their benefits Apple’s refusal to the US government’s request to unlock Syed Rizwan Farook’s iPhone has triggered public interests in personal and information security. Ever since the introduction of Touch ID by Apple, fingerprint technology has been implemented into more and more mobile devices by different manufacturers. It is being adopted as the authentic...
PIAM solutions ensure that credentials are onboarded to all the right systems The number of credentials people are carrying is on the rise. At any given time, an individual may be carrying badges, cards or other ID devices for their office, the gym, public transit and more, not to mention credit cards and government-issued identification. The more credentials people carry, the greater the challenge of managing and tracking these credentials poses, and the more likely that they...
Stringent security policies are necessary in an organization to prevent incidentsof misplaced trust leading to an attack from intruders Trust is a word closely associated with both physical and logical security, after all, knowing who to trust is a key part of any security policy. However, when trust is wrongly assumed it rapidly becomes a key problem and a significant weakness in the security regime. Often the weak link is human nature itself. This means that to begin...
What effect will the attacks in Brussels have on aviation security? Screenings inpre-security airport areas have been uncommon, but may become standard practice Will the Brussels airport attack herald a new era of aviation security? Like the bombing of Moscow’s Domodedovo Airport in 2011, the Brussels attack took place “landside”, meaning that security precautions would have been low-key and limited to spot checks and the general watchfulness of police office...
ISE’s research shows that healthcare facilities & hospitals security programsto ward off determined attackers going after specific targets A well-known security axiom posits that an effective security program can discourage would-be attackers, causing them to move on in search of softer targets. But it doesn’t always work that way. Take healthcare facilities such as hospitals, for example. Prospective attackers with no particular target in mind may see a w...
Access control and visitor management are evolving and becoming more rooted in an organization’s overall physical security structure Government regulations are driving increased security levels for visitor management. Private industry, where the need to manage and monitor visitors is an equally high security priority, is following suit. As a result, access control and visitor management are evolving and becoming more rooted in an organization’s overall physical sec...
Customer service is a vital part of any vendor’s business approach – from theplanning stages, to installation to maintenance of the access control system In today’s highly competitive and technology-rich security marketplace, an organization’s customer service is as important as the product solution they offer. Let’s face it, you will always remember if the customer service was terrible – or if it was great. Do they go the extra mile or do t...
Portable crash barriers & traffic access control systems allow security integrators to expand their deployments for municipal surveillance and critical infrastructure The Pope does it. The Democratic and Republican National Conventions do it. Leading universities and police departments do it. Just what does this diverse list of people and organizations have in common? They have all used high-security portable barriers at their events with good success. According to manufa...
ASSA ABLOY door handles with built in reader, strike, request-to-exit sensorand door contacts help maintain sterile environment of stainless steel rooms Access control technology has been around for a long time, but security professionals still run into weird problems when designing and installing systems. For example, when a hospital discovered that it was losing $4,000 per patient bed annually in medicines and other supplies, it asked ASSA ABLOY for an access control solutio...
Browse expert commentaries
Related videos
CLIQ Connect
DNAKE Access Control Terminals: Minimalist Design, Maximum Security!
Unlock the Future with Abloy Pulse: Keyless, Energy-Efficient Security Systems
Climax Mobile Lite: Advanced Personal Emergency Response System (PERS)
Hanwha Vision OnCAFE: Cloud-Based Access Control for Modern Enterprises
Delta Scientific MP100 Portable Barricade Solution