Biometric Security
DigiCert, a pioneer in intelligent trust, unveiled its 2026 Security Predictions, forecasting how AI, quantum computing, and automation will reshape global trust frameworks. The predictions highlight a pivotal shift toward AI integrity, resilience, and quantum readiness as core tenets of intelligent trust. DigiCert’s full predictions and outlook for the new year can be found at DigiCert’s blog. 1. AI Integrity Becomes the New Trust Standard: AI authenticity will overtake dat...
Iris officially launches today, introducing a platform that transforms how cameras are controlled, and productions are managed. By turning virtually any PTZ camera into a software-connected, remotely controlled device, Iris eliminates the traditional constraints of camera operation, such as hardware dependencies, inconsistent control, and the lack of on-site crews. The platform removes long-standing pain points for production teams: fragmented control tools and protocols across brands, the need...
International Security Expo is thrilled to announce that it has appointed a new chair. Figen Murray OBE, initiator and lead campaigner for Martyn's Law, will be taking on the role effective immediately. As chair, Figen will help steer the future direction and growth of International Security Expo, whilst also ensuring it best serves the needs of the industry. She will also lead the Advisory Council that is comprised of an outstanding selection of the industry’s foremost experts, represent...
Zimperium, the world's pioneer in mobile security, now announced that Alistaire Davidson has joined the company as Chief Financial Officer, reporting directly to CEO Shridhar Mittal. Alistaire brings more than 20 years of finance leadership experience across private equity–backed and public software companies. Alistaire most recently served as Regional CFO, Americas at The Access Group, where he led the post-acquisition integration of two strategic business units. Prior to The Access Grou...
The Security Industry Authority is encouraging the public to stay vigilant and report issues to security this winter as part of its ‘Safe Season Together’ campaign. At the heart of the campaign is the recognition that public safety is a collaborative effort. As the festive period begins, the Security Industry Authority is reminding everyone of the important role they play in keeping themselves and others safe. Highlighting the need for those out and about in December and January to...
Cellebrite, a pioneer in AI-powered Digital Investigative and Intelligence solutions for the public and private sectors, announces it has substantially expanded its capabilities through the acquisition of Corellium, a pioneer in Arm-based virtualization software. The addition of Corellium's technology and world-class technical talent further strengthens Cellebrite's market and technology leadership. Dramatically accelerating time This combination creates the industry's most complete digital...
News
Kindoo, a pioneer in modern smartphone wireless access control system solutions, announces the expansion of its Reseller Partner Program to serve the growing North American market. Kindoo’s unique access solution eliminates the longstanding barriers to entry for modern access control systems with a high-performance, highly cost-effective mobile access control solution that is easy to sell and to use providing a win-win for both resellers and end-users. Installing security dealers “We are looking to partner with forward-looking installing security dealers who are looking to increase sales and profits with long-term RMR,” said Michael Chaftari, Partner at Kindoo. “Kindoo has documented success with both enterprise and small business users across the United States, serving over 100,000 end-users, and we are now looking to further expand our sales network with a select group of new reseller partners.” Key advantages of the Kindoo platform Kindoo brings a revolutionary and cost-effective approach to modern access control with a unique mobile access platform that overcomes the longstanding barriers for security dealers to offer access control and users to install it. Key advantages of the Kindoo platform include: Smartphone credentialing eliminates costly physical credentials Compatibility with ANY electronic lock, gate, turnstile, or security entrance Range of battery-operated devices eliminate the need for local power Cloud-based access management – no need for network/IT expertise Remote management of all on-boarding and off-boarding credentials Unlimited scalability to accommodate system expansion 256-bit encryption ensures secure communications Personal privacy protection Kindoo offers new reseller partners Kindoo offers new reseller partners the support they need to be successful. Resources include demo kits, training videos and material, sales playbooks and marketing support resources, project registration/reseller protection, special partner pricing, and real sales leads. A limited number of resellers will be approved by regional area/coverage to further support growth.
SAGE Integration is excited to announce the newest office in Ripley, Tennessee, located at 567 Highway 51 South, Ripley, TN 38063. The latest expansion continues to enhance SAGE's ability to serve its expanding regional client base and address the rising demand for advanced electronic security solutions in the region. The new Ripley office will bolster local operations, enabling quicker response times, improved service, and deeper engagement with clients and the community while supporting our National Clients throughout the area. SAGE Integration's ongoing commitment "Our presence in Ripley, TN, marks a significant milestone for SAGE Integration," said John Nemerofsky, Chief Operating Officer. "This location allows us to deliver even greater value to our clients and strengthen our relationships within the region." The Ripley office demonstrates SAGE Integration's ongoing commitment to responsive service and reinforces its role as a trusted, innovative security integration partner nationwide.
Continuing its global expansion plan, and its commitment to the African continent, Integrity360 has acquired Redshift, a well-established and highly regarded cyber security services company operating out of Johannesburg in South Africa. The terms of the transaction were not disclosed. The acquisition comes on the back of Integrity360’s considerable investment in the region following the 2024 and early 2025 acquisitions of the Grove Group and Nclose. The acquisition brings Integrity360 resources in South Africa to a team of over 230 employees serving the needs of customers across Africa. Key locations Integrity360’s operations in Johannesburg and Cape Town also serve as key locations for its integrated “global SOC” (Security Operations Centre) operation which delivers a comprehensive suite of managed services, including EDR (Endpoint Detection and Response), XDR (Extended Detection and Response), and MDR (Managed Detection and Response) solutions for both local and international customers. Founded in 2015, Redshift has developed a reputation for service excellence amongst its customers, specifically for cyber security testing but also a selection of other specialized activities including cybercrime investigations, anti-fraud advisory, scammer group takedowns, cyber intelligence, and a focused range of managed services. Redshift adds approx. 50 customers including many leading South African finance, banking and telecommunications organizations, and an additional team of approx. 40 employees to the group. Regional center of excellence Redshift will serve as a regional center of excellence for the group for cyber security testing, and also be connected up with the existing Integrity360 cyber advisory and managed services teams operating in the region. Integrity360 will invest in the development and expansion of the business utilizing the considerable resources across the group. Redshift customers will benefit from access to Integrity360’s highly extensive and complementary cyber services portfolio encapsulating cyber risk and assurance, highly comprehensive 24/7 incident response and forensics services, infrastructure and technology services, PCI compliance, OT (operational technology) consulting and solutions, and a highly comprehensive range of cyber security managed services ranging from managing cyber infrastructure, to Managed SASE (Secure Access Service Edge), Managed CTEM (Continuous Threat Exposure Management), and a full suite of innovative XDR/MDR solutions. Innovative range of services Integrity360’s innovative range of services have been recognized five times in a Gartner market guide most recently for Incident Response and Forensic services. Ian Brown, Executive Chairman at Integrity360 commented “We are very excited to be welcoming Sean, Cailan and the entire Redshift team to Integrity360.” “The reputation and expertise they have developed since their formation in 2015 is highly impressive and we are looking forward to helping them provide an enhanced set of services to their customers and expanding further in the African market over the coming years”. Significant moment Sean Howell and Cailan Sacks Directors of Redshift commented: “This is a significant moment for us, and we could not be more delighted that Redshift is joining Integrity360 and continuing the growth and development of the business that was initially started by Sean a decade ago.” “Thanks to the support of our customers and employees, Redshift has grown enormously during that time, and having spent considerable time with Ian, and the wider Integrity360 leadership team, we are confident will continue to do so being part of the Integrity360 group.” “We are excited about the future for us as an organization, for our people and in particular for what the enhanced group can provide our customers moving forward.”
Securitas UK and Hays Travel are proud to celebrate over 10 years of working together to deliver safe, secure, and welcoming environments across Hays Travel’s nationwide network of retail branches. Since 2015, Securitas has been a trusted security partner to Hays Travel, providing a tailored service that supports the company’s commitment to customer service. From alarm response to mobile patrols, the partnership has evolved to meet the changing needs of the UK’s largest independent travel agent. Range of scenarios The partnership supports over 530 locations across the UK with alarm response. It ensures that out of hours, or when buildings are vacant and there are incidents such as an intruder, the alarm response results in an emergency key holder attending the site and resolving the incident. This could be a wide range of scenarios, including a break-in, a false alarm due to something being left unattended on the premises, or the site requiring maintenance and repair, as the result of an incident. With a deep and expansive UK estate, Hays Travel chose Securitas for its self-delivery model—free from third-party involvement. It ensures a consistent, high-quality service across all client sites. Supported by a nationwide network of branch managers it enables the delivery of tailored solutions with speed, accountability and local expertise. Trust, innovation, and shared values Rapid response across Hays Travel’s UK estates to callouts enables clients to maintain staff productivity, reduce operational disruptions, and achieve cost savings. By responding swiftly to alarm activation, not only is it a theft deterrent but also mitigates insurance liabilities, through reliable out-of-hours coverage. Securitas has played a key role in developing onsite behavioral analysis, helping teams better understand patterns, enhance safety, and improve response strategies. Alex Davis, Chief Commercial Officer, Securitas UK said, “We are delighted to mark this milestone with Hays Travel. Over the past decade, our teams have built a strong, collaborative relationship rooted in trust, innovation, and shared values. It’s been a privilege to support Hays Travel’s growth and success.” High standards of safety and service Peter Robinson, Head of Property at Hays Travel, said, “Our trusted partnership with Securitas has helped us to maintain high standards of safety and service across our retail estate. We are committed to caring for our people, customers and the communities where we operate and Securitas has been instrumental in us achieving this." “Their professionalism, responsiveness, and understanding of our business have made a real difference. We look forward to continuing this journey together.” The partnership will continue to focus on delivering value through smart security solutions that support Hays Travel in making travel accessible, enjoyable, and safe for all.
As AI-generated phishing attacks flood inboxes with more realistic and personalized scams, DigiCert, a pioneer in intelligent trust, today released new research revealing that consumers are turning to verified brand identities in email for reassurance--especially during Cyber Week. The study, conducted by independent research firm Vitreous World, surveyed 5,000 consumers across the U.S., U.K., Australia, and New Zealand to understand how verified logos and sender authentication will impact trust, engagement, and safety during the height of online shopping season. Integrity as AI With 86% of consumers saying they feel safer when verified logos appear in their inbox, the findings underscore a growing need for organizations to strengthen their email authentication practices. Doing so not only helps protect shoppers from phishing during the busiest online shopping week of the year, but also preserve brand integrity as AI rapidly increases the volume, frequency, and sophistication of phishing emails. Key findings Email trust drives clicks and conversions. 64% said they are more likely to click or act on an email that displays a verified brand logo, a critical insight for marketers competing for attention during Cyber Monday and holiday campaigns. Shoppers reward trusted brands. Given four options, nearly half (49%) said that if two competing brands sent similar offers, they would choose the one with a verified logo, suggesting that verified brand identity is not just about safety — it’s about sales. The inbox is the new battleground for brand trust. With 87% of consumers receiving suspicious emails at least a few times a year and 41% believing email providers should do more to protect them, trust in the inbox has become both a security and customer experience issue. Implementing Verified Mark Certificates “Our marketing team has seen a noticeable lift in open and engagement rates since implementing Verified Mark Certificates,” said Ryan Burton, Email & Retention Manager at OddBalls, a UK-based online retailer. “Having our verified logo appear directly in the inbox gives recipients immediate confidence that the message is authentic. It’s not just a security investment, it’s a brand trust investment. During high-volume periods like Cyber Monday, that trust translates directly into more opens, more clicks, and ultimately, more conversions.” Restoring trust in digital communication “Cyber Monday is a high-stakes moment for both brands and consumers,” said Al Iverson, Industry Strategist at DigiCert. “Our research shows that visual verification isn’t just about protecting users, it’s about restoring trust in digital communication. A verified logo can be the difference between a customer clicking ‘buy now’ or deleting your message.” The role of VMCs, CMCs, and DMARC Verified Mark Certificates (VMCs) and Common Mark Certificates (CMCs), supported by strong DMARC authentication, form the foundation for displaying verified brand logos in email. Together, they ensure that a brand’s logo appears only when the sender’s identity has been cryptographically confirmed and their domain properly authenticated. This combination not only deters phishing and spoofing attacks but also provides consumers with instant, visual assurance that the message is genuine, transforming trust into a tangible element of the inbox experience.
Global security manufacturer Gallagher Security is proud to announce a strategic partnership with Fortified Security, a pioneering perimeter systems integrator with over 30 years of specialized experience. This collaboration enables Gallagher’s Channel Partners across the Americas to offer enhanced perimeter security solutions to their customers, supported by Fortified’s expert design and installation services. Long-term client relationships This partnership empowers Gallagher Channel Partners to expand their service offerings, meet broader customer needs, and strengthen long-term client relationships. By engaging Fortified as a trusted subcontractor, Channel Partners who do not currently provide perimeter installation services can confidently deliver complete, integrated security solutions—reducing the risk of losing business to competing providers. Complete security infrastructure Natalie Bannon, Director of Strategic Alliances at Gallagher Security, says this partnership is a powerful way to help Gallagher’s Channel grow: “This partnership enables Channel Partners to expand their capabilities by offering Gallagher’s industry-pioneering perimeter security solution to both new and existing clients." "By partnering with Fortified, Channel Partners can better serve their customers through the design, installation, and integration of another critical component of a complete security infrastructure.” Install perimeter solutions Fortified President, Chase Cary, adds that the collaboration is built on a shared commitment to partnership and protection: “Gallagher, the Channel Partner, and the Fortified team each play a vital role in making this possible." "Our ultimate goal is to make end-users and their organizations safer — and stronger — because of it. We’re excited to come alongside Channel Partners, learn about their clients’ unique needs, and design and install perimeter solutions that directly address those challenges.” Fortified’s specialized integration capabilities Through this collaboration, Gallagher reinforces its commitment to supporting Channel Partners with the tools, resources, and expertise needed to drive mutual growth. By combining Gallagher’s world-class perimeter technology with Fortified’s specialized integration capabilities, Channel Partners are now better equipped than ever to deliver complete, end-to-end security solutions.


Expert commentary
It is the time of year when city centers transform, as outdoor Christmas markets fill town squares and high streets. An estimated 6,000 markets will open across Europe during the festive season, with some of the largest — including Nuremberg’s Christkindlesmarkt, London’s Hyde Park Winter Wonderland and Craiova in Romania — welcoming millions of visitors. Sadly, these popular events have in recent years been the subject of attacks, most notably Berlin in 2016 and the tragedy in Magdeburg last December, where a vehicle was driven into the crowd. Incidents such as these have encouraged governments, including the UK with the introduction of Martyn’s Law, to strengthen planning and preparation for large-scale public events. Digital twins: A new standard for event preparation Drone-based photogrammetry captures streets, squares and surrounding buildings with exceptional detail One of the most effective tools for preparing and safeguarding public spaces today is the creation of a photorealistic digital twin — a highly accurate 3D virtual model of the intended market area. Drone-based photogrammetry captures streets, squares and surrounding buildings with exceptional detail, enabling planners to work within a realistic and immersive environment long before any physical structures are installed. Digital twin design tools can ingest these datasets and visualize them using advanced technologies, creating a lifelike representation of even the most complex outdoor scenes. Designing the market in 3D before construction begins Once the digital twin is created, event organizers, city authorities and security specialists can begin shaping the market virtually. Temporary stalls, lighting installations, stages, decorative structures, back-office units, Christmas trees, ice rinks and other festive features can be positioned directly within the digital model. It‘s also possible to place static representations of people or larger groups to approximate crowd density and understand how occupied space will influence visibility, accessibility and the overall perception of the environment. This ability to design and refine the market layout before construction allows planners to test multiple variations, understand how structures interact and ensure that the environment remains safe and manageable throughout the event. Virtual camera planning, coverage assessment and analysis Digital twins also provide a robust foundation for planning the deployment of visual-monitoring systems Digital twins also provide a robust foundation for planning the deployment of visual-monitoring systems. Cameras can be placed directly into the 3D environment, allowing planners to immediately see how temporary structures, decorations or pedestrian flows will influence the field of view. Blind spots become apparent, alternative camera heights or angles can be explored and strategic decisions about additional mounting points or temporary towers can be made with confidence. For each planned camera, the expected resolution per meter or per foot is visualized directly inside the digital twin. Instead of relying on theoretical charts or static design tables, planners can instantly see whether a particular camera position will deliver the clarity required for the intended purpose, whether it is early detection of movement, recognition of behavior patterns or full identification of individuals. Real-time visual feedback This real-time visual feedback makes the entire planning process more precise, transparent and efficient. These evaluations can be carried out within the realistic daytime environment captured by the digital twin. Planners can also prepare alternative scene variants — for example, dedicated night-time versions or layouts reflecting festive lighting — to understand how visibility and coverage may change throughout the event. Even without full weather simulation, this approach allows teams to anticipate typical operational challenges and refine the monitoring concept well before the first stall is erected. Testing safety and security scenarios Perhaps the greatest advantage of working with a digital twin is the ability to explore the environment from multiple perspectives before the event begins. Although the scene itself is static, planners can move through it using a virtual intruder to understand how the market will appear from ground level and to identify potential vulnerabilities that may not be obvious from a top-down view. This makes it possible to assess where hostile-vehicle barriers should be positioned, how narrow passages might feel when occupied, or where visibility may be reduced due to temporary structures or decorations. The static digital twin also provides a clear way to evaluate emergency access lanes, determine suitable locations for help points or medical posts and plan the general layout of security patrol routes. By navigating the scene freely and observing it from different perspectives, teams can refine the design and address potential blind spots long before construction begins. A unified environment with LiDAR The created digital twin also becomes the primary visualization environment for LiDAR during live operations Beyond planning, the created digital twin also becomes the primary visualization environment for LiDAR during live operations. Operators can interact with this 3D map directly and with a single click on any location, all PTZ cameras capable of viewing that point automatically reposition to it. This provides an unmatched navigation interface for real-time camera control, making situational awareness significantly faster and more intuitive. LiDAR then works seamlessly with a video management system, which controls all camera streams, recordings and video evidence, creating a tightly integrated monitoring workflow. Supporting real-world operations Once the market opens, the digital twin continues to serve as a valuable operational resource. If layouts change during the event — for example, because of additional attractions, adjusted walkways or altered security checkpoints — these modifications can be quickly modelled and evaluated before implementation. When the festive season concludes, the same model can be repurposed for future events, long-term city planning or other public-space deployments. A safer and smarter festive season Christmas markets are vibrant, high-profile and densely populated environments, making them attractive targets for those seeking to cause disruption. By combining detailed photogrammetry, advanced 3D visualization, and rigorous spatial evaluation, cities can create safer, better-prepared, and more resilient festive settings. With tools such as digital twins and LiDAR, authorities can plan more effectively, anticipate risks earlier and ensure that every stall, pathway and vantage point contributes to a joyful — and secure — holiday season.
The Internet of Things is growing quickly. It has moved far beyond a few smart gadgets at home. Today, connected technology is in homes, factories, hospitals, farms, and cities. Experts expect the global market for IoT devices to rise from about $70 billion in 2024 to more than $181 billion by 2030. This means more devices, more data, and more opportunities for industries everywhere. This growth comes from several advances working together. 5G connections make it possible to send and receive data faster. Edge computing processes information close to where it is created, which helps with quick decisions. Analytics allow organizations to understand and act on the data they collect. Together, these improvements are opening the door to new ways of working, producing, and communicating. IoT: The next generation As devices become more advanced, they use more energy and send more data. Think about high-quality security cameras, detailed environmental sensors, or systems in vehicles that send constant updates. All of these devices require a strong supply of power and a steady connection. In 2024, sensors made up more than 32 percent of all IoT device sales. Sensors are essential, yet the next wave of devices will do even more. They will process information themselves, use artificial intelligence, and include many features in one unit. This progress depends on networks that deliver both the energy and the bandwidth to support them. Into the future Devices and applications keep improving, so networks need the flexibility to handle what comes next Setting up IoT systems is about more than meeting today’s needs. Devices and applications keep improving, so networks need the flexibility to handle what comes next. A future-ready design provides extra capacity in both power and data flow. This way, when it’s time to add new devices or upgrade existing ones, the system is prepared without requiring major changes. One smart approach is to use modular equipment. For example, a network switch might deliver more power than devices currently use, while allowing room to connect more advanced devices later. This helps keep the system ready for growth. Built for all IoT devices often operate in challenging places. Factories, power plants, rail lines, and shipping ports face extreme temperatures, dust, vibration, and other difficult conditions. Network equipment in these locations needs the strength to keep working through heat, cold, and constant use. Industrial-grade gear is designed for these environments. It can run in a wide range of temperatures, handle physical impacts, and resist interference. Features such as port security, which keep a connection safe if a cable is removed, help protect both the equipment and the data it carries. Systems with backup power inputs continue to run even when one power source goes offline. Plug into PoE Power over Ethernet (PoE) sends both energy and data through the same cable Power over Ethernet (PoE) sends both energy and data through the same cable. This makes installation simpler and allows flexibility in where devices are placed. And as devices become more capable, they often need more power to operate. The latest innovation for PoE can deliver up to 90 watts on each port. This is enough to support advanced devices like AI-enabled cameras or multi-sensor units. When every port on a switch can supply that much power at the same time, adding more devices is straightforward and performance stays strong. Protecting the network Every connected device is part of a larger network. Protecting this network means securing data from the moment it leaves the device until it reaches its planned destination. Built-in security features in network equipment — such as secure architecture, encryption support, and physical safeguards — help keep information safe. They also help meet industry and government requirements for equipment sourcing and design. A clear path Organizations leading in IoT think ahead. They prepare for the next stage of technology by building networks with flexibility, durability, and protection in mind. These networks supply extra power, allow more bandwidth, and keep data secure while adapting as the system grows. The focus is on creating a foundation that supports innovation year after year. This means planning for devices that are faster, more capable, and more connected, while making sure the infrastructure grows right along with them. Looking ahead Strong, adaptable, and secure networks will allow connected devices to reach their full potential The IoT of the future will touch nearly every part of daily life. It will help farmers grow food more efficiently, guide self-driving vehicles, improve medical care, and keep cities running smoothly. As devices multiply and gain new abilities, the networks powering them need to grow in step. Strong, adaptable, and secure networks will allow connected devices to reach their full potential. By planning for both today’s needs and tomorrow’s possibilities, organizations can make the most of the opportunities IoT brings—and keep those opportunities expanding for years to come. Key takeaways: Preparing for the future of IoT The IoT market is growing fast The global market for connected devices is expected to grow from $70 billion in 2024 to more than $181 billion by 2030. This means more devices in more industries, from farming to healthcare to transportation. Devices are using more power and data Newer devices have more features — such as high-quality video, built-in AI, and multiple sensors — and these require stronger power supplies and faster connections. Future-ready networks are essential Infrastructure should allow extra capacity for both power and data. This ensures new devices can be added without major changes or delays. Environments vary, so equipment should match the setting Industrial areas, outdoor spaces, and transportation hubs need rugged, reliable equipment that works in extreme conditions and stays secure. Security starts at the network level Built-in protections — like secure architecture, encryption, and physical safeguards — help keep information safe and meet important industry requirements.
Where and how to store security camera footage usually depends on the scale of the video surveillance project, the way you are using to record the video and how long you want to keep the recordings. If there are only few IP cameras, say 2~3 IP cameras for example, and you don’t need to keep the recordings for the month, usually using SD card which is installed in the camera is enough. Video management software A VMS provides a unified platform to manage all cameras and record footage onto centralized local storage servers If there are more than four cameras, even up to 128 cameras, NVR or CVR become the practical choice for managing and storing recordings reliably. However, if there are hundreds or thousands cameras, which need to managed and recorded, in this way video management software with centralized recording storage becomes essential. A VMS provides a unified platform to manage all cameras and record footage onto centralized local storage servers. S3-compatible cloud platforms Critically, if the VMS supports the S3 object storage protocol, users gain the flexibility to store recordings on S3-compatible cloud platforms (public or private), offering significant hardware cost savings and enhanced scalability. For such demanding environments, selecting a VMS built on an open platform architecture is strongly advised, ensuring the system can expand infinitely to meet future project growth. Video surveillance management system Users can seamlessly add subordinate servers (or disk groups like IPSAN/NAS), disk arrays, and network bandwidth Take the video surveillance management system SVMS Pro as an example. Its foundation is an open 1+N stackable architecture, enabling unlimited expansion of recording storage servers. Users can seamlessly add subordinate servers (or disk groups like IPSAN/NAS), disk arrays, and network bandwidth. This achieves extended recording durations and boosted storage performance while maintaining system stability during sustained operation (assuming environmental requirements are met). Key architectural advantages Each centralized storage module based on a Linux OS, supports up to 200 front-end video channels per server. Its N+1 stackable expansion capability utilizes a distributed architecture, forming clusters of storage servers. Scaling the project involves simply adding subordinate storage modules – no modifications to existing deployments are required. Seamless S3 object storage integration Furthermore, SVMS Pro features deep integration of the S3 object storage protocol Furthermore, SVMS Pro features deep integration of the S3 object storage protocol. This allows seamless connection to major public cloud services like Alibaba Cloud OSS, Tencent Cloud COS, and Amazon S3 cloud, as well as private S3-compatible object storage solutions. This integration delivers truly limitless capacity expansion, leveraging the inherent elasticity of the cloud to effortlessly accommodate petabyte-scale video growth. Dual insurance: Multi-layered data protection The critical value of security data comes with inherent risks; losing video footage can lead to immeasurable losses. To mitigate these risks comprehensively, SVMS Pro innovates with its "Local + Cloud" Dual-Backup mechanism, leveraging S3 features to build multiple security layers: Real-Time Dual-Writing: Recordings are first written to the local disk (acting as a cache buffer). Upon local persistence, data is simultaneously replicated to cloud-based S3 storage, guaranteeing instant failover if either node fails. Smart Hot/Cold Tiering: Frequently accessed ("hot") data remains on high-performance local storage, while historical footage is automatically archived to low-cost cloud tiers, optimizing storage expenses. Cross-Regional Disaster Recovery: Utilizing the multi-replica and cross-region replication features of carrier-grade S3 storage inherently protects against physical disasters like earthquakes or fires. Additionally, the platform ensures comprehensive data protection through integrity verification and encrypted transmission, safeguarding data integrity and confidentiality across its entire lifecycle – from storage and transmission to access. Conclusion In essence, selecting the optimal storage solution for security footage hinges on a fundamental understanding of scalability requirements, retention needs, and data protection imperatives. As surveillance deployments grow from a few cameras to enterprise-scale systems, the underlying architecture must evolve: Localized storage (SD cards/NVRs) suffices for limited scope and short retention. Centralized VMS platforms become essential for unified management at scale, with open, modular architectures providing critical future-proofing for expansion. S3 object storage integration represents a paradigm shift, decoupling storage capacity from physical hardware and enabling truly elastic, cost-efficient scaling – both on-premises and in the cloud. Ultimately, successful large-scale video surveillance storage relies on architecting for flexibility, embedding data protection intrinsically, and strategically leveraging object storage protocols to balance performance, cost, and resilience – principles essential for safeguarding critical security data now and in the future.
Security beat
Big news on the mergers and acquisitions (M&A) front is closing out 2024, a year in which several shifts changed the face of the physical security manufacturer community. Announced in December, German giant Bosch Group is selling its Building Technologies division’s product business for security and communications technology to the European investment firm Triton. Bosch division selling to Triton The transaction encompasses three business units – Video, Access and Intrusion, and Communication – and thus the entire product business of Bosch Building Technologies that was offered for sale. All 4,300 associates employed in these units at more than 90 locations worldwide will be taken over. The transaction reflects a growing confidence in the security market among private equity companies such as Triton, Becklar, and Volaris. Sharing best practices Acre Security and Bosch will remain independent, standalone companies under Triton’s ownership Acre Security, previously acquired by Triton, has benefited from Triton’s strategic guidance and expertise, according to the company, which is confident Bosch will experience the same level of support and opportunity to thrive. Acre Security and Bosch will remain independent, standalone companies under Triton’s ownership, but will benefit from the potential to collaborate and share best practices as part of the broader Triton portfolio. Resideo acquires Snap One Earlier in 2024, there were other large M&A transactions. In the spring, Resideo Technologies, Inc., a manufacturer and distributor of technology-driven products and solutions, agreed to acquire Snap One Holdings Corp., a provider of smart-living products, services, and software to professional integrators. The transaction is valued at $1.4 billion, inclusive of net debt. Upon closing, Snap One becomes part of Resideo's ADI Global Distribution business. Honeywell buys Carrier’s Access Solutions In late 2023, Honeywell announced plans to enhance and strengthen its building automation capabilities with the acquisition of Carrier Global Corporation’s Global Access Solutions business for $4.95 billion, in an all-cash transaction. The acquisition, which played out through 2024, includes both hardware and software solutions, adding three respected brands to Honeywell’s portfolio with a focus on life safety and digital access solutions. Acquired brands include LenelS2, commercial and enterprise access solutions; Onity electronic locks; and Supra cloud-based electronic real estate lock boxes. Hirsch reemerges as an iconic brand The Identiv sale was originally announced in April, subject to regulatory approval Identiv announced plans to sell its physical security business and assets to Vitaprotech, the security solutions provider that also acquired British manufacturer, TDSI, in 2019. The Identiv sale was originally announced in April, subject to regulatory approval. As a result of the sale, Hirsch, a global security technology pioneer advancing physical security, video intelligence, cybersecurity, and digital identification solutions, announces the relaunch of its iconic brand and strengthened focus on the industry’s most complete high-security, end-to-end platform. Ease of use security solutions The move seeks to reposition Hirsch as the global pioneer in physical security, video intelligence, and identity solutions, protecting everything from small enterprises to critical national infrastructure. With a 43-year-strong foundation in the industry, Hirsch’s mission has always been empowering a secure, connected world, combining government-grade high security with ease of use. Milestone and Arcules unite Effective July 1, 2024, global video technology company Milestone Systems announced its merger with the cloud-based video surveillance solutions provider, Arcules. Both companies are owned by Japanese multinational Canon Inc. Based in Irvine, Calif., Arcules was spun off from Milestone in 2017. The merger brings together Milestone and Arcules’ best-in-class capabilities within video management software (VMS), video analytics, and video surveillance as a service (VSaaS), providing a complete video technology offering. More M&A stories in 2024 In other M&A moves in 2024, cloud-based workforce management software provider Synerion USA Inc. acquired cloud-based video surveillance and access control solutions platform Qumulex Inc. Also, the global pioneer in airspace awareness and security, Dedrone, became part of the public safety and technology company Axon. The acquisition unites two companies with a shared mission to improve public safety and national security by staying ahead of persistent and escalating threats, enabling faster, more effective responses and ultimately protecting more lives in more places.
The pattern of veins in the hand contains unique information that can be used for identity. Blood flowing through veins in the human body can absorb light waves of specific wavelengths. Irradiating the human palm with near-infrared light waves yields an image of the vascular pattern. A venous distribution map can be processed and compared to pre-registered data to match and confirm identity. Palm vein biometrics The idea of palm vein biometrics goes back to the 1980s when palm vein scanners emerged as commercial products in the 1990s. The devices gained some traction in military-grade and high-security applications, although the technology was too expensive to become popular among mainstream applications such as physical access control. Anviz Global is expanding palm vein technology into mainstream applications, featuring a lower price point that will open new market opportunities. Palm vein technology “Palm vein technology has been viewed as a boutique product because it is costly and has not developed as a mainstream product,” says Mark Vena, Senior Director of Business Strategy and Development for Anviz Global. “With a more compelling price point, the market can see the technology more broadly. We can change the game in terms of how people think about palm vein technology.” FAR and FRR Palm vein technology is more accurate than either fingerprint (0.0001% FAR) or facial recognition (0.001% FAR) Iris recognition is considered the gold standard in biometric identification, but palm vein technology can almost achieve the accuracy of iris. The false accept rate (FAR) for palm vein technology is 0.00008%, compared to 0.00005% for iris recognition systems. The false reject rate (FRR) is comparable at 0.01% for either technology. Palm vein technology is more accurate than either fingerprint (0.0001% FAR) or facial recognition (0.001% FAR). Palm vein identification occurs in less than half a second. M7 Palm “Anviz is seeking to bring a high level of capability to more mainstream commercial applications,” says Vena, specifically providing a lower-cost palm vein unit. The M7 Palm by Anviz can achieve next-generation biometric access control for greater security and intelligence. The door-mounted unit combines palm vein recognition with an RFID card reader and PIN code (using a 17-button keypad), all configurable for multi-factor authentication. Outdoor applications The robust unit, including a narrow metal exterior design, provides strong vandal resistance (IK10) and stability for outdoor applications. To ensure a weatherproof design, the IP66 rating indicates the product is completely protected against dust and can withstand strong jets of water from any direction. Power-over-ethernet (PoE) enables centralized power management and the ability to remotely reboot devices. Wiegand-out interface The unit communicates using RS-485 or TCP/IP and can connect locks, exit buttons, door contacts, doorbells, etc The unit communicates using RS-485 or TCP/IP and can connect locks, exit buttons, door contacts, doorbells, etc. The Wiegand-out interface can connect to standard third-party controllers, or a built-in relay can trigger a lock directly. Capacity is 500 users. Because palm vein recognition originates from the physiological characteristics of the human body, it represents a “credential” that cannot be forged, lost, or left at home. It is not easily counterfeited or worn out. Multi-factor authentication Applications include industries requiring high security such as government, judicial, and banking. Multi-factor authentication eliminates fraud and ensures safety at banks, data centers, airports, prisons, and government. An end user might opt for higher levels of access control for a laboratory or server room. For dealers and integrators, palm vein technology, including multi-factor authentication, provides an additional option for customers seeking to protect high-security areas on a large campus. Card readers Card readers may suffice for most of the doors, but an important laboratory or cash-handling area requires more protection. Palm vein technology can secure a casino cash cage or a room containing corporate secrets. Time of Flight ToF laser-ranging uses a laser to measure the distance to an object by calculating the time Time of Flight (ToF) laser-ranging achieves accurate measurement to ensure the right distance for operation. ToF laser-ranging uses a laser to measure the distance to an object by calculating the time it takes for the laser light to travel to the object and back. Palm vein technology operates in the range of 10 to 30cm (4 to 12 inches). The proprietary BioNANO palm vein recognition algorithm enables accurate and fast scanning speed. Non-contact biometric The non-contact biometric performs in touchless environments and does not contribute to lingering health concerns in the post-COVID world. The technology is accurate across all hand types and skin tones. Users may feel more comfortable scanning their hands than their eyes. Optimal human-machine interaction M7 Palm’s optimal human-machine interaction and user experience include a low-power-consumption OLED screen to deliver clear text notifications to the user. Advantages of M7 Palm include accuracy, stability, security, and privacy. Features include easy installation with standard processes and no special tools, centralized power management, simplified cabling, and less maintenance. Managing the system is expedited by integration with the Anviz CrossChex Standard access control and time management dashboard, used by more than 30,000 enterprises, and the system can be integrated with any access control system. Security for SMBs Anviz Global is a converged intelligent security provider for SMBs and enterprise organizations Anviz Global is a converged intelligent security provider for small- and medium-sized businesses (SMBs) and enterprise organizations. The company’s product line includes biometrics, video surveillance, and security management solutions based on the cloud, Internet of Things (IoT) and artificial intelligence (AI) technologies. Privacy concerns Anviz is part of the Xthings family of companies, which includes Ultraloq (smart locks), Utec (smart home), Bright (smart lighting), Secu365 (SaaS Platform), and Ulticam (smart cameras). Privacy concerns are minimized because palm vein recognition does not directly store the original image but rather extracts feature information through algorithmic models. Personal data is protected through obfuscation and encryption.
An attention-grabbing exhibit at GSX 2024 in Orlando involved a robot dog that could open a door. Boston Dynamics robot dog ASSA ABLOY impressed attendees with the robotics demonstration, featuring the Boston Dynamics robot dog that could open a door using either an HID credential or a mechanical grip. This innovation represents a shift toward more autonomous security solutions and is suitable for environments where human access may be limited. ASSA ABLOY impressed attendees with the Boston Dynamics robot dog Operational efficiency Eye-catching exhibits at the GSX in Orlando, showcasing the future of security technology It was one of many eye-catching exhibits at the GSX in Orlando, showcasing the future of security technology, and offering practical solutions to the industry's challenges. For security professionals, the advancements presented opportunities to enhance operational efficiency and to maintain a proactive stance in a rapidly evolving market. Control ID face identification Alongside their robot demonstration, ASSA ABLOY also highlighted the Control ID Face Identification. Access Controller, providing advanced facial recognition access control. From identity management to AI-driven surveillance systems, GSX 2024 offered a glimpse into the tools that can streamline processes, increase security, and reduce costs. Here are some other highlights. ASSA ABLOY also highlighted the Control ID Face Identification More integration with critical infrastructure A major theme at GSX 2024 was the increasing integration of security solutions with critical infrastructure. ALCEA (formerly ASSA ABLOY Critical Infrastructure) is an example. Their globalized software solution ALWIN is designed for managing access control, visitor management, and other security factors across multiple locations. ALCEA's approach involves not only internal collaborations within ASSA ABLOY but also partnerships with external organizations. An example of innovation is the Neenah Foundry lockable manhole cover, blending safety and security. Solving identity management challenges The solution simplifies onboarding and access request changes while ensuring compliance with policies Identity management continues to be a key focus in the security sector, and AMAG Technology addresses this need with its Symmetry Connect product. The solution simplifies onboarding and access request changes while ensuring compliance with policies. For professionals overseeing identity access management, Symmetry Connect provides a streamlined, automated approach, reducing human error and increasing operational efficiency. AMAG also sees a growing demand for efficient visitor management systems, especially in the post-COVID landscape. AMAG’s products cater to the need for enhanced security without overburdening staff. AI and cloud-based surveillance solutions Axis Communications highlighted its advancements in AI and cloud-based video management systems with its AXIS Camera Station Edge and Pro products. These solutions can connect seamlessly to cloud systems, providing security professionals with easy access to surveillance data anywhere. With the increasing need for centralized management, Axis’s offerings ensure that security teams can efficiently manage surveillance with minimal infrastructure. Axis also showcased its commitment to AI-driven analytics based on superior video quality. There were also networked audio solutions for public announcements and background music, among other uses. Body-worn cameras for corporate and Healthcare uses Traditionally focused on law enforcement, Axon is now expanding its body-worn cameras and TASER technology into corporate, retail and healthcare environments. Their Axon Body Workforce camera is a practical solution for protecting frontline workers in high-risk environments. Axon also introduced drone-based solutions for real-time aerial awareness Axon also introduced drone-based solutions for real-time aerial awareness, a significant benefit for large campuses or remote locations. As more industries adopt corporate surveillance systems, Axon’s offerings provide flexible, scalable solutions that address the need for real-time, actionable intelligence. Cloud-based access for smart buildings Brivo’s native cloud systems and flexible credentials offer practical, future-proof security options Brivo showcased how cloud technology is revolutionizing access control by offering systems that integrate seamlessly with other smart building platforms. Their open API approach enables collaboration with IT teams, bridging the gap between physical security and IT management. Brivo’s new partnership with Comcast Smart Solutions illustrates how large enterprises can implement advanced solutions, including access control while maintaining flexibility. For professionals managing complex building environments, Brivo’s native cloud systems and flexible credentials offer practical, future-proof security options. AI-powered multi-sensor camera Hanwha focused on an AI-powered multi-sensor camera, equipped with an NVIDIA processor capable of running complex analytics. In addition, Hanwha’s new AI camera technology can process multiple video streams simultaneously, either stream from its sensors or outside cameras, enabling better tracking of objects in complex environments. Their eight-channel AI Box, which converts legacy cameras into AI-enabled devices, is an attractive solution for professionals seeking to upgrade existing systems without the need for complete overhauls. For security teams looking to enhance situational awareness, Hanwha’s AI-based offerings provide advanced, scalable solutions. Workflow management and hybrid cloud security Genetec continued the theme of integrated solutions with their Operations Centre module for Security Centre, which consolidates work management into a single platform. Built on lean management principles, this system simplifies workflow for security professionals, promoting real-time collaboration across mobile and web platforms. As the industry shifts from on-premises systems to hybrid cloud solutions, Genetec’s products provide seamless transitions for organizations. Their new SaaS Security Centre also allows for natural language video searches in multiple languages, making it easier for global teams to manage operations across locations. Simplifying remote surveillance The company’s focus on scalability and efficiency is demonstrated by the “Eagle Eye Complete” subscription service Eagle Eye Networks showcased their continued international expansion, highlighting a new data center opening in Saudi Arabia and new hiring initiatives in Australia and Europe. Their “Eagle Eye Anywhere” solar-powered camera system exemplifies the move towards flexible, easy-to-install solutions that can be deployed in remote locations. Integrators benefit from simplified maintenance through remote management, reducing the need for on-site support and ensuring operational continuity. The company’s focus on scalability and efficiency, as demonstrated by the “Eagle Eye Complete” subscription service, reflects the broader industry’s shift toward managed security services. Tailored solutions for commercial clients Everon continues its transition away from its former identity as ADT Commercial. Claiming the status of a competitive commercial integrator, Everon is reinventing itself by offering customized billing and monitoring solutions for a range of industries. Their cloud-based business intelligence platform, which combines video surveillance with data analysis, is aimed at enhancing operational awareness by detecting anomalies such as OSHA violations or retail point-of-sale exceptions. With AI-driven dashboards, clients can customize their security solutions to meet specific needs, reflecting a growing demand for tailored, data-driven security applications. Innovation through cloud and mobile LenelS2 is part of Honeywell, and they emphasized their investment in cloud and mobile solutions at GSX 2024. Their "Enterprise OnGuard Cloud" platform, launched in June 2024, is a testament to the growing demand for cloud-enabled access control systems. With the addition of NFC-enabled Blue Diamond credentials, LenelS2 is pushing towards smarter, more secure mobile access options. The strategic combination of Lenel’s solutions with Honeywell’s infrastructure offers users enhanced engineering capabilities and global reach. This reflects a broader market trend of integrating mobile devices into physical security protocols. Bringing AI to everyday security LPR system, combined with their Searchlight Cloud Analytics, offers a powerful tool for identifying security risks March Networks highlighted their new AI-driven smart search feature, designed to help security teams quickly detect operational anomalies in retail and financial environments. From identifying misplaced cash in quick-service restaurants (QSRs) to detecting "jackpotting" attacks on ATMs, their solution highlights the increasing importance of AI in enhancing both security and operational efficiency. Their Licence Plate Recognition (LPR) system, combined with their Searchlight Cloud Analytics, offers a powerful tool for identifying and responding to security risks in real-time, emphasising the practicality of AI in daily security operations. Driving sustainability in security Securitas showcased its commitment to sustainability, a growing concern for businesses across all industries. By providing CO2 data for clients and promoting digital tools like mobile credentials, Securitas is leading the charge in creating greener, more sustainable security solutions. Their focus on remote services and occupancy insights offers companies a way to reduce their environmental impact while enhancing security operations. The company’s alignment with science-based targets and circular economy practices signifies the increasing role sustainability will play in the security sector. Future lies in integration The GSX 2024 trade show revealed that the future of security lies in intelligent integration, AI-driven analytics, and cloud-based management systems. The innovations presented will help security professionals streamline their operations, enhance situational awareness, and future-proof their systems. As these technologies continue to evolve, professionals must stay informed about the latest advancements to maintain a competitive edge in the security marketplace. GSX was a great place to start. At the end of the day at GSX, it wasn’t just the robot dog that was opening doors …. to the future of security systems. {##Poll1727925373 - Of the important factors highlighted at GSX 2024, which do you consider most when adopting new security solutions?##}
Case studies
Colt Technology Services (Colt), the global digital infrastructure company, released the key enterprise technology and market trends it expects to dominate the CIO agenda in 2026. Based on customer insights, market intelligence and its own proprietary research, Colt anticipates AI Inference, the evolution of NaaS to ‘NaaS 2.0’ and quantum-safe security to shape the technology landscape over the next 12 months. Ever-changing regulatory environment “CIOs will continue to face headwinds in 2026 as they balance complex business transformation programs at scale – often centered around AI – with ongoing cost-reduction programs in an ever-changing regulatory environment,” said Buddy Bayer, chief operating officer, Colt Technology Services. “But there’s huge opportunity too: AI programs are beginning to mature, digital infrastructure has greater capacity than ever before, and we’re seeing an evolution of solutions like NaaS which are reshaping our digital experiences. It’s an exciting time and, at Colt, we’re leading the way for our customers.” New ways to generate ROI from AI Businesses continue to drive major investments in AI, but ROI, value creation and monetization are proving elusive. Colt’s research finds one in five global firms spend US$750,000 annually on AI while 95% of the respondents in a recent MIT report study see no return on their investments. This misalignment between spending and measurable returns will shrink in 2026, as AI projects mature and begin to generate ROI, and as businesses find new ways to create value from AI. More vendors will build in AI maturity assessments and structured ROI models to help businesses define, track and quantify value across their AI tools. AI inference and Agentic AI 2026 will see AI inferencing reaching the next level of maturity, shifting from experimentation to integration into the enterprise IT environment, extracting insight, making predictions, and enabling smarter, context-aware decisions in real-time. McKinsey expects AI inference to account for a majority of AI workloads by 2030. This won’t just be limited to enterprises: Agentic AI, driven by inference, will be the force behind the automation and digitalization of day-to-day consumer tasks from privacy management and healthcare to scheduling assistance and management of household chores, according to research from the IEEE. AI Wide Area Networking (WAN) Many of Colt’s conversations with customers center around digital infrastructure’s ability to manage and optimize the performance, latency and security needed for AI workloads. AI WAN moves the conversation towards software-driven wide area networks, built for AI workloads, which dynamically manage AI traffic for peak performance and ensure application-level security of critical data. Innovation in sustainable networking technologies Similarly, AI workloads transmitted over transatlantic cables will grow in 2026 and are projected to surge from just 8% of total capacity in 2025 to 30% by 20351, placing additional strain on global network routes. Innovative tech trials and global partnerships are pioneering technologies which boost performance without increasing energy consumption or carbon emissions. Sovereign AI As nations grow their AI investments and regulations around AI governance come into force across many of the world’s major economies, sovereign AI is gaining momentum. It will rise up the CIO’s agenda as countries and organizations build and run their own AI systems using their own data, infrastructure, people, and rules. Sovereign AI is becoming more prevalent and increasingly important as nations look to stay in control of their technology, protect their data, and stay resilient in a world increasingly shaped by AI. NaaS 2.0 The NaaS market continues to grow, driven by a number of factors from AI, edge computing and cloud adoption to enterprises’ need to build in flexibility as they navigate dynamic global markets. Colt research found 58% of the 1500 CIOs it questioned said they were increasing their use of NaaS features due to growing AI demands. In 2026 and beyond, people will see NaaS evolve to meet the demands of the AI era, moving beyond its traditional role in supporting digital experiences. The next generation of NaaS will be intelligent, automated, and outcome-focused, designed to deliver real-time performance, adaptability, and autonomy for AI-driven enterprises. Quantum security Rise in quantum security investment as Q Day gets nearer CIOs are under constant pressure to protect their data and infrastructure from emerging risk, and as governments and businesses develop a deeper understanding of quantum’s power and potential, attention and investment turn to quantum security. In its 2026 Technology and Security Predictions report2, Forrester forecasts that quantum security spending will exceed 5% of enterprises’ overall IT budget next year, while a report from The Quantum Insider estimates the quantum security market to grow at over 50% CAGR to 2030, reaching $10 billion. Traditional data cryptography methods are at risk of being deciphered by quantum computers. The point at when this happens is known as Q Day, and latest estimates suggest it could come as soon as 2030. Technologies such as post-quantum cryptography (PQC) and quantum key distribution (QKD) protect traffic from this risk as it travels across a network. 2026 will bring developments, trials and innovation in protecting data from quantum risk. Low Earth Orbit technologies – and quantum 2026 is set to be a breakthrough year for Low Earth Orbit satellites, with organizations launching new satellites and new services. These services are a vital part of global telecoms infrastructure, providing connectivity in underserved or rural areas, and providing resiliency to businesses looking for back-up options for their enterprise infrastructure. Colt is looking to trial low earth orbit satellite connectivity for quantum key distribution: this will enable secure and protected exchange of symmetric encryption keys using quantum technology, while overcoming the distance limitations of terrestrial connectivity. 2026 will see Colt and partners trialing space-based and subsea techniques which extend quantum security to global networks. Hybrid cloud computing models 2026 will see multi cloud models becoming the default, as enterprises look for more ways to build in flexibility and resilience to their infrastructure and move beyond single-provider strategies. Increasingly, APIs and secure interconnects between providers and hyperscalers are streamlined, complementary and competitive in pricing terms and accessible through aggregators. Edge computing will continue to grow through 2026 and beyond, driven by factors such as AI inference expansion, the rise in real-time analytics, and increasing data sovereignty requirements. Next-generation cloud providers Next-generation cloud providers are prioritizing deployment of infrastructure at the edge, processing data closer to where it’s generated, while hyperscalers focus on scale and compute power in centralized locations. Both strategies are needed and complementary: Edge requires highly distributed, localized infrastructure which complements centralized cloud, used for heavy compute and storage. As demand for Edge grows in 2026 and beyond – one forecast estimates a CAGR of 33.0% from 2025 to 2033 - expect rising demand for distributed architectures across new geographies. Tighter regulatory frameworks In 2026, expect to see a slew of reporting obligations, regulations, strategies and guidelines impacting CIOs, particularly in AI and cybersecurity. Most of the obligations under the EU AI Act will apply from 2 August 2026, while implementation of certain requirements for high-risk AI systems may be postponed. Reporting obligations for the EU Cyber Resilience Act are expected from September 2026, with phased obligations continuing from September 2026 onward under the EU Data Act. Cyber Security and Resilience Bill Peolpe also see the ISO/IEC 42001:2023 global standard for AI governance, which will lead CIOs and CAIOs to integrate AI governance into enterprise architecture and procurement decisions, as well as operational impacts for the Digital Services Act and the Digital Markets Act. In the UK, all eyes will be on the Cyber Security and Resilience Bill, while across Asia, Japan will see the impact of its AI Promotion Act and major initiatives following Singapore’s National AI Strategy 2.0 (NAIS 2.0) are also expected to come into effect in 2026.
In recent years, campus safety and student mental health have drawn growing attention. Government data in Taiwan show a rise in emotional and stress-related issues among students aged 15–24. Unauthorized attempts to enter campuses still occur, unsettling students and staff. Strengthening security management and proactive alerting has therefore become a priority for schools. To address risks such as expansive campuses, multiple entry points, blind spots, and potential intrusions, VIVOTEK (3454-TW), the leading global security solution provider, has been promoting its AI-driven education security solutions, designed to proactively detect risks and safeguard school environments. Era of real-time detection and proactive response According to a report by research firm GII, the global education security market is projected to reach USD 910 million in 2025 and grow to USD 1.6 billion by 2030, representing a compound annual growth rate (CAGR) of 11.96%. As AI video analytics, edge computing, and cloud management platforms mature, security systems are evolving beyond passive video playback into an era of real-time detection and proactive response. In education settings, AI can automatically detect intrusions into restricted zones and trigger instant alerts, enabling security personnel to make swift and informed decisions. VSS Pro platform Recently, VIVOTEK deployed a comprehensive education security solutions at a renowned national university in Taiwan, installing hundreds of AI Bullet and Fixed Dome cameras across entrances, rooftops, classrooms, corridors, walls, elevators, and parking areas. Integrated with the VAST Security Station (VSS) Pro platform, the system delivers: Proactive prevention: AI virtual fence defines restricted zones, detects loitering, notifies the security center, triggers on-site audio alerts, and coordinates real-time response. Efficient investigations: Broad coverage flags abandoned objects, while AI deep search traces intruders or vehicles in the shortest time using attributes (e.g., clothing color, backpack, vehicle type) to quickly assemble event timelines. VIVOTEK’s education security solutions With comprehensive, AI-enabled coverage, schools can monitor in real time and avert risks, fostering safe, welcoming, and sustainable learning environment. Beyond Taiwan, VIVOTEK’s education security solutions are also used in the United States, Belgium, and Indonesia, tailored to local needs to build a global network of smart, sustainable campuses.
When major fire and security specialists Cornerstone were appointed to deliver the life safety systems for the refurbishment of 77 Grosvenor Street, they faced a unique challenge. Located in the heart of London’s Mayfair district, the prestigious building features classical architecture and over 50,000 square feet of premium open-plan office space spread across six floors. The goal was to upgrade the fire protection without compromising the building’s refined aesthetics. The client, a major property management company, required a solution that was robust, reliable and unobtrusive. Working closely with the design and construction teams, Cornerstone turned to Hochiki Europe, a long-standing partner known for dependable systems that blend seamlessly into high-end environments. Latitude fire detection and alarm control system At the core of the installation is the Latitude fire detection and alarm control system. Chosen for its powerful cause and effect programming, flexible networking and modular scalability, Latitude was well suited to the demands of a multi-level heritage building. Its ability to support complex configurations made it ideal for a site where multiple zones, floors and room functions needed to be managed with precision. To deliver complete protection across the site, Cornerstone selected a combination of Hochiki's Enhanced System Protocol (ESP) addressable devices and the FIRElink aspirating detection system. The FIRElink system is adaptable to a broad range of environments and applications. ESP detectors From small, to very large areas, the system is particularly useful in protecting computer rooms or data centers but can be designed to fit almost any environment. ESP detectors offer high performance with a minimal visual footprint, ideal for preserving the character of the restored interiors. In areas requiring an even more discreet solution, such as decorative ceilings or high airflow zones, FIRElink was installed using capillary sampling pipes hidden within the building’s structure. One of the key advantages of the Latitude platform is its ability to interface with wider building management systems (BMS). At Grosvenor Street, this opens the door to centralized monitoring and control of fire safety in conjunction with other building systems. Open integration Latitude’s open integration options mean it can share status updates and alarm events in real time with the BMS, enabling facilities teams to coordinate responses quickly and efficiently. For a high-spec office environment, this not only improves safety outcomes but also supports smoother day-to-day operation and building performance. Patrick Anthony, Project Manager at Cornerstone, explained the decision: “We have a trusted relationship with the Hochiki team. Their systems and devices are reliable, help reduce false alarms and are designed to aesthetically fade into the background, exactly what this project needed and delivers complete peace of mind for the management team.” The site at Grosvenor Street is now protected by a fully integrated, future proof life safety system that meets modern building safety standards while maintaining the building’s elegance.
3xLOGIC, Inc., a major provider of integrated, intelligent security solutions, and a three-time Deloitte Technology Fast 500 winner, announced that Panda Restaurant Group, Inc. (parent of Panda Express, Panda Inn, and Hibachi-San) has completed deployment of 3xLOGIC’s VIGIL Trends Business Intelligence software to all of its North American locations. Interface Security Systems, headquartered in St. Louis, Missouri, is the integrator and overall project manager for this ambitious endeavor. Largest family-owned restaurant Panda Express is the largest family-owned restaurant in America, with more than 2,000 stores globally, 35,000 associates and $3 billion in sales. Since it was established in 1983, Panda has steadily grown with roughly 125 stores opening each year. Privately owned and operated, the restaurant is guided by the core values of its co-founders and co-CEO, Andrew and Peggy Cherng and is dedicated to developing its team members and giving back to the community. Business intelligence solutions “As an industry leader, Panda Express’s culture sets an expectation of best-in-class results,” explained Lyle Forcum, executive director of asset protection at Panda Express. “Accordingly, we needed a state-of-the-art business intelligence solution to provide us with truly actionable information. Intelligence we can act on is central to Panda’s business strategy, which focuses on meeting high standards through continuous operational improvement.” Starting in August 2017, 3xLOGIC and Interface Systems worked with Panda Express to customize Trends to meet the company’s unique, comprehensive needs. Interface began system deployment in QI 2018 with the first location going live in March 2018. Presently, Trends is deployed at 1,960 locations and has been integrated with existing Interface video surveillance and alarm systems. Tracking and improving operations “It was impressive that we were able to integrate Trends so seamlessly with existing intrusion and video systems,” said Sean Foley, senior vice president of national accounts at Interface Systems, “and the entire solution was rolled out without a single technician visiting any store.” Unlike many retail BI implementations, the focus at Panda Restaurant Group is not solely on retail loss prevention, but also on tracking and improving all operations at every store. Here are some of the key elements of store operations that Trends enables Panda to monitor, track, and improve: People Development: To set its people up for success, store managers are able to review all transactional behavior and address opportunity areas with employees within two days. Comparing Store Performance: The store managers’ Trends dashboard shows very clearly how the restaurant is performing compared to other stores in the region and to their prior month’s performance. Optimizing Store Efficiency: Trends visually displays how many people are working per hour, what job they are facilitating, and the revenue generated per hour. Monitoring Intrusion Data: Trends provides intrusion data, which shows in a very simple display when stores are opened and closed, deliveries are made, cleaning is done, and whether the store is being remotely armed and disarmed. Tracking Cash: Panda Express can track currency, how much is in the safe and when it was last counted, as well as petty cash spend along with scanned receipts for purchases. Custom Dashboards: The system provides an array of dashboards for all levels in the organization that give an at-a-glance or drilled-down overview of an employee’s priorities and responsibilities. “At Panda, safety and loss prevention are key priorities in executing great operations,” said Lyle Forcum, executive director of asset protection at Panda Express. “We worked with 3xLOGIC and Interface for over a year to implement a highly-customized solution to meet these priorities. Now, we have a cutting-edge tool deployed across the entire enterprise that we can all be proud of.”
Allied Universal®, the world’s pioneering security and facility services provider, has been selected by Seton Hall University™ to provide campus security programs. This moves strengthens the University’s commitment to providing a safe, secure, and welcoming environment for students, faculty, staff, and visitors. New security program Allied Universal will deliver comprehensive campus security services, including trained personnel, safety patrols, and emergency response support. The new security program is designed to enhance the University’s existing safety infrastructure, while helping to ensure that the campus community benefits from Allied Universal’s expertise in proactive risk management and security operations. New partnership “On behalf of Allied Universal, I want to express our sincere appreciation for this new partnership and for our shared commitment to creating a safer campus community,” said Steve Jones, Allied Universal Global Chairman and CEO. He adds, “As the pioneering security provider for higher education, we are excited to have been chosen to work with Seton Hall University as a higher education campus safety partner.” Seton Hall’s ongoing commitment The selection of Allied Universal builds on Seton Hall’s ongoing commitment to campus safety, combining the University’s strong public safety framework with Allied Universal’s proven expertise in higher education security. Together, the collaboration aims to provide a proactive, community-focused approach that reinforces a secure, welcoming environment for everyone on campus. Seton Hall’s mission “Allied Universal brings deep experience supporting higher education institutions across the country,” said Sergio Oliva, Associate Vice President for Public Safety and Security, adding “Their approach emphasises professionalism, training, and engagement with the communities they serve, values that align closely with Seton Hall’s mission and our own Public Safety philosophy.”
Cognitec Systems Pty Ltd is working with Home Affairs Australia to deliver 250 camera devices for facial image capture, image quality check, and traveler identity verification at all major international airports in Australia. With approximately 41 million international travelers entering and leaving Australia each year, the Department uses facial biometrics to collect and electronically verify the identity of eligible international travelers. Cognitec hardware and software systems Cognitec’s capture device, FaceVACS-Entry, detects the person’s height, automatically adjusts the camera position to capture a frontal pose photo, and uses automated face recognition to verify person identity. Cognitec is also providing integration software, mounting hardware, device installation services, as well as ongoing support and maintenance services for all Cognitec hardware and software systems. Relationship with the Department of Home Affairs “Cognitec is proud to continue a successful relationship with the Department of Home Affairs, and to deliver our technology for quick collection of biometric photos and for accurate traveler verification at the Australian border primary lines,” says Terry Hartmann, Cognitec’s Vice President Asia Pacific, adding “This project contributes to the security and ongoing digitization of the Australian border, ensuring trusted traveler identities.” FaceVACS-Entry is used by governments worldwide for applications that require the acquisition of standards-compliant photos, and the verification of a live image against reference images, such as access control, border control, and entry/exit programs.


Products


Round table discussion
Transportation systems need robust physical security to protect human life, to ensure economic stability, and to maintain national security. Because transportation involves moving large numbers of people and critical goods across vast, often interconnected infrastructure, it presents a highly attractive target for various threats. More threats equate to a greater need for security. We asked our Expert Panel Roundtable: What are the emerging applications of physical security in the transportation market?
Installing physical security systems requires integrating diverse technologies (e.g., cameras, access control, alarms) that often use different protocols and must be adapted to a building's unique physical layout and legacy infrastructure. Specialized technical expertise is required for seamless networking and proper configuration. Hopefully, no important factors are overlooked in the installation process. We asked our Expert Panel Roundtable: What is the most overlooked factor when installing physical security systems?
The healthcare industry faces unique and significant security challenges. Healthcare security professionals must balance an open, welcoming environment for patients and visitors with the need to protect valuable assets and personnel in a high-stress, 24/7 setting. These requirements direct the physical security technologies deployed in medical facilities. We asked our Expert Panel Roundtable: What are the unique aspects of the healthcare market, and how should the physical security industry adapt?
White papers

One System, One Card
Download
Aligning Physical And Cyber Defence For Total Protection
Download
Understanding AI-Powered Video Analytics
Download
Modernizing Access Control
Download
Enhancing Physical Access Control Using A Self-Service Model
Download
Open Credential Standards And The Impact On Physical Access Control
Download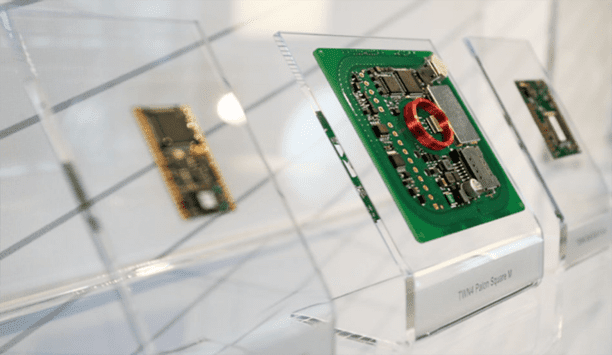
What is a universal RFID reader?
Download
System Design Considerations To Optimize Physical Access Control
Download
Milestone Cloud Deployment Guide
Download
How Biometrics Are Reshaping Security In A Connected World
Download
Using Artificial Intelligence (AI) To Automate Physical Security Systems
Download
Palm Vein Recognition
Download
Physical Access Control
Download
The 2024 State Of Physical Access Trend Report
Download
The Security Challenges Of Data Centers
Download











































