Qualys, Inc., a pioneer and renowned provider of cloud-based security and compliance solutions, announced its research team, using the Qualys Cloud Platform, has identified 7.54 million vulnerabilities related to FireEye Red Team assessment tools and compromised versions of SolarWinds Orion, tracked as Solorigate or SUNBURST, across its 15,700-member customer base.
Of the vulnerabilities identified, researchers noted that across 5.29 million unique assets most are related to the FireEye Red Team tools. These findings highlight the scope of the potential attack surface if these tools are misused. The research team further identified that 99.84% of the 7+ million vulnerability instances are from eight vulnerabilities in Microsoft software that have patches available.
IT and security organizations
Qualys' solution draws from its native security and compliance platform to deliver vulnerability management"
To help mitigate risk and exposure from this breach, Qualys is providing IT and security teams free 60-day access to its integrated Vulnerability Management, Detection and Response service, which leverages the power of the Qualys Cloud Platform. More information can be found on the Qualys advisory blog.
“The Qualys free solution provides much-needed visibility and response in a single app that many need at a time when IT and security organizations around the world are scrambling to shore up their systems,” said Frank Dickson, Program Vice President, Security and Trust at IDC.
Deliver vulnerability management
“Qualys' solution draws from its native security and compliance platform to deliver vulnerability management, detection and response, the ability to detect malware, and the integrity of files. It is great solution, easy to use and deploy, and it’s hard to beat as it is free.”
“The scope of this nation-state attack is massive, as overnight a widely used and trusted piece of software turned into known malware,” said Sumedh Thakar, President and Chief Product Officer at Qualys.
Full situational awareness
Qualys teams have been actively researching the issue and helping customers assess their environments"
“Since its discovery, Qualys teams have been actively researching the issue and helping customers assess their environments. The good news is that nearly all of the CVE’s are patchable, and we’ve made this solution available to the industry so they can immediately work to protect themselves from being exploited by these vulnerabilities.”
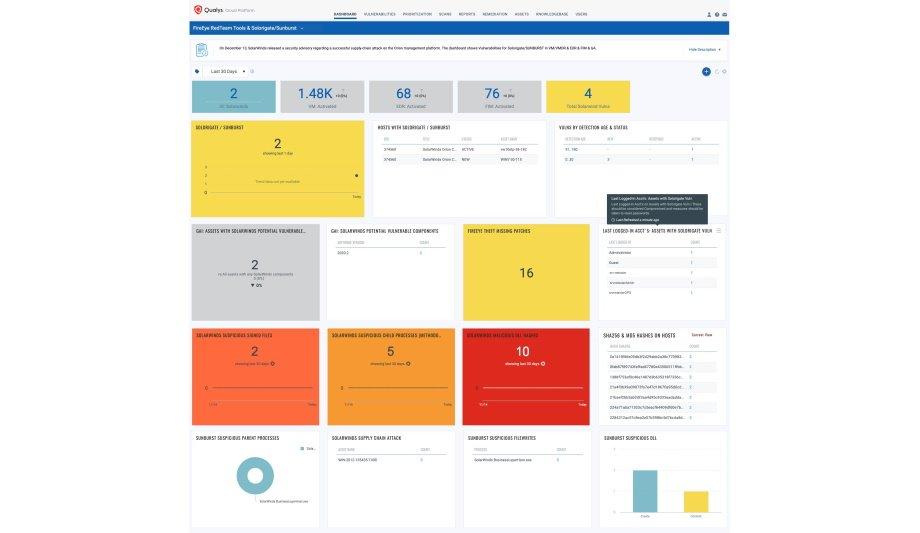
Qualys is offering a fully functional license free for 60 days. The license enables full situational awareness, detection, and remediation to reduce risk and exposure from the SolarWinds and FireEye breaches. It includes:
- Real-time, up-to-date inventory and automated organization of all assets, applications, and services running across the hybrid-IT environment
- Continuous view of all critical vulnerabilities and their prioritisation based on real-time threat indicators and attack surface
- Automatic correlation of applicable patches for identified vulnerabilities
- Patch deployment via Qualys Cloud Agents with zero impact to VPN bandwidth
- Security configuration hygiene assessment to apply as compensating controls to reduce vulnerability risk
- Unified dashboards that consolidate all insights for management visualization via a single pane of glass
Integrated security solution
“As our teams assessed the very sophisticated SolarWinds / FireEye nation-state attack, we realized that we could help the industry through our very powerful unified Cloud Platform. The integrated security solution provides real-time visibility across the entire global and hybrid IT environment allowing it to detect and prioritize critical vulnerabilities, identify malware and effectively respond all from one single pane of glass,” said Philippe Courtot, Chairman and CEO of Qualys.
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems